@workos/mcp-docs-server 0.1.0 → 0.2.0
This diff represents the content of publicly available package versions that have been released to one of the supported registries. The information contained in this diff is provided for informational purposes only and reflects changes between package versions as they appear in their respective public registries.
- package/.docs/organized/changelogs/workos-platform.json +125 -125
- package/.docs/organized/docs/admin-portal/custom-branding.mdx +2 -4
- package/.docs/organized/docs/admin-portal/example-apps.mdx +11 -11
- package/.docs/organized/docs/admin-portal/index.mdx +39 -33
- package/.docs/organized/docs/audit-logs/admin-portal.mdx +1 -1
- package/.docs/organized/docs/audit-logs/editing-events.mdx +1 -1
- package/.docs/organized/docs/audit-logs/exporting-events.mdx +1 -1
- package/.docs/organized/docs/audit-logs/index.mdx +17 -2
- package/.docs/organized/docs/audit-logs/log-streams.mdx +325 -1
- package/.docs/organized/docs/audit-logs/metadata-schema.mdx +1 -1
- package/.docs/organized/docs/authkit/_navigation.mdx +108 -0
- package/.docs/organized/docs/{user-management → authkit}/actions.mdx +3 -4
- package/.docs/organized/docs/authkit/add-ons/google-analytics.mdx +79 -0
- package/.docs/organized/docs/authkit/add-ons/segment.mdx +77 -0
- package/.docs/organized/docs/authkit/add-ons/stripe.mdx +103 -0
- package/.docs/organized/docs/authkit/api-keys.mdx +99 -0
- package/.docs/organized/docs/{user-management → authkit}/branding.mdx +220 -2
- package/.docs/organized/docs/authkit/cli-auth.mdx +76 -0
- package/.docs/organized/docs/authkit/cli-installer.mdx +157 -0
- package/.docs/organized/docs/authkit/connect/m2m.mdx +65 -0
- package/.docs/organized/docs/authkit/connect/oauth.mdx +88 -0
- package/.docs/organized/docs/authkit/connect/standalone.mdx +179 -0
- package/.docs/organized/docs/authkit/connect.mdx +65 -0
- package/.docs/organized/docs/authkit/custom-email-providers.mdx +141 -0
- package/.docs/organized/docs/{user-management → authkit}/custom-emails.mdx +15 -15
- package/.docs/organized/docs/authkit/directory-provisioning.mdx +89 -0
- package/.docs/organized/docs/{user-management → authkit}/domain-verification.mdx +5 -6
- package/.docs/organized/docs/{user-management → authkit}/email-password.mdx +2 -2
- package/.docs/organized/docs/authkit/email-verification.mdx +31 -0
- package/.docs/organized/docs/{user-management → authkit}/example-apps.mdx +3 -3
- package/.docs/organized/docs/authkit/hosted-ui.mdx +165 -0
- package/.docs/organized/docs/{user-management → authkit}/identity-linking.mdx +9 -9
- package/.docs/organized/docs/{user-management → authkit}/impersonation.mdx +8 -8
- package/.docs/organized/docs/{user-management → authkit}/index.mdx +141 -74
- package/.docs/organized/docs/{user-management → authkit}/invitations.mdx +4 -4
- package/.docs/organized/docs/{user-management → authkit}/invite-only-signup.mdx +3 -3
- package/.docs/organized/docs/authkit/jit-provisioning.mdx +42 -0
- package/.docs/organized/docs/{user-management → authkit}/jwt-templates.mdx +37 -3
- package/.docs/organized/docs/authkit/landing.mdx +22 -0
- package/.docs/organized/docs/{user-management → authkit}/magic-auth.mdx +3 -5
- package/.docs/organized/docs/{user-management → authkit}/mcp.mdx +46 -9
- package/.docs/organized/docs/{user-management → authkit}/metadata.mdx +9 -9
- package/.docs/organized/docs/{user-management → authkit}/mfa.mdx +2 -2
- package/.docs/organized/docs/{user-management → authkit}/migrations.mdx +4 -4
- package/.docs/organized/docs/{user-management → authkit}/modeling-your-app.mdx +11 -11
- package/.docs/organized/docs/{user-management → authkit}/organization-policies.mdx +3 -4
- package/.docs/organized/docs/authkit/overview.mdx +46 -0
- package/.docs/organized/docs/{user-management → authkit}/passkeys.mdx +3 -3
- package/.docs/organized/docs/authkit/pipes.mdx +75 -0
- package/.docs/organized/docs/{user-management → authkit}/radar.mdx +39 -4
- package/.docs/organized/docs/authkit/roles-and-permissions.mdx +208 -0
- package/.docs/organized/docs/{user-management → authkit}/sessions.mdx +32 -20
- package/.docs/organized/docs/{user-management → authkit}/social-login.mdx +16 -2
- package/.docs/organized/docs/{user-management → authkit}/sso-with-contractors.mdx +3 -4
- package/.docs/organized/docs/{user-management → authkit}/sso.mdx +2 -2
- package/.docs/organized/docs/authkit/users-organizations.mdx +107 -0
- package/.docs/organized/docs/custom-domains/admin-portal.mdx +0 -2
- package/.docs/organized/docs/custom-domains/authkit.mdx +0 -2
- package/.docs/organized/docs/custom-domains/email.mdx +2 -2
- package/.docs/organized/docs/deprecations/_navigation.mdx +8 -0
- package/.docs/organized/docs/deprecations/raw-attributes.mdx +136 -0
- package/.docs/organized/docs/directory-sync/attributes.mdx +50 -31
- package/.docs/organized/docs/directory-sync/example-apps.mdx +11 -11
- package/.docs/organized/docs/directory-sync/identity-provider-role-assignment.mdx +23 -26
- package/.docs/organized/docs/directory-sync/index.mdx +4 -2
- package/.docs/organized/docs/directory-sync/quick-start.mdx +3 -3
- package/.docs/organized/docs/directory-sync/understanding-events.mdx +2 -2
- package/.docs/organized/docs/domain-verification/api.mdx +8 -8
- package/.docs/organized/docs/domain-verification/index.mdx +3 -3
- package/.docs/organized/docs/email.mdx +49 -5
- package/.docs/organized/docs/events/data-syncing/events-api.mdx +3 -3
- package/.docs/organized/docs/events/data-syncing/index.mdx +2 -3
- package/.docs/organized/docs/events/data-syncing/webhooks.mdx +4 -4
- package/.docs/organized/docs/events/index.mdx +419 -33
- package/.docs/organized/docs/feature-flags/_navigation.mdx +10 -0
- package/.docs/organized/docs/feature-flags/index.mdx +80 -0
- package/.docs/organized/docs/feature-flags/slack-notifications.mdx +58 -0
- package/.docs/organized/docs/fga/_navigation.mdx +34 -54
- package/.docs/organized/docs/fga/access-checks.mdx +109 -0
- package/.docs/organized/docs/fga/assignments.mdx +124 -0
- package/.docs/organized/docs/fga/authkit-integration.mdx +92 -0
- package/.docs/organized/docs/fga/high-cardinality-entities.mdx +172 -0
- package/.docs/organized/docs/fga/idp-role-assignment.mdx +66 -0
- package/.docs/organized/docs/fga/index.mdx +94 -29
- package/.docs/organized/docs/fga/migration-openfga.mdx +306 -0
- package/.docs/organized/docs/fga/migration-oso.mdx +372 -0
- package/.docs/organized/docs/fga/migration-spicedb.mdx +364 -0
- package/.docs/organized/docs/fga/quick-start.mdx +283 -98
- package/.docs/organized/docs/fga/resource-discovery.mdx +78 -0
- package/.docs/organized/docs/fga/resource-types.mdx +165 -0
- package/.docs/organized/docs/fga/resources.mdx +179 -59
- package/.docs/organized/docs/fga/roles-and-permissions.mdx +122 -0
- package/.docs/organized/docs/fga/standalone-integration.mdx +176 -0
- package/.docs/organized/docs/glossary.mdx +7 -3
- package/.docs/organized/docs/integrations/access-people-hr.mdx +1 -1
- package/.docs/organized/docs/integrations/adp-oidc.mdx +1 -1
- package/.docs/organized/docs/integrations/apple.mdx +112 -69
- package/.docs/organized/docs/integrations/auth0-directory-sync.mdx +3 -1
- package/.docs/organized/docs/integrations/auth0-enterprise-connection.mdx +3 -1
- package/.docs/organized/docs/integrations/auth0-saml.mdx +3 -1
- package/.docs/organized/docs/integrations/bamboohr.mdx +4 -4
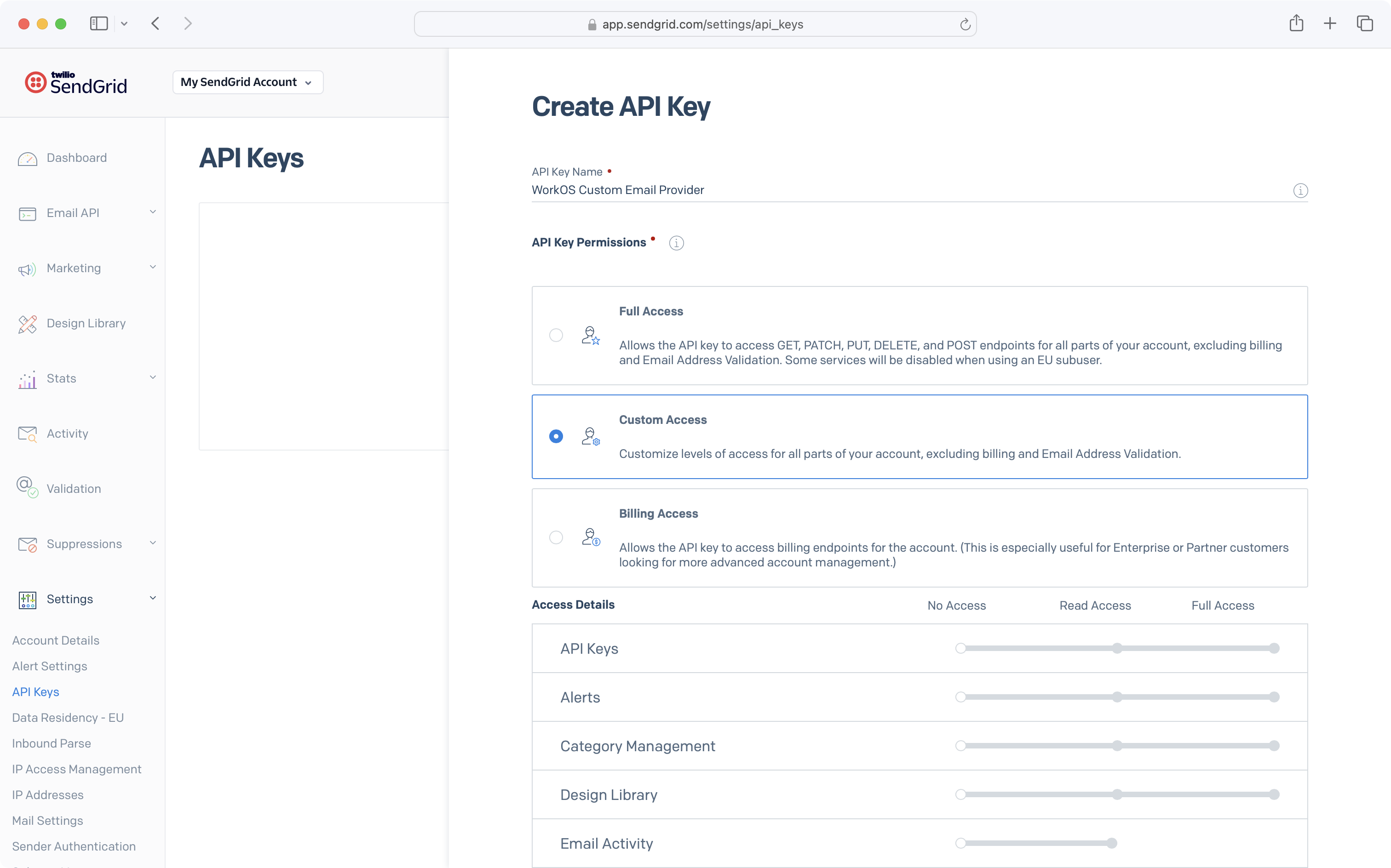
- package/.docs/organized/docs/integrations/breathe-hr.mdx +1 -1
- package/.docs/organized/docs/integrations/bubble.mdx +1 -1
- package/.docs/organized/docs/integrations/cas-saml.mdx +2 -2
- package/.docs/organized/docs/integrations/classlink-saml.mdx +2 -2
- package/.docs/organized/docs/integrations/clever-oidc.mdx +94 -0
- package/.docs/organized/docs/integrations/cloudflare-saml.mdx +35 -2
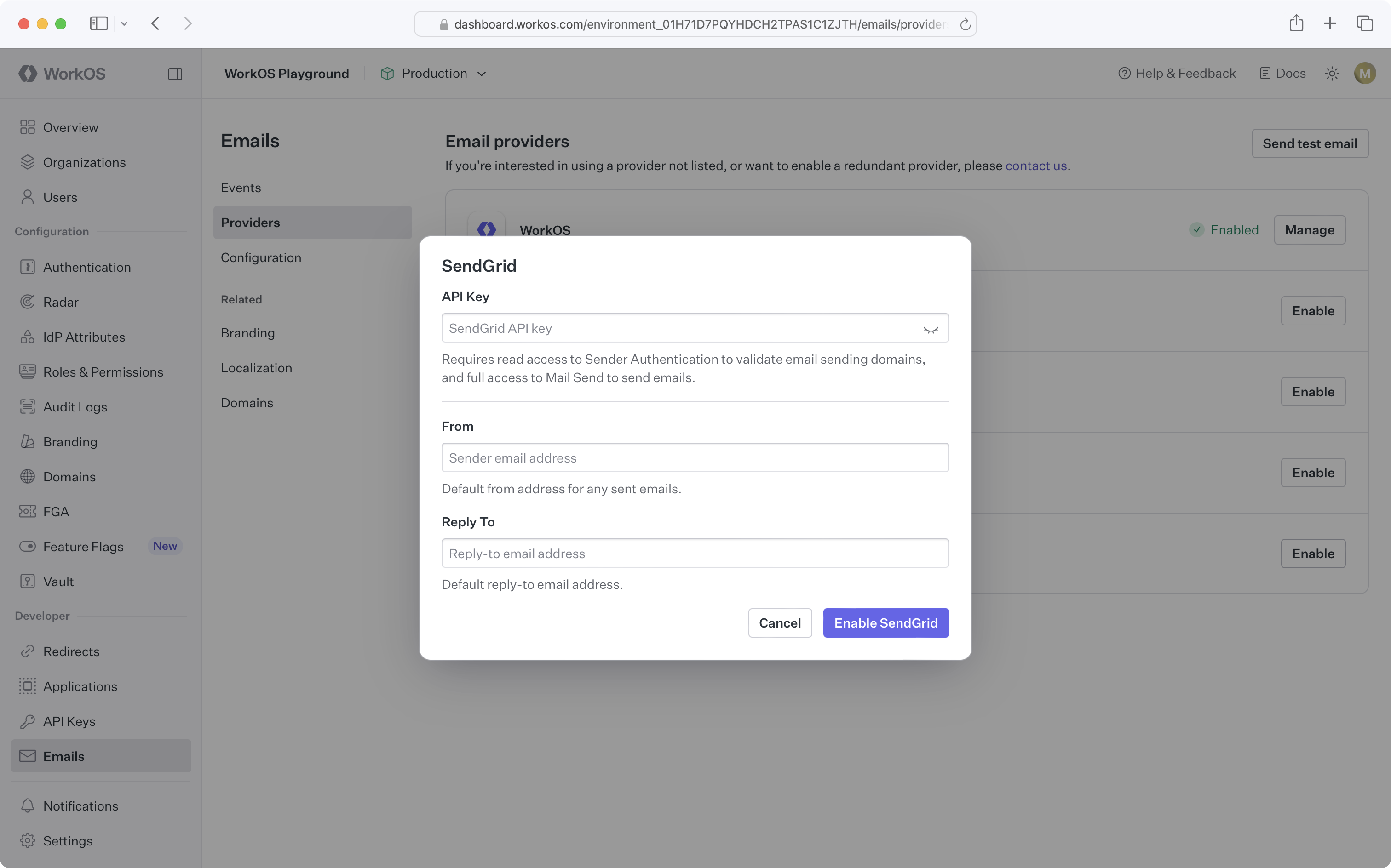
- package/.docs/organized/docs/integrations/cyberark-saml.mdx +2 -2
- package/.docs/organized/docs/integrations/cyberark-scim.mdx +1 -1
- package/.docs/organized/docs/integrations/duo-saml.mdx +2 -2
- package/.docs/organized/docs/integrations/entra-id-oidc.mdx +198 -0
- package/.docs/organized/docs/integrations/entra-id-saml.mdx +3 -3
- package/.docs/organized/docs/integrations/entra-id-scim.mdx +5 -1
- package/.docs/organized/docs/integrations/fourth.mdx +2 -2
- package/.docs/organized/docs/integrations/github-oauth.mdx +80 -33
- package/.docs/organized/docs/integrations/gitlab-oauth.mdx +86 -31
- package/.docs/organized/docs/integrations/google-directory-sync.mdx +5 -1
- package/.docs/organized/docs/integrations/google-oauth.mdx +87 -70
- package/.docs/organized/docs/integrations/google-oidc.mdx +142 -0
- package/.docs/organized/docs/integrations/google-saml.mdx +3 -3
- package/.docs/organized/docs/integrations/hibob.mdx +17 -4
- package/.docs/organized/docs/integrations/intuit-oauth.mdx +128 -0
- package/.docs/organized/docs/integrations/jumpcloud-saml.mdx +2 -2
- package/.docs/organized/docs/integrations/jumpcloud-scim.mdx +5 -1
- package/.docs/organized/docs/integrations/keycloak-saml.mdx +2 -2
- package/.docs/organized/docs/integrations/lastpass-saml.mdx +2 -2
- package/.docs/organized/docs/integrations/linkedin-oauth.mdx +69 -30
- package/.docs/organized/docs/integrations/microsoft-ad-fs-saml.mdx +2 -2
- package/.docs/organized/docs/integrations/microsoft-oauth.mdx +95 -38
- package/.docs/organized/docs/integrations/miniorange-saml.mdx +2 -2
- package/.docs/organized/docs/integrations/net-iq-saml.mdx +2 -2
- package/.docs/organized/docs/integrations/next-auth.mdx +1 -1
- package/.docs/organized/docs/integrations/oidc.mdx +37 -24
- package/.docs/organized/docs/integrations/okta-oidc.mdx +149 -0
- package/.docs/organized/docs/integrations/okta-saml.mdx +3 -3
- package/.docs/organized/docs/integrations/okta-scim.mdx +6 -2
- package/.docs/organized/docs/integrations/onelogin-saml.mdx +2 -2
- package/.docs/organized/docs/integrations/onelogin-scim.mdx +1 -1
- package/.docs/organized/docs/integrations/oracle-saml.mdx +2 -2
- package/.docs/organized/docs/integrations/pingfederate-saml.mdx +2 -2
- package/.docs/organized/docs/integrations/pingfederate-scim.mdx +1 -1
- package/.docs/organized/docs/integrations/pingone-saml.mdx +2 -2
- package/.docs/organized/docs/integrations/rippling-saml.mdx +2 -2
- package/.docs/organized/docs/integrations/rippling-scim.mdx +1 -1
- package/.docs/organized/docs/integrations/sailpoint-scim.mdx +77 -0
- package/.docs/organized/docs/integrations/salesforce-oauth.mdx +116 -0
- package/.docs/organized/docs/integrations/salesforce-saml.mdx +4 -4
- package/.docs/organized/docs/integrations/saml.mdx +43 -23
- package/.docs/organized/docs/integrations/scim.mdx +36 -24
- package/.docs/organized/docs/integrations/sftp.mdx +59 -36
- package/.docs/organized/docs/integrations/shibboleth-generic-saml.mdx +1 -1
- package/.docs/organized/docs/integrations/shibboleth-unsolicited-saml.mdx +1 -1
- package/.docs/organized/docs/integrations/simple-saml-php.mdx +2 -2
- package/.docs/organized/docs/integrations/slack-oauth.mdx +53 -49
- package/.docs/organized/docs/integrations/supabase-authkit.mdx +46 -0
- package/.docs/organized/docs/integrations/{supabase.mdx → supabase-sso.mdx} +6 -4
- package/.docs/organized/docs/integrations/vercel-oauth.mdx +120 -0
- package/.docs/organized/docs/integrations/vmware-saml.mdx +2 -2
- package/.docs/organized/docs/integrations/workday.mdx +1 -1
- package/.docs/organized/docs/integrations/xero-oauth.mdx +77 -32
- package/.docs/organized/docs/magic-link/example-apps.mdx +11 -11
- package/.docs/organized/docs/magic-link/index.mdx +2 -0
- package/.docs/organized/docs/mfa/example-apps.mdx +2 -2
- package/.docs/organized/docs/mfa/index.mdx +2 -2
- package/.docs/organized/docs/mfa/ux/enrollment.mdx +1 -1
- package/.docs/organized/docs/mfa/ux/sign-in.mdx +1 -1
- package/.docs/organized/docs/migrate/_navigation.mdx +21 -1
- package/.docs/organized/docs/migrate/auth0.mdx +5 -5
- package/.docs/organized/docs/migrate/aws-cognito.mdx +5 -5
- package/.docs/organized/docs/migrate/better-auth.mdx +282 -0
- package/.docs/organized/docs/migrate/clerk.mdx +9 -11
- package/.docs/organized/docs/migrate/descope.mdx +290 -0
- package/.docs/organized/docs/migrate/firebase.mdx +4 -4
- package/.docs/organized/docs/migrate/other-services.mdx +25 -6
- package/.docs/organized/docs/migrate/standalone-sso.mdx +14 -14
- package/.docs/organized/docs/migrate/stytch.mdx +363 -0
- package/.docs/organized/docs/migrate/supabase.mdx +255 -0
- package/.docs/organized/docs/on-prem-deployment.mdx +1 -1
- package/.docs/organized/docs/pipes/_navigation.mdx +12 -0
- package/.docs/organized/docs/pipes/index.mdx +75 -0
- package/.docs/organized/docs/pipes/providers.mdx +9 -0
- package/.docs/organized/docs/rbac/_navigation.mdx +16 -0
- package/.docs/organized/docs/rbac/configuration.mdx +80 -0
- package/.docs/organized/docs/rbac/idp-role-assignment.mdx +79 -0
- package/.docs/organized/docs/rbac/index.mdx +24 -0
- package/.docs/organized/docs/rbac/integration.mdx +59 -0
