@workos/mcp-docs-server 0.1.0
This diff represents the content of publicly available package versions that have been released to one of the supported registries. The information contained in this diff is provided for informational purposes only and reflects changes between package versions as they appear in their respective public registries.
- package/.docs/organized/changelogs/workos-platform.json +277 -0
- package/.docs/organized/docs/admin-portal/_navigation.mdx +16 -0
- package/.docs/organized/docs/admin-portal/custom-branding.mdx +111 -0
- package/.docs/organized/docs/admin-portal/example-apps.mdx +46 -0
- package/.docs/organized/docs/admin-portal/index.mdx +240 -0
- package/.docs/organized/docs/audit-logs/_navigation.mdx +22 -0
- package/.docs/organized/docs/audit-logs/admin-portal.mdx +20 -0
- package/.docs/organized/docs/audit-logs/editing-events.mdx +27 -0
- package/.docs/organized/docs/audit-logs/exporting-events.mdx +29 -0
- package/.docs/organized/docs/audit-logs/index.mdx +110 -0
- package/.docs/organized/docs/audit-logs/log-streams.mdx +56 -0
- package/.docs/organized/docs/audit-logs/metadata-schema.mdx +21 -0
- package/.docs/organized/docs/custom-domains/_navigation.mdx +16 -0
- package/.docs/organized/docs/custom-domains/admin-portal.mdx +38 -0
- package/.docs/organized/docs/custom-domains/auth-api.mdx +59 -0
- package/.docs/organized/docs/custom-domains/authkit.mdx +36 -0
- package/.docs/organized/docs/custom-domains/email.mdx +41 -0
- package/.docs/organized/docs/custom-domains/index.mdx +19 -0
- package/.docs/organized/docs/dashboard.mdx +244 -0
- package/.docs/organized/docs/demo/_navigation.mdx +26 -0
- package/.docs/organized/docs/demo/accordion.mdx +34 -0
- package/.docs/organized/docs/demo/checklist.mdx +33 -0
- package/.docs/organized/docs/demo/code-block.mdx +185 -0
- package/.docs/organized/docs/demo/definition-list.mdx +35 -0
- package/.docs/organized/docs/demo/index.mdx +7 -0
- package/.docs/organized/docs/demo/punctuation.mdx +37 -0
- package/.docs/organized/docs/demo/replacements.mdx +26 -0
- package/.docs/organized/docs/demo/table.mdx +26 -0
- package/.docs/organized/docs/demo/tabs.mdx +17 -0
- package/.docs/organized/docs/directory-sync/_navigation.mdx +28 -0
- package/.docs/organized/docs/directory-sync/attributes.mdx +209 -0
- package/.docs/organized/docs/directory-sync/example-apps.mdx +46 -0
- package/.docs/organized/docs/directory-sync/handle-inactive-users.mdx +52 -0
- package/.docs/organized/docs/directory-sync/identity-provider-role-assignment.mdx +134 -0
- package/.docs/organized/docs/directory-sync/index.mdx +107 -0
- package/.docs/organized/docs/directory-sync/quick-start.mdx +129 -0
- package/.docs/organized/docs/directory-sync/understanding-events.mdx +209 -0
- package/.docs/organized/docs/domain-verification/_navigation.mdx +10 -0
- package/.docs/organized/docs/domain-verification/api.mdx +60 -0
- package/.docs/organized/docs/domain-verification/index.mdx +67 -0
- package/.docs/organized/docs/email.mdx +109 -0
- package/.docs/organized/docs/events/_navigation.mdx +22 -0
- package/.docs/organized/docs/events/data-syncing/data-reconciliation.mdx +56 -0
- package/.docs/organized/docs/events/data-syncing/events-api.mdx +114 -0
- package/.docs/organized/docs/events/data-syncing/index.mdx +66 -0
- package/.docs/organized/docs/events/data-syncing/webhooks.mdx +173 -0
- package/.docs/organized/docs/events/index.mdx +783 -0
- package/.docs/organized/docs/events/observability/datadog.mdx +76 -0
- package/.docs/organized/docs/fga/_navigation.mdx +64 -0
- package/.docs/organized/docs/fga/identity-provider-sessions.mdx +68 -0
- package/.docs/organized/docs/fga/index.mdx +60 -0
- package/.docs/organized/docs/fga/local-development.mdx +155 -0
- package/.docs/organized/docs/fga/modeling/abac.mdx +107 -0
- package/.docs/organized/docs/fga/modeling/blocklist.mdx +84 -0
- package/.docs/organized/docs/fga/modeling/conditional-roles.mdx +99 -0
- package/.docs/organized/docs/fga/modeling/custom-roles.mdx +90 -0
- package/.docs/organized/docs/fga/modeling/entitlements.mdx +127 -0
- package/.docs/organized/docs/fga/modeling/managed-service-provider.mdx +131 -0
- package/.docs/organized/docs/fga/modeling/org-roles-and-permissions.mdx +95 -0
- package/.docs/organized/docs/fga/modeling/policy-context.mdx +231 -0
- package/.docs/organized/docs/fga/modeling/public-access.mdx +61 -0
- package/.docs/organized/docs/fga/modeling/shareable-content.mdx +106 -0
- package/.docs/organized/docs/fga/modeling/superusers.mdx +74 -0
- package/.docs/organized/docs/fga/modeling/user-groups.mdx +92 -0
- package/.docs/organized/docs/fga/operations-usage.mdx +104 -0
- package/.docs/organized/docs/fga/playground.mdx +12 -0
- package/.docs/organized/docs/fga/policies.mdx +462 -0
- package/.docs/organized/docs/fga/query-language.mdx +112 -0
- package/.docs/organized/docs/fga/quick-start.mdx +174 -0
- package/.docs/organized/docs/fga/resources.mdx +92 -0
- package/.docs/organized/docs/fga/schema-management.mdx +224 -0
- package/.docs/organized/docs/fga/schema.mdx +388 -0
- package/.docs/organized/docs/fga/warrant-tokens.mdx +44 -0
- package/.docs/organized/docs/fga/warrants.mdx +92 -0
- package/.docs/organized/docs/glossary.mdx +184 -0
- package/.docs/organized/docs/integrations/_navigation.mdx +6 -0
- package/.docs/organized/docs/integrations/access-people-hr.mdx +87 -0
- package/.docs/organized/docs/integrations/adp-oidc.mdx +103 -0
- package/.docs/organized/docs/integrations/apple.mdx +169 -0
- package/.docs/organized/docs/integrations/auth0-directory-sync.mdx +78 -0
- package/.docs/organized/docs/integrations/auth0-enterprise-connection.mdx +92 -0
- package/.docs/organized/docs/integrations/auth0-saml.mdx +81 -0
- package/.docs/organized/docs/integrations/aws-cognito.mdx +81 -0
- package/.docs/organized/docs/integrations/bamboohr.mdx +90 -0
- package/.docs/organized/docs/integrations/breathe-hr.mdx +89 -0
- package/.docs/organized/docs/integrations/bubble.mdx +129 -0
- package/.docs/organized/docs/integrations/cas-saml.mdx +65 -0
- package/.docs/organized/docs/integrations/cezanne.mdx +74 -0
- package/.docs/organized/docs/integrations/classlink-saml.mdx +100 -0
- package/.docs/organized/docs/integrations/cloudflare-saml.mdx +164 -0
- package/.docs/organized/docs/integrations/cyberark-saml.mdx +138 -0
- package/.docs/organized/docs/integrations/cyberark-scim.mdx +100 -0
- package/.docs/organized/docs/integrations/duo-saml.mdx +127 -0
- package/.docs/organized/docs/integrations/entra-id-saml.mdx +156 -0
- package/.docs/organized/docs/integrations/entra-id-scim.mdx +218 -0
- package/.docs/organized/docs/integrations/firebase.mdx +98 -0
- package/.docs/organized/docs/integrations/fourth.mdx +66 -0
- package/.docs/organized/docs/integrations/github-oauth.mdx +85 -0
- package/.docs/organized/docs/integrations/gitlab-oauth.mdx +81 -0
- package/.docs/organized/docs/integrations/google-directory-sync.mdx +86 -0
- package/.docs/organized/docs/integrations/google-oauth.mdx +173 -0
- package/.docs/organized/docs/integrations/google-saml.mdx +135 -0
- package/.docs/organized/docs/integrations/hibob.mdx +98 -0
- package/.docs/organized/docs/integrations/jumpcloud-saml.mdx +96 -0
- package/.docs/organized/docs/integrations/jumpcloud-scim.mdx +106 -0
- package/.docs/organized/docs/integrations/keycloak-saml.mdx +128 -0
- package/.docs/organized/docs/integrations/lastpass-saml.mdx +134 -0
- package/.docs/organized/docs/integrations/linkedin-oauth.mdx +77 -0
- package/.docs/organized/docs/integrations/login-gov-oidc.mdx +103 -0
- package/.docs/organized/docs/integrations/microsoft-ad-fs-saml.mdx +96 -0
- package/.docs/organized/docs/integrations/microsoft-oauth.mdx +101 -0
- package/.docs/organized/docs/integrations/miniorange-saml.mdx +124 -0
- package/.docs/organized/docs/integrations/net-iq-saml.mdx +75 -0
- package/.docs/organized/docs/integrations/next-auth.mdx +257 -0
- package/.docs/organized/docs/integrations/oidc.mdx +64 -0
- package/.docs/organized/docs/integrations/okta-saml.mdx +144 -0
- package/.docs/organized/docs/integrations/okta-scim.mdx +210 -0
- package/.docs/organized/docs/integrations/onelogin-saml.mdx +131 -0
- package/.docs/organized/docs/integrations/onelogin-scim.mdx +150 -0
- package/.docs/organized/docs/integrations/oracle-saml.mdx +76 -0
- package/.docs/organized/docs/integrations/pingfederate-saml.mdx +103 -0
- package/.docs/organized/docs/integrations/pingfederate-scim.mdx +150 -0
- package/.docs/organized/docs/integrations/pingone-saml.mdx +86 -0
- package/.docs/organized/docs/integrations/react-native-expo.mdx +93 -0
- package/.docs/organized/docs/integrations/rippling-saml.mdx +174 -0
- package/.docs/organized/docs/integrations/rippling-scim.mdx +148 -0
- package/.docs/organized/docs/integrations/salesforce-saml.mdx +143 -0
- package/.docs/organized/docs/integrations/saml.mdx +64 -0
- package/.docs/organized/docs/integrations/scim.mdx +64 -0
- package/.docs/organized/docs/integrations/sftp.mdx +150 -0
- package/.docs/organized/docs/integrations/shibboleth-generic-saml.mdx +84 -0
- package/.docs/organized/docs/integrations/shibboleth-unsolicited-saml.mdx +84 -0
- package/.docs/organized/docs/integrations/simple-saml-php.mdx +78 -0
- package/.docs/organized/docs/integrations/slack-oauth.mdx +102 -0
- package/.docs/organized/docs/integrations/supabase.mdx +68 -0
- package/.docs/organized/docs/integrations/vmware-saml.mdx +100 -0
- package/.docs/organized/docs/integrations/workday.mdx +156 -0
- package/.docs/organized/docs/integrations/xero-oauth.mdx +83 -0
- package/.docs/organized/docs/magic-link/_navigation.mdx +16 -0
- package/.docs/organized/docs/magic-link/example-apps.mdx +46 -0
- package/.docs/organized/docs/magic-link/index.mdx +199 -0
- package/.docs/organized/docs/magic-link/launch-checklist.mdx +27 -0
- package/.docs/organized/docs/mfa/_navigation.mdx +18 -0
- package/.docs/organized/docs/mfa/example-apps.mdx +46 -0
- package/.docs/organized/docs/mfa/index.mdx +140 -0
- package/.docs/organized/docs/mfa/ux/enrollment.mdx +74 -0
- package/.docs/organized/docs/mfa/ux/sign-in.mdx +30 -0
- package/.docs/organized/docs/migrate/_navigation.mdx +6 -0
- package/.docs/organized/docs/migrate/auth0.mdx +98 -0
- package/.docs/organized/docs/migrate/aws-cognito.mdx +115 -0
- package/.docs/organized/docs/migrate/clerk.mdx +106 -0
- package/.docs/organized/docs/migrate/firebase.mdx +80 -0
- package/.docs/organized/docs/migrate/other-services.mdx +179 -0
- package/.docs/organized/docs/migrate/standalone-sso.mdx +105 -0
- package/.docs/organized/docs/on-prem-deployment.mdx +119 -0
- package/.docs/organized/docs/postman.mdx +90 -0
- package/.docs/organized/docs/reference/_navigation.mdx +527 -0
- package/.docs/organized/docs/reference/admin-portal/index.mdx +6 -0
- package/.docs/organized/docs/reference/admin-portal/portal-link/generate.mdx +268 -0
- package/.docs/organized/docs/reference/admin-portal/portal-link/index.mdx +15 -0
- package/.docs/organized/docs/reference/admin-portal/provider-icons/index.mdx +52 -0
- package/.docs/organized/docs/reference/api-keys.mdx +22 -0
- package/.docs/organized/docs/reference/audit-logs/audit-log-export.mdx +239 -0
- package/.docs/organized/docs/reference/audit-logs/audit-log-schema.mdx +69 -0
- package/.docs/organized/docs/reference/audit-logs/create-event.mdx +673 -0
