@workos/mcp-docs-server 0.1.0
This diff represents the content of publicly available package versions that have been released to one of the supported registries. The information contained in this diff is provided for informational purposes only and reflects changes between package versions as they appear in their respective public registries.
- package/.docs/organized/changelogs/workos-platform.json +277 -0
- package/.docs/organized/docs/admin-portal/_navigation.mdx +16 -0
- package/.docs/organized/docs/admin-portal/custom-branding.mdx +111 -0
- package/.docs/organized/docs/admin-portal/example-apps.mdx +46 -0
- package/.docs/organized/docs/admin-portal/index.mdx +240 -0
- package/.docs/organized/docs/audit-logs/_navigation.mdx +22 -0
- package/.docs/organized/docs/audit-logs/admin-portal.mdx +20 -0
- package/.docs/organized/docs/audit-logs/editing-events.mdx +27 -0
- package/.docs/organized/docs/audit-logs/exporting-events.mdx +29 -0
- package/.docs/organized/docs/audit-logs/index.mdx +110 -0
- package/.docs/organized/docs/audit-logs/log-streams.mdx +56 -0
- package/.docs/organized/docs/audit-logs/metadata-schema.mdx +21 -0
- package/.docs/organized/docs/custom-domains/_navigation.mdx +16 -0
- package/.docs/organized/docs/custom-domains/admin-portal.mdx +38 -0
- package/.docs/organized/docs/custom-domains/auth-api.mdx +59 -0
- package/.docs/organized/docs/custom-domains/authkit.mdx +36 -0
- package/.docs/organized/docs/custom-domains/email.mdx +41 -0
- package/.docs/organized/docs/custom-domains/index.mdx +19 -0
- package/.docs/organized/docs/dashboard.mdx +244 -0
- package/.docs/organized/docs/demo/_navigation.mdx +26 -0
- package/.docs/organized/docs/demo/accordion.mdx +34 -0
- package/.docs/organized/docs/demo/checklist.mdx +33 -0
- package/.docs/organized/docs/demo/code-block.mdx +185 -0
- package/.docs/organized/docs/demo/definition-list.mdx +35 -0
- package/.docs/organized/docs/demo/index.mdx +7 -0
- package/.docs/organized/docs/demo/punctuation.mdx +37 -0
- package/.docs/organized/docs/demo/replacements.mdx +26 -0
- package/.docs/organized/docs/demo/table.mdx +26 -0
- package/.docs/organized/docs/demo/tabs.mdx +17 -0
- package/.docs/organized/docs/directory-sync/_navigation.mdx +28 -0
- package/.docs/organized/docs/directory-sync/attributes.mdx +209 -0
- package/.docs/organized/docs/directory-sync/example-apps.mdx +46 -0
- package/.docs/organized/docs/directory-sync/handle-inactive-users.mdx +52 -0
- package/.docs/organized/docs/directory-sync/identity-provider-role-assignment.mdx +134 -0
- package/.docs/organized/docs/directory-sync/index.mdx +107 -0
- package/.docs/organized/docs/directory-sync/quick-start.mdx +129 -0
- package/.docs/organized/docs/directory-sync/understanding-events.mdx +209 -0
- package/.docs/organized/docs/domain-verification/_navigation.mdx +10 -0
- package/.docs/organized/docs/domain-verification/api.mdx +60 -0
- package/.docs/organized/docs/domain-verification/index.mdx +67 -0
- package/.docs/organized/docs/email.mdx +109 -0
- package/.docs/organized/docs/events/_navigation.mdx +22 -0
- package/.docs/organized/docs/events/data-syncing/data-reconciliation.mdx +56 -0
- package/.docs/organized/docs/events/data-syncing/events-api.mdx +114 -0
- package/.docs/organized/docs/events/data-syncing/index.mdx +66 -0
- package/.docs/organized/docs/events/data-syncing/webhooks.mdx +173 -0
- package/.docs/organized/docs/events/index.mdx +783 -0
- package/.docs/organized/docs/events/observability/datadog.mdx +76 -0
- package/.docs/organized/docs/fga/_navigation.mdx +64 -0
- package/.docs/organized/docs/fga/identity-provider-sessions.mdx +68 -0
- package/.docs/organized/docs/fga/index.mdx +60 -0
- package/.docs/organized/docs/fga/local-development.mdx +155 -0
- package/.docs/organized/docs/fga/modeling/abac.mdx +107 -0
- package/.docs/organized/docs/fga/modeling/blocklist.mdx +84 -0
- package/.docs/organized/docs/fga/modeling/conditional-roles.mdx +99 -0
- package/.docs/organized/docs/fga/modeling/custom-roles.mdx +90 -0
- package/.docs/organized/docs/fga/modeling/entitlements.mdx +127 -0
- package/.docs/organized/docs/fga/modeling/managed-service-provider.mdx +131 -0
- package/.docs/organized/docs/fga/modeling/org-roles-and-permissions.mdx +95 -0
- package/.docs/organized/docs/fga/modeling/policy-context.mdx +231 -0
- package/.docs/organized/docs/fga/modeling/public-access.mdx +61 -0
- package/.docs/organized/docs/fga/modeling/shareable-content.mdx +106 -0
- package/.docs/organized/docs/fga/modeling/superusers.mdx +74 -0
- package/.docs/organized/docs/fga/modeling/user-groups.mdx +92 -0
- package/.docs/organized/docs/fga/operations-usage.mdx +104 -0
- package/.docs/organized/docs/fga/playground.mdx +12 -0
- package/.docs/organized/docs/fga/policies.mdx +462 -0
- package/.docs/organized/docs/fga/query-language.mdx +112 -0
- package/.docs/organized/docs/fga/quick-start.mdx +174 -0
- package/.docs/organized/docs/fga/resources.mdx +92 -0
- package/.docs/organized/docs/fga/schema-management.mdx +224 -0
- package/.docs/organized/docs/fga/schema.mdx +388 -0
- package/.docs/organized/docs/fga/warrant-tokens.mdx +44 -0
- package/.docs/organized/docs/fga/warrants.mdx +92 -0
- package/.docs/organized/docs/glossary.mdx +184 -0
- package/.docs/organized/docs/integrations/_navigation.mdx +6 -0
- package/.docs/organized/docs/integrations/access-people-hr.mdx +87 -0
- package/.docs/organized/docs/integrations/adp-oidc.mdx +103 -0
- package/.docs/organized/docs/integrations/apple.mdx +169 -0
- package/.docs/organized/docs/integrations/auth0-directory-sync.mdx +78 -0
- package/.docs/organized/docs/integrations/auth0-enterprise-connection.mdx +92 -0
- package/.docs/organized/docs/integrations/auth0-saml.mdx +81 -0
- package/.docs/organized/docs/integrations/aws-cognito.mdx +81 -0
- package/.docs/organized/docs/integrations/bamboohr.mdx +90 -0
- package/.docs/organized/docs/integrations/breathe-hr.mdx +89 -0
- package/.docs/organized/docs/integrations/bubble.mdx +129 -0
- package/.docs/organized/docs/integrations/cas-saml.mdx +65 -0
- package/.docs/organized/docs/integrations/cezanne.mdx +74 -0
- package/.docs/organized/docs/integrations/classlink-saml.mdx +100 -0
- package/.docs/organized/docs/integrations/cloudflare-saml.mdx +164 -0
- package/.docs/organized/docs/integrations/cyberark-saml.mdx +138 -0
- package/.docs/organized/docs/integrations/cyberark-scim.mdx +100 -0
- package/.docs/organized/docs/integrations/duo-saml.mdx +127 -0
- package/.docs/organized/docs/integrations/entra-id-saml.mdx +156 -0
- package/.docs/organized/docs/integrations/entra-id-scim.mdx +218 -0
- package/.docs/organized/docs/integrations/firebase.mdx +98 -0
- package/.docs/organized/docs/integrations/fourth.mdx +66 -0
- package/.docs/organized/docs/integrations/github-oauth.mdx +85 -0
- package/.docs/organized/docs/integrations/gitlab-oauth.mdx +81 -0
- package/.docs/organized/docs/integrations/google-directory-sync.mdx +86 -0
- package/.docs/organized/docs/integrations/google-oauth.mdx +173 -0
- package/.docs/organized/docs/integrations/google-saml.mdx +135 -0
- package/.docs/organized/docs/integrations/hibob.mdx +98 -0
- package/.docs/organized/docs/integrations/jumpcloud-saml.mdx +96 -0
- package/.docs/organized/docs/integrations/jumpcloud-scim.mdx +106 -0
- package/.docs/organized/docs/integrations/keycloak-saml.mdx +128 -0
- package/.docs/organized/docs/integrations/lastpass-saml.mdx +134 -0
- package/.docs/organized/docs/integrations/linkedin-oauth.mdx +77 -0
- package/.docs/organized/docs/integrations/login-gov-oidc.mdx +103 -0
- package/.docs/organized/docs/integrations/microsoft-ad-fs-saml.mdx +96 -0
- package/.docs/organized/docs/integrations/microsoft-oauth.mdx +101 -0
- package/.docs/organized/docs/integrations/miniorange-saml.mdx +124 -0
- package/.docs/organized/docs/integrations/net-iq-saml.mdx +75 -0
- package/.docs/organized/docs/integrations/next-auth.mdx +257 -0
- package/.docs/organized/docs/integrations/oidc.mdx +64 -0
- package/.docs/organized/docs/integrations/okta-saml.mdx +144 -0
- package/.docs/organized/docs/integrations/okta-scim.mdx +210 -0
- package/.docs/organized/docs/integrations/onelogin-saml.mdx +131 -0
- package/.docs/organized/docs/integrations/onelogin-scim.mdx +150 -0
- package/.docs/organized/docs/integrations/oracle-saml.mdx +76 -0
- package/.docs/organized/docs/integrations/pingfederate-saml.mdx +103 -0
- package/.docs/organized/docs/integrations/pingfederate-scim.mdx +150 -0
- package/.docs/organized/docs/integrations/pingone-saml.mdx +86 -0
- package/.docs/organized/docs/integrations/react-native-expo.mdx +93 -0
- package/.docs/organized/docs/integrations/rippling-saml.mdx +174 -0
- package/.docs/organized/docs/integrations/rippling-scim.mdx +148 -0
- package/.docs/organized/docs/integrations/salesforce-saml.mdx +143 -0
- package/.docs/organized/docs/integrations/saml.mdx +64 -0
- package/.docs/organized/docs/integrations/scim.mdx +64 -0
- package/.docs/organized/docs/integrations/sftp.mdx +150 -0
- package/.docs/organized/docs/integrations/shibboleth-generic-saml.mdx +84 -0
- package/.docs/organized/docs/integrations/shibboleth-unsolicited-saml.mdx +84 -0
- package/.docs/organized/docs/integrations/simple-saml-php.mdx +78 -0
- package/.docs/organized/docs/integrations/slack-oauth.mdx +102 -0
- package/.docs/organized/docs/integrations/supabase.mdx +68 -0
- package/.docs/organized/docs/integrations/vmware-saml.mdx +100 -0
- package/.docs/organized/docs/integrations/workday.mdx +156 -0
- package/.docs/organized/docs/integrations/xero-oauth.mdx +83 -0
- package/.docs/organized/docs/magic-link/_navigation.mdx +16 -0
- package/.docs/organized/docs/magic-link/example-apps.mdx +46 -0
- package/.docs/organized/docs/magic-link/index.mdx +199 -0
- package/.docs/organized/docs/magic-link/launch-checklist.mdx +27 -0
- package/.docs/organized/docs/mfa/_navigation.mdx +18 -0
- package/.docs/organized/docs/mfa/example-apps.mdx +46 -0
- package/.docs/organized/docs/mfa/index.mdx +140 -0
- package/.docs/organized/docs/mfa/ux/enrollment.mdx +74 -0
- package/.docs/organized/docs/mfa/ux/sign-in.mdx +30 -0
- package/.docs/organized/docs/migrate/_navigation.mdx +6 -0
- package/.docs/organized/docs/migrate/auth0.mdx +98 -0
- package/.docs/organized/docs/migrate/aws-cognito.mdx +115 -0
- package/.docs/organized/docs/migrate/clerk.mdx +106 -0
- package/.docs/organized/docs/migrate/firebase.mdx +80 -0
- package/.docs/organized/docs/migrate/other-services.mdx +179 -0
- package/.docs/organized/docs/migrate/standalone-sso.mdx +105 -0
- package/.docs/organized/docs/on-prem-deployment.mdx +119 -0
- package/.docs/organized/docs/postman.mdx +90 -0
- package/.docs/organized/docs/reference/_navigation.mdx +527 -0
- package/.docs/organized/docs/reference/admin-portal/index.mdx +6 -0
- package/.docs/organized/docs/reference/admin-portal/portal-link/generate.mdx +268 -0
- package/.docs/organized/docs/reference/admin-portal/portal-link/index.mdx +15 -0
- package/.docs/organized/docs/reference/admin-portal/provider-icons/index.mdx +52 -0
- package/.docs/organized/docs/reference/api-keys.mdx +22 -0
- package/.docs/organized/docs/reference/audit-logs/audit-log-export.mdx +239 -0
- package/.docs/organized/docs/reference/audit-logs/audit-log-schema.mdx +69 -0