- package/.docs/organized/docs/rbac/organization-roles.mdx +38 -0
- package/.docs/organized/docs/rbac/quick-start.mdx +52 -0
- package/.docs/organized/docs/reference/_navigation.mdx +437 -284
- package/.docs/organized/docs/reference/admin-portal/portal-link/index.mdx +1 -1
- package/.docs/organized/docs/reference/admin-portal/provider-icons/index.mdx +3 -3
- package/.docs/organized/docs/reference/{api-keys.mdx → api-authentication/index.mdx} +3 -3
- package/.docs/organized/docs/reference/audit-logs/configuration/index.mdx +97 -0
- package/.docs/organized/docs/reference/audit-logs/{create-event.mdx → event/create.mdx} +12 -2
- package/.docs/organized/docs/reference/audit-logs/event/index.mdx +92 -0
- package/.docs/organized/docs/reference/audit-logs/{create-export.mdx → export/create.mdx} +1 -1
- package/.docs/organized/docs/reference/audit-logs/{get-export.mdx → export/get.mdx} +1 -1
- package/.docs/organized/docs/reference/audit-logs/{audit-log-export.mdx → export/index.mdx} +11 -12
- package/.docs/organized/docs/reference/audit-logs/{get-retention.mdx → retention/get.mdx} +1 -1
- package/.docs/organized/docs/reference/audit-logs/retention/index.mdx +25 -0
- package/.docs/organized/docs/reference/audit-logs/{set-retention.mdx → retention/set.mdx} +1 -1
- package/.docs/organized/docs/reference/audit-logs/{create-schema.mdx → schema/create.mdx} +1 -1
- package/.docs/organized/docs/reference/audit-logs/{audit-log-schema.mdx → schema/index.mdx} +5 -6
- package/.docs/organized/docs/reference/audit-logs/{list-actions.mdx → schema/list-actions.mdx} +2 -1
- package/.docs/organized/docs/reference/audit-logs/{list-schemas.mdx → schema/list.mdx} +1 -1
- package/.docs/organized/docs/reference/authkit/api-keys/create-for-organization.mdx +40 -0
- package/.docs/organized/docs/reference/authkit/api-keys/delete.mdx +23 -0
- package/.docs/organized/docs/reference/authkit/api-keys/index.mdx +275 -0
- package/.docs/organized/docs/reference/authkit/api-keys/list-for-organization.mdx +41 -0
- package/.docs/organized/docs/reference/authkit/api-keys/validate.mdx +77 -0
- package/.docs/organized/docs/reference/{user-management → authkit}/authentication/code.mdx +138 -18
- package/.docs/organized/docs/reference/{user-management → authkit}/authentication/email-verification.mdx +10 -10
- package/.docs/organized/docs/reference/{user-management → authkit}/authentication/get-authorization-url/error-codes.mdx +3 -3
- package/.docs/organized/docs/reference/{user-management → authkit}/authentication/get-authorization-url/index.mdx +64 -17
- package/.docs/organized/docs/reference/{user-management → authkit}/authentication/get-authorization-url/pkce.mdx +2 -2
- package/.docs/organized/docs/reference/authkit/authentication/get-authorization-url/redirect-uri.mdx +47 -0
- package/.docs/organized/docs/reference/{user-management → authkit}/authentication/index.mdx +19 -11
- package/.docs/organized/docs/reference/{user-management → authkit}/authentication/magic-auth.mdx +9 -9
- package/.docs/organized/docs/reference/{user-management → authkit}/authentication/organization-selection.mdx +9 -9
- package/.docs/organized/docs/reference/{user-management → authkit}/authentication/password.mdx +8 -8
- package/.docs/organized/docs/reference/{user-management → authkit}/authentication/refresh-and-seal-session-data.mdx +3 -3
- package/.docs/organized/docs/reference/{user-management → authkit}/authentication/refresh-token.mdx +17 -17
- package/.docs/organized/docs/reference/{user-management → authkit}/authentication/session-cookie.mdx +7 -3
- package/.docs/organized/docs/reference/{user-management → authkit}/authentication/totp.mdx +10 -10
- package/.docs/organized/docs/reference/{user-management → authkit}/authentication-errors/email-verification-required-error.mdx +3 -3
- package/.docs/organized/docs/reference/{user-management → authkit}/authentication-errors/index.mdx +1 -3
- package/.docs/organized/docs/reference/{user-management → authkit}/authentication-errors/mfa-challenge-error.mdx +3 -3
- package/.docs/organized/docs/reference/{user-management → authkit}/authentication-errors/mfa-enrollment-error.mdx +3 -3
- package/.docs/organized/docs/reference/{user-management → authkit}/authentication-errors/organization-authentication-required-error.mdx +3 -3
- package/.docs/organized/docs/reference/{user-management → authkit}/authentication-errors/organization-selection-error.mdx +3 -4
- package/.docs/organized/docs/reference/{user-management → authkit}/authentication-errors/sso-required-error.mdx +3 -3
- package/.docs/organized/docs/reference/authkit/cli-auth/device-authorization.mdx +61 -0
- package/.docs/organized/docs/reference/authkit/cli-auth/device-code.mdx +57 -0
- package/.docs/organized/docs/reference/authkit/cli-auth/error-codes.mdx +31 -0
- package/.docs/organized/docs/reference/authkit/cli-auth/index.mdx +22 -0
- package/.docs/organized/docs/reference/{user-management → authkit}/email-verification/get.mdx +8 -8
- package/.docs/organized/docs/reference/{user-management → authkit}/email-verification/index.mdx +9 -11
- package/.docs/organized/docs/reference/{user-management → authkit}/identity/index.mdx +6 -9
- package/.docs/organized/docs/reference/{user-management → authkit}/identity/list.mdx +5 -6
- package/.docs/organized/docs/reference/authkit/index.mdx +13 -0
- package/.docs/organized/docs/reference/{user-management → authkit}/invitation/accept.mdx +5 -5
- package/.docs/organized/docs/reference/{user-management → authkit}/invitation/find-by-token.mdx +8 -8
- package/.docs/organized/docs/reference/{user-management → authkit}/invitation/get.mdx +8 -9
- package/.docs/organized/docs/reference/{user-management → authkit}/invitation/index.mdx +10 -15
- package/.docs/organized/docs/reference/{user-management → authkit}/invitation/list.mdx +10 -11
- package/.docs/organized/docs/reference/authkit/invitation/resend.mdx +109 -0
- package/.docs/organized/docs/reference/{user-management → authkit}/invitation/revoke.mdx +8 -8
- package/.docs/organized/docs/reference/{user-management → authkit}/invitation/send.mdx +23 -13
- package/.docs/organized/docs/reference/{user-management → authkit}/logout/get-logout-url-from-session-cookie.mdx +2 -2
- package/.docs/organized/docs/reference/{user-management → authkit}/logout/get-logout-url.mdx +8 -8
- package/.docs/organized/docs/reference/{user-management → authkit}/logout/index.mdx +4 -5
- package/.docs/organized/docs/reference/{user-management → authkit}/magic-auth/create.mdx +10 -10
- package/.docs/organized/docs/reference/{user-management → authkit}/magic-auth/get.mdx +9 -10
- package/.docs/organized/docs/reference/{user-management → authkit}/magic-auth/index.mdx +10 -15
- package/.docs/organized/docs/reference/{user-management → authkit}/mfa/authentication-challenge.mdx +9 -10
- package/.docs/organized/docs/reference/{user-management → authkit}/mfa/authentication-factor.mdx +11 -11
- package/.docs/organized/docs/reference/{user-management → authkit}/mfa/enroll-auth-factor.mdx +19 -15
- package/.docs/organized/docs/reference/authkit/mfa/index.mdx +11 -0
- package/.docs/organized/docs/reference/{user-management → authkit}/mfa/list-auth-factors.mdx +9 -9
- package/.docs/organized/docs/reference/{user-management → authkit}/organization-membership/create.mdx +27 -10
- package/.docs/organized/docs/reference/{user-management → authkit}/organization-membership/deactivate.mdx +10 -10
- package/.docs/organized/docs/reference/{user-management → authkit}/organization-membership/delete.mdx +8 -8
- package/.docs/organized/docs/reference/{user-management → authkit}/organization-membership/get.mdx +8 -8
- package/.docs/organized/docs/reference/{user-management → authkit}/organization-membership/index.mdx +107 -14
- package/.docs/organized/docs/reference/{user-management → authkit}/organization-membership/list.mdx +10 -10
- package/.docs/organized/docs/reference/{user-management → authkit}/organization-membership/reactivate.mdx +11 -11
- package/.docs/organized/docs/reference/{user-management → authkit}/organization-membership/update.mdx +25 -9
- package/.docs/organized/docs/reference/{user-management → authkit}/password-reset/create.mdx +8 -8
- package/.docs/organized/docs/reference/{user-management → authkit}/password-reset/get.mdx +8 -8
- package/.docs/organized/docs/reference/{user-management → authkit}/password-reset/index.mdx +10 -12
- package/.docs/organized/docs/reference/{user-management → authkit}/password-reset/reset-password.mdx +8 -8
- package/.docs/organized/docs/reference/authkit/session/index.mdx +128 -0
- package/.docs/organized/docs/reference/authkit/session/list.mdx +110 -0
- package/.docs/organized/docs/reference/authkit/session/revoke.mdx +73 -0
- package/.docs/organized/docs/reference/{user-management → authkit}/session-helpers/authenticate.mdx +22 -6
- package/.docs/organized/docs/reference/{user-management → authkit}/session-helpers/get-logout-url.mdx +5 -5
- package/.docs/organized/docs/reference/{user-management → authkit}/session-helpers/index.mdx +2 -2
- package/.docs/organized/docs/reference/{user-management → authkit}/session-helpers/load-sealed-session.mdx +4 -4
- package/.docs/organized/docs/reference/{user-management → authkit}/session-helpers/refresh.mdx +18 -6
- package/.docs/organized/docs/reference/{user-management → authkit}/session-tokens/access-token.mdx +16 -8
- package/.docs/organized/docs/reference/authkit/session-tokens/index.mdx +5 -0
- package/.docs/organized/docs/reference/{user-management → authkit}/session-tokens/jwks.mdx +8 -8
- package/.docs/organized/docs/reference/authkit/session-tokens/refresh-token.mdx +8 -0
- package/.docs/organized/docs/reference/{user-management → authkit}/user/create.mdx +36 -17
- package/.docs/organized/docs/reference/{user-management → authkit}/user/delete.mdx +8 -9
- package/.docs/organized/docs/reference/{user-management → authkit}/user/get-by-external-id.mdx +16 -4
- package/.docs/organized/docs/reference/{user-management → authkit}/user/get.mdx +8 -8
- package/.docs/organized/docs/reference/{user-management → authkit}/user/index.mdx +25 -15
- package/.docs/organized/docs/reference/{user-management → authkit}/user/list.mdx +9 -12
- package/.docs/organized/docs/reference/{user-management → authkit}/user/update.mdx +43 -20
- package/.docs/organized/docs/reference/{client-libraries.mdx → client-libraries/index.mdx} +2 -2
- package/.docs/organized/docs/reference/directory-sync/directory/index.mdx +1 -1
- package/.docs/organized/docs/reference/directory-sync/directory-group/index.mdx +1 -24
- package/.docs/organized/docs/reference/directory-sync/directory-user/index.mdx +1 -29
- package/.docs/organized/docs/reference/directory-sync/directory-user/list.mdx +1 -1
- package/.docs/organized/docs/reference/directory-sync/index.mdx +1 -1
- package/.docs/organized/docs/reference/domain-verification/create.mdx +35 -0
- package/.docs/organized/docs/reference/domain-verification/delete.mdx +55 -0
- package/.docs/organized/docs/reference/domain-verification/get.mdx +29 -0
- package/.docs/organized/docs/reference/domain-verification/index.mdx +57 -1
- package/.docs/organized/docs/reference/domain-verification/verify.mdx +29 -0
- package/.docs/organized/docs/reference/{errors.mdx → errors/index.mdx} +1 -1
- package/.docs/organized/docs/reference/events/list.mdx +5 -4
- package/.docs/organized/docs/reference/feature-flags/flag/disable.mdx +33 -0
- package/.docs/organized/docs/reference/feature-flags/flag/enable.mdx +33 -0
- package/.docs/organized/docs/reference/feature-flags/flag/get.mdx +32 -0
- package/.docs/organized/docs/reference/feature-flags/flag/index.mdx +116 -0
- package/.docs/organized/docs/reference/feature-flags/flag/list.mdx +67 -0
- package/.docs/organized/docs/reference/feature-flags/index.mdx +123 -0
- package/.docs/organized/docs/reference/feature-flags/targeting/add.mdx +43 -0
- package/.docs/organized/docs/reference/feature-flags/targeting/index.mdx +23 -0
- package/.docs/organized/docs/reference/feature-flags/targeting/list-for-organization.mdx +132 -0
- package/.docs/organized/docs/reference/feature-flags/targeting/list-for-user.mdx +94 -0
- package/.docs/organized/docs/reference/feature-flags/targeting/remove.mdx +43 -0
- package/.docs/organized/docs/reference/fga/access-check/check.mdx +102 -0
- package/.docs/organized/docs/reference/fga/access-check/index.mdx +6 -0
- package/.docs/organized/docs/reference/fga/access-check/list-memberships-by-external-id.mdx +143 -0
- package/.docs/organized/docs/reference/fga/access-check/list-memberships.mdx +127 -0
- package/.docs/organized/docs/reference/fga/access-check/list-resources.mdx +152 -0
- package/.docs/organized/docs/reference/fga/index.mdx +14 -2
- package/.docs/organized/docs/reference/fga/resource/create.mdx +74 -88
- package/.docs/organized/docs/reference/fga/resource/delete-by-external-id.mdx +78 -0
- package/.docs/organized/docs/reference/fga/resource/delete.mdx +38 -62
- package/.docs/organized/docs/reference/fga/resource/get-by-external-id.mdx +60 -0