- package/.docs/organized/docs/reference/audit-logs/create-export.mdx +308 -0
- package/.docs/organized/docs/reference/audit-logs/create-schema.mdx +95 -0
- package/.docs/organized/docs/reference/audit-logs/get-export.mdx +117 -0
- package/.docs/organized/docs/reference/audit-logs/get-retention.mdx +34 -0
- package/.docs/organized/docs/reference/audit-logs/index.mdx +6 -0
- package/.docs/organized/docs/reference/audit-logs/list-actions.mdx +40 -0
- package/.docs/organized/docs/reference/audit-logs/list-schemas.mdx +40 -0
- package/.docs/organized/docs/reference/audit-logs/set-retention.mdx +39 -0
- package/.docs/organized/docs/reference/client-libraries.mdx +19 -0
- package/.docs/organized/docs/reference/directory-sync/directory/delete.mdx +90 -0
- package/.docs/organized/docs/reference/directory-sync/directory/get.mdx +105 -0
- package/.docs/organized/docs/reference/directory-sync/directory/index.mdx +385 -0
- package/.docs/organized/docs/reference/directory-sync/directory/list.mdx +281 -0
- package/.docs/organized/docs/reference/directory-sync/directory-group/get.mdx +105 -0
- package/.docs/organized/docs/reference/directory-sync/directory-group/index.mdx +277 -0
- package/.docs/organized/docs/reference/directory-sync/directory-group/list.mdx +295 -0
- package/.docs/organized/docs/reference/directory-sync/directory-user/get.mdx +112 -0
- package/.docs/organized/docs/reference/directory-sync/directory-user/index.mdx +470 -0
- package/.docs/organized/docs/reference/directory-sync/directory-user/list.mdx +304 -0
- package/.docs/organized/docs/reference/directory-sync/index.mdx +10 -0
- package/.docs/organized/docs/reference/domain-verification/create.mdx +38 -0
- package/.docs/organized/docs/reference/domain-verification/get.mdx +32 -0
- package/.docs/organized/docs/reference/domain-verification/index.mdx +84 -0
- package/.docs/organized/docs/reference/domain-verification/verify.mdx +36 -0
- package/.docs/organized/docs/reference/errors.mdx +30 -0
- package/.docs/organized/docs/reference/events/index.mdx +9 -0
- package/.docs/organized/docs/reference/events/list.mdx +246 -0
- package/.docs/organized/docs/reference/fga/batch-check.mdx +277 -0
- package/.docs/organized/docs/reference/fga/check.mdx +563 -0
- package/.docs/organized/docs/reference/fga/index.mdx +6 -0
- package/.docs/organized/docs/reference/fga/policy/create.mdx +27 -0
- package/.docs/organized/docs/reference/fga/policy/delete.mdx +18 -0
- package/.docs/organized/docs/reference/fga/policy/get.mdx +23 -0
- package/.docs/organized/docs/reference/fga/policy/index.mdx +52 -0
- package/.docs/organized/docs/reference/fga/policy/list.mdx +41 -0
- package/.docs/organized/docs/reference/fga/policy/update.mdx +26 -0
- package/.docs/organized/docs/reference/fga/query.mdx +375 -0
- package/.docs/organized/docs/reference/fga/resource/batch-write.mdx +175 -0
- package/.docs/organized/docs/reference/fga/resource/create.mdx +130 -0
- package/.docs/organized/docs/reference/fga/resource/delete.mdx +86 -0
- package/.docs/organized/docs/reference/fga/resource/get.mdx +88 -0
- package/.docs/organized/docs/reference/fga/resource/index.mdx +98 -0
- package/.docs/organized/docs/reference/fga/resource/list.mdx +188 -0
- package/.docs/organized/docs/reference/fga/resource/update.mdx +115 -0
- package/.docs/organized/docs/reference/fga/resource-type/apply.mdx +35 -0
- package/.docs/organized/docs/reference/fga/resource-type/create.mdx +24 -0
- package/.docs/organized/docs/reference/fga/resource-type/delete.mdx +22 -0
- package/.docs/organized/docs/reference/fga/resource-type/get.mdx +23 -0
- package/.docs/organized/docs/reference/fga/resource-type/index.mdx +68 -0
- package/.docs/organized/docs/reference/fga/resource-type/list.mdx +36 -0
- package/.docs/organized/docs/reference/fga/resource-type/update.mdx +23 -0
- package/.docs/organized/docs/reference/fga/schema/apply.mdx +42 -0
- package/.docs/organized/docs/reference/fga/schema/get.mdx +24 -0
- package/.docs/organized/docs/reference/fga/schema/index.mdx +39 -0
- package/.docs/organized/docs/reference/fga/warrant/batch-write.mdx +226 -0
- package/.docs/organized/docs/reference/fga/warrant/create.mdx +215 -0
- package/.docs/organized/docs/reference/fga/warrant/delete.mdx +212 -0
- package/.docs/organized/docs/reference/fga/warrant/index.mdx +186 -0
- package/.docs/organized/docs/reference/fga/warrant/list.mdx +282 -0
- package/.docs/organized/docs/reference/idempotency.mdx +21 -0
- package/.docs/organized/docs/reference/index.mdx +194 -0
- package/.docs/organized/docs/reference/magic-link/index.mdx +8 -0
- package/.docs/organized/docs/reference/magic-link/passwordless-session/create.mdx +268 -0
- package/.docs/organized/docs/reference/magic-link/passwordless-session/index.mdx +203 -0
- package/.docs/organized/docs/reference/magic-link/passwordless-session/send-email.mdx +158 -0
- package/.docs/organized/docs/reference/mfa/authentication-challenge.mdx +217 -0
- package/.docs/organized/docs/reference/mfa/authentication-factor.mdx +381 -0
- package/.docs/organized/docs/reference/mfa/challenge-factor.mdx +170 -0
- package/.docs/organized/docs/reference/mfa/delete-factor.mdx +93 -0
- package/.docs/organized/docs/reference/mfa/enroll-factor.mdx +241 -0
- package/.docs/organized/docs/reference/mfa/get-factor.mdx +108 -0
- package/.docs/organized/docs/reference/mfa/index.mdx +8 -0
- package/.docs/organized/docs/reference/mfa/verify-challenge.mdx +228 -0
- package/.docs/organized/docs/reference/organization/create.mdx +216 -0
- package/.docs/organized/docs/reference/organization/delete.mdx +89 -0
- package/.docs/organized/docs/reference/organization/get-by-external-id.mdx +40 -0
- package/.docs/organized/docs/reference/organization/get.mdx +104 -0
- package/.docs/organized/docs/reference/organization/index.mdx +274 -0
- package/.docs/organized/docs/reference/organization/list.mdx +258 -0
- package/.docs/organized/docs/reference/organization/update.mdx +236 -0
- package/.docs/organized/docs/reference/organization-domain.mdx +189 -0
- package/.docs/organized/docs/reference/pagination.mdx +244 -0
- package/.docs/organized/docs/reference/radar/attempts/create.mdx +115 -0
- package/.docs/organized/docs/reference/radar/attempts/index.mdx +7 -0
- package/.docs/organized/docs/reference/radar/attempts/update.mdx +34 -0
- package/.docs/organized/docs/reference/radar/index.mdx +8 -0
- package/.docs/organized/docs/reference/radar/lists/delete.mdx +36 -0
- package/.docs/organized/docs/reference/radar/lists/index.mdx +7 -0
- package/.docs/organized/docs/reference/radar/lists/update.mdx +36 -0
- package/.docs/organized/docs/reference/rate-limits.mdx +50 -0
- package/.docs/organized/docs/reference/roles/index.mdx +268 -0
- package/.docs/organized/docs/reference/roles/list-for-organization.mdx +152 -0
- package/.docs/organized/docs/reference/sso/connection/delete.mdx +89 -0
- package/.docs/organized/docs/reference/sso/connection/get.mdx +104 -0
- package/.docs/organized/docs/reference/sso/connection/index.mdx +388 -0
- package/.docs/organized/docs/reference/sso/connection/list.mdx +320 -0
- package/.docs/organized/docs/reference/sso/get-authorization-url/error-codes.mdx +28 -0
- package/.docs/organized/docs/reference/sso/get-authorization-url/index.mdx +434 -0
- package/.docs/organized/docs/reference/sso/get-authorization-url/redirect-uri.mdx +21 -0
- package/.docs/organized/docs/reference/sso/index.mdx +8 -0
- package/.docs/organized/docs/reference/sso/logout/authorize.mdx +47 -0
- package/.docs/organized/docs/reference/sso/logout/index.mdx +14 -0
- package/.docs/organized/docs/reference/sso/logout/redirect.mdx +32 -0
- package/.docs/organized/docs/reference/sso/profile/get-profile-and-token.mdx +229 -0
- package/.docs/organized/docs/reference/sso/profile/get-user-profile.mdx +127 -0
- package/.docs/organized/docs/reference/sso/profile/index.mdx +364 -0
- package/.docs/organized/docs/reference/testing.mdx +8 -0
- package/.docs/organized/docs/reference/user-management/access-token/index.mdx +13 -0
- package/.docs/organized/docs/reference/user-management/authentication/code.mdx +448 -0
- package/.docs/organized/docs/reference/user-management/authentication/email-verification.mdx +359 -0
- package/.docs/organized/docs/reference/user-management/authentication/get-authorization-url/error-codes.mdx +25 -0
- package/.docs/organized/docs/reference/user-management/authentication/get-authorization-url/index.mdx +425 -0
- package/.docs/organized/docs/reference/user-management/authentication/get-authorization-url/pkce.mdx +9 -0
- package/.docs/organized/docs/reference/user-management/authentication/get-authorization-url/redirect-uri.mdx +23 -0
- package/.docs/organized/docs/reference/user-management/authentication/index.mdx +66 -0
- package/.docs/organized/docs/reference/user-management/authentication/magic-auth.mdx +353 -0
- package/.docs/organized/docs/reference/user-management/authentication/organization-selection.mdx +349 -0
- package/.docs/organized/docs/reference/user-management/authentication/password.mdx +350 -0
- package/.docs/organized/docs/reference/user-management/authentication/refresh-and-seal-session-data.mdx +57 -0
- package/.docs/organized/docs/reference/user-management/authentication/refresh-token.mdx +381 -0
- package/.docs/organized/docs/reference/user-management/authentication/session-cookie.mdx +79 -0
- package/.docs/organized/docs/reference/user-management/authentication/totp.mdx +369 -0
- package/.docs/organized/docs/reference/user-management/authentication-errors/email-verification-required-error.mdx +42 -0
- package/.docs/organized/docs/reference/user-management/authentication-errors/index.mdx +20 -0
- package/.docs/organized/docs/reference/user-management/authentication-errors/mfa-challenge-error.mdx +44 -0
- package/.docs/organized/docs/reference/user-management/authentication-errors/mfa-enrollment-error.mdx +37 -0
- package/.docs/organized/docs/reference/user-management/authentication-errors/organization-authentication-required-error.mdx +68 -0
- package/.docs/organized/docs/reference/user-management/authentication-errors/organization-selection-error.mdx +44 -0
- package/.docs/organized/docs/reference/user-management/authentication-errors/sso-required-error.mdx +51 -0
- package/.docs/organized/docs/reference/user-management/email-verification/get.mdx +88 -0
- package/.docs/organized/docs/reference/user-management/email-verification/index.mdx +227 -0
- package/.docs/organized/docs/reference/user-management/identity/index.mdx +74 -0
- package/.docs/organized/docs/reference/user-management/identity/list.mdx +52 -0
- package/.docs/organized/docs/reference/user-management/index.mdx +13 -0
- package/.docs/organized/docs/reference/user-management/invitation/accept.mdx +39 -0
- package/.docs/organized/docs/reference/user-management/invitation/find-by-token.mdx +87 -0
- package/.docs/organized/docs/reference/user-management/invitation/get.mdx +87 -0
- package/.docs/organized/docs/reference/user-management/invitation/index.mdx +374 -0
- package/.docs/organized/docs/reference/user-management/invitation/list.mdx +247 -0
- package/.docs/organized/docs/reference/user-management/invitation/revoke.mdx +90 -0
- package/.docs/organized/docs/reference/user-management/invitation/send.mdx +230 -0
- package/.docs/organized/docs/reference/user-management/logout/get-logout-url-from-session-cookie.mdx +52 -0