- package/.docs/organized/docs/reference/audit-logs/create-event.mdx +673 -0
- package/.docs/organized/docs/reference/audit-logs/create-export.mdx +308 -0
- package/.docs/organized/docs/reference/audit-logs/create-schema.mdx +95 -0
- package/.docs/organized/docs/reference/audit-logs/get-export.mdx +117 -0
- package/.docs/organized/docs/reference/audit-logs/get-retention.mdx +34 -0
- package/.docs/organized/docs/reference/audit-logs/index.mdx +6 -0
- package/.docs/organized/docs/reference/audit-logs/list-actions.mdx +40 -0
- package/.docs/organized/docs/reference/audit-logs/list-schemas.mdx +40 -0
- package/.docs/organized/docs/reference/audit-logs/set-retention.mdx +39 -0
- package/.docs/organized/docs/reference/client-libraries.mdx +19 -0
- package/.docs/organized/docs/reference/directory-sync/directory/delete.mdx +90 -0
- package/.docs/organized/docs/reference/directory-sync/directory/get.mdx +105 -0
- package/.docs/organized/docs/reference/directory-sync/directory/index.mdx +385 -0
- package/.docs/organized/docs/reference/directory-sync/directory/list.mdx +281 -0
- package/.docs/organized/docs/reference/directory-sync/directory-group/get.mdx +105 -0
- package/.docs/organized/docs/reference/directory-sync/directory-group/index.mdx +277 -0
- package/.docs/organized/docs/reference/directory-sync/directory-group/list.mdx +295 -0
- package/.docs/organized/docs/reference/directory-sync/directory-user/get.mdx +112 -0
- package/.docs/organized/docs/reference/directory-sync/directory-user/index.mdx +470 -0
- package/.docs/organized/docs/reference/directory-sync/directory-user/list.mdx +304 -0
- package/.docs/organized/docs/reference/directory-sync/index.mdx +10 -0
- package/.docs/organized/docs/reference/domain-verification/create.mdx +38 -0
- package/.docs/organized/docs/reference/domain-verification/get.mdx +32 -0
- package/.docs/organized/docs/reference/domain-verification/index.mdx +84 -0
- package/.docs/organized/docs/reference/domain-verification/verify.mdx +36 -0
- package/.docs/organized/docs/reference/errors.mdx +30 -0
- package/.docs/organized/docs/reference/events/index.mdx +9 -0
- package/.docs/organized/docs/reference/events/list.mdx +246 -0
- package/.docs/organized/docs/reference/fga/batch-check.mdx +277 -0
- package/.docs/organized/docs/reference/fga/check.mdx +563 -0
- package/.docs/organized/docs/reference/fga/index.mdx +6 -0
- package/.docs/organized/docs/reference/fga/policy/create.mdx +27 -0
- package/.docs/organized/docs/reference/fga/policy/delete.mdx +18 -0
- package/.docs/organized/docs/reference/fga/policy/get.mdx +23 -0
- package/.docs/organized/docs/reference/fga/policy/index.mdx +52 -0
- package/.docs/organized/docs/reference/fga/policy/list.mdx +41 -0
- package/.docs/organized/docs/reference/fga/policy/update.mdx +26 -0
- package/.docs/organized/docs/reference/fga/query.mdx +375 -0
- package/.docs/organized/docs/reference/fga/resource/batch-write.mdx +175 -0
- package/.docs/organized/docs/reference/fga/resource/create.mdx +130 -0
- package/.docs/organized/docs/reference/fga/resource/delete.mdx +86 -0
- package/.docs/organized/docs/reference/fga/resource/get.mdx +88 -0
- package/.docs/organized/docs/reference/fga/resource/index.mdx +98 -0
- package/.docs/organized/docs/reference/fga/resource/list.mdx +188 -0
- package/.docs/organized/docs/reference/fga/resource/update.mdx +115 -0
- package/.docs/organized/docs/reference/fga/resource-type/apply.mdx +35 -0
- package/.docs/organized/docs/reference/fga/resource-type/create.mdx +24 -0
- package/.docs/organized/docs/reference/fga/resource-type/delete.mdx +22 -0
- package/.docs/organized/docs/reference/fga/resource-type/get.mdx +23 -0
- package/.docs/organized/docs/reference/fga/resource-type/index.mdx +68 -0
- package/.docs/organized/docs/reference/fga/resource-type/list.mdx +36 -0
- package/.docs/organized/docs/reference/fga/resource-type/update.mdx +23 -0
- package/.docs/organized/docs/reference/fga/schema/apply.mdx +42 -0
- package/.docs/organized/docs/reference/fga/schema/get.mdx +24 -0
- package/.docs/organized/docs/reference/fga/schema/index.mdx +39 -0
- package/.docs/organized/docs/reference/fga/warrant/batch-write.mdx +226 -0
- package/.docs/organized/docs/reference/fga/warrant/create.mdx +215 -0
- package/.docs/organized/docs/reference/fga/warrant/delete.mdx +212 -0
- package/.docs/organized/docs/reference/fga/warrant/index.mdx +186 -0
- package/.docs/organized/docs/reference/fga/warrant/list.mdx +282 -0
- package/.docs/organized/docs/reference/idempotency.mdx +21 -0
- package/.docs/organized/docs/reference/index.mdx +194 -0
- package/.docs/organized/docs/reference/magic-link/index.mdx +8 -0
- package/.docs/organized/docs/reference/magic-link/passwordless-session/create.mdx +268 -0
- package/.docs/organized/docs/reference/magic-link/passwordless-session/index.mdx +203 -0
- package/.docs/organized/docs/reference/magic-link/passwordless-session/send-email.mdx +158 -0
- package/.docs/organized/docs/reference/mfa/authentication-challenge.mdx +217 -0
- package/.docs/organized/docs/reference/mfa/authentication-factor.mdx +381 -0
- package/.docs/organized/docs/reference/mfa/challenge-factor.mdx +170 -0
- package/.docs/organized/docs/reference/mfa/delete-factor.mdx +93 -0
- package/.docs/organized/docs/reference/mfa/enroll-factor.mdx +241 -0
- package/.docs/organized/docs/reference/mfa/get-factor.mdx +108 -0
- package/.docs/organized/docs/reference/mfa/index.mdx +8 -0
- package/.docs/organized/docs/reference/mfa/verify-challenge.mdx +228 -0
- package/.docs/organized/docs/reference/organization/create.mdx +216 -0
- package/.docs/organized/docs/reference/organization/delete.mdx +89 -0
- package/.docs/organized/docs/reference/organization/get-by-external-id.mdx +40 -0
- package/.docs/organized/docs/reference/organization/get.mdx +104 -0
- package/.docs/organized/docs/reference/organization/index.mdx +274 -0
- package/.docs/organized/docs/reference/organization/list.mdx +258 -0
- package/.docs/organized/docs/reference/organization/update.mdx +236 -0
- package/.docs/organized/docs/reference/organization-domain.mdx +189 -0
- package/.docs/organized/docs/reference/pagination.mdx +244 -0
- package/.docs/organized/docs/reference/radar/attempts/create.mdx +115 -0
- package/.docs/organized/docs/reference/radar/attempts/index.mdx +7 -0
- package/.docs/organized/docs/reference/radar/attempts/update.mdx +34 -0
- package/.docs/organized/docs/reference/radar/index.mdx +8 -0
- package/.docs/organized/docs/reference/radar/lists/delete.mdx +36 -0
- package/.docs/organized/docs/reference/radar/lists/index.mdx +7 -0
- package/.docs/organized/docs/reference/radar/lists/update.mdx +36 -0
- package/.docs/organized/docs/reference/rate-limits.mdx +50 -0
- package/.docs/organized/docs/reference/roles/index.mdx +268 -0
- package/.docs/organized/docs/reference/roles/list-for-organization.mdx +152 -0
- package/.docs/organized/docs/reference/sso/connection/delete.mdx +89 -0
- package/.docs/organized/docs/reference/sso/connection/get.mdx +104 -0
- package/.docs/organized/docs/reference/sso/connection/index.mdx +388 -0
- package/.docs/organized/docs/reference/sso/connection/list.mdx +320 -0
- package/.docs/organized/docs/reference/sso/get-authorization-url/error-codes.mdx +28 -0
- package/.docs/organized/docs/reference/sso/get-authorization-url/index.mdx +434 -0
- package/.docs/organized/docs/reference/sso/get-authorization-url/redirect-uri.mdx +21 -0
- package/.docs/organized/docs/reference/sso/index.mdx +8 -0
- package/.docs/organized/docs/reference/sso/logout/authorize.mdx +47 -0
- package/.docs/organized/docs/reference/sso/logout/index.mdx +14 -0
- package/.docs/organized/docs/reference/sso/logout/redirect.mdx +32 -0
- package/.docs/organized/docs/reference/sso/profile/get-profile-and-token.mdx +229 -0
- package/.docs/organized/docs/reference/sso/profile/get-user-profile.mdx +127 -0
- package/.docs/organized/docs/reference/sso/profile/index.mdx +364 -0
- package/.docs/organized/docs/reference/testing.mdx +8 -0
- package/.docs/organized/docs/reference/user-management/access-token/index.mdx +13 -0
- package/.docs/organized/docs/reference/user-management/authentication/code.mdx +448 -0
- package/.docs/organized/docs/reference/user-management/authentication/email-verification.mdx +359 -0
- package/.docs/organized/docs/reference/user-management/authentication/get-authorization-url/error-codes.mdx +25 -0
- package/.docs/organized/docs/reference/user-management/authentication/get-authorization-url/index.mdx +425 -0
- package/.docs/organized/docs/reference/user-management/authentication/get-authorization-url/pkce.mdx +9 -0
- package/.docs/organized/docs/reference/user-management/authentication/get-authorization-url/redirect-uri.mdx +23 -0
- package/.docs/organized/docs/reference/user-management/authentication/index.mdx +66 -0
- package/.docs/organized/docs/reference/user-management/authentication/magic-auth.mdx +353 -0
- package/.docs/organized/docs/reference/user-management/authentication/organization-selection.mdx +349 -0
- package/.docs/organized/docs/reference/user-management/authentication/password.mdx +350 -0
- package/.docs/organized/docs/reference/user-management/authentication/refresh-and-seal-session-data.mdx +57 -0
- package/.docs/organized/docs/reference/user-management/authentication/refresh-token.mdx +381 -0
- package/.docs/organized/docs/reference/user-management/authentication/session-cookie.mdx +79 -0
- package/.docs/organized/docs/reference/user-management/authentication/totp.mdx +369 -0
- package/.docs/organized/docs/reference/user-management/authentication-errors/email-verification-required-error.mdx +42 -0
- package/.docs/organized/docs/reference/user-management/authentication-errors/index.mdx +20 -0
- package/.docs/organized/docs/reference/user-management/authentication-errors/mfa-challenge-error.mdx +44 -0
- package/.docs/organized/docs/reference/user-management/authentication-errors/mfa-enrollment-error.mdx +37 -0
- package/.docs/organized/docs/reference/user-management/authentication-errors/organization-authentication-required-error.mdx +68 -0
- package/.docs/organized/docs/reference/user-management/authentication-errors/organization-selection-error.mdx +44 -0
- package/.docs/organized/docs/reference/user-management/authentication-errors/sso-required-error.mdx +51 -0
- package/.docs/organized/docs/reference/user-management/email-verification/get.mdx +88 -0
- package/.docs/organized/docs/reference/user-management/email-verification/index.mdx +227 -0
- package/.docs/organized/docs/reference/user-management/identity/index.mdx +74 -0
- package/.docs/organized/docs/reference/user-management/identity/list.mdx +52 -0
- package/.docs/organized/docs/reference/user-management/index.mdx +13 -0
- package/.docs/organized/docs/reference/user-management/invitation/accept.mdx +39 -0
- package/.docs/organized/docs/reference/user-management/invitation/find-by-token.mdx +87 -0
- package/.docs/organized/docs/reference/user-management/invitation/get.mdx +87 -0
- package/.docs/organized/docs/reference/user-management/invitation/index.mdx +374 -0
- package/.docs/organized/docs/reference/user-management/invitation/list.mdx +247 -0
- package/.docs/organized/docs/reference/user-management/invitation/revoke.mdx +90 -0