- package/.docs/organized/docs/reference/fga/resource/get.mdx +15 -63
- package/.docs/organized/docs/reference/fga/resource/index.mdx +74 -73
- package/.docs/organized/docs/reference/fga/resource/list.mdx +90 -131
- package/.docs/organized/docs/reference/fga/resource/update-by-external-id.mdx +81 -0
- package/.docs/organized/docs/reference/fga/resource/update.mdx +29 -85
- package/.docs/organized/docs/reference/fga/role-assignment/create.mdx +89 -0
- package/.docs/organized/docs/reference/fga/role-assignment/delete-by-id.mdx +59 -0
- package/.docs/organized/docs/reference/fga/role-assignment/delete.mdx +90 -0
- package/.docs/organized/docs/reference/fga/role-assignment/index.mdx +106 -0
- package/.docs/organized/docs/reference/fga/role-assignment/list.mdx +86 -0
- package/.docs/organized/docs/reference/index.mdx +21 -12
- package/.docs/organized/docs/reference/magic-link/passwordless-session/index.mdx +1 -1
- package/.docs/organized/docs/reference/mfa/{challenge-factor.mdx → challenge/create.mdx} +1 -1
- package/.docs/organized/docs/reference/mfa/{authentication-challenge.mdx → challenge/index.mdx} +11 -14
- package/.docs/organized/docs/reference/mfa/{verify-challenge.mdx → challenge/verify.mdx} +10 -12
- package/.docs/organized/docs/reference/mfa/{delete-factor.mdx → factor/delete.mdx} +1 -1
- package/.docs/organized/docs/reference/mfa/{enroll-factor.mdx → factor/enroll.mdx} +1 -1
- package/.docs/organized/docs/reference/mfa/{get-factor.mdx → factor/get.mdx} +1 -1
- package/.docs/organized/docs/reference/mfa/{authentication-factor.mdx → factor/index.mdx} +11 -12
- package/.docs/organized/docs/reference/organization/create.mdx +1 -6
- package/.docs/organized/docs/reference/organization/get-by-external-id.mdx +1 -1
- package/.docs/organized/docs/reference/organization/index.mdx +5 -5
- package/.docs/organized/docs/reference/organization/update.mdx +1 -1
- package/.docs/organized/docs/reference/{pagination.mdx → pagination/index.mdx} +1 -3
- package/.docs/organized/docs/reference/pipes/access-token/get.mdx +174 -0
- package/.docs/organized/docs/reference/pipes/access-token/index.mdx +44 -0
- package/.docs/organized/docs/reference/pipes/connected-account/delete.mdx +42 -0
- package/.docs/organized/docs/reference/pipes/connected-account/get-authorize-url.mdx +49 -0
- package/.docs/organized/docs/reference/pipes/connected-account/get.mdx +42 -0
- package/.docs/organized/docs/reference/pipes/connected-account/index.mdx +69 -0
- package/.docs/organized/docs/reference/pipes/index.mdx +8 -0
- package/.docs/organized/docs/reference/pipes/provider/index.mdx +70 -0
- package/.docs/organized/docs/reference/pipes/provider/list.mdx +47 -0
- package/.docs/organized/docs/reference/radar/attempts/index.mdx +1 -1
- package/.docs/organized/docs/reference/radar/lists/index.mdx +1 -1
- package/.docs/organized/docs/reference/rate-limits/index.mdx +56 -0
- package/.docs/organized/docs/reference/roles/index.mdx +12 -262
- package/.docs/organized/docs/reference/roles/organization-role/add-permission.mdx +75 -0
- package/.docs/organized/docs/reference/roles/organization-role/create.mdx +95 -0
- package/.docs/organized/docs/reference/roles/organization-role/delete.mdx +47 -0
- package/.docs/organized/docs/reference/roles/organization-role/get.mdx +55 -0
- package/.docs/organized/docs/reference/roles/organization-role/index.mdx +148 -0
- package/.docs/organized/docs/reference/roles/organization-role/list.mdx +68 -0
- package/.docs/organized/docs/reference/roles/organization-role/remove-permission.mdx +68 -0
- package/.docs/organized/docs/reference/roles/organization-role/set-permissions.mdx +79 -0
- package/.docs/organized/docs/reference/roles/organization-role/update.mdx +85 -0
- package/.docs/organized/docs/reference/roles/permission/create.mdx +101 -0
- package/.docs/organized/docs/reference/roles/permission/delete.mdx +38 -0
- package/.docs/organized/docs/reference/roles/permission/get.mdx +45 -0
- package/.docs/organized/docs/reference/roles/permission/index.mdx +128 -0
- package/.docs/organized/docs/reference/roles/permission/list.mdx +91 -0
- package/.docs/organized/docs/reference/roles/permission/update.mdx +80 -0
- package/.docs/organized/docs/reference/roles/role/add-permission.mdx +63 -0
- package/.docs/organized/docs/reference/roles/role/create.mdx +103 -0
- package/.docs/organized/docs/reference/roles/role/get.mdx +52 -0
- package/.docs/organized/docs/reference/roles/role/index.mdx +135 -0
- package/.docs/organized/docs/reference/roles/role/list.mdx +56 -0
- package/.docs/organized/docs/reference/roles/role/set-permissions.mdx +67 -0
- package/.docs/organized/docs/reference/roles/role/update.mdx +78 -0
- package/.docs/organized/docs/reference/sso/connection/index.mdx +2 -2
- package/.docs/organized/docs/reference/sso/get-authorization-url/error-codes.mdx +5 -3
- package/.docs/organized/docs/reference/sso/get-authorization-url/index.mdx +24 -2
- package/.docs/organized/docs/reference/sso/get-authorization-url/redirect-uri.mdx +25 -1
- package/.docs/organized/docs/reference/sso/index.mdx +1 -1
- package/.docs/organized/docs/reference/sso/logout/authorize.mdx +0 -1
- package/.docs/organized/docs/reference/sso/logout/index.mdx +1 -2
- package/.docs/organized/docs/reference/sso/logout/redirect.mdx +0 -1
- package/.docs/organized/docs/reference/sso/profile/get-profile-and-token.mdx +13 -1
- package/.docs/organized/docs/reference/sso/profile/index.mdx +25 -24
- package/.docs/organized/docs/reference/{testing.mdx → testing/index.mdx} +1 -1
- package/.docs/organized/docs/reference/vault/key/create-data-key.mdx +29 -0
- package/.docs/organized/docs/reference/vault/key/decrypt-data-key.mdx +20 -0
- package/.docs/organized/docs/reference/vault/key/decrypt-data.mdx +24 -0
- package/.docs/organized/docs/reference/vault/key/encrypt-data.mdx +20 -0
- package/.docs/organized/docs/reference/vault/object/create.mdx +17 -0
- package/.docs/organized/docs/reference/vault/object/delete.mdx +12 -0
- package/.docs/organized/docs/reference/vault/object/get-by-name.mdx +61 -0
- package/.docs/organized/docs/reference/vault/object/get.mdx +11 -0
- package/.docs/organized/docs/reference/vault/object/index.mdx +50 -4
- package/.docs/organized/docs/reference/vault/object/list.mdx +40 -1
- package/.docs/organized/docs/reference/vault/object/update.mdx +18 -0
- package/.docs/organized/docs/reference/vault/object/version.mdx +15 -2
- package/.docs/organized/docs/reference/vault/object/versions.mdx +13 -0
- package/.docs/organized/docs/reference/widgets/get-token.mdx +8 -5
- package/.docs/organized/docs/reference/workos-connect/applications/client-secrets/create.mdx +55 -0
- package/.docs/organized/docs/reference/workos-connect/applications/client-secrets/delete.mdx +28 -0
- package/.docs/organized/docs/reference/workos-connect/applications/client-secrets/index.mdx +60 -0
- package/.docs/organized/docs/reference/workos-connect/applications/client-secrets/list.mdx +52 -0
- package/.docs/organized/docs/reference/workos-connect/applications/create.mdx +79 -0
- package/.docs/organized/docs/reference/workos-connect/applications/delete.mdx +28 -0
- package/.docs/organized/docs/reference/workos-connect/applications/get.mdx +59 -0
- package/.docs/organized/docs/reference/workos-connect/applications/index.mdx +40 -0
- package/.docs/organized/docs/reference/workos-connect/applications/list.mdx +49 -0
- package/.docs/organized/docs/reference/workos-connect/applications/m2m.mdx +52 -0
- package/.docs/organized/docs/reference/workos-connect/applications/oauth.mdx +85 -0
- package/.docs/organized/docs/reference/workos-connect/applications/update.mdx +59 -0
- package/.docs/organized/docs/reference/workos-connect/authorize/index.mdx +29 -1
- package/.docs/organized/docs/reference/workos-connect/cli-auth/authorize-device/index.mdx +81 -0
- package/.docs/organized/docs/reference/workos-connect/cli-auth/device-code-grant.mdx +74 -0
- package/.docs/organized/docs/reference/workos-connect/cli-auth/index.mdx +23 -0
- package/.docs/organized/docs/reference/workos-connect/index.mdx +1 -1
- package/.docs/organized/docs/reference/workos-connect/introspection/index.mdx +8 -3
- package/.docs/organized/docs/reference/workos-connect/metadata/index.mdx +1 -1
- package/.docs/organized/docs/reference/workos-connect/metadata/oauth-authorization-server/index.mdx +1 -1
- package/.docs/organized/docs/reference/workos-connect/standalone/complete.mdx +68 -0
- package/.docs/organized/docs/reference/workos-connect/standalone/index.mdx +9 -0
- package/.docs/organized/docs/reference/workos-connect/standalone/user-consent-options.mdx +41 -0
- package/.docs/organized/docs/reference/workos-connect/token/authorization-code-grant/access-token.mdx +6 -0
- package/.docs/organized/docs/reference/workos-connect/token/authorization-code-grant/id-token.mdx +1 -1
- package/.docs/organized/docs/reference/workos-connect/token/{authorization-code-grant/index.mdx → authorization-code-grant.mdx} +23 -2
- package/.docs/organized/docs/reference/workos-connect/token/client-credentials-grant/access-token.mdx +1 -1
- package/.docs/organized/docs/reference/workos-connect/token/{client-credentials-grant/index.mdx → client-credentials-grant.mdx} +2 -2
- package/.docs/organized/docs/reference/workos-connect/token/index.mdx +5 -4
- package/.docs/organized/docs/reference/workos-connect/token/refresh-token-grant.mdx +1 -1
- package/.docs/organized/docs/reference/workos-connect/userinfo/index.mdx +2 -2
- package/.docs/organized/docs/sdks/authkit-js.mdx +14 -0
- package/.docs/organized/docs/sdks/authkit-nextjs.mdx +14 -0
- package/.docs/organized/docs/sdks/authkit-react-router.mdx +14 -0
- package/.docs/organized/docs/sdks/authkit-react.mdx +14 -0
- package/.docs/organized/docs/sdks/authkit-remix.mdx +14 -0
- package/.docs/organized/docs/sdks/authkit-tanstack-start.mdx +14 -0
- package/.docs/organized/docs/sso/_navigation.mdx +8 -2
- package/.docs/organized/docs/sso/attributes.mdx +15 -3
- package/.docs/organized/docs/sso/domains.mdx +8 -6
- package/.docs/organized/docs/sso/example-apps.mdx +2 -2
- package/.docs/organized/docs/sso/identity-provider-role-assignment.mdx +30 -30
- package/.docs/organized/docs/sso/index.mdx +7 -6
- package/.docs/organized/docs/sso/it-team-faq.mdx +1 -1
- package/.docs/organized/docs/sso/jit-provisioning.mdx +2 -3
- package/.docs/organized/docs/sso/launch-checklist.mdx +2 -2
- package/.docs/organized/docs/sso/login-flows.mdx +3 -3
- package/.docs/organized/docs/sso/redirect-uris.mdx +22 -11
- package/.docs/organized/docs/sso/saml-security.mdx +1 -1
- package/.docs/organized/docs/sso/sign-in-consent.mdx +59 -0
- package/.docs/organized/docs/sso/signing-certificates.mdx +7 -7
- package/.docs/organized/docs/sso/single-logout.mdx +0 -1
- package/.docs/organized/docs/sso/ux/sessions.mdx +99 -0
- package/.docs/organized/docs/sso/ux/sign-in.mdx +1 -1
- package/.docs/organized/docs/vault/_navigation.mdx +2 -0
- package/.docs/organized/docs/vault/byok.mdx +140 -0
- package/.docs/organized/docs/vault/index.mdx +1 -1
- package/.docs/organized/docs/widgets/_navigation.mdx +48 -0
- package/.docs/organized/docs/widgets/admin-portal-domain-verification.mdx +24 -0
- package/.docs/organized/docs/widgets/admin-portal-sso-connection.mdx +20 -0
- package/.docs/organized/docs/widgets/api-keys.mdx +28 -0
- package/.docs/organized/docs/widgets/audit-log-streaming.mdx +25 -0
- package/.docs/organized/docs/widgets/directory-sync.mdx +23 -0
- package/.docs/organized/docs/widgets/index.mdx +12 -0
- package/.docs/organized/docs/widgets/localization.mdx +111 -0
- package/.docs/organized/docs/widgets/organization-switcher.mdx +47 -0
- package/.docs/organized/docs/widgets/pipes.mdx +27 -0
- package/.docs/organized/docs/widgets/quick-start.mdx +38 -0
- package/.docs/organized/docs/widgets/styling/css-customization.mdx +100 -0
- package/.docs/organized/docs/widgets/styling/index.mdx +29 -0
- package/.docs/organized/docs/widgets/styling/theme-customization.mdx +51 -0
- package/.docs/organized/docs/widgets/tokens.mdx +17 -0
- package/.docs/organized/docs/widgets/user-management.mdx +28 -0
- package/.docs/organized/docs/widgets/user-profile.mdx +30 -0
- package/.docs/organized/docs/widgets/user-security.mdx +31 -0
- package/.docs/organized/docs/widgets/user-sessions.mdx +26 -0
- package/LICENSE +21 -0
- package/README.md +14 -1
- package/dist/prepare.js +1 -1
- package/dist/prepare.js.map +1 -1
- package/package.json +2 -1
- package/.docs/organized/docs/dashboard.mdx +0 -244
- package/.docs/organized/docs/demo/_navigation.mdx +0 -26
- package/.docs/organized/docs/demo/accordion.mdx +0 -34
- package/.docs/organized/docs/demo/checklist.mdx +0 -33
- package/.docs/organized/docs/demo/code-block.mdx +0 -185
- package/.docs/organized/docs/demo/definition-list.mdx +0 -35
- package/.docs/organized/docs/demo/index.mdx +0 -7
- package/.docs/organized/docs/demo/punctuation.mdx +0 -37
- package/.docs/organized/docs/demo/replacements.mdx +0 -26
- package/.docs/organized/docs/demo/table.mdx +0 -26
- package/.docs/organized/docs/demo/tabs.mdx +0 -17