- package/.docs/organized/docs/reference/user-management/logout/get-logout-url.mdx +147 -0
- package/.docs/organized/docs/reference/user-management/logout/index.mdx +26 -0
- package/.docs/organized/docs/reference/user-management/magic-auth/create.mdx +148 -0
- package/.docs/organized/docs/reference/user-management/magic-auth/get.mdx +88 -0
- package/.docs/organized/docs/reference/user-management/magic-auth/index.mdx +225 -0
- package/.docs/organized/docs/reference/user-management/mfa/authentication-challenge.mdx +194 -0
- package/.docs/organized/docs/reference/user-management/mfa/authentication-factor.mdx +324 -0
- package/.docs/organized/docs/reference/user-management/mfa/enroll-auth-factor.mdx +296 -0
- package/.docs/organized/docs/reference/user-management/mfa/index.mdx +5 -0
- package/.docs/organized/docs/reference/user-management/mfa/list-auth-factors.mdx +194 -0
- package/.docs/organized/docs/reference/user-management/organization-membership/create.mdx +155 -0
- package/.docs/organized/docs/reference/user-management/organization-membership/deactivate.mdx +106 -0
- package/.docs/organized/docs/reference/user-management/organization-membership/delete.mdx +76 -0
- package/.docs/organized/docs/reference/user-management/organization-membership/get.mdx +95 -0
- package/.docs/organized/docs/reference/user-management/organization-membership/index.mdx +265 -0
- package/.docs/organized/docs/reference/user-management/organization-membership/list.mdx +291 -0
- package/.docs/organized/docs/reference/user-management/organization-membership/reactivate.mdx +106 -0
- package/.docs/organized/docs/reference/user-management/organization-membership/update.mdx +119 -0
- package/.docs/organized/docs/reference/user-management/password-reset/create.mdx +108 -0
- package/.docs/organized/docs/reference/user-management/password-reset/get.mdx +88 -0
- package/.docs/organized/docs/reference/user-management/password-reset/index.mdx +227 -0
- package/.docs/organized/docs/reference/user-management/password-reset/reset-password.mdx +144 -0
- package/.docs/organized/docs/reference/user-management/session-helpers/authenticate.mdx +176 -0
- package/.docs/organized/docs/reference/user-management/session-helpers/get-logout-url.mdx +42 -0
- package/.docs/organized/docs/reference/user-management/session-helpers/index.mdx +14 -0
- package/.docs/organized/docs/reference/user-management/session-helpers/load-sealed-session.mdx +105 -0
- package/.docs/organized/docs/reference/user-management/session-helpers/refresh.mdx +213 -0
- package/.docs/organized/docs/reference/user-management/session-tokens/access-token.mdx +90 -0
- package/.docs/organized/docs/reference/user-management/session-tokens/index.mdx +5 -0
- package/.docs/organized/docs/reference/user-management/session-tokens/jwks.mdx +110 -0
- package/.docs/organized/docs/reference/user-management/session-tokens/refresh-token.mdx +8 -0
- package/.docs/organized/docs/reference/user-management/user/create.mdx +327 -0
- package/.docs/organized/docs/reference/user-management/user/delete.mdx +76 -0
- package/.docs/organized/docs/reference/user-management/user/get-by-external-id.mdx +39 -0
- package/.docs/organized/docs/reference/user-management/user/get.mdx +103 -0
- package/.docs/organized/docs/reference/user-management/user/index.mdx +322 -0
- package/.docs/organized/docs/reference/user-management/user/list.mdx +260 -0
- package/.docs/organized/docs/reference/user-management/user/update.mdx +344 -0
- package/.docs/organized/docs/reference/vault/index.mdx +6 -0
- package/.docs/organized/docs/reference/vault/key/create-data-key.mdx +106 -0
- package/.docs/organized/docs/reference/vault/key/decrypt-data-key.mdx +84 -0
- package/.docs/organized/docs/reference/vault/key/decrypt-data.mdx +52 -0
- package/.docs/organized/docs/reference/vault/key/encrypt-data.mdx +58 -0
- package/.docs/organized/docs/reference/vault/key/index.mdx +25 -0
- package/.docs/organized/docs/reference/vault/object/create.mdx +62 -0
- package/.docs/organized/docs/reference/vault/object/delete.mdx +75 -0
- package/.docs/organized/docs/reference/vault/object/get.mdx +50 -0
- package/.docs/organized/docs/reference/vault/object/index.mdx +174 -0
- package/.docs/organized/docs/reference/vault/object/list.mdx +105 -0
- package/.docs/organized/docs/reference/vault/object/metadata.mdx +52 -0
- package/.docs/organized/docs/reference/vault/object/update.mdx +67 -0
- package/.docs/organized/docs/reference/vault/object/version.mdx +87 -0
- package/.docs/organized/docs/reference/vault/object/versions.mdx +83 -0
- package/.docs/organized/docs/reference/widgets/get-token.mdx +185 -0
- package/.docs/organized/docs/reference/widgets/index.mdx +6 -0
- package/.docs/organized/docs/reference/workos-connect/authorize/index.mdx +75 -0
- package/.docs/organized/docs/reference/workos-connect/index.mdx +33 -0
- package/.docs/organized/docs/reference/workos-connect/introspection/index.mdx +122 -0
- package/.docs/organized/docs/reference/workos-connect/metadata/index.mdx +25 -0
- package/.docs/organized/docs/reference/workos-connect/metadata/oauth-authorization-server/index.mdx +99 -0
- package/.docs/organized/docs/reference/workos-connect/metadata/openid-configuration/index.mdx +70 -0
- package/.docs/organized/docs/reference/workos-connect/token/authorization-code-grant/access-token.mdx +53 -0
- package/.docs/organized/docs/reference/workos-connect/token/authorization-code-grant/id-token.mdx +60 -0
- package/.docs/organized/docs/reference/workos-connect/token/authorization-code-grant/index.mdx +69 -0
- package/.docs/organized/docs/reference/workos-connect/token/client-credentials-grant/access-token.mdx +46 -0
- package/.docs/organized/docs/reference/workos-connect/token/client-credentials-grant/index.mdx +56 -0
- package/.docs/organized/docs/reference/workos-connect/token/index.mdx +39 -0
- package/.docs/organized/docs/reference/workos-connect/token/refresh-token-grant.mdx +69 -0
- package/.docs/organized/docs/reference/workos-connect/userinfo/index.mdx +46 -0
- package/.docs/organized/docs/sdks/dotnet.mdx +6 -0
- package/.docs/organized/docs/sdks/elixir.mdx +6 -0
- package/.docs/organized/docs/sdks/go.mdx +6 -0
- package/.docs/organized/docs/sdks/java.mdx +9 -0
- package/.docs/organized/docs/sdks/laravel.mdx +6 -0
- package/.docs/organized/docs/sdks/node.mdx +9 -0
- package/.docs/organized/docs/sdks/php.mdx +6 -0
- package/.docs/organized/docs/sdks/python.mdx +6 -0
- package/.docs/organized/docs/sdks/ruby.mdx +9 -0
- package/.docs/organized/docs/sso/_navigation.mdx +44 -0
- package/.docs/organized/docs/sso/_sequence-diagrams/saml-protocol-security-considerations.md +59 -0
- package/.docs/organized/docs/sso/attributes.mdx +110 -0
- package/.docs/organized/docs/sso/domains.mdx +111 -0
- package/.docs/organized/docs/sso/example-apps.mdx +46 -0
- package/.docs/organized/docs/sso/identity-provider-role-assignment.mdx +113 -0
- package/.docs/organized/docs/sso/index.mdx +295 -0
- package/.docs/organized/docs/sso/it-team-faq.mdx +35 -0
- package/.docs/organized/docs/sso/jit-provisioning.mdx +101 -0
- package/.docs/organized/docs/sso/launch-checklist.mdx +71 -0
- package/.docs/organized/docs/sso/login-flows.mdx +101 -0
- package/.docs/organized/docs/sso/redirect-uris.mdx +44 -0
- package/.docs/organized/docs/sso/saml-security.mdx +122 -0
- package/.docs/organized/docs/sso/signing-certificates.mdx +121 -0
- package/.docs/organized/docs/sso/single-logout.mdx +45 -0
- package/.docs/organized/docs/sso/test-sso.mdx +73 -0
- package/.docs/organized/docs/sso/ux/sign-in.mdx +44 -0
- package/.docs/organized/docs/user-management/_navigation.mdx +87 -0
- package/.docs/organized/docs/user-management/actions.mdx +169 -0
- package/.docs/organized/docs/user-management/authkit.mdx +69 -0
- package/.docs/organized/docs/user-management/branding.mdx +143 -0
- package/.docs/organized/docs/user-management/connect.mdx +110 -0
- package/.docs/organized/docs/user-management/custom-emails.mdx +164 -0
- package/.docs/organized/docs/user-management/directory-provisioning.mdx +78 -0
- package/.docs/organized/docs/user-management/domain-verification.mdx +28 -0
- package/.docs/organized/docs/user-management/email-password.mdx +42 -0
- package/.docs/organized/docs/user-management/email-verification.mdx +29 -0
- package/.docs/organized/docs/user-management/entitlements.mdx +46 -0
- package/.docs/organized/docs/user-management/example-apps.mdx +39 -0
- package/.docs/organized/docs/user-management/identity-linking.mdx +52 -0
- package/.docs/organized/docs/user-management/impersonation.mdx +82 -0
- package/.docs/organized/docs/user-management/index.mdx +525 -0
- package/.docs/organized/docs/user-management/invitations.mdx +60 -0
- package/.docs/organized/docs/user-management/invite-only-signup.mdx +72 -0
- package/.docs/organized/docs/user-management/jit-provisioning.mdx +36 -0
- package/.docs/organized/docs/user-management/jwt-templates.mdx +278 -0
- package/.docs/organized/docs/user-management/magic-auth.mdx +36 -0
- package/.docs/organized/docs/user-management/mcp.mdx +146 -0
- package/.docs/organized/docs/user-management/metadata.mdx +119 -0
- package/.docs/organized/docs/user-management/mfa.mdx +32 -0
- package/.docs/organized/docs/user-management/migrations.mdx +20 -0
- package/.docs/organized/docs/user-management/modeling-your-app.mdx +149 -0
- package/.docs/organized/docs/user-management/organization-policies.mdx +33 -0
- package/.docs/organized/docs/user-management/overview.mdx +46 -0
- package/.docs/organized/docs/user-management/passkeys.mdx +42 -0
- package/.docs/organized/docs/user-management/radar.mdx +127 -0
- package/.docs/organized/docs/user-management/roles-and-permissions.mdx +155 -0
- package/.docs/organized/docs/user-management/sessions.mdx +101 -0
- package/.docs/organized/docs/user-management/social-login.mdx +34 -0
- package/.docs/organized/docs/user-management/sso-with-contractors.mdx +85 -0
- package/.docs/organized/docs/user-management/sso.mdx +96 -0
- package/.docs/organized/docs/user-management/users-organizations.mdx +91 -0
- package/.docs/organized/docs/user-management/widgets.mdx +190 -0
- package/.docs/organized/docs/vault/_navigation.mdx +14 -0
- package/.docs/organized/docs/vault/index.mdx +38 -0
- package/.docs/organized/docs/vault/key-context.mdx +32 -0
- package/.docs/organized/docs/vault/quick-start.mdx +82 -0
- package/README.md +252 -0
- package/dist/chunk-64GKEK6G.js +48 -0
- package/dist/chunk-64GKEK6G.js.map +1 -0
- package/dist/get-tools.d.ts +23 -0
- package/dist/get-tools.js +8 -0
- package/dist/get-tools.js.map +1 -0
- package/dist/index.d.ts +1 -0
- package/dist/index.js +552 -0
- package/dist/index.js.map +1 -0
- package/dist/prepare.d.ts +2 -0
- package/dist/prepare.js +269 -0
- package/dist/prepare.js.map +1 -0
- package/package.json +49 -0
|
@@ -0,0 +1,59 @@
|
|
|
1
|
+
---
|
|
2
|
+
originalPath: >-
|
|
3
|
+
.tmp-workos-clone/packages/docs/content/sso/_sequence-diagrams/saml-protocol-security-considerations.md
|
|
4
|
+
---
|
|
5
|
+
# Diagrams for 'SAML Security Considerations'
|
|
6
|
+
|
|
7
|
+
Currently MermaidJS rendering is not supported in docs.workos.com, so to see the rendering you’ll need to view this file on the GitHub website (VS Code Markdown preview does not support rendering).
