n8n-nodes-trusera 0.4.1 → 0.4.3
This diff represents the content of publicly available package versions that have been released to one of the supported registries. The information contained in this diff is provided for informational purposes only and reflects changes between package versions as they appear in their respective public registries.
- package/README.md +296 -44
- package/dist/nodes/TruseraWebhook/TruseraWebhook.node.d.ts.map +1 -1
- package/dist/nodes/TruseraWebhook/TruseraWebhook.node.js +1 -0
- package/dist/nodes/TruseraWebhook/TruseraWebhook.node.js.map +1 -1
- package/nodes/TruseraWebhook/TruseraWebhook.node.ts +2 -1
- package/package.json +1 -1
package/README.md
CHANGED
|
@@ -1,76 +1,328 @@
|
|
|
1
1
|
# n8n-nodes-trusera
|
|
2
2
|
|
|
3
|
-
n8n
|
|
3
|
+
[](https://www.npmjs.com/package/n8n-nodes-trusera)
|
|
4
|
+
[](LICENSE)
|
|
4
5
|
|
|
5
|
-
|
|
6
|
+
n8n community node package that scans your workflows for AI security risks using [Trusera AI-BOM](https://github.com/trusera/ai-bom).
|
|
6
7
|
|
|
7
|
-
|
|
8
|
+
Drop a single node, activate, and visit `/webhook/trusera` to see a full interactive security dashboard of every AI component in your n8n instance.
|
|
9
|
+
|
|
10
|
+
|
|
11
|
+
|
|
12
|
+
## Installation
|
|
13
|
+
|
|
14
|
+
In your n8n instance:
|
|
15
|
+
|
|
16
|
+
1. Go to **Settings > Community Nodes**
|
|
17
|
+
2. Enter `n8n-nodes-trusera`
|
|
18
|
+
3. Click **Install**
|
|
19
|
+
|
|
20
|
+
Or install manually via CLI:
|
|
21
|
+
|
|
22
|
+
```bash
|
|
23
|
+
cd ~/.n8n/nodes
|
|
24
|
+
npm install n8n-nodes-trusera
|
|
25
|
+
# Restart n8n
|
|
26
|
+
```
|
|
27
|
+
|
|
28
|
+
## Quick Start (1 minute)
|
|
29
|
+
|
|
30
|
+
The **Trusera Webhook** node gives you a full security dashboard with zero configuration:
|
|
31
|
+
|
|
32
|
+
1. Create a new workflow
|
|
33
|
+
2. Add the **Trusera Webhook** node
|
|
34
|
+
3. Add your **n8n API** credential (Settings > n8n API > Create API Key)
|
|
35
|
+
4. Activate the workflow
|
|
36
|
+
5. Visit `http://your-n8n-url/webhook/trusera`
|
|
37
|
+
|
|
38
|
+
That's it. One node, full dashboard.