- package/.docs/organized/docs/fga/identity-provider-sessions.mdx +0 -68
- package/.docs/organized/docs/fga/local-development.mdx +0 -155
- package/.docs/organized/docs/fga/modeling/abac.mdx +0 -107
- package/.docs/organized/docs/fga/modeling/blocklist.mdx +0 -84
- package/.docs/organized/docs/fga/modeling/conditional-roles.mdx +0 -99
- package/.docs/organized/docs/fga/modeling/custom-roles.mdx +0 -90
- package/.docs/organized/docs/fga/modeling/entitlements.mdx +0 -127
- package/.docs/organized/docs/fga/modeling/managed-service-provider.mdx +0 -131
- package/.docs/organized/docs/fga/modeling/org-roles-and-permissions.mdx +0 -95
- package/.docs/organized/docs/fga/modeling/policy-context.mdx +0 -231
- package/.docs/organized/docs/fga/modeling/public-access.mdx +0 -61
- package/.docs/organized/docs/fga/modeling/shareable-content.mdx +0 -106
- package/.docs/organized/docs/fga/modeling/superusers.mdx +0 -74
- package/.docs/organized/docs/fga/modeling/user-groups.mdx +0 -92
- package/.docs/organized/docs/fga/operations-usage.mdx +0 -104
- package/.docs/organized/docs/fga/playground.mdx +0 -12
- package/.docs/organized/docs/fga/policies.mdx +0 -462
- package/.docs/organized/docs/fga/query-language.mdx +0 -112
- package/.docs/organized/docs/fga/schema-management.mdx +0 -224
- package/.docs/organized/docs/fga/schema.mdx +0 -388
- package/.docs/organized/docs/fga/warrant-tokens.mdx +0 -44
- package/.docs/organized/docs/fga/warrants.mdx +0 -92
- package/.docs/organized/docs/reference/fga/batch-check.mdx +0 -277
- package/.docs/organized/docs/reference/fga/check.mdx +0 -563
- package/.docs/organized/docs/reference/fga/policy/create.mdx +0 -27
- package/.docs/organized/docs/reference/fga/policy/delete.mdx +0 -18
- package/.docs/organized/docs/reference/fga/policy/get.mdx +0 -23
- package/.docs/organized/docs/reference/fga/policy/index.mdx +0 -52
- package/.docs/organized/docs/reference/fga/policy/list.mdx +0 -41
- package/.docs/organized/docs/reference/fga/policy/update.mdx +0 -26
- package/.docs/organized/docs/reference/fga/query.mdx +0 -375
- package/.docs/organized/docs/reference/fga/resource/batch-write.mdx +0 -175
- package/.docs/organized/docs/reference/fga/resource-type/apply.mdx +0 -35
- package/.docs/organized/docs/reference/fga/resource-type/create.mdx +0 -24
- package/.docs/organized/docs/reference/fga/resource-type/delete.mdx +0 -22
- package/.docs/organized/docs/reference/fga/resource-type/get.mdx +0 -23
- package/.docs/organized/docs/reference/fga/resource-type/index.mdx +0 -68
- package/.docs/organized/docs/reference/fga/resource-type/list.mdx +0 -36
- package/.docs/organized/docs/reference/fga/resource-type/update.mdx +0 -23
- package/.docs/organized/docs/reference/fga/schema/apply.mdx +0 -42
- package/.docs/organized/docs/reference/fga/schema/get.mdx +0 -24
- package/.docs/organized/docs/reference/fga/schema/index.mdx +0 -39
- package/.docs/organized/docs/reference/fga/warrant/batch-write.mdx +0 -226
- package/.docs/organized/docs/reference/fga/warrant/create.mdx +0 -215
- package/.docs/organized/docs/reference/fga/warrant/delete.mdx +0 -212
- package/.docs/organized/docs/reference/fga/warrant/index.mdx +0 -186
- package/.docs/organized/docs/reference/fga/warrant/list.mdx +0 -282
- package/.docs/organized/docs/reference/idempotency.mdx +0 -21
- package/.docs/organized/docs/reference/organization-domain.mdx +0 -189
- package/.docs/organized/docs/reference/rate-limits.mdx +0 -50
- package/.docs/organized/docs/reference/roles/list-for-organization.mdx +0 -152
- package/.docs/organized/docs/reference/user-management/access-token/index.mdx +0 -13
- package/.docs/organized/docs/reference/user-management/authentication/get-authorization-url/redirect-uri.mdx +0 -23
- package/.docs/organized/docs/reference/user-management/index.mdx +0 -13
- package/.docs/organized/docs/reference/user-management/mfa/index.mdx +0 -5
- package/.docs/organized/docs/reference/user-management/session-tokens/index.mdx +0 -5
- package/.docs/organized/docs/reference/user-management/session-tokens/refresh-token.mdx +0 -8
- package/.docs/organized/docs/user-management/_navigation.mdx +0 -87
- package/.docs/organized/docs/user-management/authkit.mdx +0 -69
- package/.docs/organized/docs/user-management/connect.mdx +0 -110
- package/.docs/organized/docs/user-management/directory-provisioning.mdx +0 -78
- package/.docs/organized/docs/user-management/email-verification.mdx +0 -29
- package/.docs/organized/docs/user-management/entitlements.mdx +0 -46
- package/.docs/organized/docs/user-management/jit-provisioning.mdx +0 -36
- package/.docs/organized/docs/user-management/overview.mdx +0 -46
- package/.docs/organized/docs/user-management/roles-and-permissions.mdx +0 -155
- package/.docs/organized/docs/user-management/users-organizations.mdx +0 -91
- package/.docs/organized/docs/user-management/widgets.mdx +0 -190
|
@@ -0,0 +1,179 @@
|
|
|
1
|
+
---
|
|
2
|
+
title: Standalone Connect
|
|
3
|
+
description: Integrate Connect's OAuth API with your existing authentication stack.
|
|
4
|
+
showNextPage: true
|
|
5
|
+
originalPath: .tmp-workos-clone/packages/docs/content/authkit/connect/standalone.mdx
|
|
6
|
+
---
|
|
7
|
+
|
|
8
|
+
## Overview
|
|
9
|
+
|
|
10
|
+
Standalone Connect allows applications with existing authentication systems to use AuthKit as their OAuth authorization server. You maintain your existing authentication stack while leveraging AuthKit's OAuth infrastructure for token issuance and management.
|
|
11
|
+
|
|
12
|
+
Unlike standard AuthKit integration, Standalone Connect delegates authentication to your application, then handles the OAuth flow and token issuance for OAuth clients. This feature works with [OAuth applications](/authkit/connect/oauth) only—[M2M applications](/authkit/connect/m2m) use the `client_credentials` flow which doesn't involve user authentication.
|
|
13
|
+
|
|
14
|
+
## When to use Standalone Connect
|
|
15
|
+
|
|
16
|
+
Use Standalone Connect when you:
|
|
17
|
+
|
|
18
|
+
- Have an existing authentication stack in your application.
|
|
19
|
+
- Need to enable OAuth-based integrations, like a [CLI](/authkit/cli-auth) app or [MCP](/authkit/mcp) server.
|
|
20
|
+
- Want to support third-party applications accessing your users' resources.
|
|
21
|
+
|
|
22
|
+
## Getting started
|
|
23
|
+
|
|
24
|
+
### Create an OAuth application
|
|
25
|
+
|
|
26
|
+
Before testing your Standalone Connect integration, you'll need to [create an OAuth application](/authkit/connect/oauth) in the WorkOS Dashboard. If you need to support MCP auth, you'll need to enable Client ID Metadata Document (CIMD), which you can read more about in the [MCP guide](/authkit/mcp).
|
|
27
|
+
|
|
28
|
+
### Configure your Login URI
|
|
29
|
+
|
|
30
|
+
Navigate to _Connect_ → _Configuration_ in the [WorkOS Dashboard](https://dashboard.workos.com) and provide your **Login URI**.
|
|
31
|
+
|
|
32
|
+
The **Login URI** is where AuthKit will redirect users to authenticate with your existing system. You can only configure one Login URI per environment.
|
|
33
|
+
|
|
34
|
+
Your Login URI must:
|
|
35
|
+
|
|
36
|
+
- Use HTTPS in production.
|
|
37
|
+
- Accept an `external_auth_id` query parameter.
|
|
38
|
+
- Authenticate users with your existing system.
|
|
39
|
+
- Call the AuthKit completion API after successful authentication. More on that below.
|
|
40
|
+
|
|
41
|
+
Example: `https://your-app.example.com/auth/login`
|
|
42
|
+
|
|
43
|
+
## Authentication flow
|
|
44
|
+
|
|
45
|
+
### (1) OAuth client initiates flow
|
|
46
|
+
|
|
47
|
+
OAuth clients start the authorization flow with AuthKit following standard OAuth 2.0. This could be a third-party application, partner integration, or any OAuth-enabled client.
|
|
48
|
+
|
|
49
|
+
### (2) AuthKit redirects to your application
|
|
50
|
+
|
|
51
|
+
AuthKit redirects users to your Login URI with an `external_auth_id` parameter:
|
|
52
|
+
|
|
53
|
+
```txt
|
|
54
|
+
https://your-app.example.com/auth/login?external_auth_id=01J3X4Y5Z6A7B8C9D0E1F2G3H4
|
|
55
|
+
```
|
|
56
|
+
|
|
57
|
+
The `external_auth_id` is a temporary identifier used to complete the flow with AuthKit.
|
|
58
|
+
|
|
59
|
+
### (3) Authenticate the user
|
|
60
|
+
|
|
61
|
+
Your application authenticates users with your existing system. If users have an active session, skip to the next step.
|
|
62
|
+
|
|
63
|
+
AuthKit handles OAuth consent separately, so your application doesn't need to display any consent screens.
|
|
64
|
+
|
|
65
|
+
### (4) Complete authentication with AuthKit
|
|
66
|
+
|
|
67
|
+
Call the [AuthKit completion API](/reference/workos-connect/standalone/complete) after authenticating the user, passing the `external_auth_id` that your Login URI originally received:
|
|
68
|
+
|
|
69
|
+
```js
|
|
70
|
+
const response = await fetch('https://api.workos.com/authkit/oauth2/complete', {
|
|
71
|
+
method: 'POST',
|
|
72
|
+
headers: {
|
|
73
|
+
'Content-Type': 'application/json',
|
|
74
|
+
'Authorization': `Bearer ${process.env.WORKOS_API_KEY}`,
|
|
75
|
+
},
|
|
76
|
+
body: JSON.stringify({
|
|
77
|
+
external_auth_id: externalAuthId,
|
|
78
|
+
user: {
|
|
79
|
+
id: user.id,
|
|
80
|
+
email: user.email,
|
|
81
|
+
first_name: user.firstName,
|
|
82
|
+
last_name: user.lastName,
|
|
83
|
+
metadata: { department: user.department },
|
|
84
|
+
},
|
|
85
|
+
}),
|
|
86
|
+
});
|
|
87
|
+
|
|
88
|
+
const { redirect_uri } = await response.json();
|
|
89
|
+
```
|
|
90
|
+
|
|
91
|
+
### (5) Return control to AuthKit
|
|
92
|
+
|
|
93
|
+
Redirect users to the `redirect_uri` from the API response. AuthKit displays a consent screen if needed, issues tokens, and completes the OAuth flow.
|
|
94
|
+
|
|
95
|
+
## Integrating via the API
|
|
96
|
+
|
|
97
|
+
### Dynamic consent options
|
|
98
|
+
|
|
99
|
+
You can provide `user_consent_options` to display options during the OAuth consent screen. This is useful when users need to choose specific resources or contexts (like a parent resource in your application) to grant access to.
|
|
100
|
+
|
|
101
|
+
Each consent option must include:
|
|
102
|
+
|
|
103
|
+
- `claim`: The name of the access token claim that will hold the user's selected value.
|
|
104
|
+
- `type`: The format of the option. Only `enum` is supported currently.
|
|
105
|
+
- `label`: Display text for the option.
|
|
106
|
+
- `choices`: Array of choices (can be flat or grouped).
|
|
107
|
+
|
|
108
|
+
```js
|
|
109
|
+
const response = await fetch('https://api.workos.com/authkit/oauth2/complete', {
|
|
110
|
+
method: 'POST',
|
|
111
|
+
headers: {
|
|
112
|
+
'Content-Type': 'application/json',
|
|
113
|
+
'Authorization': `Bearer ${process.env.WORKOS_API_KEY}`,
|
|
114
|
+
},
|
|
115
|
+
body: JSON.stringify({
|
|
116
|
+
external_auth_id,
|
|
117
|
+
user: { id: user.id, email: user.email },
|
|
118
|
+
user_consent_options: [
|
|
119
|
+
{
|
|
120
|
+
claim: 'urn:example:tenant',
|
|
121
|
+
type: 'enum',
|
|
122
|
+
label: 'Environment',
|
|
123
|
+
choices: [
|
|
124
|
+
{
|
|
125
|
+
group: 'Production',
|
|
126
|
+
choices: [
|
|
127
|
+
{ value: 'prod_us', label: 'US-East' },
|
|
128
|
+
{ value: 'prod_eu', label: 'EU-West' },
|
|
129
|
+
],
|
|
130
|
+
},
|
|
131
|
+
{
|
|
132
|
+
group: 'Development',
|
|
133
|
+
choices: [
|
|
134
|
+
{ value: 'dev_main', label: 'Development' },
|
|
135
|
+
{ value: 'staging', label: 'Staging' },
|
|
136
|
+
],
|
|
137
|
+
},
|
|
138
|
+
],
|
|
139
|
+
},
|
|
140
|
+
],
|
|
141
|
+
}),
|
|
142
|
+
});
|
|
143
|
+
```
|
|
144
|
+
|
|
145
|
+
The selected values appear as custom claims in the issued tokens. For example, if the user selects one of the above options, the token will include:
|
|
146
|
+
|
|
147
|
+
```json
|
|
148
|
+
{
|
|
149
|
+
"sub": "user_123",
|
|
150
|
+
"email": "user@example.com",
|
|
151
|
+
"urn:example:tenant": "prod_us"
|
|
152
|
+
// ...
|
|
153
|
+
}
|
|
154
|
+
```
|
|
155
|
+
|
|
156
|
+
### Error handling
|
|
157
|
+
|
|
158
|
+
If the `external_auth_id` is invalid, the call to the AuthKit completion API will fail. Your application is free to choose how to handle this case, but redirecting to your application's homepage is recommended.
|
|
159
|
+
|
|
160
|
+
### Token verification
|
|
161
|
+
|
|
162
|
+
Resource servers verify tokens issued by AuthKit using standard Connect token verification:
|
|
163
|
+
|
|
164
|
+
```js
|
|
165
|
+
import { jwtVerify, createRemoteJWKSet } from 'jose';
|
|
166
|
+
|
|
167
|
+
const JWKS = createRemoteJWKSet(new URL('https://authkit_domain/oauth2/jwks'));
|
|
168
|
+
|
|
169
|
+
async function verifyToken(token) {
|
|
170
|
+
const { payload } = await jwtVerify(token, JWKS, {
|
|
171
|
+
audience: 'client_123456789',
|
|
172
|
+
issuer: 'https://authkit_domain',
|
|
173
|
+
});
|
|
174
|
+
|
|
175
|
+
return payload;
|
|
176
|
+
}
|
|
177
|
+
```
|
|
178
|
+
|
|
179
|
+
See the [Connect documentation](/authkit/connect/oauth/verifying-tokens) for details on token expiration, refresh tokens, and revocation.