|
|
8
|
+
Alternatively you could paste the contents into [Mermaid's live editor](https://mermaid.live/) to see rendering.
|
|
9
|
+
|
|
10
|
+
In the WorkOS docs it is required to draw sequence diagrams in FigJam, you can use the Mermaid generated sequence diagram as a guide to copy from.
|
|
11
|
+
|
|
12
|
+
## SP to IdP flows (SP initiated)
|
|
13
|
+
|
|
14
|
+
```mermaid
|
|
15
|
+
%%{
|
|
16
|
+
init: {
|
|
17
|
+
"sequence": {
|
|
18
|
+
"noteAlign": "left"
|
|
19
|
+
}
|
|
20
|
+
}
|
|
21
|
+
}%%
|
|
22
|
+
|
|
23
|
+
sequenceDiagram
|
|
24
|
+
autonumber
|
|
25
|
+
participant u as User Agent
|
|
26
|
+
participant a as Your Application
|
|
27
|
+
participant sp as WorkOS
|
|
28
|
+
|
|
29
|
+
u -->> a: Begin login flow
|
|
30
|
+
a ->> u: redirect to WorkOS
|
|
31
|
+
u ->> sp:
|
|
32
|
+
sp -->> sp: create SAML AuthN Request
|
|
33
|
+
note right of sp: Optional: <br><br> 1. Sign the whole SAML Request message (envelope)
|
|
34
|
+
sp ->> u: redirect to IdP with {SAML Request}
|
|
35
|
+
```
|
|
36
|
+
|
|
37
|
+
## IdP to SP flows (SP initiated)
|
|
38
|
+
|
|
39
|
+
```mermaid
|
|
40
|
+
%%{
|
|
41
|
+
init: {
|
|
42
|
+
"sequence": {
|
|
43
|
+
"noteAlign": "left"
|
|
44
|
+
}
|
|
45
|
+
}
|
|
46
|
+
}%%
|
|
47
|
+
|
|
48
|
+
sequenceDiagram
|
|
49
|
+
autonumber
|
|
50
|
+
participant u as User Agent
|
|
51
|
+
participant idp as IdP
|
|
52
|
+
participant sp as WorkOS
|
|
53
|
+
|
|
54
|
+
u ->> idp: present {SAML AuthN Request}
|
|
55
|
+
idp --> u: authenticate the user
|
|
56
|
+
idp -->> idp: create SAML AuthN Response
|
|
57
|
+
idp ->> u: redirect with {SAML Response} to WorkOS
|
|
58
|
+
u -->> sp:
|
|
59
|
+
```
|
|
@@ -0,0 +1,110 @@
|
|
|
1
|
+
---
|
|
2
|
+
title: Profile Attributes
|
|
3
|
+
description: Configure how attributes map from identity providers to SSO Profiles.
|
|
4
|
+
originalPath: .tmp-workos-clone/packages/docs/content/sso/attributes.mdx
|
|
5
|
+
---
|
|
6
|
+
|
|
7
|
+
## Introduction
|
|
8
|
+
|
|
9
|
+
WorkOS automatically normalizes a standard set of attributes from identity providers (IdPs) into the [Single Sign-On (SSO) Profile](/reference/sso/profile) object. More unique cases can be mapped by your customer admins. In this guide, we’ll explain how to map data from identity providers to the SSO Profiles.
|
|
10
|
+
|
|
11
|
+
## Definitions
|
|
12
|
+
|
|
13
|
+
**Standard attributes**
|
|
14
|
+
: The most common user information, normalized across providers.
|
|
15
|
+
|
|
16
|
+
**Predefined attributes**
|
|
17
|
+
: Detailed user attributes for specific use cases, normalized across providers. You can opt-in to each attribute you'd like organization admins to map during SSO connection configuration.
|
|
18
|
+
|
|
19
|
+
**Custom attributes**
|
|
20
|
+
: For unique cases, you can create custom attributes your customers can map when setting up an SSO connection.
|
|
21
|
+
|
|
22
|
+
## Standard attributes
|
|
23
|
+
|
|
24
|
+
Every SSO Profile comes with the following standard attributes. These are the core set of attributes that are common across all identity providers. These are structured fields with a guaranteed schema in the top-level SSO Profile payload.
|
|
25
|
+
|
|
26
|
+
| Attribute | Description |
|
|
27
|
+
| ------------ | ---------------------------------------------------------------------------------------------------------------------- |
|
|
28
|
+
| `idp_id` | The user’s unique identifier, assigned by the identity provider. Different identity providers use different ID formats |
|
|
29
|
+
| `email` | The user’s email |
|
|
30
|
+
| `first_name` | The user’s first name |
|
|
31
|
+
| `last_name` | The user’s last name |
|
|
32
|
+
|
|
33
|
+
---
|
|
34
|
+
|
|
35
|
+
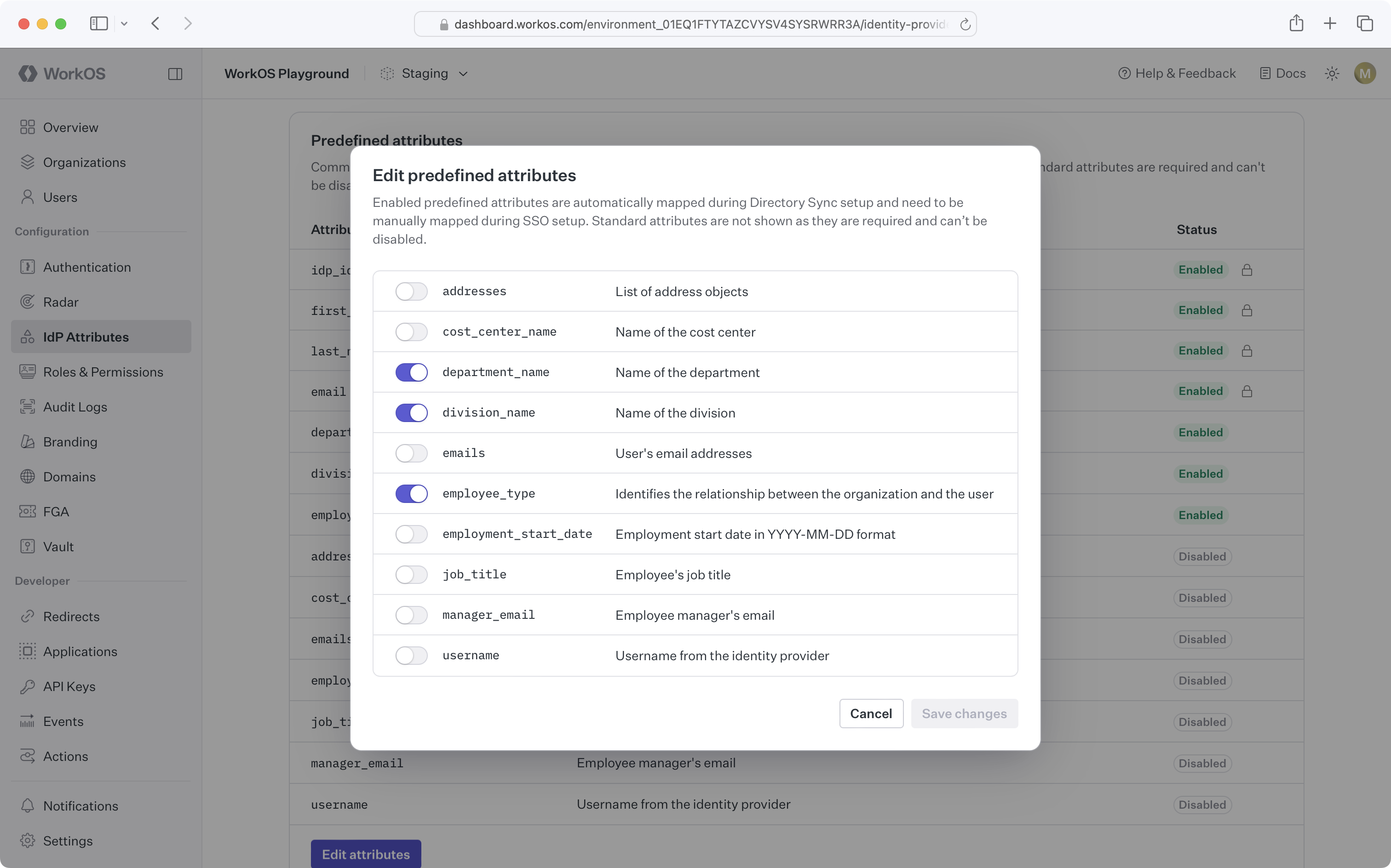
## Custom attributes
|
|
36
|
+
|
|
37
|
+
For more detailed user information, you can opt-in to additional predefined attributes and define your own custom attributes. These attributes will appear in the `custom_attributes` field on [SSO Profile](/reference/sso/profile) objects and can be configured in the [WorkOS Dashboard](https://dashboard.workos.com/).
|
|
38
|
+
|
|
39
|
+
> Custom attributes are currently only supported for SAML SSO connections. If you are interested in custom attributes for OIDC and OAuth connections, please reach out to [support](mailto:support@workos.com).
|
|
40
|
+
|
|
41
|
+
### Predefined attributes
|
|
42
|
+
|
|
43
|
+
When enabled, organization admins will we asked to map these attributes during SSO configuration in [Admin Portal](/admin-portal). These fields are always optional if enabled. These fields are named and schematized by WorkOS – they cannot be renamed.
|
|
44
|
+
|
|
45
|
+
| Attribute | Type and description | Status |
|
|
46
|
+
| ----------------------- | ------------------------------------------------------------------------------------------------------------------------------- | -------- |
|
|
47
|
+
| `addresses` | The user’s list of address objects (`street_address`, `locality`, `region`, `postal_code`, `country`, `primary`, `raw_address`) | Optional |
|
|
48
|
+
| `cost_center_name` | The user’s cost center name | Optional |
|
|
49
|
+
| `department_name` | The user’s department name | Optional |
|
|
50
|
+
| `division_name` | The user’s division name | Optional |
|
|
51
|
+
| `emails` | The user’s list of email objects (`type`, `value`, `primary`) | Optional |
|
|
52
|
+
| `employee_type` | The user’s employment type | Optional |
|
|
53
|
+
| `employment_start_date` | The user’s start date | Optional |
|
|
54
|
+
| `job_title` | The user’s job title | Optional |
|
|
55
|
+
| `manager_email` | The email address for the user’s manager | Optional |
|
|
56
|
+
| `username` | The user’s username | Optional |
|
|
57
|
+
|
|
58
|
+
#### Enable or disable a predefined attribute
|
|
59
|
+
|
|
60
|
+
Predefined attributes can be enabled or disabled in the [WorkOS Dashboard](https://dashboard.workos.com/) on the Identity Provider Attributes page.