- package/.docs/organized/docs/reference/user-management/invitation/send.mdx +230 -0
- package/.docs/organized/docs/reference/user-management/logout/get-logout-url-from-session-cookie.mdx +52 -0
- package/.docs/organized/docs/reference/user-management/logout/get-logout-url.mdx +147 -0
- package/.docs/organized/docs/reference/user-management/logout/index.mdx +26 -0
- package/.docs/organized/docs/reference/user-management/magic-auth/create.mdx +148 -0
- package/.docs/organized/docs/reference/user-management/magic-auth/get.mdx +88 -0
- package/.docs/organized/docs/reference/user-management/magic-auth/index.mdx +225 -0
- package/.docs/organized/docs/reference/user-management/mfa/authentication-challenge.mdx +194 -0
- package/.docs/organized/docs/reference/user-management/mfa/authentication-factor.mdx +324 -0
- package/.docs/organized/docs/reference/user-management/mfa/enroll-auth-factor.mdx +296 -0
- package/.docs/organized/docs/reference/user-management/mfa/index.mdx +5 -0
- package/.docs/organized/docs/reference/user-management/mfa/list-auth-factors.mdx +194 -0
- package/.docs/organized/docs/reference/user-management/organization-membership/create.mdx +155 -0
- package/.docs/organized/docs/reference/user-management/organization-membership/deactivate.mdx +106 -0
- package/.docs/organized/docs/reference/user-management/organization-membership/delete.mdx +76 -0
- package/.docs/organized/docs/reference/user-management/organization-membership/get.mdx +95 -0
- package/.docs/organized/docs/reference/user-management/organization-membership/index.mdx +265 -0
- package/.docs/organized/docs/reference/user-management/organization-membership/list.mdx +291 -0
- package/.docs/organized/docs/reference/user-management/organization-membership/reactivate.mdx +106 -0
- package/.docs/organized/docs/reference/user-management/organization-membership/update.mdx +119 -0
- package/.docs/organized/docs/reference/user-management/password-reset/create.mdx +108 -0
- package/.docs/organized/docs/reference/user-management/password-reset/get.mdx +88 -0
- package/.docs/organized/docs/reference/user-management/password-reset/index.mdx +227 -0
- package/.docs/organized/docs/reference/user-management/password-reset/reset-password.mdx +144 -0
- package/.docs/organized/docs/reference/user-management/session-helpers/authenticate.mdx +176 -0
- package/.docs/organized/docs/reference/user-management/session-helpers/get-logout-url.mdx +42 -0
- package/.docs/organized/docs/reference/user-management/session-helpers/index.mdx +14 -0
- package/.docs/organized/docs/reference/user-management/session-helpers/load-sealed-session.mdx +105 -0
- package/.docs/organized/docs/reference/user-management/session-helpers/refresh.mdx +213 -0
- package/.docs/organized/docs/reference/user-management/session-tokens/access-token.mdx +90 -0
- package/.docs/organized/docs/reference/user-management/session-tokens/index.mdx +5 -0
- package/.docs/organized/docs/reference/user-management/session-tokens/jwks.mdx +110 -0
- package/.docs/organized/docs/reference/user-management/session-tokens/refresh-token.mdx +8 -0
- package/.docs/organized/docs/reference/user-management/user/create.mdx +327 -0
- package/.docs/organized/docs/reference/user-management/user/delete.mdx +76 -0
- package/.docs/organized/docs/reference/user-management/user/get-by-external-id.mdx +39 -0
- package/.docs/organized/docs/reference/user-management/user/get.mdx +103 -0
- package/.docs/organized/docs/reference/user-management/user/index.mdx +322 -0
- package/.docs/organized/docs/reference/user-management/user/list.mdx +260 -0
- package/.docs/organized/docs/reference/user-management/user/update.mdx +344 -0
- package/.docs/organized/docs/reference/vault/index.mdx +6 -0
- package/.docs/organized/docs/reference/vault/key/create-data-key.mdx +106 -0
- package/.docs/organized/docs/reference/vault/key/decrypt-data-key.mdx +84 -0
- package/.docs/organized/docs/reference/vault/key/decrypt-data.mdx +52 -0
- package/.docs/organized/docs/reference/vault/key/encrypt-data.mdx +58 -0
- package/.docs/organized/docs/reference/vault/key/index.mdx +25 -0
- package/.docs/organized/docs/reference/vault/object/create.mdx +62 -0
- package/.docs/organized/docs/reference/vault/object/delete.mdx +75 -0
- package/.docs/organized/docs/reference/vault/object/get.mdx +50 -0
- package/.docs/organized/docs/reference/vault/object/index.mdx +174 -0
- package/.docs/organized/docs/reference/vault/object/list.mdx +105 -0
- package/.docs/organized/docs/reference/vault/object/metadata.mdx +52 -0
- package/.docs/organized/docs/reference/vault/object/update.mdx +67 -0
- package/.docs/organized/docs/reference/vault/object/version.mdx +87 -0
- package/.docs/organized/docs/reference/vault/object/versions.mdx +83 -0
- package/.docs/organized/docs/reference/widgets/get-token.mdx +185 -0
- package/.docs/organized/docs/reference/widgets/index.mdx +6 -0
- package/.docs/organized/docs/reference/workos-connect/authorize/index.mdx +75 -0
- package/.docs/organized/docs/reference/workos-connect/index.mdx +33 -0
- package/.docs/organized/docs/reference/workos-connect/introspection/index.mdx +122 -0
- package/.docs/organized/docs/reference/workos-connect/metadata/index.mdx +25 -0
- package/.docs/organized/docs/reference/workos-connect/metadata/oauth-authorization-server/index.mdx +99 -0
- package/.docs/organized/docs/reference/workos-connect/metadata/openid-configuration/index.mdx +70 -0
- package/.docs/organized/docs/reference/workos-connect/token/authorization-code-grant/access-token.mdx +53 -0
- package/.docs/organized/docs/reference/workos-connect/token/authorization-code-grant/id-token.mdx +60 -0
- package/.docs/organized/docs/reference/workos-connect/token/authorization-code-grant/index.mdx +69 -0
- package/.docs/organized/docs/reference/workos-connect/token/client-credentials-grant/access-token.mdx +46 -0
- package/.docs/organized/docs/reference/workos-connect/token/client-credentials-grant/index.mdx +56 -0
- package/.docs/organized/docs/reference/workos-connect/token/index.mdx +39 -0
- package/.docs/organized/docs/reference/workos-connect/token/refresh-token-grant.mdx +69 -0
- package/.docs/organized/docs/reference/workos-connect/userinfo/index.mdx +46 -0
- package/.docs/organized/docs/sdks/dotnet.mdx +6 -0
- package/.docs/organized/docs/sdks/elixir.mdx +6 -0
- package/.docs/organized/docs/sdks/go.mdx +6 -0
- package/.docs/organized/docs/sdks/java.mdx +9 -0
- package/.docs/organized/docs/sdks/laravel.mdx +6 -0
- package/.docs/organized/docs/sdks/node.mdx +9 -0
- package/.docs/organized/docs/sdks/php.mdx +6 -0
- package/.docs/organized/docs/sdks/python.mdx +6 -0
- package/.docs/organized/docs/sdks/ruby.mdx +9 -0
- package/.docs/organized/docs/sso/_navigation.mdx +44 -0
- package/.docs/organized/docs/sso/_sequence-diagrams/saml-protocol-security-considerations.md +59 -0
- package/.docs/organized/docs/sso/attributes.mdx +110 -0
- package/.docs/organized/docs/sso/domains.mdx +111 -0
- package/.docs/organized/docs/sso/example-apps.mdx +46 -0
- package/.docs/organized/docs/sso/identity-provider-role-assignment.mdx +113 -0
- package/.docs/organized/docs/sso/index.mdx +295 -0
- package/.docs/organized/docs/sso/it-team-faq.mdx +35 -0
- package/.docs/organized/docs/sso/jit-provisioning.mdx +101 -0
- package/.docs/organized/docs/sso/launch-checklist.mdx +71 -0
- package/.docs/organized/docs/sso/login-flows.mdx +101 -0
- package/.docs/organized/docs/sso/redirect-uris.mdx +44 -0
- package/.docs/organized/docs/sso/saml-security.mdx +122 -0
- package/.docs/organized/docs/sso/signing-certificates.mdx +121 -0
- package/.docs/organized/docs/sso/single-logout.mdx +45 -0
- package/.docs/organized/docs/sso/test-sso.mdx +73 -0
- package/.docs/organized/docs/sso/ux/sign-in.mdx +44 -0
- package/.docs/organized/docs/user-management/_navigation.mdx +87 -0
- package/.docs/organized/docs/user-management/actions.mdx +169 -0
- package/.docs/organized/docs/user-management/authkit.mdx +69 -0
- package/.docs/organized/docs/user-management/branding.mdx +143 -0
- package/.docs/organized/docs/user-management/connect.mdx +110 -0
- package/.docs/organized/docs/user-management/custom-emails.mdx +164 -0
- package/.docs/organized/docs/user-management/directory-provisioning.mdx +78 -0
- package/.docs/organized/docs/user-management/domain-verification.mdx +28 -0
- package/.docs/organized/docs/user-management/email-password.mdx +42 -0
- package/.docs/organized/docs/user-management/email-verification.mdx +29 -0
- package/.docs/organized/docs/user-management/entitlements.mdx +46 -0
- package/.docs/organized/docs/user-management/example-apps.mdx +39 -0
- package/.docs/organized/docs/user-management/identity-linking.mdx +52 -0
- package/.docs/organized/docs/user-management/impersonation.mdx +82 -0
- package/.docs/organized/docs/user-management/index.mdx +525 -0
- package/.docs/organized/docs/user-management/invitations.mdx +60 -0
- package/.docs/organized/docs/user-management/invite-only-signup.mdx +72 -0
- package/.docs/organized/docs/user-management/jit-provisioning.mdx +36 -0
- package/.docs/organized/docs/user-management/jwt-templates.mdx +278 -0
- package/.docs/organized/docs/user-management/magic-auth.mdx +36 -0
- package/.docs/organized/docs/user-management/mcp.mdx +146 -0
- package/.docs/organized/docs/user-management/metadata.mdx +119 -0
- package/.docs/organized/docs/user-management/mfa.mdx +32 -0
- package/.docs/organized/docs/user-management/migrations.mdx +20 -0
- package/.docs/organized/docs/user-management/modeling-your-app.mdx +149 -0
- package/.docs/organized/docs/user-management/organization-policies.mdx +33 -0
- package/.docs/organized/docs/user-management/overview.mdx +46 -0
- package/.docs/organized/docs/user-management/passkeys.mdx +42 -0
- package/.docs/organized/docs/user-management/radar.mdx +127 -0
- package/.docs/organized/docs/user-management/roles-and-permissions.mdx +155 -0
- package/.docs/organized/docs/user-management/sessions.mdx +101 -0
- package/.docs/organized/docs/user-management/social-login.mdx +34 -0
- package/.docs/organized/docs/user-management/sso-with-contractors.mdx +85 -0
- package/.docs/organized/docs/user-management/sso.mdx +96 -0
- package/.docs/organized/docs/user-management/users-organizations.mdx +91 -0
- package/.docs/organized/docs/user-management/widgets.mdx +190 -0
- package/.docs/organized/docs/vault/_navigation.mdx +14 -0
- package/.docs/organized/docs/vault/index.mdx +38 -0
- package/.docs/organized/docs/vault/key-context.mdx +32 -0
- package/.docs/organized/docs/vault/quick-start.mdx +82 -0
- package/README.md +252 -0
- package/dist/chunk-64GKEK6G.js +48 -0
- package/dist/chunk-64GKEK6G.js.map +1 -0
- package/dist/get-tools.d.ts +23 -0
- package/dist/get-tools.js +8 -0
- package/dist/get-tools.js.map +1 -0
- package/dist/index.d.ts +1 -0
- package/dist/index.js +552 -0
- package/dist/index.js.map +1 -0
- package/dist/prepare.d.ts +2 -0
- package/dist/prepare.js +269 -0
- package/dist/prepare.js.map +1 -0
- package/package.json +49 -0
|
@@ -0,0 +1,295 @@
|
|
|
1
|
+
---
|
|
2
|
+
title: Single Sign-On
|
|
3
|
+
description: "Facilitate greater security, easier account management, and\_accelerated application onboarding and adoption."