|
|
@@ -0,0 +1,65 @@
|
|
|
1
|
+
---
|
|
2
|
+
title: Connect
|
|
3
|
+
description: Enable other applications to access your users and their identities.
|
|
4
|
+
showNextPage: true
|
|
5
|
+
originalPath: .tmp-workos-clone/packages/docs/content/authkit/connect.mdx
|
|
6
|
+
---
|
|
7
|
+
|
|
8
|
+
## Introduction
|
|
9
|
+
|
|
10
|
+
Connect is a set of controls and APIs that developers can use to allow different types of applications to access their users' identity and resources. Connect is built on top of industry-standard specifications like OAuth 2.0 and OpenID Connect in order to support many common use-cases out of the box.
|
|
11
|
+
|
|
12
|
+
Unlike AuthKit's other features that help users sign into **your application**, Connect enables **other applications** to authenticate and access your users' data through secure, managed APIs.
|
|
13
|
+
|
|
14
|
+
## Common use-cases
|
|
15
|
+
|
|
16
|
+
**Customer applications**
|
|
17
|
+
: Enable your customers to build custom integrations with your platform. This can include allowing them to add a "Sign in with [your app]" button on their login page.
|
|
18
|
+
|
|
19
|
+
**Auxiliary applications**
|
|
20
|
+
: Allow secondary applications that support your primary application, such as support tools or discussion forums, to authenticate using the same user identities in AuthKit.
|
|
21
|
+
|
|
22
|
+
**Partner integrations**
|
|
23
|
+
: Issue credentials for trusted partners to authenticate with when calling your application's API.
|
|
24
|
+
|
|
25
|
+
## Getting started
|
|
26
|
+
|
|
27
|
+
Each Connect integration is defined as an Application, which can be created inside of the WorkOS Dashboard.
|
|
28
|
+
|
|
29
|
+
When creating an application, you first choose the type of integration: **OAuth** or Machine-to-Machine (**M2M**).
|
|
30
|
+
|
|
31
|
+
### OAuth applications
|
|
32
|
+
|
|
33
|
+
Select OAuth when building web or mobile applications where the actor being authenticated is a [User](/reference/authkit/user). Integrating with an OAuth application uses the underlying `authorization_code` OAuth flow which is supported by many libraries and frameworks out of the box.
|
|
34
|
+
|
|
35
|
+
Upon successful authorization, the issued tokens will contain information about the user who signed in.
|
|
36
|
+
|
|
37
|
+
[Learn more about OAuth applications →](/authkit/connect/oauth)
|
|
38
|
+
|
|
39
|
+
### M2M applications
|
|
40
|
+
|
|
41
|
+
Select M2M when the application will be a third-party service, such as one of your customer's applications. Integrating with an M2M application uses the underlying `client_credentials` flow.
|
|
42
|
+
|
|
43
|
+
Unlike OAuth applications, the actor being authenticated is not an individual user. Instead issued access tokens will contain an `org_id` claim which represents the customer you are granting access to via the M2M application.
|
|
44
|
+
|
|
45
|
+
The M2M application will use its `client_id` and `client_secret` to authenticate requests to your application's API or services.
|
|
46
|
+
|
|
47
|
+
[Learn more about M2M applications →](/authkit/connect/m2m)
|
|
48
|
+
|
|
49
|
+
## Concepts
|
|
50
|
+
|
|
51
|
+
All Connect applications share the following concepts:
|
|
52
|
+
|
|
53
|
+
### Participants
|
|
54
|
+
|
|
55
|
+
When using Connect, there are several actors involved with the integration of each Application:
|
|
56
|
+
|
|
57
|
+
- **Relying Party**: The application that receives Connect-issued tokens and identity information. It may also use the access token to make requests to your API.
|
|
58
|
+
- **Resource server**: The service (generally your app) that allows other clients to authenticate using the Connect-issued tokens.
|
|
59
|
+
- **Authorization server**: This is Connect, the issuer of identity and access tokens to requesting clients after authenticating the user.
|
|
60
|
+
|
|
61
|
+
### Credentials
|
|
62
|
+
|
|
63
|
+
Applications can have up to 5 credentials. These are only shown once upon creation and do not expire. The application `client_id` and `client_secret` from a credential can be used to authenticate to the [Connect APIs](/reference/workos-connect).
|
|
64
|
+
|
|
65
|
+
When sharing app credentials with an external party, use a secure method — like encrypted email or file sharing — and make sure the recipient is properly authenticated.
|
|
@@ -0,0 +1,141 @@
|
|
|
1
|
+
---
|
|
2
|
+
title: Custom Email Providers
|
|
3
|
+
description: Learn how to send emails through your own email service provider.
|
|
4
|
+
showNextPage: true
|
|
5
|
+
originalPath: .tmp-workos-clone/packages/docs/content/authkit/custom-email-providers.mdx
|
|
6
|
+
---
|
|
7
|
+
|
|
8
|
+
## Introduction
|
|
9
|
+
|
|
10
|
+
By default, WorkOS will send emails via our default email service provider, either through our domain or through your own [custom email domain](/custom-domains/email). If you would like to have more control over deliverability, reputation, and compliance, while still offloading the heavy lifting of email handling, you can configure a custom email provider. This option is also ideal if you already have an existing email service provider configuration.
|
|
11
|
+
|
|
12
|
+
---
|
|
13
|
+
|
|
14
|
+
## Configure a custom email provider
|
|
15
|
+
|
|
16
|
+
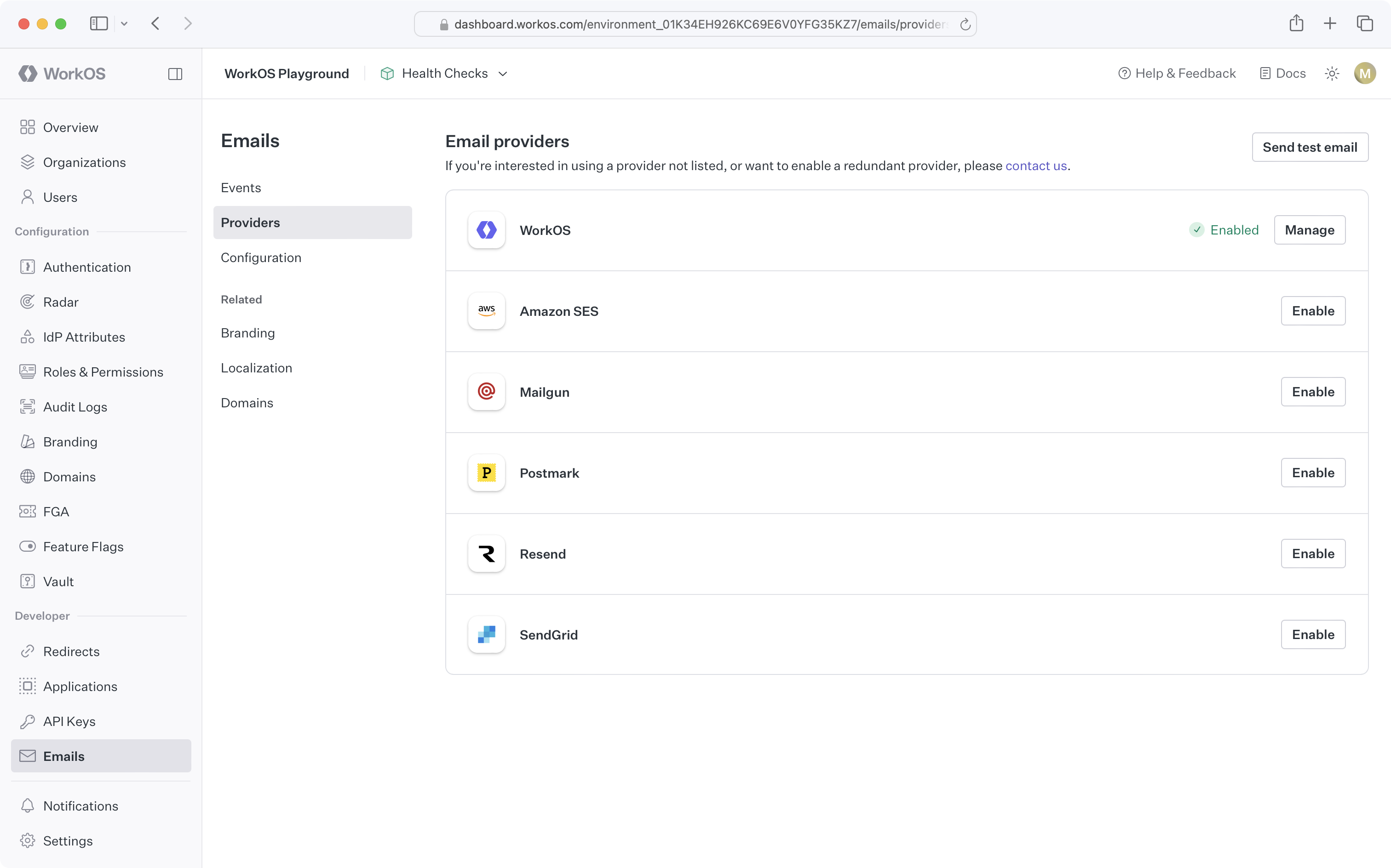
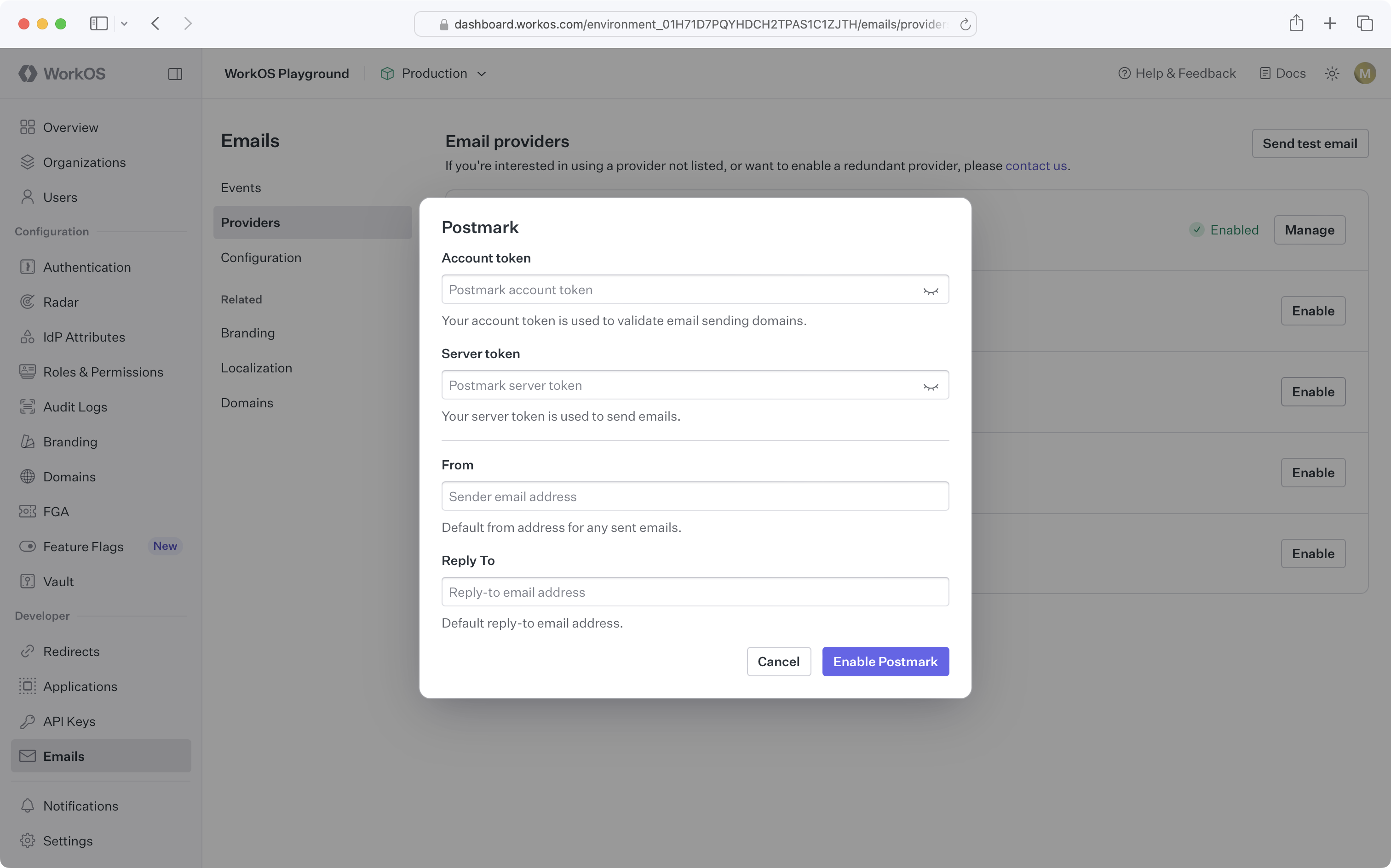
To configure a custom email provider for an environment, navigate to [_Emails_ → _Providers_](https://dashboard.workos.com/environment/emails/providers) and click _Enable_ next to the provider you would like to use and enter the required information.
|
|
17
|
+
|
|
18
|
+
> If the email service provider you'd like to use is not listed, please [contact support](mailto:support@workos.com).
|
|
19
|
+
|
|
20
|
+
|
|
21
|
+
|
|
22
|
+
### Amazon SES
|
|
23
|
+
|
|
24
|
+
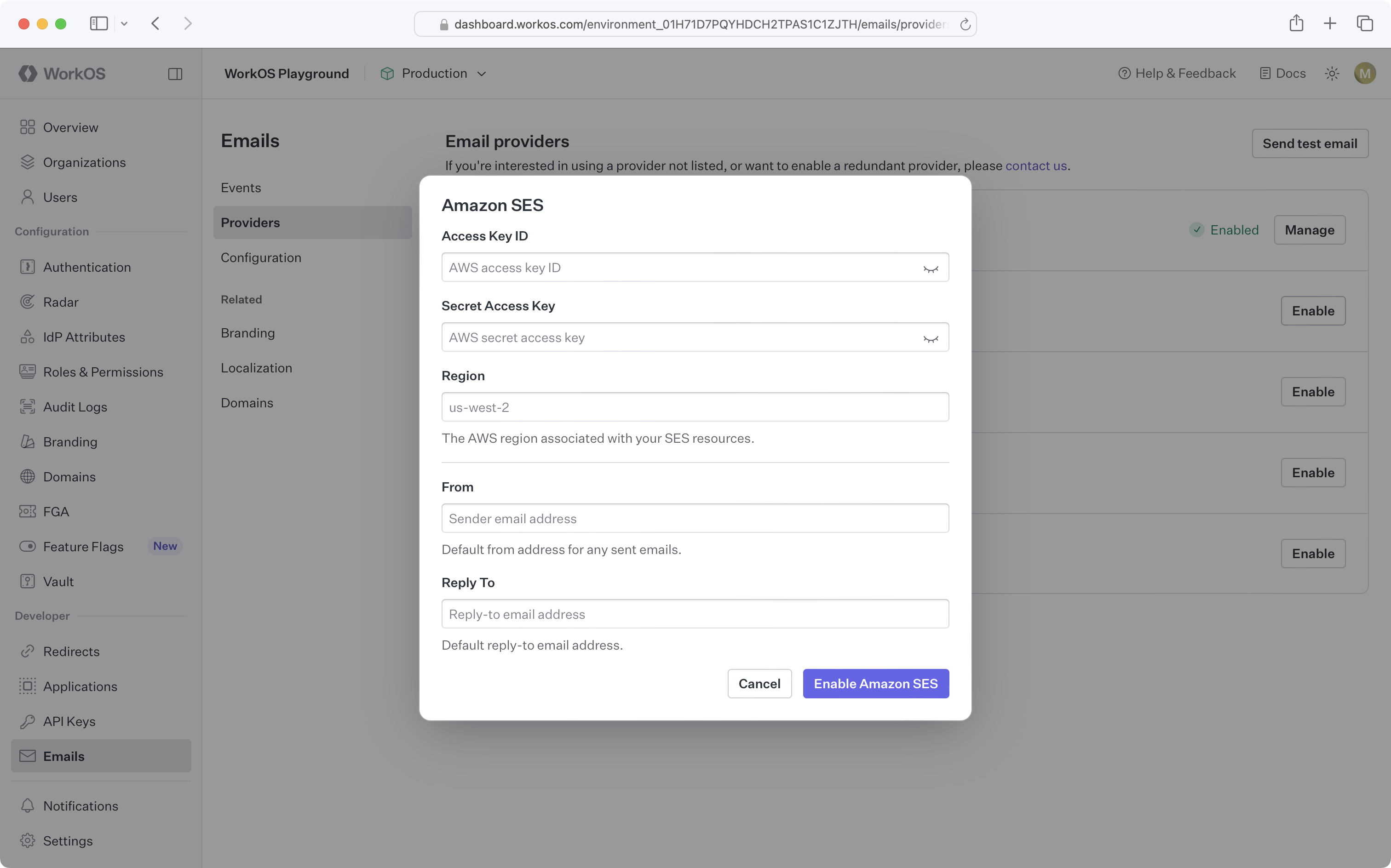
To connect WorkOS to Amazon SES, you'll need to [create an IAM user](https://docs.aws.amazon.com/IAM/latest/UserGuide/id_users_create.html) with an access key, and [verify email sending identities](https://docs.aws.amazon.com/ses/latest/dg/creating-identities.html). Ensure the IAM user has a policy like the following:
|
|
25
|
+
|
|
26
|
+
```json
|
|
27
|
+
{
|
|
28
|
+
"Version": "2012-10-17",
|
|
29
|
+
"Statement": [
|
|
30
|
+
{
|
|
31
|
+
"Sid": "SendEmailAccess",
|
|
32
|
+
"Effect": "Allow",
|
|
33
|
+
"Action": "ses:SendEmail",
|
|
34
|
+
"Resource": [
|
|
35
|
+
"arn:aws:ses:<region>:<accountId>:identity/*",
|
|
36
|
+
"arn:aws:ses:<region>:<accountId>:configuration-set/*"
|
|
37
|
+
]
|
|
38
|
+
},
|
|
39
|
+
{
|
|
40
|
+
"Sid": "IdentityManagementAccess",
|
|
41
|
+
"Effect": "Allow",
|
|
42
|
+
"Action": ["ses:GetIdentityVerificationAttributes", "ses:ListIdentities"],
|
|
43
|
+
"Resource": "*"
|
|
44
|
+
}
|
|
45
|
+
]
|
|
46
|
+
}
|
|
47
|
+
```
|
|
48
|
+
|
|
49
|
+
You'll need to update the resource scope with your Amazon SES region and account ID. For additional ways to restrict access, refer to the [Amazon SES documentation](https://docs.aws.amazon.com/ses/latest/dg/control-user-access.html).