|
|
8
39
|
|
|
9
40
|
## Nodes
|
|
10
41
|
|
|
42
|
+
This package includes 5 nodes for different use cases:
|
|
43
|
+
|
|
44
|
+
### Trusera Webhook (Recommended)
|
|
45
|
+
|
|
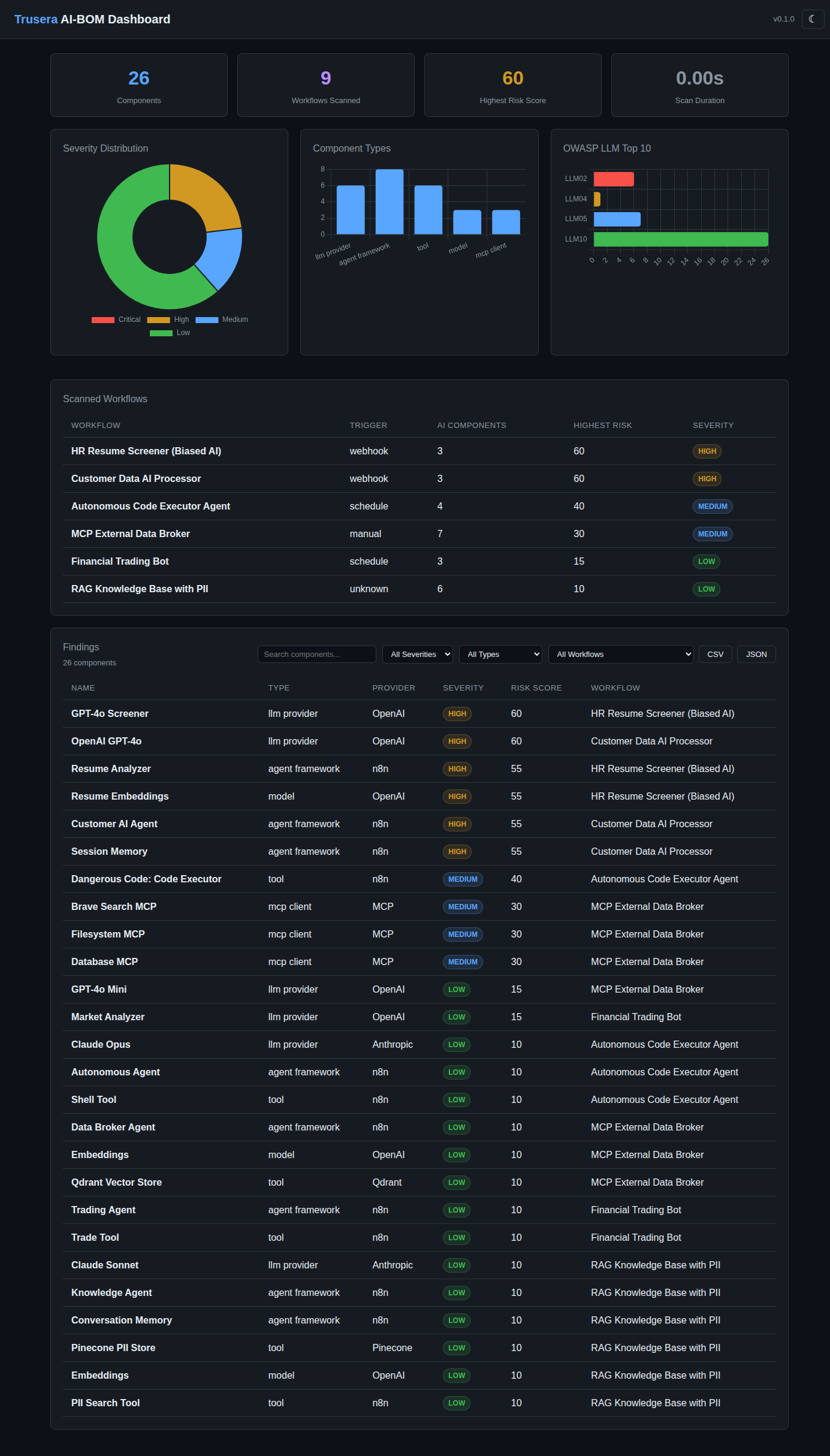
46
|
+
> **The one-node solution.** This is what most users need.