|
|
4
|
+
showNextPage: true
|
|
5
|
+
originalPath: .tmp-workos-clone/packages/docs/content/sso/index.mdx
|
|
6
|
+
---
|
|
7
|
+
|
|
8
|
+
## Choose your integration approach
|
|
9
|
+
|
|
10
|
+
There are two ways to integrate Single Sign-On (SSO) with WorkOS:
|
|
11
|
+
|
|
12
|
+
### (A) With the standalone SSO API
|
|
13
|
+
|
|
14
|
+
The standalone API (covered in this document), is a standalone API for integrating into an existing auth stack.
|
|
15
|
+
|
|
16
|
+
### (B) Using WorkOS User Management
|
|
17
|
+
|
|
18
|
+
[User Management](/user-management) is a complete authentication platform which includes SSO out of the box.
|
|
19
|
+
|
|
20
|
+
## How Single Sign-On works
|
|
21
|
+
|
|
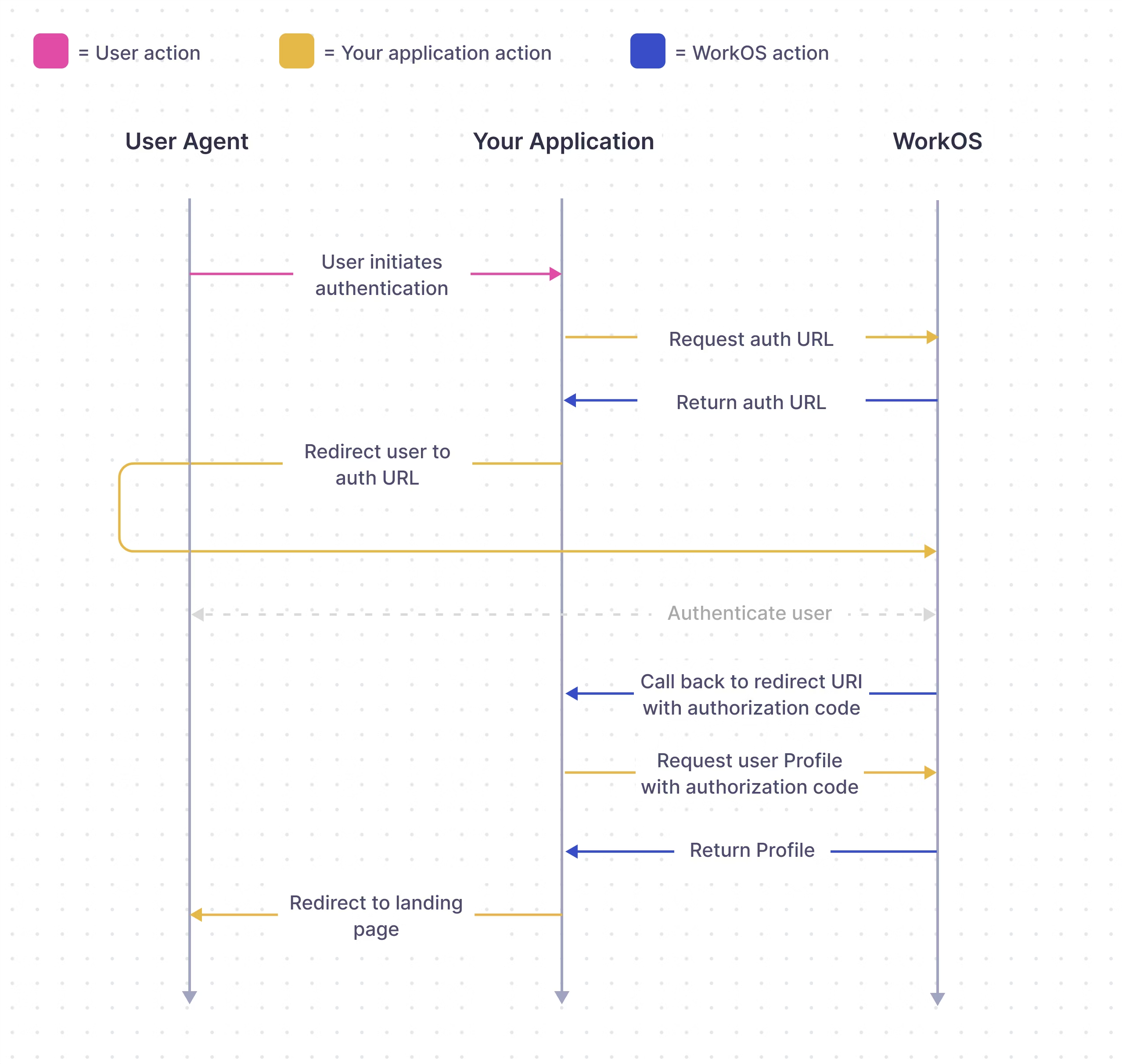
22
|
+
Single Sign-On is the most frequently asked for requirement by organizations looking to adopt new SaaS applications. SSO enables authentication via an organization’s [identity provider (IdP)](/glossary/idp).
|
|
23
|
+
|
|
24
|
+
This service is compatible with any IdP that supports either the [SAML](/glossary/saml) or [OIDC](/glossary/oidc) protocols. It’s modeled to meet the [OAuth 2.0](/glossary/oauth-2-0) framework specification, abstracting away the underlying authentication handshakes between different IdPs.
|
|
25
|
+
|
|
26
|
+
[border=false]
|
|
27
|
+
|
|
28
|
+
WorkOS SSO API acts as authentication middleware and intentionally does not handle user database management for your application.
|
|
29
|
+
|
|
30
|
+
## What you’ll build
|
|
31
|
+
|
|
32
|
+
In this guide, we’ll take you from learning about Single Sign-On and POC-ing all the way through to authenticating your first user via the WorkOS SSO API.
|
|
33
|
+
|
|
34
|
+
## Before getting started
|
|
35
|
+
|
|
36
|
+
To get the most out of this guide, you’ll need:
|
|
37
|
+
|
|
38
|
+
- A [WorkOS account](https://dashboard.workos.com/)
|
|
39
|
+
- A local app to integrate SSO with.
|
|
40
|
+
|
|
41
|
+
Reference these [example apps](/sso/example-apps) as you follow this guide.
|
|
42
|
+
|
|
43
|
+
## API object definitions
|
|
44
|
+
|
|
45
|
+
[Connection](/reference/sso/connection)
|
|
46
|
+
: The method by which a group of users (typically in a single organization) sign in to your application.
|
|
47
|
+
|
|
48
|
+
[Profile](/reference/sso/profile)
|
|
49
|
+
: Represents an authenticated user. The Profile object contains information relevant to a user in the form of normalized and raw attributes.
|
|
50
|
+
|
|
51
|
+
## (1) Add SSO to your app
|
|
52
|
+
|
|
53
|
+
Let’s build the SSO authentication workflow into your app.
|
|
54
|
+
|
|
55
|
+
### Install the WorkOS SDK
|
|
56
|
+
|
|
57
|
+
WorkOS offers native SDKs in several popular programming languages. Choose a language below to see instructions in your application’s language.
|
|
58
|
+
|
|
59
|
+
<LanguageSelector>
|
|
60
|
+
Install the SDK using the command below.
|
|
61
|
+
|
|
62
|
+
<CodeBlock title="Install the WorkOS SDK" file="install-sdk">
|
|
63
|
+
<CodeBlockTab language="js" file="install-sdk-npm" title="npm" />
|
|
64
|
+
<CodeBlockTab language="js" file="install-sdk-yarn" title="Yarn" />
|
|
65
|
+
<CodeBlockTab language="java" file="install-sdk-maven" title="Maven" />
|
|
66
|
+
<CodeBlockTab language="java" file="install-sdk-gradle" title="Gradle" />
|
|
67
|
+
<CodeBlockTab language="ruby" file="install-sdk-terminal" title="Terminal" />
|
|
68
|
+
<CodeBlockTab language="ruby" file="install-sdk-bundler" title="Bundler" />
|
|
69
|
+
</CodeBlock>
|
|
70
|
+
</LanguageSelector>
|
|
71
|
+
|
|
72
|
+
### Set secrets
|
|
73
|
+
|
|
74
|
+
To make calls to WorkOS, provide the API key and, in some cases, the client ID. Store these values as managed secrets, such as `WORKOS_API_KEY` and `WORKOS_CLIENT_ID`, and pass them to the SDKs either as environment variables or directly in your app’s configuration based on your preferences.
|
|
75
|
+
|
|
76
|
+
```plain title="Environment variables"
|
|
77
|
+
WORKOS_API_KEY='sk_example_123456789'
|
|
78
|
+
WORKOS_CLIENT_ID='client_123456789'
|
|
79
|
+
```
|
|
80
|
+
|
|
81
|
+
> The code examples use your staging API keys when [signed in](https://dashboard.workos.com)
|
|
82
|
+
|
|
83
|
+
### Add an endpoint to initiate SSO
|
|
84
|
+
|
|
85
|
+
The endpoint to initiate SSO via the WorkOS API is responsible for handing off the rest of the authentication workflow to WorkOS. There are a couple configuration options shown below.
|
|
86
|
+
|
|
87
|
+
You can use the optional `state` parameter to encode arbitrary information to help restore application state between redirects.
|
|
88
|
+
|
|
89
|
+
- | Using organization ID
|
|
90
|
+
|
|
91
|
+
Use the organization parameter when authenticating a user by their specific organization. This is the preferred parameter for SAML and OIDC connections.
|
|
92
|
+
|
|
93
|
+
The example below uses the Test Organization that is available in your staging environment and uses a mock identity provider. It’s created to help you test your SSO integration without having to go through the process of setting up an account with a real identity provider.
|
|
94
|
+
|
|
95
|
+
<CodeBlock
|
|
96
|
+
title="Authentication Endpoint"
|
|
97
|
+
file="get-authorization-with-organization-id"
|
|
98
|
+
>
|
|
99
|
+
<CodeBlockTab
|
|
100
|
+
language="js"
|
|
101
|
+
file="get-authorization-with-organization-id-next"
|
|
102
|
+
title="Next.js"
|
|
103
|
+
/>
|
|
104
|
+
<CodeBlockTab
|
|
105
|
+
language="js"
|
|
106
|
+
file="get-authorization-with-organization-id-next-app-router"
|
|
107
|
+
title="Next.js (App Router)"
|
|
108
|
+
/>
|
|
109
|
+
<CodeBlockTab
|
|
110
|
+
language="js"
|
|
111
|
+
file="get-authorization-with-organization-id-express"
|
|
112
|
+
title="Express"
|
|
113
|
+
/>
|
|
114
|
+
<CodeBlockTab
|
|
115
|
+
language="ruby"
|
|
116
|
+
file="get-authorization-with-organization-id-rails"
|
|
117
|
+
title="Rails"
|
|
118
|
+
/>
|
|
119
|
+
<CodeBlockTab
|
|
120
|
+
language="ruby"
|
|
121
|
+
file="get-authorization-with-organization-id-sinatra"
|
|
122
|
+
title="Sinatra"
|
|
123
|
+
/>
|
|
124
|
+
<CodeBlockTab
|
|
125
|
+
language="python"
|
|
126
|
+
file="get-authorization-with-organization-id-django"
|
|
127
|
+
title="Django"
|
|
128
|
+
/>
|
|
129
|
+
<CodeBlockTab
|
|
130
|
+
language="python"
|
|
131
|
+
file="get-authorization-with-organization-id-flask"
|
|
132
|
+
title="Flask"
|
|
133
|
+
/>
|
|
134
|
+
</CodeBlock>
|
|
135
|
+
|
|
136
|
+
- | Using connection ID
|
|
137
|
+
|
|
138
|
+
You can also use the connection parameter for SAML or OIDC connections when authenticating a user by their connection ID.