|
|
61
|
+
|
|
62
|
+
|
|
63
|
+
|
|
64
|
+
> For SSO Profiles, making changes to IdP attributes will take effect upon next sign-in.
|
|
65
|
+
|
|
66
|
+
### Custom attributes
|
|
67
|
+
|
|
68
|
+
Custom attributes can be utilized to enrich SSO Profiles with additional data from the identity provider. You can create attributes that appear as fields in the [Admin Portal](https://workos.com/admin-portal). Your customers can map these fields to the correct values in their system when setting up SSO with their identity provider.
|
|
69
|
+
|
|
70
|
+
#### Create a custom attribute
|
|
71
|
+
|
|
72
|
+
Custom attributes can be created in the [WorkOS Dashboard](https://dashboard.workos.com/) on the Identity Provider Attributes page.
|
|
73
|
+
|
|
74
|
+

|
|
75
|
+
|
|
76
|
+
> For SSO Profiles, making changes to IdP attributes will take effect upon next sign-in.
|
|
77
|
+
|
|
78
|
+
#### Delete a custom attribute
|
|
79
|
+
|
|
80
|
+
When a custom attribute is deleted, [SSO Profiles](/reference/sso/profile) will retain these existing attribute values until the next sign-in.
|
|
81
|
+
|
|
82
|
+
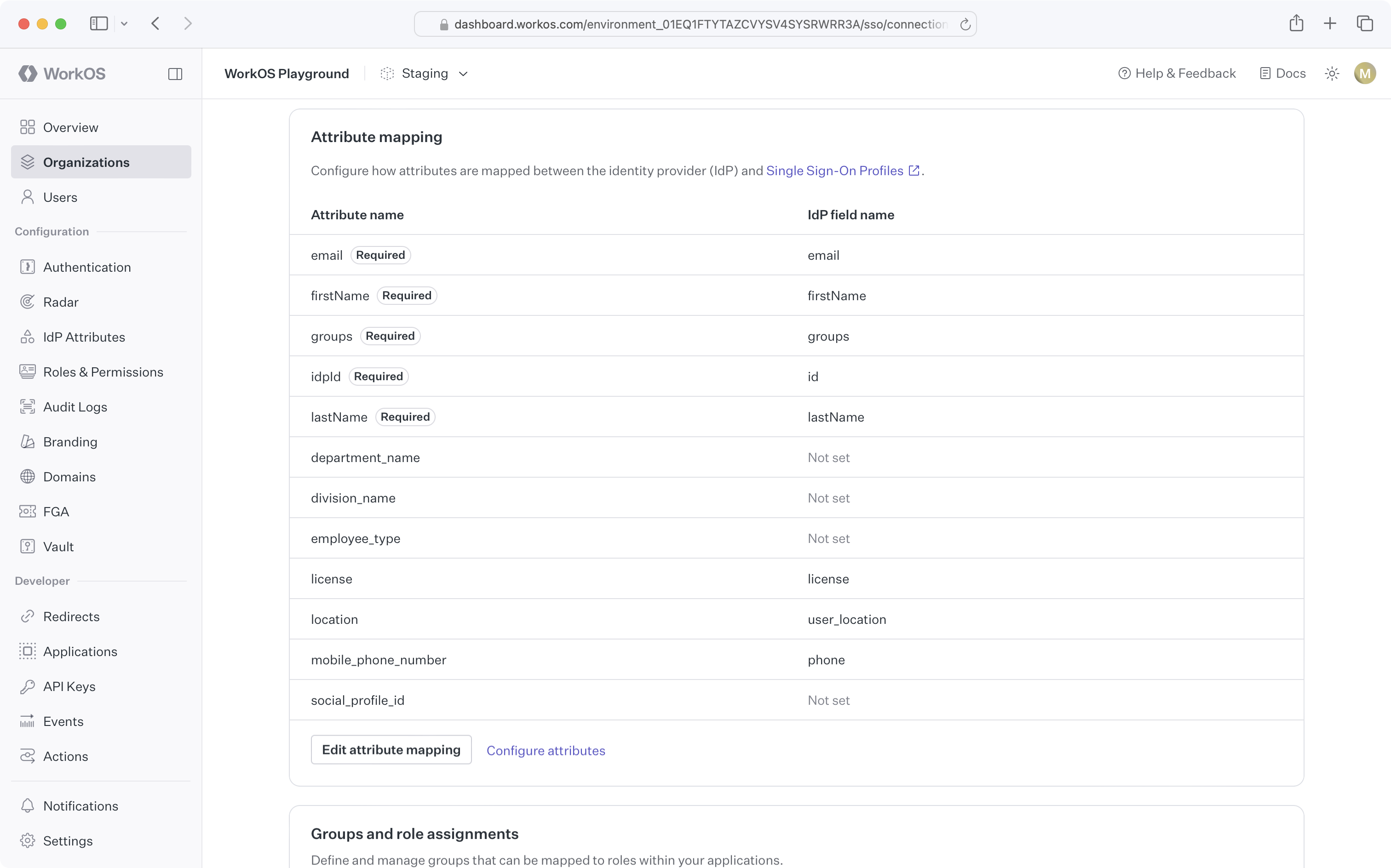
#### Editing attribute mappings
|
|
83
|
+
|
|
84
|
+
If attribute data for a particular SSO connection has changed and is no longer mapped properly, you or the organization admin can edit the attribute mappings via the [WorkOS Dashboard](https://dashboard.workos.com/) connection page or [Admin Portal](https://workos.com/admin-portal), respectively.
|
|
85
|
+
|
|
86
|
+
|
|
87
|
+
|
|
88
|
+
### Custom attribute mapping in Admin Portal
|
|
89
|
+
|
|
90
|
+
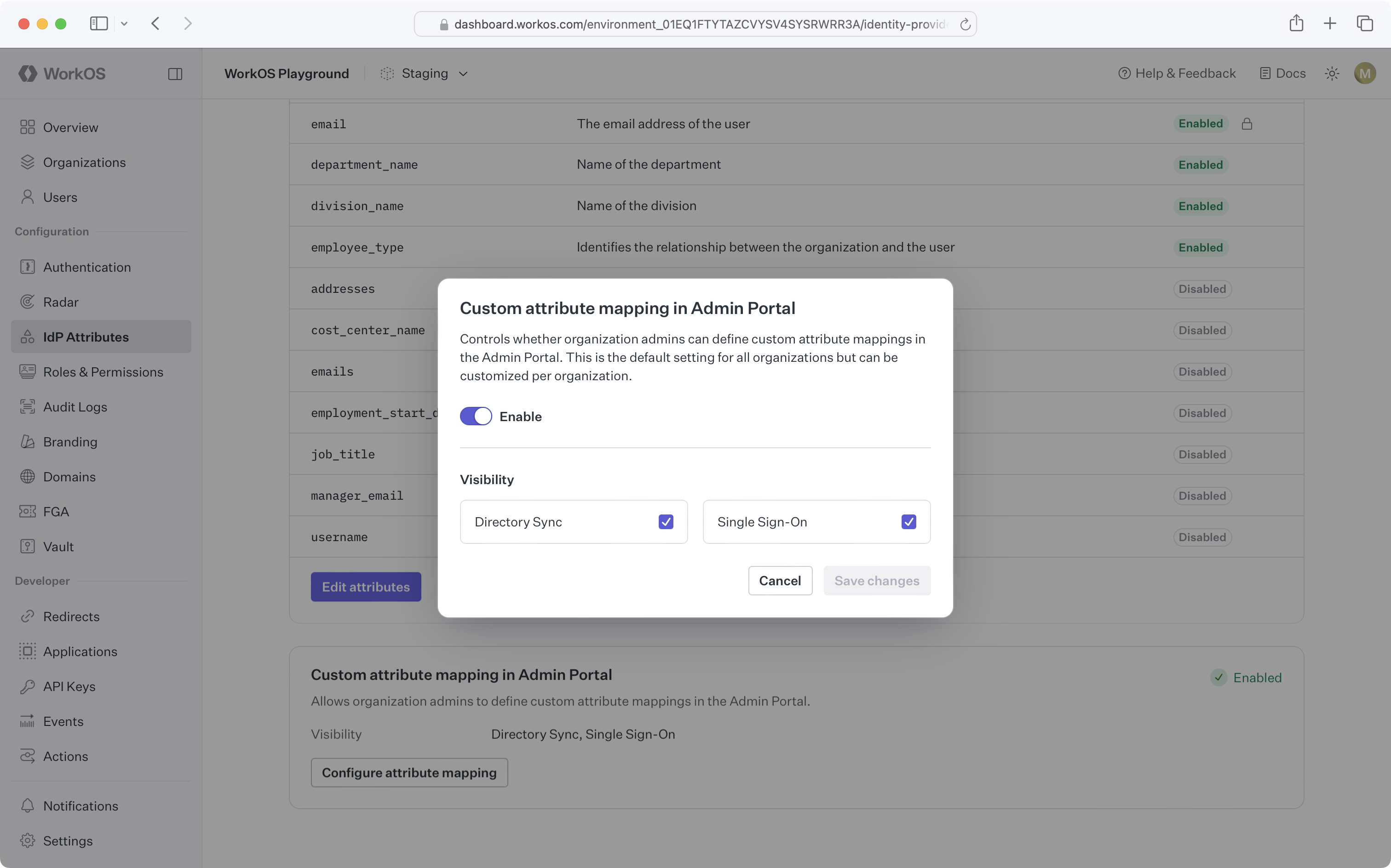
You can control the visibility of custom attribute mapping for Directory Sync and Single Sign-On flows in the Admin Portal at the environment and organization level.
|
|
91
|
+
|
|
92
|
+
The environment-level setting is controlled on the Identity Provider Attributes page in the [WorkOS Dashboard](https://dashboard.workos.com/).
|
|
93
|
+
|
|
94
|
+
|
|
95
|
+
|
|
96
|
+
Organization-level settings are controlled on an individual organization's Attributes tab in the [WorkOS Dashboard](https://dashboard.workos.com/). Organizations mirror the environment-level settings by default.
|
|
97
|
+
|
|
98
|
+
## Frequently asked questions
|
|
99
|
+
|
|
100
|
+
### Which identity providers support mapping additional predefined and custom attributes?
|
|
101
|
+
|
|
102
|
+
Additional predefined and custom attributes are supported for all SAML SSO connections.
|
|
103
|
+
|
|
104
|
+
### Can our customers add their own custom attributes outside of what is defined in the WorkOS Dashboard?
|
|
105
|
+
|
|
106
|
+
We do not currently support this functionality. Custom attributes must be defined in the WorkOS Dashboard first. Please reach out to [support](mailto:support@workos.com) if you have a specific use case that you would like to discuss.
|
|
107
|
+
|
|
108
|
+
### What happens if an attribute cannot be mapped from the IdP?
|
|
109
|
+
|
|
110
|
+
Attributes that cannot be mapped for a particular [SSO Profile](/reference/sso/profile) will result in a `null` value for the attribute.
|
|
@@ -0,0 +1,111 @@
|
|
|
1
|
+
---
|
|
2
|
+
title: Domains
|
|
3
|
+
description: Understand how Organization domains are used with SSO.
|
|
4
|
+
originalPath: .tmp-workos-clone/packages/docs/content/sso/domains.mdx
|
|
5
|
+
---
|
|
6
|
+
|
|
7
|
+
## Organizations
|
|
8
|
+
|
|
9
|
+
When an [Organization](/reference/organization) is created in the WorkOS Dashboard or the [Create Organization API](/reference/organization/create), one or more domains can be associated with the organization.
|
|
10
|
+
|
|
11
|
+
Domains added to an organization need to be verified. In the API, they can be initially added `'pending'` verification, and later verified using the [Domain Verification API](/domain-verification). Or, if previously verified through other means, can be added as `'verified'`.
|
|
12
|
+
|
|
13
|
+
> Domains in the WorkOS Dashboard are always considered verified.
|
|
14
|
+
|
|
15
|
+
## Email validation
|
|
16
|
+
|
|
17
|
+
During authentication, WorkOS uses these domains to verify the user signing in through the organization's [Connection](/reference/sso/connection) belongs to one of these domains. If the domain of the user's email address does not match one of the organization's domains (or the organization has no verified domains) they will sent to your [Redirect URI](/sso/redirect-uris) with a [`profile_not_allowed_outside_organization`](/reference/sso/get-authorization-url/error-codes) error.