|
|
50
|
+
|
|
51
|
+
> If you're interested in using temporary security credentials to access Amazon SES, please [contact support](mailto:support@workos.com).
|
|
52
|
+
|
|
53
|
+
Once you have an IAM user with the necessary permissions and have verified sending identities, you can configure the Amazon SES custom email provider in the [WorkOS Dashboard](https://dashboard.workos.com/):
|
|
54
|
+
|
|
55
|
+
|
|
56
|
+
|
|
57
|
+
### Mailgun
|
|
58
|
+
|
|
59
|
+
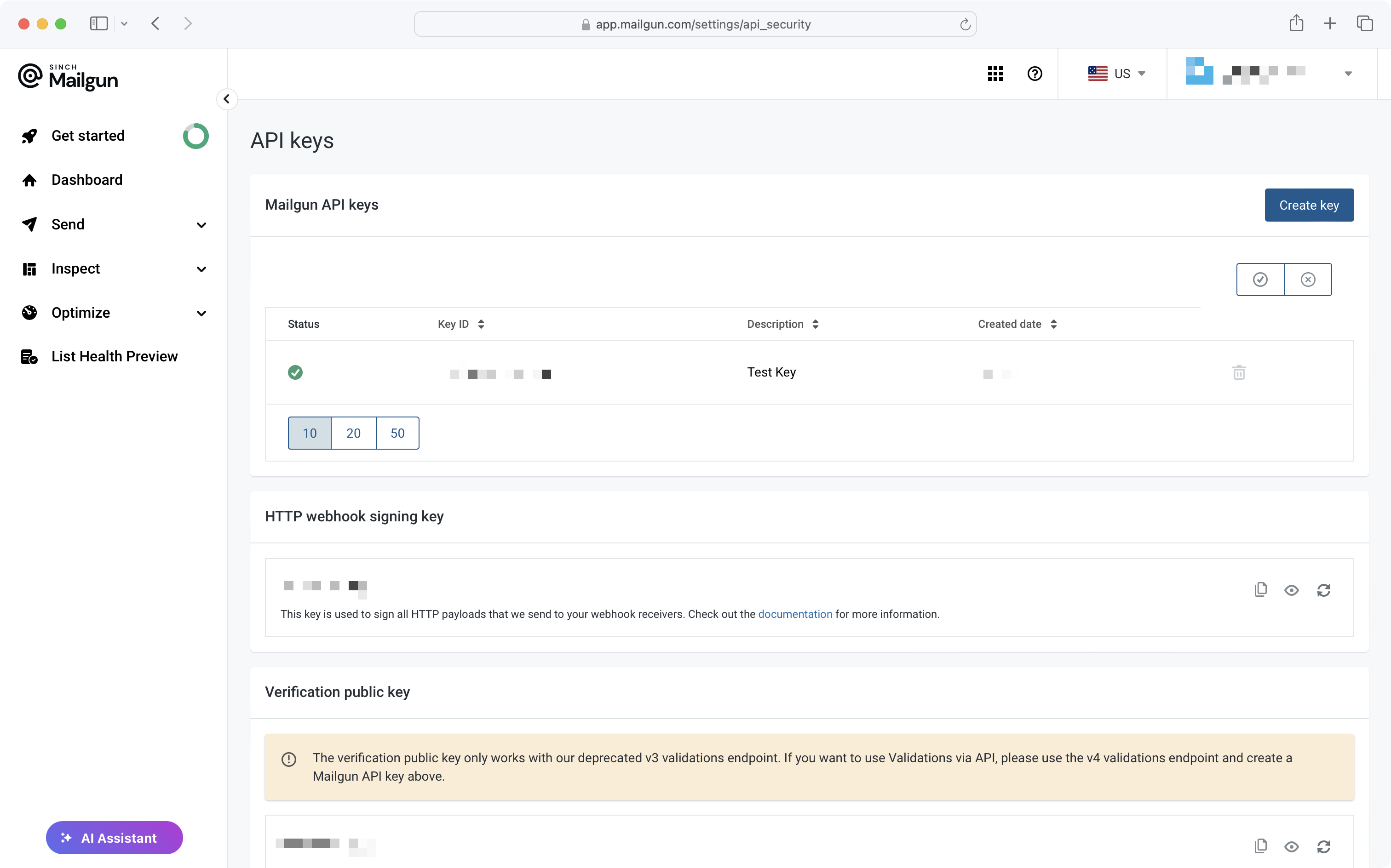
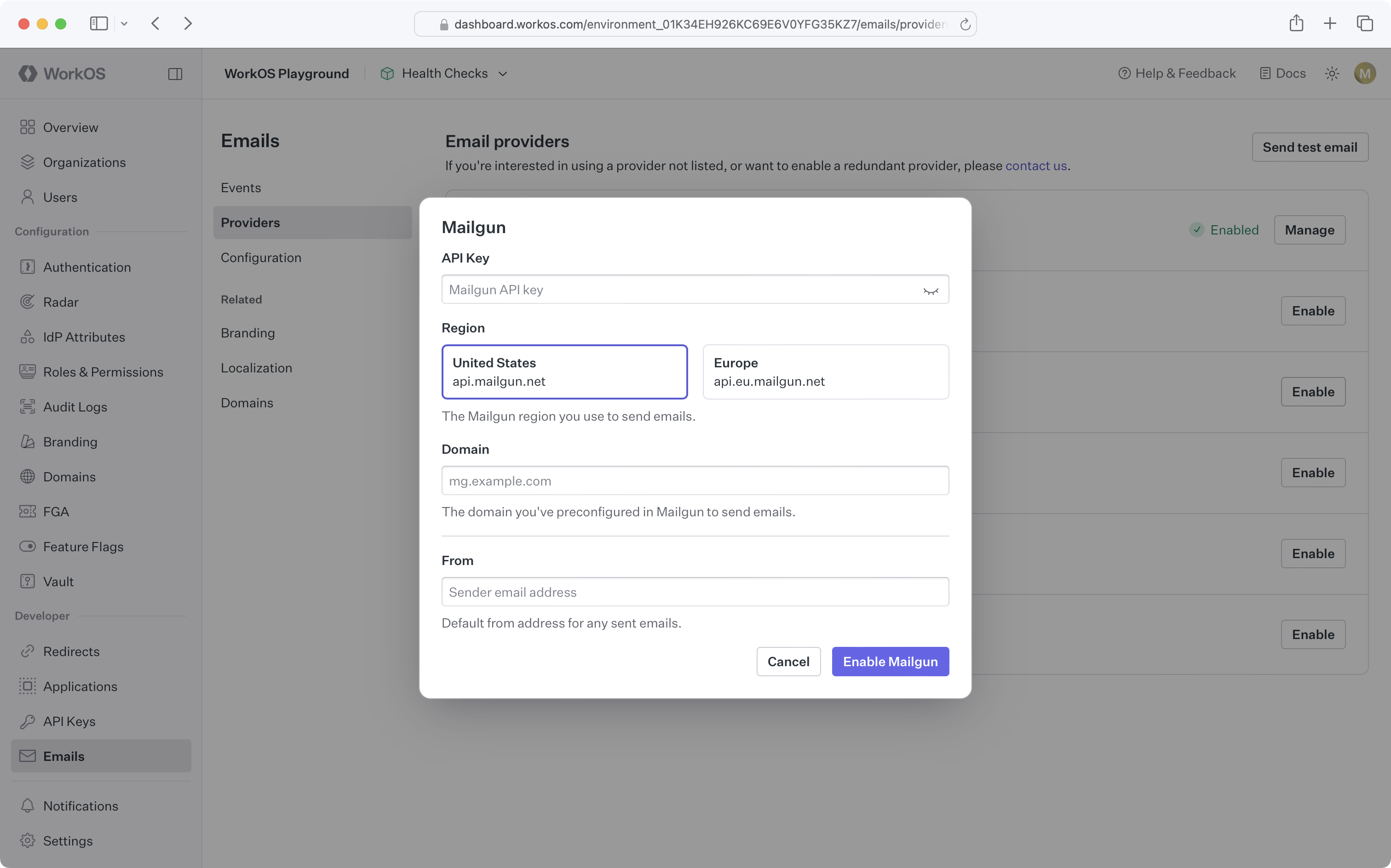
Before configuring the Mailgun custom email provider in WorkOS, you'll need to [verify your domain in your Mailgun account](https://help.mailgun.com/hc/en-us/articles/32884700912923-Domain-Verification-Setup-Guide).
|
|
60
|
+
|
|
61
|
+
Once you've verified a domain, you'll need an API key, which you can create on the [API Security page of the Mailgun dashboard](https://app.mailgun.com/settings/api_security). The API key is used to validate verified domains in your account and send emails.
|
|
62
|
+
|
|
63
|
+
|
|
64
|
+
|
|
65
|
+
Once you've verified your domain and obtained an API key, you can configure the Mailgun custom email provider in the [WorkOS Dashboard](https://dashboard.workos.com/):
|
|
66
|
+
|
|
67
|
+
|
|
68
|
+
|
|
69
|
+
### Postmark
|
|
70
|
+
|
|
71
|
+
Before configuring the Postmark custom email provider in WorkOS, you'll need to [verify sender signatures in your Postmark account](https://postmarkapp.com/developer/user-guide/managing-your-account/managing-sender-signatures).
|
|
72
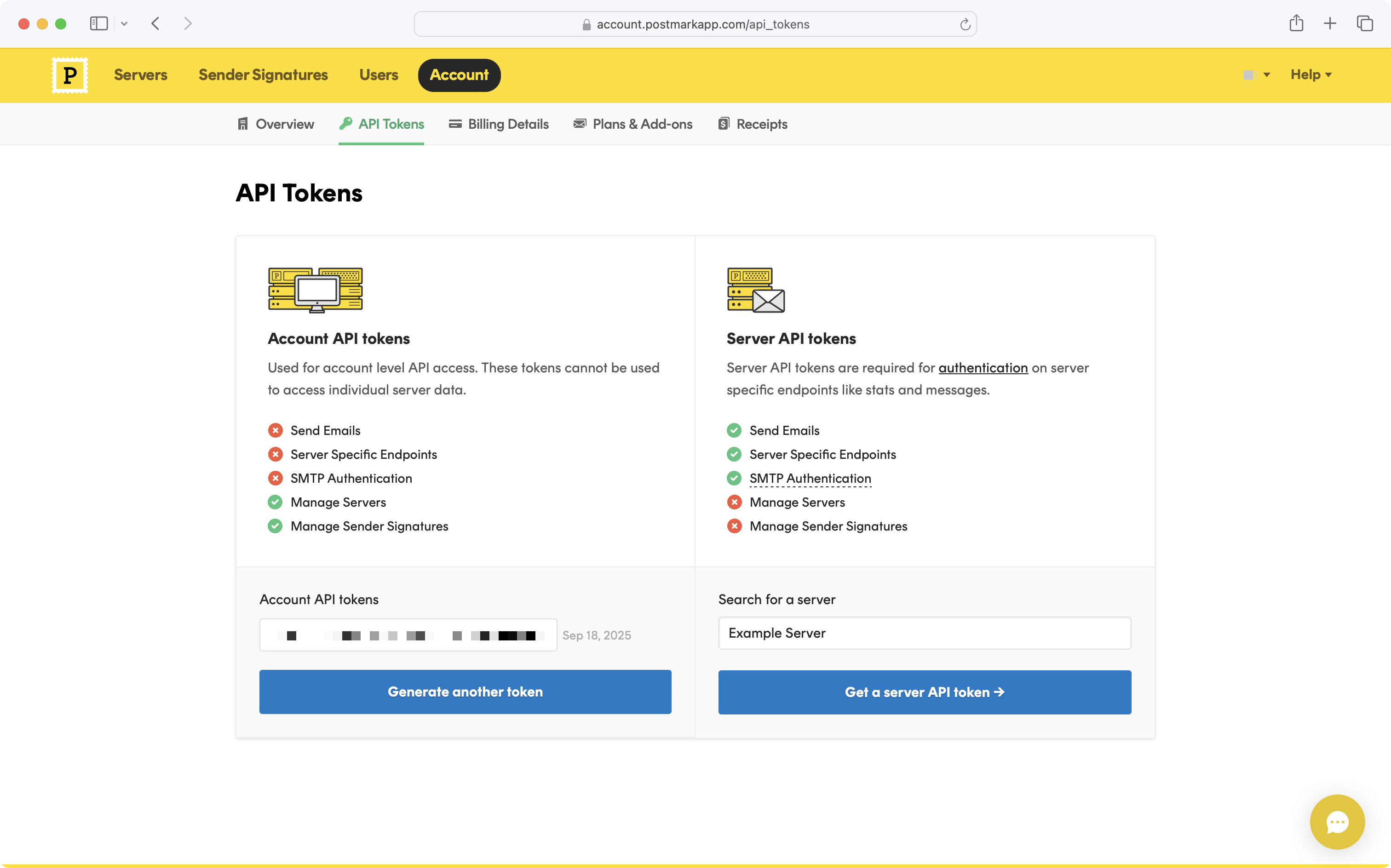
|
+
|
|
73
|
+
Once you've verified a sender signature, you'll need an account and server token, which you can find on the [API Tokens page of the Postmark dashboard](https://postmarkapp.com/account/api-tokens).
|
|
74
|
+
|
|
75
|
+
|
|
76
|
+
|
|
77
|
+
The account token is used to validate sender signatures in your account, and the server token is used to send emails.
|
|
78
|
+
|
|
79
|
+
Once you've verified your sender signature and obtained your account and server token, you can configure the Postmark custom email provider in the [WorkOS Dashboard](https://dashboard.workos.com/):
|
|
80
|
+
|
|
81
|
+
|
|
82
|
+
|
|
83
|
+
Upon enabling the Postmark custom email provider, a WorkOS transactional message stream with the ID `workos-transactional-s` will be created for you. All WorkOS emails will be sent using this message stream.
|
|
84
|
+
|
|
85
|
+
### Resend
|
|
86
|
+
|
|
87
|
+
Before configuring the Resend custom email provider in WorkOS, you'll need to [verify domains in your Resend account](https://resend.com/docs/dashboard/domains/introduction).