|
|
139
|
+
|
|
140
|
+
<CodeBlock
|
|
141
|
+
title="Authentication Endpoint"
|
|
142
|
+
file="get-authorization-with-connection-id"
|
|
143
|
+
>
|
|
144
|
+
<CodeBlockTab
|
|
145
|
+
language="js"
|
|
146
|
+
file="get-authorization-with-connection-id-next"
|
|
147
|
+
title="Next.js"
|
|
148
|
+
/>
|
|
149
|
+
<CodeBlockTab
|
|
150
|
+
language="js"
|
|
151
|
+
file="get-authorization-with-connection-id-next-app-router"
|
|
152
|
+
title="Next.js (App Router)"
|
|
153
|
+
/>
|
|
154
|
+
<CodeBlockTab
|
|
155
|
+
language="js"
|
|
156
|
+
file="get-authorization-with-connection-id-express"
|
|
157
|
+
title="Express"
|
|
158
|
+
/>
|
|
159
|
+
<CodeBlockTab
|
|
160
|
+
language="ruby"
|
|
161
|
+
file="get-authorization-with-connection-id-rails"
|
|
162
|
+
title="Rails"
|
|
163
|
+
/>
|
|
164
|
+
<CodeBlockTab
|
|
165
|
+
language="ruby"
|
|
166
|
+
file="get-authorization-with-connection-id-sinatra"
|
|
167
|
+
title="Sinatra"
|
|
168
|
+
/>
|
|
169
|
+
<CodeBlockTab
|
|
170
|
+
language="python"
|
|
171
|
+
file="get-authorization-with-connection-id-django"
|
|
172
|
+
title="Django"
|
|
173
|
+
/>
|
|
174
|
+
<CodeBlockTab
|
|
175
|
+
language="python"
|
|
176
|
+
file="get-authorization-with-connection-id-flask"
|
|
177
|
+
title="Flask"
|
|
178
|
+
/>
|
|
179
|
+
</CodeBlock>
|
|
180
|
+
|
|
181
|
+
- | Using provider
|
|
182
|
+
|
|
183
|
+
The provider parameter is used for OAuth connections which are configured at the environment level.
|
|
184
|
+
|
|
185
|
+
> The supported `provider` values are `GoogleOAuth`, `MicrosoftOAuth`, `GitHubOAuth`, and `AppleOAuth`.
|
|
186
|
+
|
|
187
|
+
<CodeBlock
|
|
188
|
+
title="Authentication Endpoint"
|
|
189
|
+
file="get-authorization-with-provider"
|
|
190
|
+
>
|
|
191
|
+
<CodeBlockTab
|
|
192
|
+
language="js"
|
|
193
|
+
file="get-authorization-with-provider-next"
|
|
194
|
+
title="Next.js"
|
|
195
|
+
/>
|
|
196
|
+
<CodeBlockTab
|
|
197
|
+
language="js"
|
|
198
|
+
file="get-authorization-with-provider-next-app-router"
|
|
199
|
+
title="Next.js (App Router)"
|
|
200
|
+
/>
|
|
201
|
+
<CodeBlockTab
|
|
202
|
+
language="js"
|
|
203
|
+
file="get-authorization-with-provider-express"
|
|
204
|
+
title="Express"
|
|
205
|
+
/>
|
|
206
|
+
<CodeBlockTab
|
|
207
|
+
language="ruby"
|
|
208
|
+
file="get-authorization-with-provider-rails"
|
|
209
|
+
title="Rails"
|
|
210
|
+
/>
|
|
211
|
+
<CodeBlockTab
|
|
212
|
+
language="ruby"
|
|
213
|
+
file="get-authorization-with-provider-sinatra"
|
|
214
|
+
title="Sinatra"
|
|
215
|
+
/>
|
|
216
|
+
<CodeBlockTab
|
|
217
|
+
language="python"
|
|
218
|
+
file="get-authorization-with-provider-django"
|
|
219
|
+
title="Django"
|
|
220
|
+
/>
|
|
221
|
+
<CodeBlockTab
|
|
222
|
+
language="python"
|
|
223
|
+
file="get-authorization-with-provider-flask"
|
|
224
|
+
title="Flask"
|
|
225
|
+
/>
|
|
226
|
+
</CodeBlock>
|
|
227
|
+
|
|
228
|
+
If there is an issue generating an authorization URL, WorkOS will return the redirect URI as is. Read the [API Reference](/reference/sso/get-authorization-url) for more details.
|
|
229
|
+
|
|
230
|
+
### Add a callback endpoint
|
|
231
|
+
|
|
232
|
+
Next, let’s add the redirect endpoint which will handle the callback from WorkOS after a user has authenticated with their identity provider. This endpoint should exchange the authorization code returned by WorkOS with the authenticated user’s profile. The authorization code is valid for 10 minutes.
|
|
233
|
+
|
|
234
|
+
<CodeBlock file="callback-endpoint" title="Callback Endpoint">
|
|
235
|
+
<CodeBlockTab language="js" file="callback-endpoint-next" title="Next.js" />
|
|
236
|
+
<CodeBlockTab
|
|
237
|
+
language="js"
|
|
238
|
+
file="callback-endpoint-next-app-router"
|
|
239
|
+
title="Next.js (App Router)"
|
|
240
|
+
/>
|
|
241
|
+
<CodeBlockTab
|
|
242
|
+
language="js"
|
|
243
|
+
file="callback-endpoint-express"
|
|
244
|
+
title="Express"
|
|
245
|
+
/>
|
|
246
|
+
<CodeBlockTab language="ruby" file="callback-endpoint-rails" title="Rails" />
|
|
247
|
+
<CodeBlockTab
|
|
248
|
+
language="ruby"
|
|
249
|
+
file="callback-endpoint-sinatra"
|
|
250
|
+
title="Sinatra"
|
|
251
|
+
/>
|
|
252
|
+
<CodeBlockTab
|
|
253
|
+
language="python"
|
|
254
|
+
file="callback-endpoint-django"
|
|
255
|
+
title="Django"
|
|
256
|
+
/>
|
|
257
|
+
<CodeBlockTab
|
|
258
|
+
language="python"
|
|
259
|
+
file="callback-endpoint-flask"
|
|
260
|
+
title="Flask"
|
|
261
|
+
/>
|
|
262
|
+
</CodeBlock>
|
|
263
|
+
|
|
264
|
+
When adding your callback endpoint, it is important to always validate the returned profile’s organization ID. It’s unsafe to validate using email domains as organizations might allow email addresses from outside their corporate domain (e.g. for guest users).
|
|
265
|
+
|
|
266
|
+
---
|
|
267
|
+
|
|
268
|
+
## (2) Configure a redirect URI
|
|
269
|
+
|
|
270
|
+
Go to the [Redirects](https://dashboard.workos.com/redirects) page in the dashboard to configure allowed redirect URIs. This is your callback endpoint you used in the previous section.
|
|
271
|
+
|
|
272
|
+
Multi-tenant apps will typically have a single redirect URI specified. You can set multiple redirect URIs for single-tenant apps. You’ll need to be sure to specify which redirect URI to use in the WorkOS client call to fetch the authorization URL.
|
|
273
|
+
|
|
274
|
+
> WorkOS staging environments allow wildcard characters in redirect URIs. More information about wildcard characters support can be found in the [Redirect URIs](/sso/redirect-uris/wildcard-characters) guide.
|
|
275
|
+
> Query parameters are not allowed in any environment.
|
|
276
|
+
|
|
277
|
+
|
|
278
|
+
|
|
279
|
+
### Identity provider-initiated SSO
|
|
280
|
+
|
|
281
|
+
Normally, the default redirect URI you configure in the WorkOS dashboard is going to be used for all identity provider-initiated SSO sessions. This is because the WorkOS client is not used to initiate the authentication flow.
|
|
282
|
+
|
|
283
|
+
However, your customer can specify a separate redirect URI to be used for all their IdP-initiated sessions as a `RelayState` parameter in the SAML settings on their side.
|
|
284
|
+
|
|
285
|
+
Learn more about configuring IdP-initiated SSO in the [Login Flows](/sso/login-flows/idp-initiated-sso/configure-idp-initiated-sso) guide.
|
|
286
|
+
|
|
287
|
+
---
|
|
288
|
+
|
|
289
|
+
## (3) Test end-to-end
|
|
290
|
+
|
|
291
|
+
If you followed this guide, you used the Test Organization available in your staging environment to initiate SSO. With that, you can already test your integration end-to-end.
|
|
292
|
+
|
|
293
|
+
|
|
294
|
+
|
|
295
|
+
Head to the _Test SSO_ page in the [WorkOS Dashboard](https://dashboard.workos.com/) to get started with testing common login flows, or read on about that in detail in the next guide.
|
|
@@ -0,0 +1,35 @@
|
|
|
1
|
+
---
|
|
2
|
+
title: FAQ for IT teams
|
|
3
|
+
description: Answers to common questions from your customer’s IT team.
|
|
4
|
+
originalPath: .tmp-workos-clone/packages/docs/content/sso/it-team-faq.mdx
|
|
5
|
+
---
|
|
6
|
+
|
|
7
|
+
## What is WorkOS?
|
|
8
|
+
|
|
9
|
+
WorkOS is a software company that provides a suite of products to make an app enterprise-ready. These products include Single Sign-On, Directory Sync, and User Management, among others.
|
|
10
|
+
|
|
11
|
+
Developers integrate WorkOS services into their apps in order to provide a secure authentication and user provisioning experience. It’s trusted by companies like Webflow, Plaid, Vercel, and many others.
|
|
12
|
+
|
|
13
|
+
## What data does WorkOS store?
|
|
14
|
+
|
|
15
|
+
For Single Sign-On, WorkOS stores the user profile from the identity provider. This includes the user's name, email and IP address.
|
|
16
|
+
|
|
17
|
+
For Directory Sync, WorkOS will store the data that the identity provider sends. The shape and content of that data is at the discretion of the identity provider.
|
|
18
|
+
|
|
19
|
+
For more information, view our [Privacy Policy](https://workos.com/legal/privacy)
|
|
20
|
+
|
|
21
|
+
## How do developer apps communicate with WorkOS?
|
|
22
|
+
|
|
23
|
+
Developers integrate with WorkOS using its Rest API and the related SDKs. You can find a list of all WorkOS API endpoints in the [API reference](/reference).
|
|
24
|
+
|
|
25
|
+
## What IP addresses does WorkOS use?
|
|
26
|
+
|
|
27
|
+
WorkOS uses Cloudflare to ensure security and reliability of all operations. If you are looking to create a list of allowed IP addresses for the WorkOS API, you can use the IP ranges listed in the [Cloudflare documentation](https://www.cloudflare.com/ips/).
|
|
28
|
+
|
|
29
|
+
## Is WorkOS certified for SOC 2 Type II, SOC 3 and SIG Lite?
|
|
30
|
+
|
|
31
|
+
Yes, WorkOS is compliant with all the above and regularly undergoes penetration testing.
|
|
32
|
+
|
|
33
|
+
## Is WorkOS GDPR compliant?
|
|
34
|
+
|
|
35
|
+
Yes, WorkOS is GDPR compliant. Reach out to [support](mailto:support@workos.com) to request deletion of data.
|
|
@@ -0,0 +1,101 @@
|
|
|
1
|
+
---
|
|
2
|
+
title: Just-In-Time User Provisioning
|
|
3
|
+
description: Learn how to provision users in your app using Just-In-Time user provisioning.