|
|
18
|
+
|
|
19
|
+
Rejecting users with non-matching email domains prevents the impersonation of users in other organizations. This would otherwise be possible since many Identity Providers allow IT admins to create user accounts with _any_ email address, regardless if the IT admin actually controls the email address or its domain.
|
|
20
|
+
|
|
21
|
+
For example, an IT admin of an organization with the domain `foo.com` can create a user account for `user@bar.com` in their Identity Provider and then sign in as that user. If the application were to receive the profile and naively look up the user record using _only_ the email address, then the IT admin will have gained access to the `user@bar.com` account.
|
|
22
|
+
|
|
23
|
+
Since WorkOS cannot guarantee every application handles this scenario correctly, **the default behavior is to reject profiles when its email address does not match the associated organization's domains.**
|
|
24
|
+
|
|
25
|
+
## Allowing any domain
|
|
26
|
+
|
|
27
|
+
Some applications may have organizations whose users sign in using a list of domains that cannot be statically defined, or a set of domains so large as to be cumbersome to configure.
|
|
28
|
+
|
|
29
|
+
A common use-case is non-domain guests. Imagine an organization hires a design consultancy and requires the designers to sign in using the organization's IdP. While the organization can create accounts in their IdP for these guests, they cannot add the designer's domain to the WorkOS organization since they cannot verify ownership of it. The default organization domain verification policy will prevent these designer's from signing in.
|
|
30
|
+
|
|
31
|
+
If your application has a similar use-case, [contact support](mailto:support@workos.com) and we can work with you to relax the default organization domain verification policy. SSO will no longer require any domains to be added to the organization. This change can be made for any of your environments and will affect all organizations in the environment.
|
|
32
|
+
|
|
33
|
+
## Implement profile validation
|
|
34
|
+
|
|
35
|
+
Your application will be responsible for validating the email addresses of users using SSO, and checking the appropriate fields from the SSO profile.
|
|
36
|
+
|
|
37
|
+
Important data from the SSO profile includes the `id` and the `organization_id`. Generally applications will store the Profile `id` alongside its users, such as a column on a `users` table. Similarly, the `organization_id` will be stored on the matching entity, such as a `teams` or `workspace` table; whichever represents a collection of users that are related to each other.
|
|
38
|
+
|
|
39
|
+
```json language="json" title="SSO profile"
|
|
40
|
+
{
|
|
41
|
+
"object": "profile",
|
|
42
|
+
"id": "prof_01DMC79VCBZ0NY2099737PSVF1",
|
|
43
|
+
"connection_id": "conn_01E4ZCR3C56J083X43JQXF3JK5",
|
|
44
|
+
|
|
45
|
+
// Your application should restrict any email-based JIT user
|
|
46
|
+
// provisioning to within the organization that matches this ID.
|
|
47
|
+
"organization_id": "org_01EHWNCE74X7JSDV0X3SZ3KJNY",
|
|
48
|
+
|
|
49
|
+
// Only match based on email or email domain unless if are
|
|
50
|
+
// filtering potential matches by the organization ID above.
|
|
51
|
+
"email": "todd@example.com"
|
|
52
|
+
|
|
53
|
+
// ...
|
|
54
|
+
}
|
|
55
|
+
```
|
|
56
|
+
|
|
57
|
+
Here's a updated version of the WorkOS callback endpoint from the [Quick Start guide](/sso/1-add-sso-to-your-app/add-a-callback-endpoint) with examples of these checks added:
|
|
58
|
+
|
|
59
|
+
```javascript langauge="JavaScript" title="WorkOS callback"
|
|
60
|
+
const { WorkOS } = require('@workos-inc/node');
|
|
61
|
+
const workos = new WorkOS(process.env.WORKOS_API_KEY);
|
|
62
|
+
|
|
63
|
+
app.get('/callback', async (req, res) => {
|
|
64
|
+
const { profile } = await workos.sso.getProfileAndToken({
|
|
65
|
+
code: req.query.code,
|
|
66
|
+
clientId: process.env.WORKOS_CLIENT_ID,
|
|
67
|
+
});
|
|
68
|
+
|
|
69
|
+
// Your application should have a resource that is analogous to the WorkOS
|
|
70
|
+
// organization, like a "team" or "workspace".
|
|
71
|
+
const team = TeamsService.findByWorkOsOrganizationId(profile.organizationId);
|
|
72
|
+
|
|
73
|
+
if (!team) {
|
|
74
|
+
return res.status(401).send({
|
|
75
|
+
message: 'Unauthorized',
|
|
76
|
+
});
|
|
77
|
+
}
|
|
78
|
+
|
|
79
|
+
// Your application should use the Profile ID to determine whether there is an
|
|
80
|
+
// existing user linked to the SSO profile, within the scope of the "team" or
|
|
81
|
+
// "workspace" associated with the WorkOS organization.
|
|
82
|
+
//
|
|
83
|
+
// If none is found, you can then fall back to the `email` address. If one is
|
|
84
|
+
// found you should link the profile ID to the user for subsequent sign-ins.
|
|
85
|
+
//
|
|
86
|
+
// Finally, if no user exists with the email either, you can implement
|
|
87
|
+
// JIT-provisioning and create a new user record, persisting both the `email`
|
|
88
|
+
// and the ID from the profile.
|
|
89
|
+
const { user } = team.users.findOrCreateByWorkOsProfile(profile);
|
|
90
|
+
|
|
91
|
+
// Make sure to verify the user's email address. You may choose to skip
|
|
92
|
+
// email verification in order to improve UX, but should only do so if
|
|
93
|
+
// the new user's email address matches an expected domain for the "team".
|
|
94
|
+
if (!user.emailVerified) {
|
|
95
|
+
res.redirect('/verify-email');
|
|
96
|
+
} else {
|
|
97
|
+
// Start a session for the user.
|
|
98
|
+
// ...
|
|
99
|
+
|
|
100
|
+
res.redirect('/');
|
|
101
|
+
}
|
|
102
|
+
});
|
|
103
|
+
```
|
|
104
|
+
|
|
105
|
+
> The above example makes use of JIT-provisioning, which you can read more about in more our dedicated [JIT-provisioning guide](/sso/jit-provisioning).
|
|
106
|
+
|
|
107
|
+
With the above checks in place, your application can safely sign in and verify users through SSO from any domain.
|
|
108
|
+
|
|
109
|
+
## Custom ACS domains
|
|
110
|
+
|
|
111
|
+
While your users will authenticate with SSO using your application, they might briefly see the WorkOS [ACS URL](/glossary/acs-url). This can be configured in the production environment to a custom domain of your choosing. For more information see the [Custom Domains](/custom-domains) documentation.
|
|
@@ -0,0 +1,46 @@
|
|
|
1
|
+
---
|
|
2
|
+
title: Example Apps
|
|
3
|
+
description: "View sample Single\_Sign-On apps for\_each\_SDK."
|
|
4
|
+
originalPath: .tmp-workos-clone/packages/docs/content/sso/example-apps.mdx
|
|
5
|
+
---
|
|
6
|
+
|
|
7
|
+
You can view minimal example apps that demonstrate how to use the WorkOS SDKs to authenticate users via SSO:
|
|
8
|
+
|
|
9
|
+
<ExampleApps.Root>
|
|
10
|
+
<ExampleApps.Card
|
|
11
|
+
href="https://github.com/workos/node-example-applications/tree/main/node-sso-example"
|
|
12
|
+
title="Node.js SSO app"
|
|
13
|
+
/>
|
|
14
|
+
<ExampleApps.Card
|
|
15
|
+
href="https://github.com/workos/typescript-example-applications/tree/main/typescript-sso-example"
|
|
16
|
+
title="TypeScript SSO app"
|
|
17
|
+
/>
|
|
18
|
+
<ExampleApps.Card
|
|
19
|
+
href="https://github.com/workos/ruby-example-applications/tree/main/ruby-sso-example"
|
|
20
|
+
title="Ruby SSO app"
|
|
21
|
+
/>
|
|
22
|
+
<ExampleApps.Card
|
|
23
|
+
href="https://github.com/workos/python-flask-example-applications/tree/main/python-flask-sso-example"
|
|
24
|
+
title="Python Flask SSO app"
|
|
25
|
+
/>
|
|
26
|
+
<ExampleApps.Card
|
|
27
|
+
href="https://github.com/workos/python-django-example-applications/tree/main/python-django-sso-example"
|
|
28
|
+
title="Python Django SSO app"
|
|
29
|
+
/>
|
|
30
|
+
<ExampleApps.Card
|
|
31
|
+
href="https://github.com/workos/go-example-applications/tree/main/go-sso-example"
|
|
32
|
+
title="Go SSO app"
|
|
33
|
+
/>
|
|
34
|
+
<ExampleApps.Card
|
|
35
|
+
href="https://github.com/workos/java-example-applications/tree/main/java-sso-example"
|
|
36
|
+
title="Java SSO app"
|
|
37
|
+
/>
|
|
38
|
+
<ExampleApps.Card
|
|
39
|
+
href="https://github.com/workos/php-example-applications/tree/main/php-sso-example"
|
|
40
|
+
title="PHP SSO app"
|
|
41
|
+
/>
|
|
42
|
+
<ExampleApps.Card
|
|
43
|
+
href="https://github.com/workos/dotnet-example-applications/tree/main/dotnet-sso-example"
|
|
44
|
+
title=".NET SSO app"
|
|
45
|
+
/>
|
|
46
|
+
</ExampleApps.Root>
|
|
@@ -0,0 +1,113 @@
|
|
|
1
|
+
---
|
|
2
|
+
title: Identity Provider Role Assignment
|
|
3
|
+
description: >-
|
|
4
|
+
Learn how to map role data from identity providers to roles in your app with
|
|
5
|
+
SSO.
|
|
6
|
+
showNextPage: true
|
|
7
|
+
originalPath: >-
|
|
8
|
+
.tmp-workos-clone/packages/docs/content/sso/identity-provider-role-assignment.mdx
|
|
9
|
+
---
|
|
10
|
+
|
|
11
|
+
## Introduction
|
|
12
|
+
|
|
13
|
+
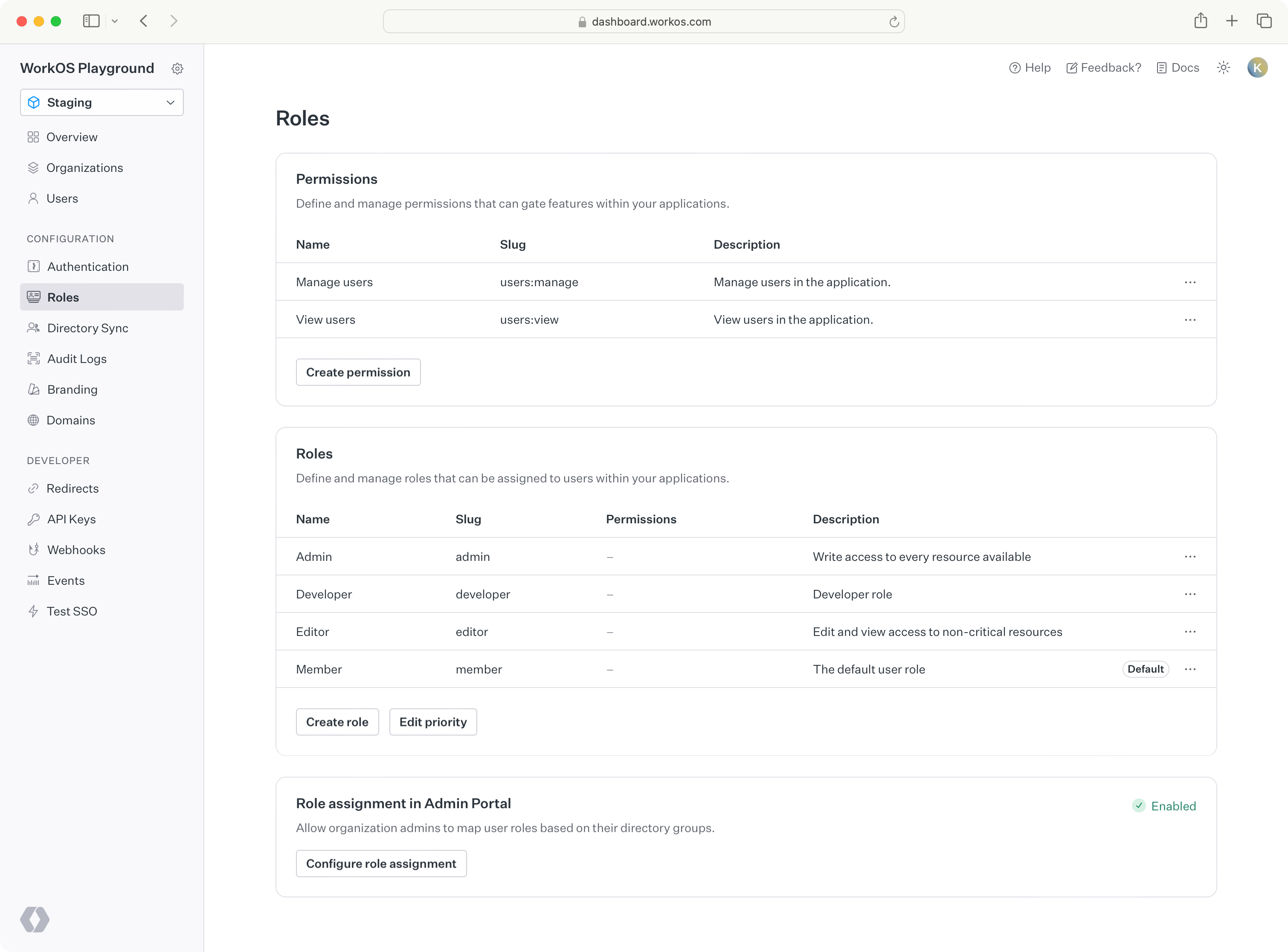
A role represents a logical grouping of permissions, defining access control levels for users within your application. Roles are identified by a unique, immutable slug and are assigned to [SSO user profiles](/reference/sso/profile) through their identity provider group memberships. These group role mappings can be configured on the WorkOS dashboard.