|
|
88
|
+
|
|
89
|
+
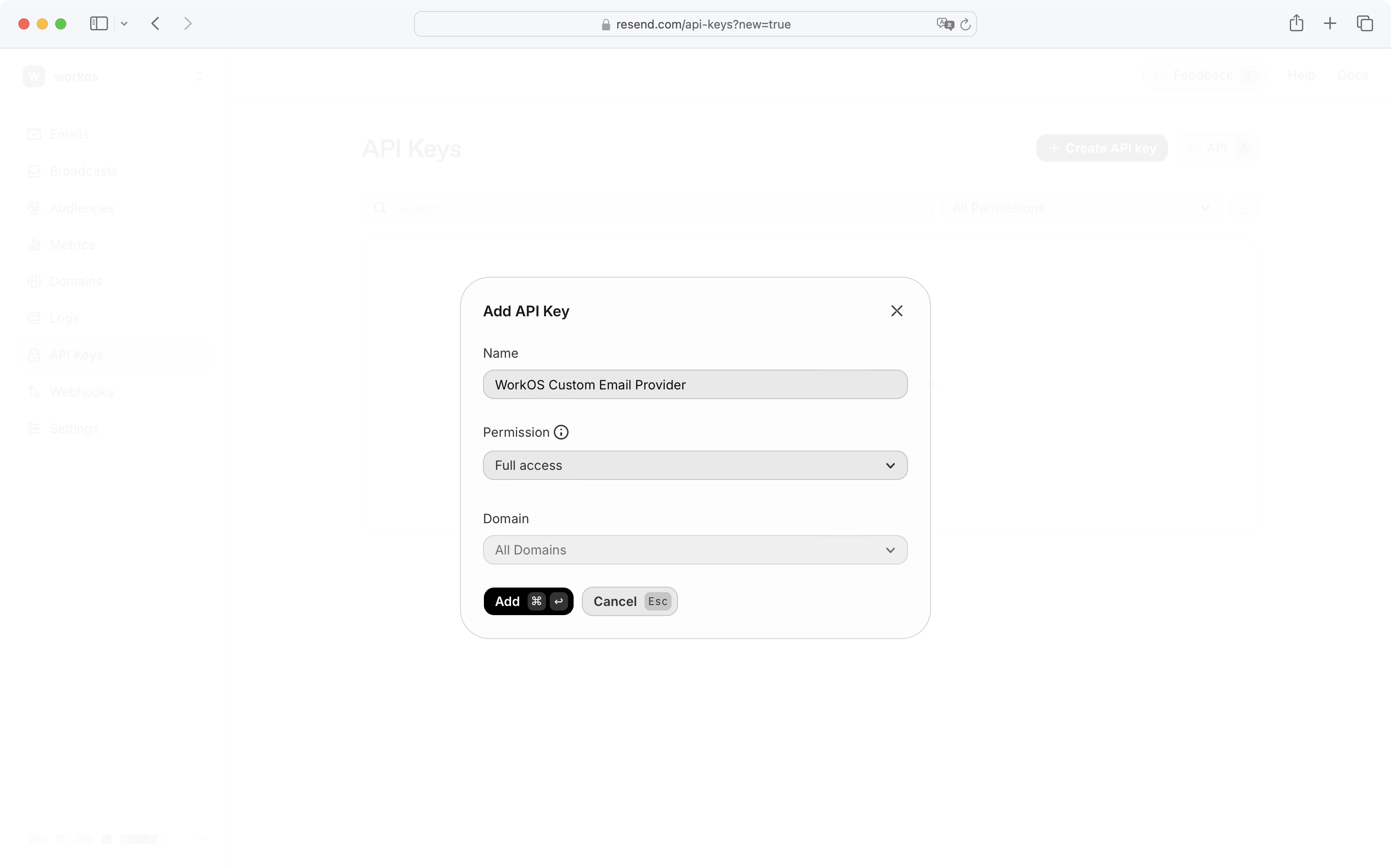
Once you've verified your domain, you'll need to create an API key with the "Full access" permission on the [Resend API Keys page](https://resend.com/api-keys).
|
|
90
|
+
|
|
91
|
+
|
|
92
|
+
|
|
93
|
+
"Full access" permission is required to fetch verified domains and send emails.
|
|
94
|
+
|
|
95
|
+
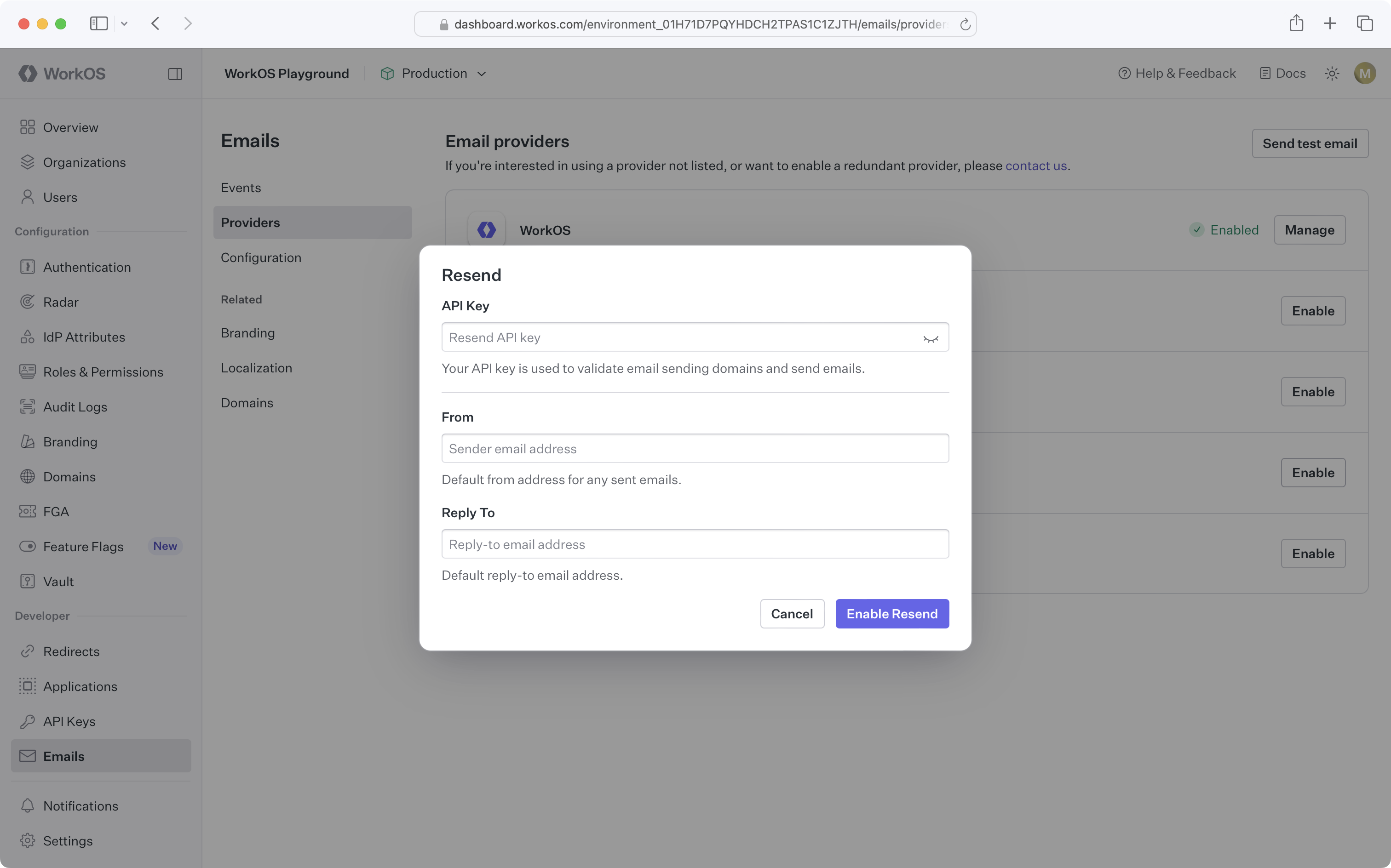
Once you've verified your domain and obtained an API key, you can configure the Resend custom email provider in the [WorkOS Dashboard](https://dashboard.workos.com/):
|
|
96
|
+
|
|
97
|
+
|
|
98
|
+
|
|
99
|
+
### SendGrid
|
|
100
|
+
|
|
101
|
+
Before configuring the SendGrid custom email provider in WorkOS, you'll need to verify your domain in the [Sender Authentication settings in your SendGrid dashboard](https://app.sendgrid.com/settings/sender_auth).
|
|
102
|
+
|
|
103
|
+
Once you've verified your domain, you'll need to create an API key under _Settings_ → _API Keys_ in the [SendGrid dashboard](https://app.sendgrid.com/settings/api_keys).
|
|
104
|
+
|
|
105
|
+
|
|
106
|
+
|
|
107
|
+
For API key permissions, select "Full Access" for Mail Send, and "Read Access" for Sender Authentication.
|
|
108
|
+
|
|
109
|
+
Once you've verified your domain and obtained an API key, you can configure the SendGrid custom email provider in the [WorkOS Dashboard](https://dashboard.workos.com/):
|
|
110
|
+
|
|
111
|
+
|
|
112
|
+
|
|
113
|
+
---
|
|
114
|
+
|
|
115
|
+
## Re-enable the WorkOS default provider
|
|
116
|
+
|
|
117
|
+
At any time when you are using a custom email provider, you can re-enable the WorkOS default provider by navigating to [_Emails_ → _Providers_](https://dashboard.workos.com/environment/emails/providers) and clicking _Enable_ next to the WorkOS provider.
|
|
118
|
+
|
|
119
|
+
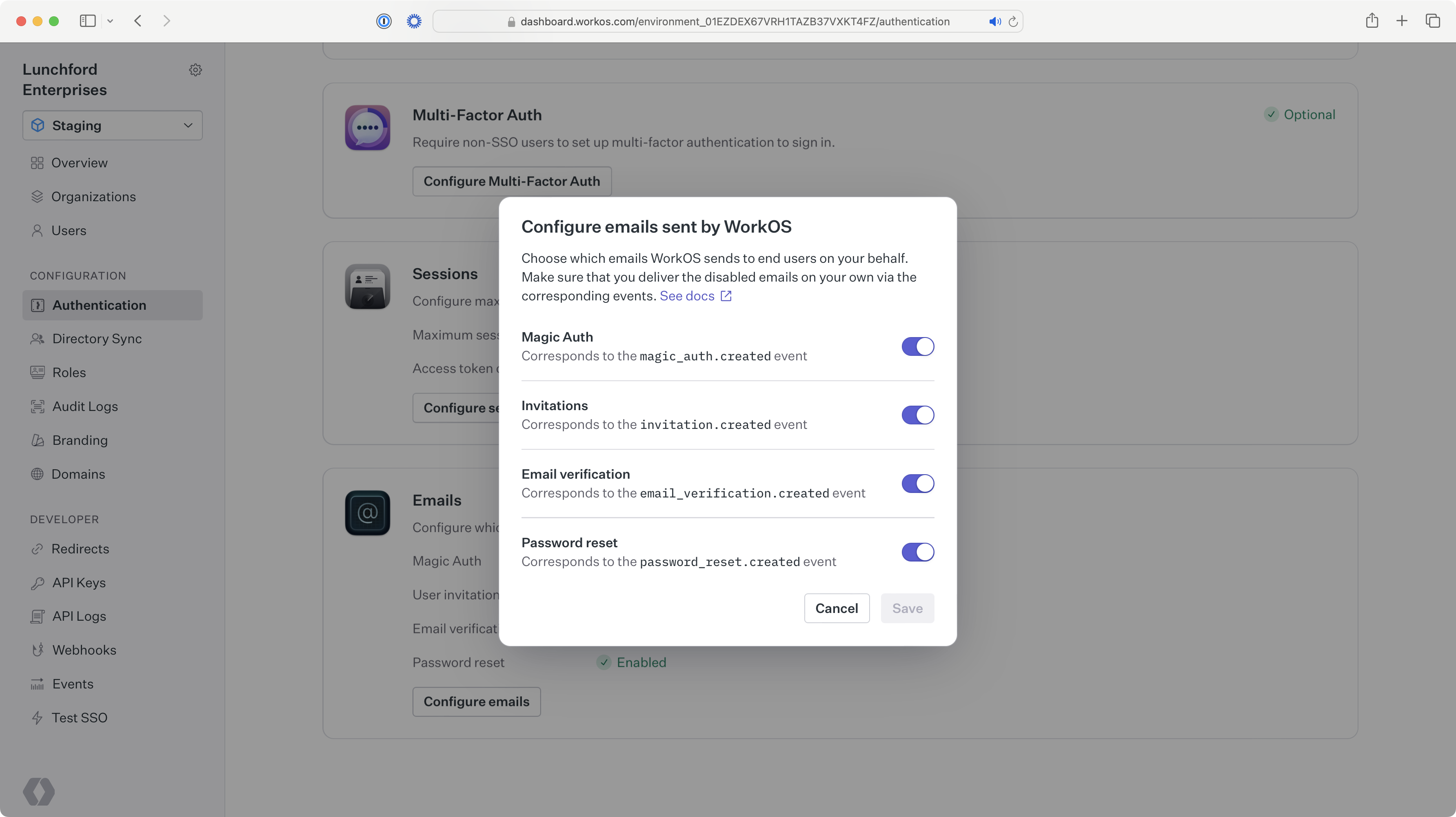
|
|
120
|
+
|
|
121
|
+
Alternatively, you can also remove your current custom email provider, which will automatically re-enable the WorkOS default provider.
|
|
122
|
+
|
|
123
|
+
|
|
124
|
+
|
|
125
|
+
---
|
|
126
|
+
|
|
127
|
+
## Frequently asked questions
|
|
128
|
+
|
|
129
|
+
### What types of emails are sent through custom email providers?
|
|
130
|
+
|
|
131
|
+
All transactional emails for your users will be sent through your custom email provider when configured. This includes AuthKit invitations and magic codes, Radar challenges, and Admin Portal notification emails.
|
|
132
|
+
|
|
133
|
+
### If I am using a custom email provider, do I need to set up a custom email domain in WorkOS?
|
|
134
|
+
|
|
135
|
+
No. When using a custom email provider, you configure the sending domain in that provider, not in WorkOS. Any custom email domain set up in WorkOS will not be used.
|
|
136
|
+
|
|
137
|
+
### What happens if emails fail to send via my custom email provider?
|
|
138
|
+
|
|
139
|
+
If emails fail to send via your custom email provider, you will be notified according to your notifications preferences via the [WorkOS Dashboard](https://dashboard.workos.com/), email, or Slack. You can also utilize the [_Emails_ → _Events_ page](https://dashboard.workos.com/environment/emails/events) in the WorkOS Dashboard to track email delivery failures.
|
|
140
|
+
|
|
141
|
+
Additionally, repeated delivery failures may cause the provider to suppress the recipient's email address. See [Check suppression status](/email/e-check-suppression-status) for how to check and resolve suppressions.
|
|
@@ -2,12 +2,12 @@
|
|
|
2
2
|
title: Custom Emails
|
|
3
3
|
description: Learn how to send your own emails for user lifecycle events.
|
|
4
4
|
showNextPage: true
|
|
5
|
-
originalPath: .tmp-workos-clone/packages/docs/content/
|
|
5
|
+
originalPath: .tmp-workos-clone/packages/docs/content/authkit/custom-emails.mdx
|
|
6
6
|
---
|
|
7
7
|
|
|
8
8
|
## Introduction
|
|
9
9
|
|
|
10
|
-
By default, WorkOS will send emails related to
|
|
10
|
+
By default, WorkOS will send emails related to AuthKit for you, such as password reset and Magic Auth. If you'd like to customize email content or have more control over deliverability, you can turn off the default emails and deliver your own emails using the WorkOS API.
|
|
11
11
|
|
|
12
12
|
---
|
|
13
13
|
|
|
@@ -28,17 +28,17 @@ Once you've turned off the default user invitation emails, use the information b
|
|
|
28
28
|
**[invitation.created](/events/invitation)**
|
|
29
29
|
: Event emitted when an invitation is created, which can be consumed using the events API or webhooks.
|
|
30
30
|
|
|
31
|
-
**[Get Invitation API](/reference/
|
|
31
|
+
**[Get Invitation API](/reference/authkit/invitation/get)**
|
|
32
32
|
: Used to retrieve the invitation object from the ID in the invitation created event.
|
|
33
33
|
|
|
34
|
-
**[Send Invitation API](/reference/
|
|
34
|
+
**[Send Invitation API](/reference/authkit/invitation/send)**
|
|
35
35
|
: Used to create an invitation via the API without handling the invitation created event.