|
|
4
|
+
originalPath: .tmp-workos-clone/packages/docs/content/sso/jit-provisioning.mdx
|
|
5
|
+
---
|
|
6
|
+
|
|
7
|
+
## Introduction
|
|
8
|
+
|
|
9
|
+
User provisioning is the process of creating a user account and associated identity information. There are various ways for an application to provision users. This guide explores user provisioning strategies and offers a deep dive into SSO-based just-in-time (JIT) user provisioning.
|
|
10
|
+
|
|
11
|
+
## Definitions
|
|
12
|
+
|
|
13
|
+
**User provisioning**
|
|
14
|
+
: Provisioning is the process of creating a user and setting attributes for them inside an app.
|
|
15
|
+
|
|
16
|
+
**JIT user provisioning**
|
|
17
|
+
: Just-in-time user provisioning creates a user in an app when the user attempts to sign in for the first time. The account and respective role don’t exist until the app creates them – just-in-time.
|
|
18
|
+
|
|
19
|
+
**Identity**
|
|
20
|
+
: An identity is a collection of attributes associated with a user or entity in an identity provider. For example, an identity includes at least one unique identifier, such as id, and user profile attributes, such as name and email.
|
|
21
|
+
|
|
22
|
+
**Role**
|
|
23
|
+
: A primitive in your app that defines specific permissions for the users. Roles are often defined as an ability or a job title, for example, “Editor” or “Accountant”.
|
|
24
|
+
|
|
25
|
+
## User provisioning strategies
|
|
26
|
+
|
|
27
|
+
User provisioning is the process of creating a user account with associated identity data in your app. Your app needs to determine a unique identifier for an identity, create a unique account for that user, and link the identity profile attributes to that user’s account. There are many strategies to provision users in an app, but the main three are:
|
|
28
|
+
|
|
29
|
+
1. Self-registration
|
|
30
|
+
2. Provisioning users via [Directory Sync](/directory-sync)
|
|
31
|
+
3. JIT provisioning via SSO
|
|
32
|
+
|
|
33
|
+
The type of provisioning needed will depend on your app’s architecture and level of enterprise feature support:
|
|
34
|
+
|
|
35
|
+
| Strategy | Description | Usage |
|
|
36
|
+
| ---------------------- | --------------------------------------------------------------------- | ---------------------------------------------------------------------------------------------------- |
|
|
37
|
+
| Self-registration | Users fill out a registration form to create an account in the app | For users that don’t have an SSO service, usually the first authentication mechanism built in an app |
|
|
38
|
+
| Pre-provisioning users | Use a service like Directory Sync to create users in the app | Required by large enterprises to automatically provision users |
|
|
39
|
+
| JIT provisioning | Create a user account when a user signs in via SSO for the first time | Leverage user identity from an SSO provider to create an account in your app |
|
|
40
|
+
|
|
41
|
+
## What is JIT provisioning?
|
|
42
|
+
|
|
43
|
+
JIT provisioning creates a user account with associated identity information when a user authenticates via SSO for the first time. IT admins often use JIT provisioning to quickly set up accounts in an app. Typically, apps that implement only SSO will have JIT provisioning support as the alternative is self-registration by individual users or manual entry of all users by the IT admin.
|
|
44
|
+
|
|
45
|
+
### Sample scenario
|
|
46
|
+
|
|
47
|
+
Consider the fictional SaaS company _HireOS_, which offers recruiting software to other businesses. _HireOS_ is an online app allowing customers to track leads, candidates, and interviews.
|
|
48
|
+
|
|
49
|
+
_HireOS_ has integrated SSO using WorkOS and supports JIT provisioning. For example, a _HireOS_ customer would like their users to have accounts automatically provisioned in _HireOS_ when they first log in. The customer’s IT admin will only need to assign the users to the _HireOS_ SAML app in their identity provider. When users log into _HireOS_ via SSO, they will have accounts created in _HireOS_, just in time.
|
|
50
|
+
|
|
51
|
+
A usual account setup flow using JIT provisioning follows these steps:
|
|
52
|
+
|
|
53
|
+
1. An IT admin self-registers via username and password to create a team account in _HireOS_.
|
|
54
|
+
2. The IT admin configures the _HireOS_ team account to use SSO as the authentication mechanism.
|
|
55
|
+
3. The IT admin enables JIT provisioning for this team account by clicking the "Enable JIT Provisioning" checkbox.
|
|
56
|
+
4. The IT admin adds the users that should get access to _HireOS_ to the app in the identity provider.
|
|
57
|
+
5. When a user logs into _HireOS_ with the correct email domain and authenticates via SSO, _HireOS_ creates the user account upon successful first-time login.
|
|
58
|
+
|
|
59
|
+
## JIT provisioning with WorkOS SSO
|
|
60
|
+
|
|
61
|
+
When a user authenticates to your app via SSO for the first time, and JIT provisioning is enabled, your app provisions a new user account. You can create the account by saving the identity information (the WorkOS SSO profile) directly on your app's user account. Or, you can create a separate identity from the WorkOS SSO profile related to this new user account. This logic allows users to have multiple identities if your app supports several login methods per user.
|
|
62
|
+
|
|
63
|
+
You can use the WorkOS SSO profile `id` attribute as the unique identifier for this identity from WorkOS. WorkOS ensures the profile is unique per SSO connection via the `idp_id`. In addition, your app can use either the `connection_id` or `organization_id` to tie the identity to a team account.
|
|
64
|
+
|
|
65
|
+
```json language="json" title="SSO user profile"
|
|
66
|
+
{
|
|
67
|
+
"object": "profile",
|
|
68
|
+
"id": "prof_01DMC79VCBZ0NY2099737PSVF1",
|
|
69
|
+
"connection_id": "conn_01E4ZCR3C56J083X43JQXF3JK5",
|
|
70
|
+
"connection_type": "OktaSAML",
|
|
71
|
+
"organization_id": "org_01EHWNCE74X7JSDV0X3SZ3KJNY",
|
|
72
|
+
"email": "todd@example.com",
|
|
73
|
+
"first_name": "Todd",
|
|
74
|
+
"last_name": "Rundgren",
|
|
75
|
+
"idp_id": "00u1a0ufowBJlzPlk357",
|
|
76
|
+
"role": {
|
|
77
|
+
"slug": "admin"
|
|
78
|
+
},
|
|
79
|
+
"raw_attributes": {}
|
|
80
|
+
}
|
|
81
|
+
```
|
|
82
|
+
|
|
83
|
+
You may want to grant new users roles in your application via JIT provisioning. For more information on mapping role data between the IdP and your app, see the [Mapping Roles](/sso/identity-provider-role-assignment) guide.
|
|
84
|
+
|
|
85
|
+
### New account creation
|
|
86
|
+
|
|
87
|
+
When your app receives a WorkOS SSO profile, it is standard to perform the following series of checks:
|
|
88
|
+
|
|
89
|
+
1. Find an identity with the profile `id` or `idp_id`. If found, log in the corresponding user.
|
|
90
|
+
2. If you cannot find an identity, try to find a user with the same `email` as the profile. If found, create an identity for the user and log them in.
|
|
91
|
+
3. Otherwise, create a new identity using the WorkOS SSO profile, create a new user, and associate this identity with the user account.
|
|
92
|
+
|
|
93
|
+
### Linking an existing user
|
|
94
|
+
|
|
95
|
+
If an admin adds SSO authentication to their team account after they've had users register, your app can link these new SSO identities to the current user accounts, just-in-time.
|
|
96
|
+
|
|
97
|
+
A linking field (e.g. `email`) should be established to find a current user with the incoming WorkOS SSO Profile. Then, the identity information can be linked with the existing user account via a persistent identifier in case of an email change later.
|
|
98
|
+
|
|
99
|
+
## Implementing SSO with WorkOS
|
|
100
|
+
|
|
101
|
+
This document offers guidance to integrate Single Sign-On with our standalone API into your existing auth stack. You might also want to look at [User Management](/user-management), a complete authentication platform that leverages Single Sign-On functionality out of the box, following best practices.
|
|
@@ -0,0 +1,71 @@
|
|
|
1
|
+
---
|
|
2
|
+
title: Launch Checklist
|
|
3
|
+
description: Make sure you’re ready to take your app to production.
|
|
4
|
+
originalPath: .tmp-workos-clone/packages/docs/content/sso/launch-checklist.mdx
|
|
5
|
+
---
|
|
6
|
+
|
|
7
|
+
## Implement complementary enterprise features
|
|
8
|
+
|
|
9
|
+
- Integrate the WorkOS [Admin Portal](/admin-portal) to enable your users to onboard and set up SSO themselves.
|
|
10
|
+
- Integrate the WorkOS Directory Sync API for automatic user updating, provisioning, and deprovisioning.
|
|
11
|
+
|
|
12
|
+
### Before you start
|
|
13
|
+
|
|
14
|
+
This document offers guidance to integrate Single Sign-On with our standalone API into your existing auth stack. You might also want to look at [User Management](/user-management), a complete authentication platform that leverages Single Sign-On functionality out of the box, following best practices.
|
|
15
|
+
|
|
16
|
+
## Create an IP Allowlist
|
|
17
|
+
|
|
18
|
+
WorkOS makes use of Cloudflare to ensure security and reliability of all operations. If you are looking to create a list of allowed IP addresses for redirect requests, you can use the IP Ranges listed in the [Cloudflare documentation](https://www.cloudflare.com/ips/).
|
|
19
|
+
|
|
20
|
+
## Go-live checklist
|
|
21
|
+
|
|
22
|
+
- [ ] Implement an SSO UI/UX. See our guide for ideas – [UI/UX Best Practices for IdP & SP-Initiated SSO](https://workos.com/blog/ui-ux-best-practices-for-idp-and-sp-initiated-sso)
|
|
23
|
+
- [ ] [Test the end-to-end SSO](/sso/test-sso) experience in your Staging environment.
|
|
24
|
+
- [ ] Unlock your Production environment by adding your billing information
|
|
25
|
+
> Only enterprise connections in your Production environment will be charged. OAuth connections in Production will be free.
|
|
26
|
+
- [ ] Set your Production Client’s ID and API Key as environment variables
|
|
27
|
+
- [ ] Secure your Production Project’s API key
|
|
28
|
+
- [ ] Configure production redirect URI(s) in your Product Project. Verify the default redirect URI is correct
|
|
29
|
+
- [ ] Ensure that your application can receive redirects from WorkOS.
|
|
30
|
+
Depending on your network architecture, you may need to allowlist incoming redirect traffic from `api.workos.com`.
|
|
31
|
+
- [ ] Add Connections for your customers in the Production Environment
|
|
32
|
+
|
|
33
|
+
## Frequently asked questions
|
|
34
|
+
|
|
35
|
+
### How should an application handle the first time a user authenticates using WorkOS?
|
|
36
|
+
|
|
37
|
+
If a user is authenticating to your application for the first time via SSO and doesn’t have an account, you can implement just-in-time provisioning to create a user when authentication is complete.
|
|
38
|
+
|
|
39
|
+
You can also leverage [Directory Sync](/directory-sync) to pre-provision users with API endpoints or webhooks. In this case, the user will already be created in your application when they authenticate for the first time.
|
|
40
|
+
|
|
41
|
+
### Can we add SSO authentication for a current user in an application?
|
|
42
|
+
|
|
43
|
+
If a user is authenticating to your application via SSO, but already has an account (with username/password for example), you can “upgrade” them to SSO. Usually the emails are the same for both methods of authentication, so you can match on email address. Once SSO via WorkOS is enabled, you can restrict users to sign in with only SSO.
|
|
44
|
+
|
|
45
|
+
### How does WorkOS manage user attributes from an identity provider?
|
|
46
|
+
|
|
47
|
+
WorkOS normalizes user attributes so you can expect known values such as `id`, `email`,`firstName`, and `lastName`.
|
|
48
|
+
|
|
49
|
+
### Is the user attribute mapping configurable in WorkOS?
|
|
50
|
+
|
|
51
|
+
Yes. For example, let’s say the `http://schemas.xmlsoap.org/ws/2005/05/identity/claims/surname` attribute contains the user email rather than the `surname` as the attribute name suggests. In these edge cases, WorkOS will identify any attributes that are misconfigured and recommend correct mapping in the “Attribute Mapper“ section of the “Connection info” page.