|
|
14
|
+
|
|
15
|
+
## Configure roles
|
|
16
|
+
|
|
17
|
+
You can manage roles in the _Roles & Permissions_ section of the [WorkOS Dashboard](https://dashboard.workos.com/).
|
|
18
|
+
|
|
19
|
+
|
|
20
|
+
|
|
21
|
+
### Default role
|
|
22
|
+
|
|
23
|
+
Role configuration occurs at the environment level. Each environment is seeded with a default `member` role, which is automatically assigned to every new profile. The default role cannot be deleted, but any role can be set as the default.
|
|
24
|
+
|
|
25
|
+
If you need to set default roles or other role configurations at the organization level, refer to the [organization roles](/user-management/roles-and-permissions/organization-roles) documentation.
|
|
26
|
+
|
|
27
|
+
### Priority order
|
|
28
|
+
|
|
29
|
+
Role priority order determines which role is assigned when a user sign-ins with multiple groups that contain conflicting role mappings. In that scenario, the role with the highest priority will be assigned. For example, there might be a case where an employee _Jane_ is an _Engineering Manager_ and belongs to an “Engineering”, “Manager”, and “Admin” group. With group-based role assignment, the user will be assigned the role that has the highest priority defined.
|
|
30
|
+
|
|
31
|
+
### Delete roles
|
|
32
|
+
|
|
33
|
+
When a role is deleted, all SSO user profiles with that role will be granted the default role.
|
|
34
|
+
|
|
35
|
+
> To migrate from one default role to another, set the new default role and delete the old one. SSO user profiles will then receive the new default role at the next sign-in.
|
|
36
|
+
|
|
37
|
+
## SSO group role assignment
|
|
38
|
+
|
|
39
|
+
Users are assigned to groups via the identity provider. Groups usually correspond to roles in your app. Therefore, IT admins will often map a group one-to-one to a role.
|
|
40
|
+
|
|
41
|
+
During authentication, a user's identity provider group memberships can be read via attributes. This enables you to define SSO groups that correspond to IdP groups and set role assignments for those groups in the WorkOS Dashboard.
|
|
42
|
+
|
|
43
|
+
Based on these settings, SSO user profiles returned from WorkOS will include a role attribute that reflects their highest priority group membership. The SSO user profile role is calculated during each sign-in.
|
|
44
|
+
|
|
45
|
+
|
|
46
|
+
|
|
47
|
+
> Supported in both SAML and OIDC-based connection types, except for Okta OIDC. [Reach out to us](mailto:support@workos.com) if you need this for an Okta OIDC connection.
|
|
48
|
+
|
|
49
|
+
### Sample scenario
|
|
50
|
+
|
|
51
|
+
Consider the fictional SaaS company _HireOS_. _HireOS_ has set up an SSO Connection and configured group-based role assignment. For example, a _HireOS_ customer would like to assign their engineering team to the application. The customer’s IT admin would take the following steps:
|
|
52
|
+
|
|
53
|
+
1. Create an “Engineering” group using their identity provider.
|
|
54
|
+
2. Configure the `groups` attribute in their SAML app to return the group memberships.
|
|
55
|
+
3. Provide the developer with the IdP ID for the "Engineering" group.
|
|
56
|
+
|
|
57
|
+
In the WorkOS dashboard, the developer can then assign users of that group to the role "Developer".
|
|
58
|
+
|
|
59
|
+
1. Navigate to the _Connection_ section of the WorkOS dashboard.
|
|
60
|
+
|
|
61
|
+
|
|
62
|
+
|
|
63
|
+
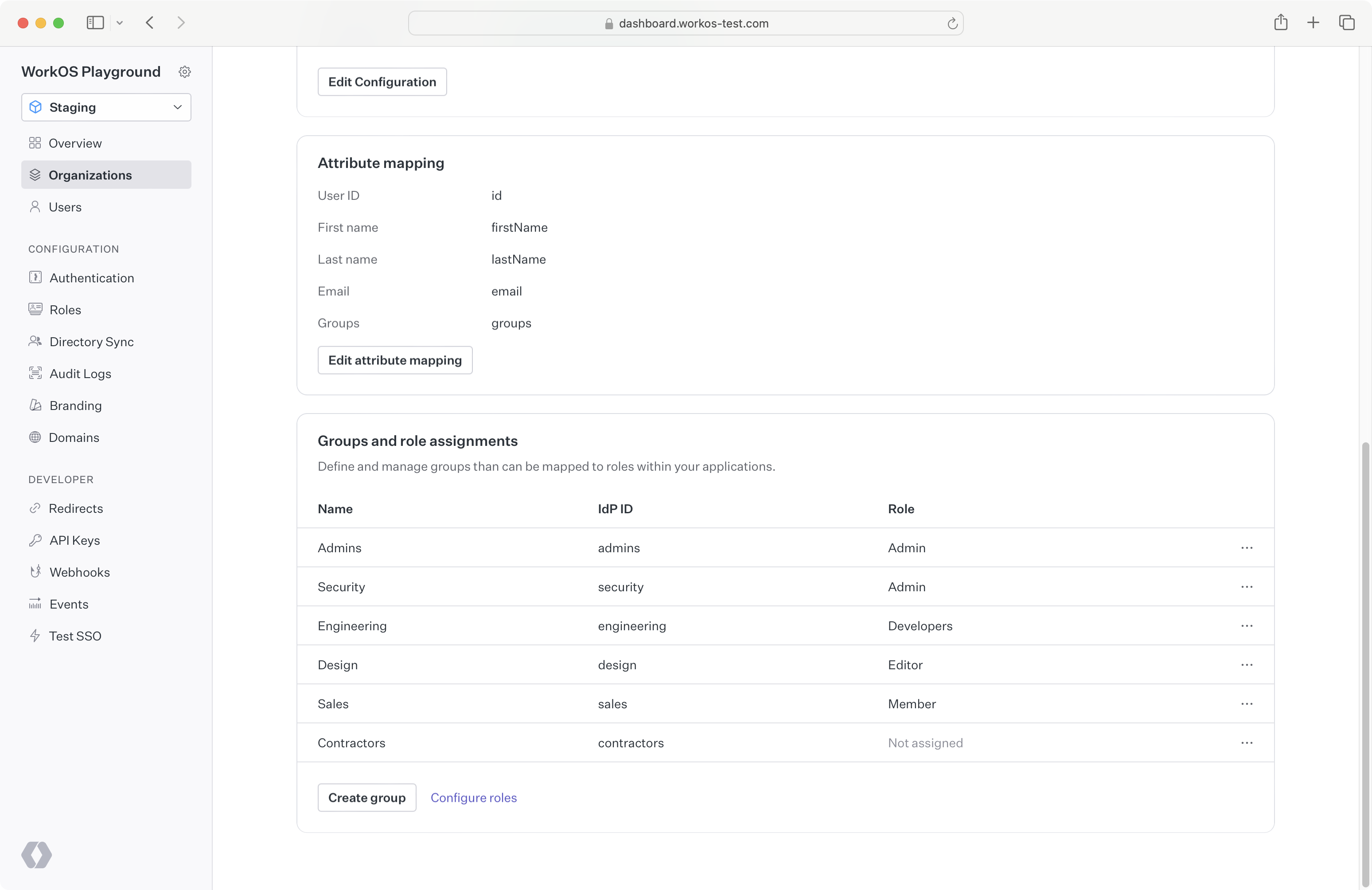
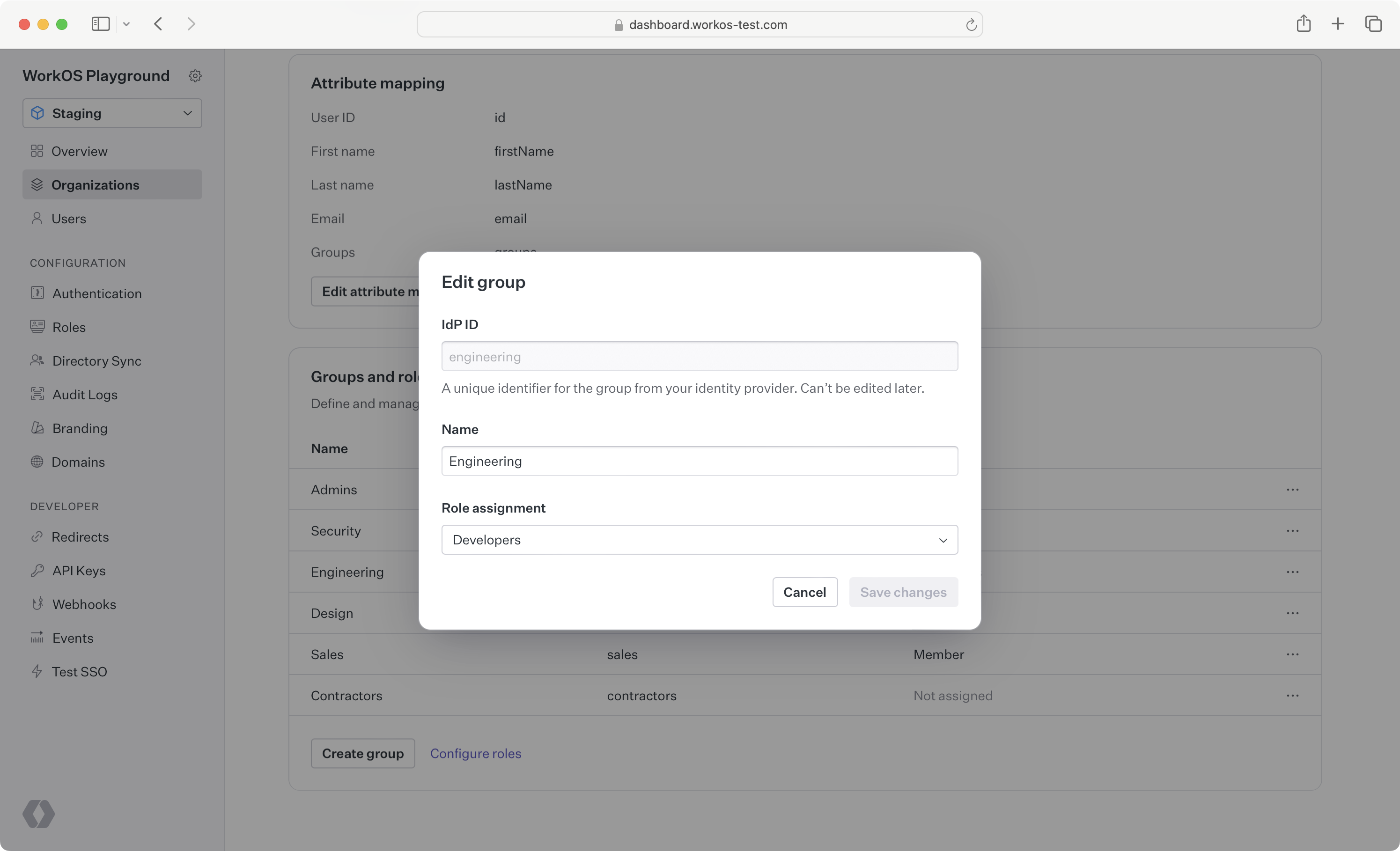
2. Create an SSO group defining the IdP ID for the "Engineering" group. Then, assign this group to the "Developer" role.
|
|
64
|
+
|
|
65
|
+
|
|
66
|
+
|
|
67
|
+
From this point on, whenever a user in the "Engineering" group authenticates via SSO, they will be granted the "Developer” role for that session from the WorkOS API. The role will be returned in the [profile response](/reference/sso/profile).