|
|
36
36
|
|
|
37
37
|
### Set up your user invitation URL {{ "visibility": "no-quick-nav" }}
|
|
38
38
|
|
|
39
|
-
Make sure you have the correct user invitation URL set on your _Redirects_ page. The default setting is the AuthKit URL for accepting invitations. If you are using your own authentication UI, make sure the URL path is configured on your end to capture the `invitation_token` query parameter, and [pass it into one of the authenticate methods](/reference/
|
|
39
|
+
Make sure you have the correct user invitation URL set on your _Redirects_ page. The default setting is the AuthKit URL for accepting invitations. If you are using your own authentication UI, make sure the URL path is configured on your end to capture the `invitation_token` query parameter, and [pass it into one of the authenticate methods](/reference/authkit/authentication/code).
|
|
40
40
|
|
|
41
|
-

|
|
42
42
|
|
|
43
43
|
### (A) Handle manually creating invitations {{ "visibility": "no-quick-nav" }}
|
|
44
44
|
|
|
@@ -71,10 +71,10 @@ Once you've turned off the default Magic Auth emails, use the information below
|
|
|
71
71
|
**[magic_auth.created](/events/magic-auth)**
|
|
72
72
|
: Event emitted when a user initiates a Magic Auth authentication, which can be consumed using the events API or webhooks.
|
|
73
73
|
|
|
74
|
-
**[Get Magic Auth API](/reference/
|
|
74
|
+
**[Get Magic Auth API](/reference/authkit/magic-auth/get)**
|
|
75
75
|
: Used to retrieve the Magic Auth object from the ID in the Magic Auth created event.
|
|
76
76
|
|
|
77
|
-
**[Create Magic Auth API](/reference/
|
|
77
|
+
**[Create Magic Auth API](/reference/authkit/magic-auth/create)**
|
|
78
78
|
: Used to create a Magic Auth code via the API without handling the Magic Auth created event.
|
|
79
79
|
|
|
80
80
|
### (A) Handle Magic Auth codes created via AuthKit {{ "visibility": "no-quick-nav" }}
|
|
@@ -102,10 +102,10 @@ Once you've turned off the default email verification emails, use the informatio
|
|
|
102
102
|
**[email_verification.created](/events/email-verification)**
|
|
103
103
|
: Event emitted when a user requires email verification, which can be consumed using the events API or webhooks.
|
|
104
104
|
|
|
105
|
-
**[Get Email Verification API](/reference/
|
|
105
|
+
**[Get Email Verification API](/reference/authkit/email-verification/get)**
|
|
106
106
|
: Used to retrieve the email verification object from the ID in the email verification created event.
|
|
107
107
|
|
|
108
|
-
**[Email Verification Required error](/reference/
|
|
108
|
+
**[Email Verification Required error](/reference/authkit/authentication-errors/email-verification-required-error)**
|
|
109
109
|
: Returned in the API when attempting to authenticate a user that requires email verification.
|
|
110
110
|
|
|
111
111
|
### (A) Handle email verification codes created via AuthKit {{ "visibility": "no-quick-nav" }}
|
|
@@ -118,7 +118,7 @@ You can skip this step if you're building your own authentication app.
|
|
|
118
118
|
|
|
119
119
|
### (B) Handle email verification codes created via the API {{ "visibility": "no-quick-nav" }}
|
|
120
120
|
|
|
121
|
-
If you are using the [authentication API](/reference/
|
|
121
|
+
If you are using the [authentication API](/reference/authkit/authentication), an `email_verification_required` error will be returned if the user you're authenticating needs to verify their email. This error contains an `email_verification_id` that can be used to call the Get Email Verification API endpoint which returns the email verification object that contains the information needed to send the email.
|
|
122
122
|
|
|
123
123
|
### Send your email {{ "visibility": "no-quick-nav" }}
|
|
124
124
|
|
|
@@ -133,17 +133,17 @@ Once you've turned off the default password reset emails, use the information be
|
|
|
133
133
|
**[password_reset.created](/events/password-reset)**
|
|
134
134
|
: Event emitted when a user requests to reset their password, which can be consumed using the events API or webhooks.
|
|
135
135
|
|
|
136
|
-
**[Get Password Reset API](/reference/
|
|
136
|
+
**[Get Password Reset API](/reference/authkit/password-reset/get)**
|
|
137
137
|
: Used to retrieve the password reset object from the ID in the password reset created event.
|
|
138
138
|
|
|
139
|
-
**[Create Password Reset API](/reference/
|
|
139
|
+
**[Create Password Reset API](/reference/authkit/password-reset/create)**
|
|
140
140
|
: Used to create a password reset object via the API without handling the password reset created event.
|
|
141
141
|
|
|
142
142
|
### Set up your password reset URL {{ "visibility": "no-quick-nav" }}
|
|
143
143
|
|
|
144
|
-
Make sure you have the correct password reset URL set on your _Redirects_ page. The default setting is the AuthKit URL for resetting passwords. If you are using your own authentication UI, make sure the URL path is configured on your end to capture the `token` query parameter, and [use it to reset the password](/reference/
|
|
144
|
+
Make sure you have the correct password reset URL set on your _Redirects_ page. The default setting is the AuthKit URL for resetting passwords. If you are using your own authentication UI, make sure the URL path is configured on your end to capture the `token` query parameter, and [use it to reset the password](/reference/authkit/password-reset/reset-password).
|
|
145
145
|
|
|
146
|
-

|
|
147
147
|
|
|
148
148
|
### (A) Handle password resets created via AuthKit {{ "visibility": "no-quick-nav" }}
|
|
149
149
|
|
|
@@ -0,0 +1,89 @@
|
|
|
1
|
+
---
|
|
2
|
+
title: Directory Provisioning
|
|
3
|
+
description: Manage users and organization memberships via directory sync providers.
|
|
4
|
+
showNextPage: true
|
|
5
|
+
originalPath: .tmp-workos-clone/packages/docs/content/authkit/directory-provisioning.mdx
|
|
6
|
+
---
|
|
7
|
+
|
|
8
|
+
> Please reach out to [support@workos.com](mailto:support@workos.com) or via your team’s WorkOS Slack channel if you would like Directory Provisioning enabled.
|
|
9
|
+
|
|
10
|
+
## Introduction
|
|
11
|
+
|
|
12
|
+
Directory provisioning gives IT admins full control over user and membership management, eliminating the need for manually adding or removing members. Users from a directory are pre-provisioned and managed by their [Identity Provider](/glossary/idp).
|
|
13
|
+
|
|
14
|
+
## Initial configuration
|
|
15
|
+
|
|
16
|
+
A [Directory Sync](/directory-sync) integration will need to be configured for every organization that wants to source users and memberships via directory provisioning. Directories can be set up via the [WorkOS Dashboard](https://dashboard.workos.com/) with [Setup Links](/admin-portal/a-setup-link-from-workos-dashboard). You can also [integrate the Admin Portal with your app](/admin-portal/b-integrate-with-your-app) to generate links to configure directories.
|
|
17
|
+
|
|
18
|
+
### Supported directory providers
|
|
19
|
+
|
|
20
|
+
Directory provisioning is supported for all SCIM directory providers, Google Workspace, and SFTP.
|
|
21
|
+
|
|
22
|
+
## Provision users from a directory
|
|
23
|
+
|
|
24
|
+
Users provisioned through a directory with an email domain matching a verified organization domain will be automatically added as members of the organization, without needing an invitation.
|
|
25
|
+
|
|
26
|
+
Other users are created with `pending` memberships and receive an email [invitation](/authkit/invitations) to join the organization. Pending members cannot sign in until the invitation is accepted, at which point they become active organization members.
|
|
27
|
+
|
|
28
|
+
> [Invitation emails](/authkit/custom-emails/disabling-default-emails) can be disabled if you prefer to manage invitations with a custom approach.
|
|
29
|
+
|
|
30
|
+
## Manage users from a directory
|
|
31
|
+
|
|
32
|
+
In addition to provisioning new users, any updates to existing users and de-provisioning events will be reflected in AuthKit.
|
|
33
|
+
|
|
34
|
+
Users with email addresses matching one of the organization’s verified domains are fully managed by the directory. Updates to their attributes from the directory will override changes made through SSO, the API, or manually in the dashboard.
|
|
35
|
+
|
|
36
|
+
> If multiple organizations with directory provisioning contain the same verified domain, the user's name will always reflect the most recent directory update.
|
|
37
|
+
|
|
38
|
+
Other users, with email domains not verified by the organization, will not be fully managed by the directory, so updates made via SSO, API, or manually in the dashboard will persist.
|
|
39
|
+
|
|
40
|
+
When a user is de-provisioned in the directory, the [status](/reference/authkit/organization-membership) of their corresponding organization membership will be set to `inactive`. While the user will no longer be able to sign in to the organization, the membership and user are not automatically deleted.
|
|
41
|
+
|
|
42
|
+
If a user is re-provisioned in the directory, their organization membership will be reactivated with its previous role and its [status](/reference/authkit/organization-membership) will be set to `active`.
|
|
43
|
+
|
|
44
|
+
## Custom attributes
|
|
45
|
+
|
|
46
|
+
When using directory provisioning, [custom attributes](/directory-sync/attributes) configured on directory users are available on the corresponding organization membership. This allows you to access IdP-sourced attributes like department, job title, and cost center directly from the [membership object](/reference/authkit/organization-membership) or in [JWT templates](/authkit/jwt-templates).
|
|
47
|
+
|
|
48
|
+
When a directory user's attributes are updated, the changes are automatically reflected on the linked organization membership's `custom_attributes`.
|
|
49
|
+
|
|
50
|
+
> If the membership is also linked to an [SSO Profile](/reference/sso/profile), the directory user's custom attributes take precedence.
|
|
51
|
+
|
|
52
|
+
## Directory provisioning actions
|
|
53
|
+
|
|
54
|
+
Below is a list of directory provisioning and deprovisioning actions and the corresponding changes triggered in AuthKit. If you're using standalone Directory Sync, refer to the [standalone Directory Sync documentation](/directory-sync/api-overview/directory).
|
|
55
|
+
|
|
56
|
+
Actions depend on the user's email domain:
|
|
57
|
+
|
|
58
|
+
- A user is domain-managed when their email domain matches one of the [organization's verified domains](/reference/domain-verification). These users are fully managed by the directory.
|
|
59
|
+
- A user is a domain guest when their email domain does not match one of the [organization's verified domains](/reference/domain-verification). Changes only impact the linked organization membership.
|
|
60
|
+
|
|
61
|
+
| Directory Action | Changes triggered in WorkOS | Event(s) Emitted |
|
|
62
|
+
| ---------------------------------------------------- | ------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------ | ------------------------------------------------------------------------------------------------ |
|
|
63
|
+
| Directory user provisioned | [User](/reference/authkit/user) and [organization membership](/reference/authkit/organization-membership) objects created. Domain-managed users are created with an active status, while domain guest users are invited to the organization with a pending status. | [user.created](/events/user), [organization_membership.created](/events/organization-membership) |
|
|
64
|
+
| Directory user info updated | For domain-managed users, any updates to the user's name will be reflected on the [user](/reference/authkit/user) object. Otherwise, the user object will not be modified. User email address is always immutable. | [user.updated](/events/user), [organization_membership.updated](/events/organization-membership) |
|
|
65
|
+
| Directory user with active membership deprovisioned | Organization membership deactivated and all sessions for the user are revoked. Their role is reset to the default role. | [organization_membership.updated](/events/organization-membership) |
|
|
66
|
+
| Directory user with pending membership deprovisioned | Organization membership deleted. | [organization_membership.deleted](/events/organization-membership) |
|
|
67
|
+
| Directory user reactivated | Organization membership reactivated. | [organization_membership.updated](/events/organization-membership) |
|
|
68
|
+
|
|
69
|
+
---
|
|
70
|
+
|
|
71
|
+
## Frequently asked questions
|
|
72
|
+
|
|
73
|
+
### I am using directory provisioning, but some directory users aren't being provisioned in AuthKit. Why would a directory user not be provisioned in AuthKit?
|
|
74
|
+
|
|
75
|
+
Directory users need to have a primary email address to be provisioned in AuthKit. If the directory user is missing a primary email, they won't be provisioned. Additionally, if the primary email of a directory user is shared by another directory user, only one will be provisioned in AuthKit, as emails are unique to AuthKit users.
|
|
76
|
+
|
|
77
|
+
### If a user's email is changed in the directory, will this change be reflected on the user's email in WorkOS?
|
|
78
|
+
|
|
79
|
+
The email address on the [User object](/reference/authkit/user) is immutable, but the email on the underlying [directory user](/reference/directory-sync/directory-user) object will be modified.
|
|
80
|
+
|
|
81
|
+
### Why is there a distinction between domain-managed users and domain guest users?
|
|
82
|
+
|
|
83
|
+
For domain-managed users, the organization has proven they own the email domain through [domain verification](/authkit/domain-verification), and therefore have full control over the user's account and email. This allows the directory to manage all aspects of the [user object](/reference/authkit/user).
|
|
84
|
+
|
|
85
|
+
For domain guests, the organization has not proven ownership of the user's email domain. As a result, the organization only has the ability to manage data within the scope of the organization itself, represented by the [organization membership object](/reference/authkit/organization-membership).
|
|
86
|
+
|
|
87
|
+
### Why aren't organization memberships deactivated when a directory is deleted?
|
|
88
|
+
|
|
89
|
+
User deprovisioning and directory deletion have different behaviors because they serve different use cases. Deactivating all users is typically an off-boarding task that affects the entire organization, not just the directory. By leaving memberships active when a directory is deleted, customers can switch directory providers without the disruption of deactivating all memberships.
|
|
@@ -2,8 +2,7 @@
|
|
|
2
2
|
title: Domain Verification
|
|
3
3
|
description: Verify organization domains for secure authentication and provisioning.
|
|
4
4
|
showNextPage: true
|
|
5
|
-
originalPath:
|
|
6
|
-
.tmp-workos-clone/packages/docs/content/user-management/domain-verification.mdx
|
|
5
|
+
originalPath: .tmp-workos-clone/packages/docs/content/authkit/domain-verification.mdx
|
|
7
6
|
---
|
|
8
7
|
|
|
9
8
|
## Introduction
|
|
@@ -12,8 +11,8 @@ Domain verification allows IT admins to prove they control specific domains. Thi
|
|
|
12
11
|
|
|
13
12
|
Verifying an organization domain enables the following features:
|
|
14
13
|
|
|
15
|
-
1. Users with the verified domain who sign in with the organization’s SSO connection don't need to [verify their email](/
|
|
16
|
-
2. By default, users with the verified domain are managed by the organization's [domain policy](/
|
|
14
|
+
1. Users with the verified domain who sign in with the organization’s SSO connection don't need to [verify their email](/authkit/email-verification).
|
|
15
|
+
2. By default, users with the verified domain are managed by the organization's [domain policy](/authkit/organization-policies/domain-policy), allowing for enhanced control over authentication and membership.
|
|
17
16
|
|
|
18
17
|
## Self-serve domain verification
|
|
19
18
|
|
|
@@ -23,6 +22,6 @@ Domain verification can be delegated to the [Admin Portal domain verification fl
|
|
|
23
22
|
|
|
24
23
|
Verified domains may also be added manually via the [WorkOS Dashboard](https://dashboard.workos.com) or [API](/reference/organization/update). This shortcut is useful if the IT admin has already proven domain ownership in another context.
|
|
25
24
|
|
|
26
|
-
> Manually verified domains can be used to define a domain policy that applies to any users with email addresses on that domain. The organization that defines this [domain policy](/
|
|
25
|
+
> Manually verified domains can be used to define a domain policy that applies to any users with email addresses on that domain. The organization that defines this [domain policy](/authkit/organization-policies/domain-policy) exerts authentication policy control over that domain across your application. For this reason, it is important to verify ownership of manually added domains. Additionally, WorkOS does not allow addition of common consumer domains, like `gmail.com`.
|
|
27
26
|
|
|
28
|
-

|
|
@@ -2,7 +2,7 @@
|
|
|
2
2
|
title: Email + Password
|
|
3
3
|
description: Configuring email and password authentication and requirements.
|
|
4
4
|
showNextPage: true
|
|
5
|
-
originalPath: .tmp-workos-clone/packages/docs/content/
|
|
5
|
+
originalPath: .tmp-workos-clone/packages/docs/content/authkit/email-password.mdx
|
|
6
6
|
---
|
|
7
7
|
|
|
8
8
|
## Introduction
|
|
@@ -37,6 +37,6 @@ Disabling this method entirely will prevent users from signing up or signing in
|
|
|
37
37
|
|
|
38
38
|
## Integrating via the API
|
|
39
39
|
|
|
40
|
-
If you’d prefer to build and manage your own authentication UI, you can do so via the
|
|
40
|
+
If you’d prefer to build and manage your own authentication UI, you can do so via the AuthKit [Authentication API](/reference/authkit/authentication).
|
|
41
41
|
|
|
42
42
|
Examples of building custom UI are also [available on GitHub](https://github.com/workos/authkit).
|