|
|
52
|
+
|
|
53
|
+
### What does the “Allow Profiles Outside Organization” option do?
|
|
54
|
+
|
|
55
|
+
By default, WorkOS restricts user profiles for SAML Connections to profiles that have email domains that are in the set of [User Email Domains](/reference/organization-domain) on the Organization.
|
|
56
|
+
|
|
57
|
+
Enabling this option removes this restriction and allows user profiles with any email address to sign in through Connections under this Organization.
|
|
58
|
+
|
|
59
|
+
If this option is enabled, your code can not exclusively trust the returned `email` attribute on user profiles to be a verified email address. Instead, you must use the `organization_id` or `connection_id` in order to verify that the profile belongs to whom it claims.
|
|
60
|
+
|
|
61
|
+
### What does “There are 0 profiles awaiting reconciliation” refer to?
|
|
62
|
+
|
|
63
|
+
This refers to the number of user profiles that have inconsistent attribute mappings, and that need to be updated in order to successfully authenticate.
|
|
64
|
+
|
|
65
|
+
### How do I integrate WorkOS SSO with my native mobile application?
|
|
66
|
+
|
|
67
|
+
When it comes to mobile applications, our typical advice in implementing SSO authentication goes like this:
|
|
68
|
+
|
|
69
|
+
1. Generate the authentication URL and route the user to a browser or browser fragment in order to authenticate.
|
|
70
|
+
2. The end user authenticates via the native UI of their IdP within that browser.
|
|
71
|
+
3. Upon successful authentication, deep-link the user back into your native application.
|
|
@@ -0,0 +1,101 @@
|
|
|
1
|
+
---
|
|
2
|
+
title: Login Flows
|
|
3
|
+
description: "Learn the differences between SP‑initiated and IdP‑initiated\_SSO."
|
|
4
|
+
originalPath: .tmp-workos-clone/packages/docs/content/sso/login-flows.mdx
|
|
5
|
+
---
|
|
6
|
+
|
|
7
|
+
The instructions in the [Quick Start guide](/sso) focus on setting up Service Provider (SP)-initiated SSO. In these scenarios, when a user attempts to login, they navigate to an application (a service provider) and are then redirected to the [Identity Provider (IdP)](/glossary/idp) for authentication, via the WorkOS API.
|
|
8
|
+
|
|
9
|
+
Alternatively, most users are able to start the process from the Identity Provider itself. Organizations will often provide an IdP dashboard where employees can select any of the eligible applications that they can access via the IdP, similar to the screenshot below. Clicking on a tile results in an IdP-initiated login flow, since the user initiates the login from the Identity Provider, not the application.
|
|
10
|
+
|
|
11
|
+
|
|
12
|
+
|
|
13
|
+
---
|
|
14
|
+
|
|
15
|
+
## SP-initiated SSO
|
|
16
|
+
|
|
17
|
+
With an SP-initiated login flow, the user begins the authentication process from your application. You can control where the user will be redirected after login by specifying the `redirectURI` parameter when making the [Get Authorization URL](/reference/sso/get-authorization-url) call. Additionally, this call can take an optional `state` parameter - this parameter will be returned in the callback after authentication, where your application can use it to verify the validity of the response or to pass any state from the originating session. One common practice is to route requests from different Organizations to a single Redirect URI, but instead utilize the `state` parameter to deep link users into the application after the authentication is completed.
|
|
18
|
+
|
|
19
|
+
<CodeBlock file="get-authorization-url" title="Get Authorization URL Call" />
|
|
20
|
+
|
|
21
|
+
---
|
|
22
|
+
|
|
23
|
+
## IdP-initiated SSO
|
|
24
|
+
|
|
25
|
+
If you follow the instructions in the [Quick Start guide](/sso), IdP-initiated login flows will automatically be available, and users will be able to find a tile for your application within their IdP, similar to the screenshot above. Clicking on the tile will send an IdP-initiated SSO response to your application's callback endpoint.
|
|
26
|
+
|
|
27
|
+
### Configure IdP-initiated SSO
|
|
28
|
+
|
|
29
|
+
Additionally, since IdP-initiated flows do not generate a customized authorization URL the way SP-initiated flows do, there is no way to dynamically pass the `redirectURI` and `state` parameters to your application's callback. By default, users will be redirected to the default Redirect URI upon a successful login. However, IdP Administrators can customize the redirect destination by configuring a default `RelayState` in the IdP, and including a `redirect_uri` parameter in it. The URI must be specified in the format of a URL parameter: `redirect_uri=uri`, and the URI must be one of the Redirect URIs specified in your WorkOS [Dashboard](https://dashboard.workos.com). Any other values in the IdP’s `RelayState` will be ignored and discarded.
|
|
30
|
+
|
|
31
|
+
Your application will also be able to retrieve the [Profile object](/reference/sso/profile) for the user upon successful authentication. If your IdP is unable to provide a `redirect_uri` in its default `RelayState`, or if you would like to generate a custom redirect URI for each user after they sign in, you can use the [Profile object](/reference/sso/profile) to dynamically generate a redirect URI.
|
|
32
|
+
|
|
33
|
+
```json title="Example Profile"
|
|
34
|
+
{
|
|
35
|
+
"id": "prof_01DMC79VCBZ0NY2099737PSVF1",
|
|
36
|
+
"connection_id": "conn_01E4ZCR3C56J083X43JQXF3JK5",
|
|
37
|
+
"connection_type": "okta",
|
|
38
|
+
"email": "todd@example.com",
|
|
39
|
+
"first_name": "Todd",
|
|
40
|
+
"idp_id": "00u1a0ufowBJlzPlk357",
|
|
41
|
+
"last_name": "Rundgren",
|
|
42
|
+
"object": "profile",
|
|
43
|
+
"raw_attributes": {}
|
|
44
|
+
}
|
|
45
|
+
```
|
|
46
|
+
|
|
47
|
+
The Profile object includes the `connection_id` which identifies the connection that the profile is associated with in WorkOS. We recommend using the connection information for routing requests in an IdP-Initiated flow.
|
|
48
|
+
|
|
49
|
+
### Disable IdP-initiated SSO (Beta)
|
|
50
|
+
|
|
51
|
+
We have recently added Beta support for fully disabling IdP-initiated SSO logins for a connection. Once disabled, any attempted IdP-initiated requests will fail with an `idp_initiated_sso_disabled` error.
|
|
52
|
+
|
|
53
|
+
> Disabling IdP-initiated SSO is currently in invite-only beta, please reach out to [WorkOS support](mailto:support@workos.com) if you’d like to use it or learn more about it.
|
|
54
|
+
|
|
55
|
+
For applications that need to support IdP-initiated workflows, but would like to mitigate the security risks of unsolicited SAML responses, WorkOS recommends the following:
|
|
56
|
+
|
|
57
|
+
- Disable IdP-initiated SSO for your connection.
|
|
58
|
+
- Adjust your callback method to capture the `idp_initiated_sso_disabled` error.
|
|
59
|
+
- Start a new SP-initiated request from the callback when the error is detected.
|
|
60
|
+
|
|
61
|
+
The error callback will include the connection and organization ID’s, which can be used to request a new authorization URL for the SP-initiated request. The new request will generally be transparent to the user, as they are already logged in to the Identity Provider.
|
|
62
|
+
|
|
63
|
+
<CodeBlock
|
|
64
|
+
file="callback-endpoint-idp-initiated"
|
|
65
|
+
title="Callback Endpoint with IdP-Initiated error support"
|
|
66
|
+
>
|
|
67
|
+
<CodeBlockTab
|
|
68
|
+
language="js"
|
|
69
|
+
file="callback-endpoint-idp-initiated-next"
|
|
70
|
+
title="Next.js"
|
|
71
|
+
/>
|
|
72
|
+
<CodeBlockTab
|
|
73
|
+
language="js"
|
|
74
|
+
file="callback-endpoint-idp-initiated-express"
|
|
75
|
+
title="Express"
|
|
76
|
+
/>
|
|
77
|
+
<CodeBlockTab
|
|
78
|
+
language="ruby"
|
|
79
|
+
file="callback-endpoint-idp-initiated-rails"
|
|
80
|
+
title="Rails"
|
|
81
|
+
/>
|
|
82
|
+
<CodeBlockTab
|
|
83
|
+
language="ruby"
|
|
84
|
+
file="callback-endpoint-idp-initiated-sinatra"
|
|
85
|
+
title="Sinatra"
|
|
86
|
+
/>
|
|
87
|
+
<CodeBlockTab
|
|
88
|
+
language="python"
|
|
89
|
+
file="callback-endpoint-idp-initiated-django"
|
|
90
|
+
title="Django"
|
|
91
|
+
/>
|
|
92
|
+
<CodeBlockTab
|
|
93
|
+
language="python"
|
|
94
|
+
file="callback-endpoint-idp-initiated-flask"
|
|
95
|
+
title="Flask"
|
|
96
|
+
/>
|
|
97
|
+
</CodeBlock>
|
|
98
|
+
|
|
99
|
+
## Implementing SSO with WorkOS
|
|
100
|
+
|
|
101
|
+
This document offers guidance to integrate Single Sign-On with our standalone API into your existing auth stack. You might also want to look at [User Management](/user-management), a complete authentication platform that leverages Single Sign-On functionality out of the box, following best practices.
|
|
@@ -0,0 +1,44 @@
|
|
|
1
|
+
---
|
|
2
|
+
title: Redirect URIs
|
|
3
|
+
description: >-
|
|
4
|
+
Learn what a redirect URI is and how it relates to Service Provider and
|
|
5
|
+
Identity Provider initiated login flows.
|
|
6
|
+
originalPath: .tmp-workos-clone/packages/docs/content/sso/redirect-uris.mdx
|
|
7
|
+
---
|
|
8
|
+
|
|
9
|
+
## Introduction
|
|
10
|
+
|
|
11
|
+
With a [WorkOS Service Provider (SP) initiated login flow](/sso), there are a series of exchanges that take place between a Service Provider (your application), WorkOS, and the IdP that’s being used to authenticate the user as shown in the diagram below. The [Redirect URI](/glossary/redirect-uri) is the location to which the user gets returned to after successfully completing the authentication with their [Identity Provider (IdP)](/glossary/idp).
|
|
12
|
+
|
|
13
|
+
With an Identity Provider (IdP) initiated login flow, the approach is similar but the user will begin the login flow by clicking on the tile within their IdP platform instead of from your application.