|
|
68
|
+
|
|
69
|
+
```json language="json" title="SSO user profile"
|
|
70
|
+
{
|
|
71
|
+
"object": "profile",
|
|
72
|
+
"id": "prof_01DMC79VCBZ0NY2099737PSVF1",
|
|
73
|
+
"connection_id": "conn_01E4ZCR3C56J083X43JQXF3JK5",
|
|
74
|
+
"connection_type": "OktaSAML",
|
|
75
|
+
"organization_id": "org_01EHWNCE74X7JSDV0X3SZ3KJNY",
|
|
76
|
+
"email": "todd@example.com",
|
|
77
|
+
"first_name": "Todd",
|
|
78
|
+
"last_name": "Rundgren",
|
|
79
|
+
"idp_id": "00u1a0ufowBJlzPlk357",
|
|
80
|
+
"role": {
|
|
81
|
+
"slug": "developer"
|
|
82
|
+
},
|
|
83
|
+
"raw_attributes": {}
|
|
84
|
+
}
|
|
85
|
+
```
|
|
86
|
+
|
|
87
|
+
> When a user is not a member of any groups or their groups do not match any SSO group role assignments, the user will be granted the [default role](/sso/identity-provider-role-assignment/configure-roles/default-role) in the SSO profile.
|
|
88
|
+
|
|
89
|
+
### Role assignment in Admin Portal
|
|
90
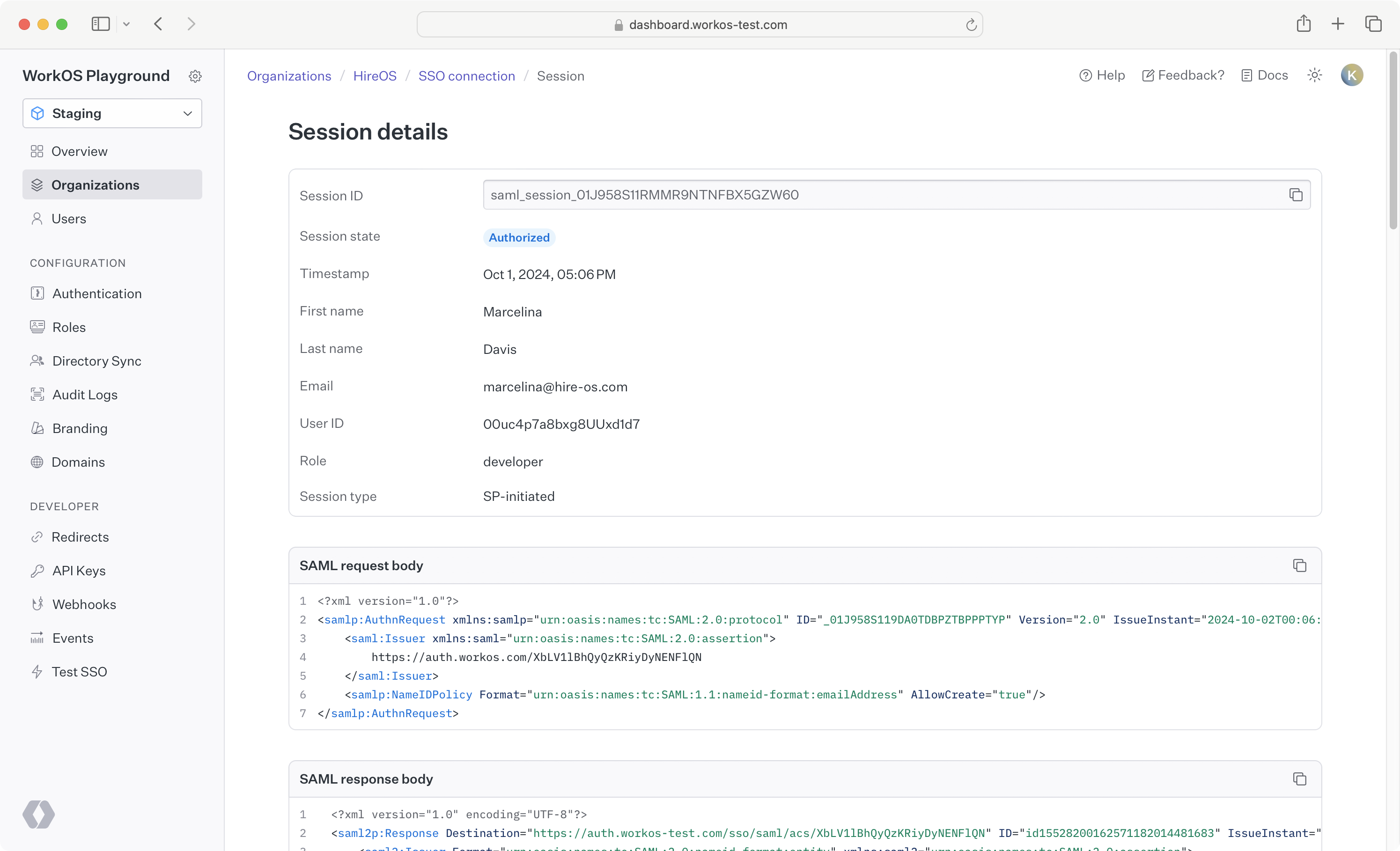
|
+
|
|
91
|
+
Once [roles](/sso/identity-provider-role-assignment/configure-roles) are configured for your application, enable SSO group role assignment in [Admin Portal](/admin-portal) to allow IT admins to assign roles to groups during SSO connection setup. If enabled, all Admin Portal sessions for SSO connections will have the ability to configure and assign roles to groups.
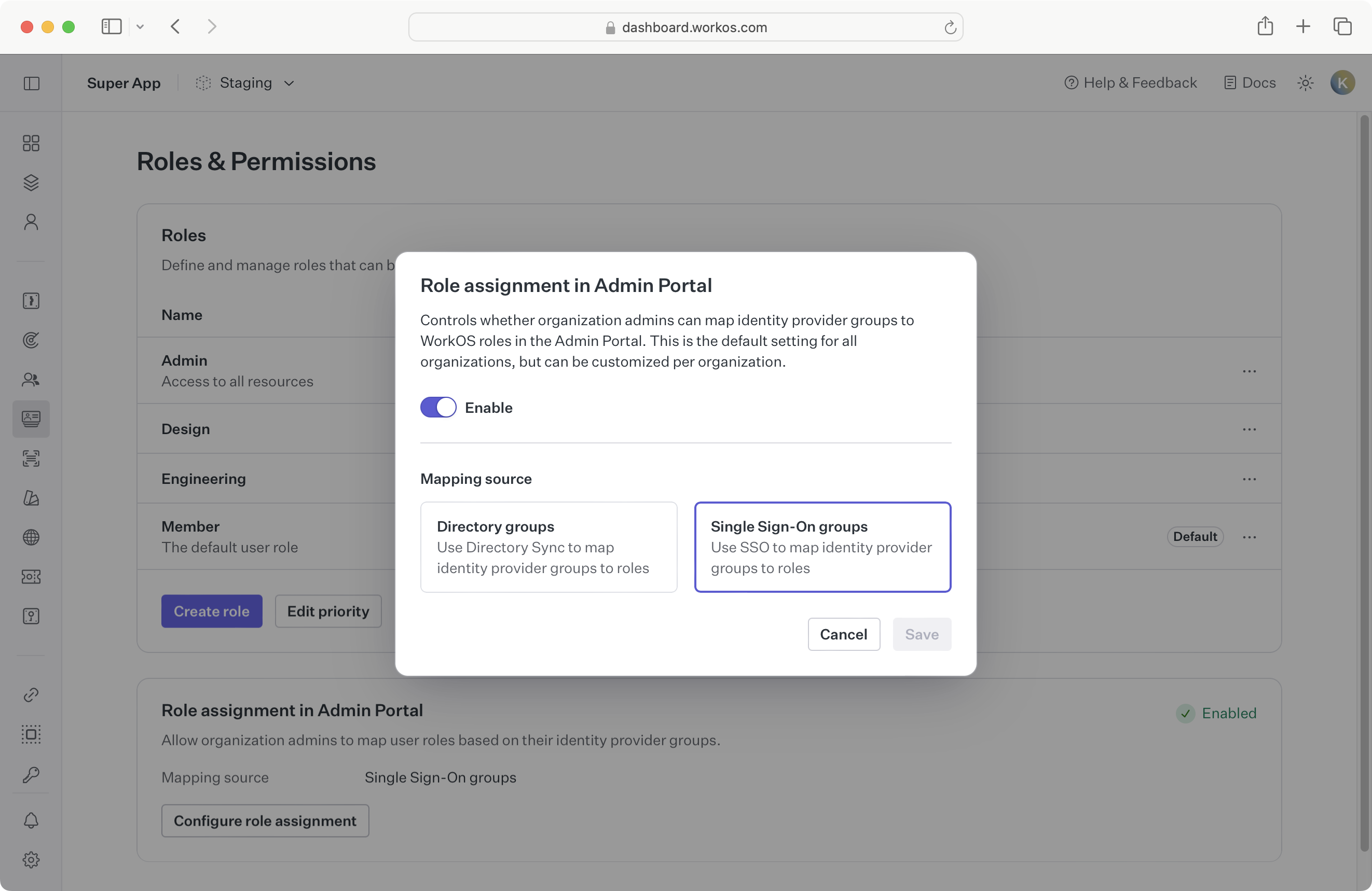
|
|
92
|
+
|
|
93
|
+
|
|
94
|
+
|
|
95
|
+
This is an environment-level setting, but can be configured per organization via the _Roles_ tab under an organization in the WorkOS Dashboard.
|
|
96
|
+
|
|
97
|
+
## Considerations
|
|
98
|
+
|
|
99
|
+
Your customers will store role information in different forms, depending on their preferred provisioning workflow. WorkOS allows for flexibility in how you source role data. However, there are some considerations to keep in mind when using SSO-based connection groups for role assignment.
|
|
100
|
+
|
|
101
|
+
### Drawbacks
|
|
102
|
+
|
|
103
|
+
**Strictly** assigning roles during [JIT user provisioning](/sso/jit-provisioning) has a few caveats:
|
|
104
|
+
|
|
105
|
+
- Your customer must explicitly map the SAML `groups` attribute in the SSO setup so that you can retrieve that attribute in the SSO profile.
|
|
106
|
+
- SSO groups need to be manually defined.
|
|
107
|
+
- Your app will receive updates to this user’s group data only once they sign-in with SSO again. This delay can allow unauthorized users to access resources using a stale role.
|
|
108
|
+
|
|
109
|
+
### Directory group role assignment
|
|
110
|
+
|
|
111
|
+
Directory Sync supports [group-based role assignment](/directory-sync/identity-provider-role-assignment/directory-group-role-assignment) and avoids the pitfalls mentioned above. For organizations with a directory, this method of group-based role assignment is preferred.
|
|
112
|
+
|
|
113
|
+
It’s recommended to use only one method of role assignment—either from a Directory or an SSO Connection—to avoid overlap.
|