|
|
14
|
+
|
|
15
|
+
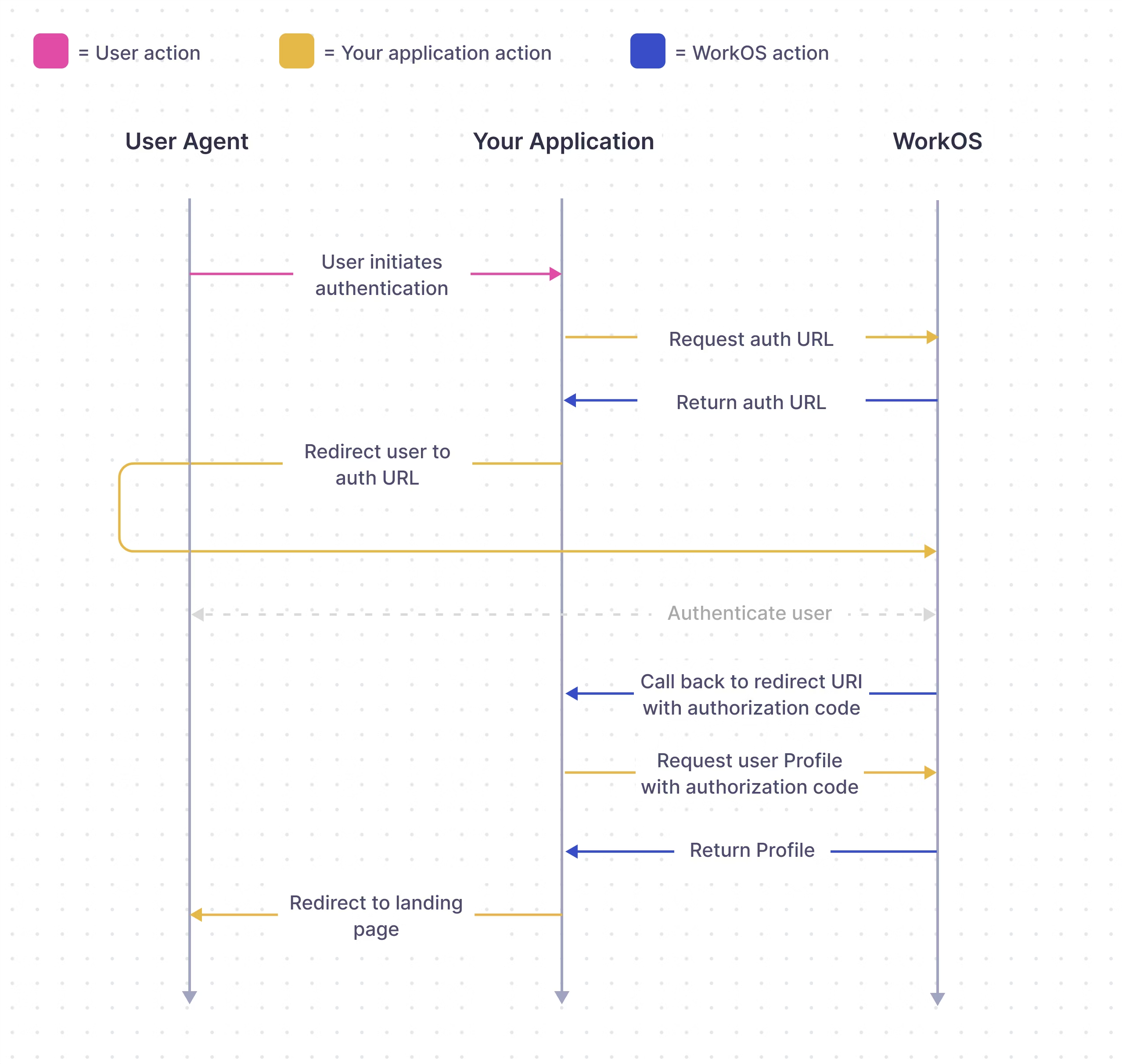
|
|
16
|
+
|
|
17
|
+
In WorkOS Production Environments, the Redirect URI to your application cannot use HTTP or localhost, however, Redirect URIs that use HTTP and localhost are allowed in Sandbox Environments.
|
|
18
|
+
|
|
19
|
+
There should be at least one redirect URI configured and selected as a default for a WorkOS Environment. This can be done from the [Redirects](https://dashboard.workos.com/redirects) page in the WorkOS dashboard. If you try to route the authorization flow to a Redirect URI that is not yet defined in the Dashboard it will result in an error and users will be unable to sign in, so it’s important to define them in the dashboard first.
|
|
20
|
+
|
|
21
|
+
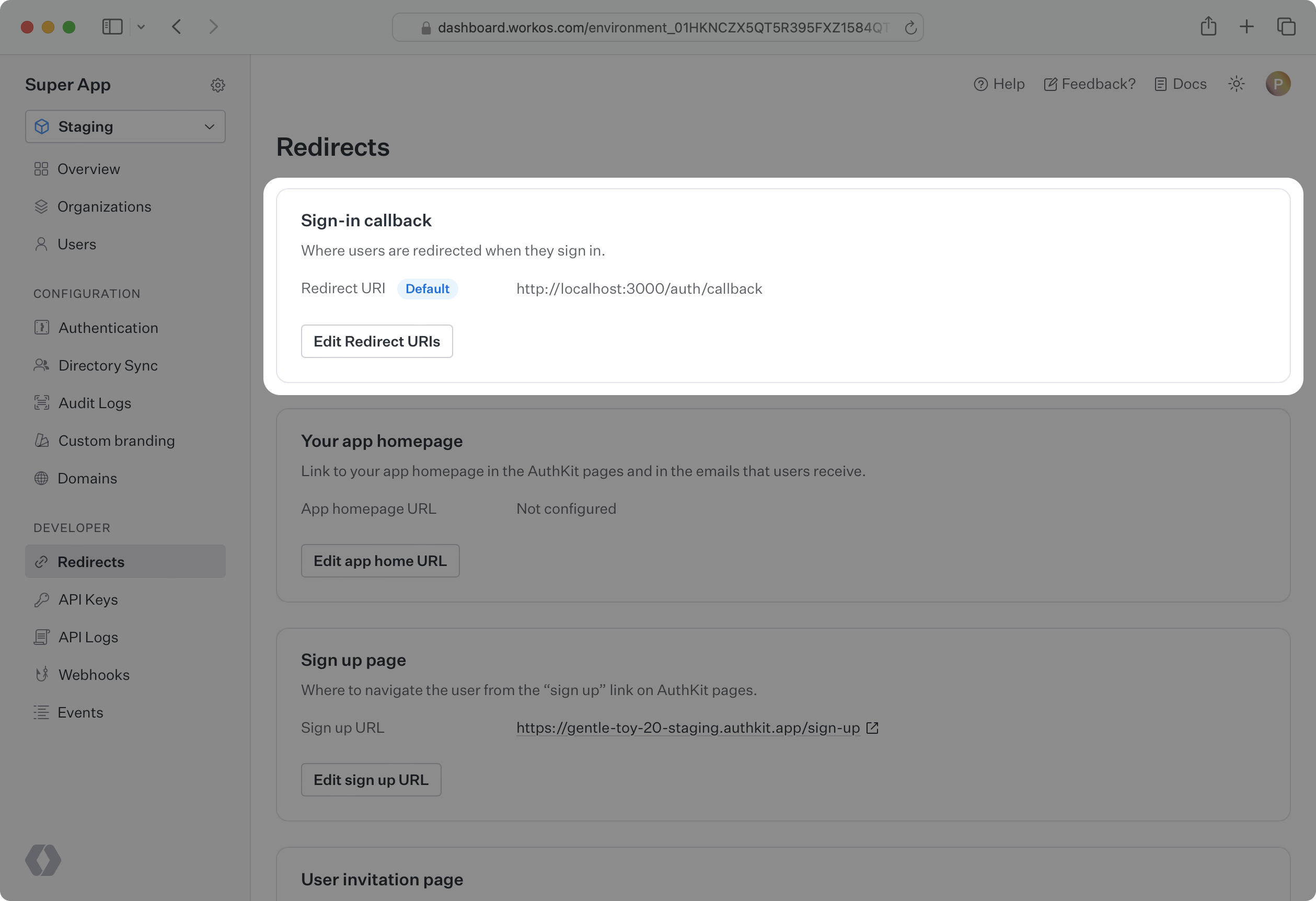
|
|
22
|
+
|
|
23
|
+
The Redirect URI can also be included directly in the Get Authorization URL call as a redirect_uri parameter. When the Redirect URI is set in this fashion, it will override the default Redirect URI that is set in the WorkOS Dashboard.
|
|
24
|
+
|
|
25
|
+
---
|
|
26
|
+
|
|
27
|
+
## Wildcard characters
|
|
28
|
+
|
|
29
|
+
WorkOS supports using wildcard characters in Redirect URIs for staging environments.
|
|
30
|
+
|
|
31
|
+
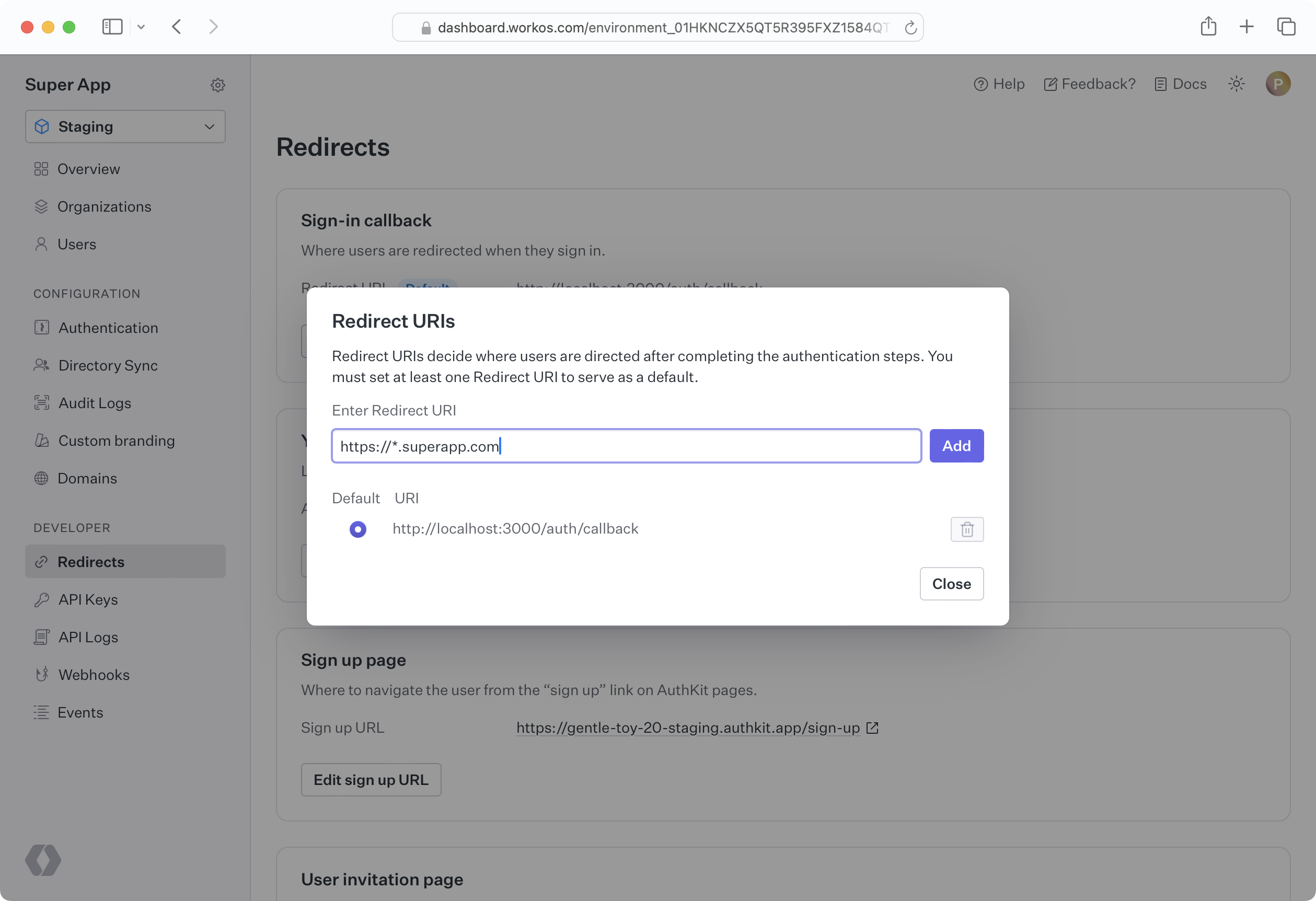
|
|
32
|
+
|
|
33
|
+
The `*` symbol can be used as a wildcard for subdomains; however, it must be used in accordance with the following rules in order to properly function.
|
|
34
|
+
|
|
35
|
+
- The protocol of the URL **must not** be `http:` in Production Environments.
|
|
36
|
+
- The wildcard **must** be located in a subdomain within the hostname component. For example, `http://*.com` will not work.
|
|
37
|
+
- The wildcard **must** be located in the subdomain which is furthest from the root domain. For example, `https://sub.*.example.com` will not work.
|
|
38
|
+
- The URL **must not** contain more than one wildcard. For example, `https://*.*.example.com` will not work.
|
|
39
|
+
- A wildcard character **may** be prefixed and/or suffixed with additional valid hostname characters. For example, `https://prefix-*-suffix.example.com` will work.
|
|
40
|
+
- A URL with a valid wildcard **will not** match a URL more than one subdomain level in place of the wildcard. For example, `https://*.example.com` will not work with `https://sub1.sub2.example.com`.
|
|
41
|
+
|
|
42
|
+
## Implementing SSO with WorkOS
|
|
43
|
+
|
|
44
|
+
This document offers guidance to integrate Single Sign-On with our standalone API into your existing auth stack. You might also want to look at [User Management](/user-management), a complete authentication platform that leverages Single Sign-On functionality out of the box, following best practices.
|