|
|
47
|
+
|
|
48
|
+
| | |
|
|
49
|
+
|---|---|
|
|
50
|
+
| **Type** | Trigger (webhook) |
|
|
51
|
+
| **Credential** | n8n API (required) |
|
|
52
|
+
| **URL** | `/webhook/trusera` |
|
|
53
|
+
| **Method** | GET |
|
|
54
|
+
|
|
55
|
+
Self-contained trigger node that:
|
|
56
|
+
- Fetches all workflows from your n8n instance via the REST API
|
|
57
|
+
- Scans every workflow for AI components and security risks
|
|
58
|
+
- Serves an interactive HTML dashboard directly at `/webhook/trusera`
|
|
59
|
+
|
|
60
|
+
**Parameters:**
|
|
61
|
+
|
|
62
|
+
| Parameter | Type | Default | Description |
|
|
63
|
+
|-----------|------|---------|-------------|
|
|
64
|
+
| Dashboard Password | string | _(empty)_ | Optional. If set, the dashboard is AES-256-GCM encrypted and visitors must enter this password to view it. |
|
|
65
|
+
|
|
66
|
+
**Setup:**
|
|
67
|
+
|
|
68
|
+
```
|
|
69
|
+
[Trusera Webhook] → (no other nodes needed)
|
|
70
|
+
```
|
|
71
|
+
|
|
72
|
+
---
|
|
73
|
+
|
|
74
|
+
### Trusera Dashboard
|
|
75
|
+
|
|
76
|
+
> Use this if you already have a built-in Webhook node configured and want to chain it.
|
|
77
|
+
|
|
78
|
+
| | |
|
|
79
|
+
|---|---|
|
|
80
|
+
| **Type** | Action |
|
|
81
|
+
| **Credential** | n8n API (required) |
|
|
82
|
+
| **Input** | Any trigger |
|
|
83
|
+
| **Output** | `{ html, headers, statusCode, body }` |
|
|
84
|
+
|
|
85
|
+
Fetches all workflows, scans them, and returns an HTML dashboard as output. Designed to connect after a built-in n8n Webhook node for custom webhook setups.
|
|
86
|
+
|
|
87
|
+
**Parameters:**
|
|
88
|
+
|
|
89
|
+
| Parameter | Type | Default | Description |
|
|
90
|
+
|-----------|------|---------|-------------|
|
|
91
|
+
| Dashboard Password | string | _(empty)_ | Optional AES-256-GCM encryption password. |
|
|
92
|
+
|
|
93
|
+
**Setup:**
|
|
94
|
+
|
|
95
|
+
```
|
|
96
|
+
[Webhook (GET /dashboard, responseMode: lastNode)] → [Trusera Dashboard]
|
|
97
|
+
```
|
|
98
|
+
|
|
99
|
+
Configure the Webhook node with:
|
|
100
|
+
- Response Mode: `Last Node`
|
|
101
|
+
- Response Content Type: `text/html`
|
|
102
|
+
- Response Data: `First Entry JSON`
|
|
103
|
+
- Response Property Name: `html`
|
|
104
|
+
|
|
105
|
+
---
|
|
106
|
+
|
|
11
107
|
### Trusera Scan
|
|
12
108
|
|
|
13
|
-
|
|
109
|
+
> Use this for programmatic scanning — pipe workflow JSON in, get structured results out.
|
|
110
|
+
|
|
111
|
+
| | |
|
|
112
|
+
|---|---|
|
|
113
|
+
| **Type** | Action |
|
|
114
|
+
| **Credential** | n8n API (optional) |
|
|
115
|
+
| **Input** | Workflow JSON |
|
|
116
|
+
| **Output** | Components array with risk scores |
|
|
117
|
+
|
|
118
|
+
Scans workflow JSON for AI components and returns structured scan results. Use this when you want to process scan results programmatically (e.g., send Slack alerts, store in a database, trigger CI/CD gates).
|
|
119
|
+
|
|
120
|
+
**Operations:**
|
|
121
|
+
|
|
122
|
+
| Operation | Description |
|
|
123
|
+
|-----------|-------------|
|
|
124
|
+
| Scan Workflow JSON | Scan a single workflow JSON from input |
|
|
125
|
+
| Scan Multiple Workflows | Scan an array of workflow JSONs |
|
|
14
126
|
|
|
15
|
-
|
|
16
|
-
|
|
17
|
-
|
|
18
|
-
|
|
19
|
-
|
|
20
|
-
|
|
21
|
-
|
|
127
|
+
**Parameters:**
|
|
128
|
+
|
|
129
|
+
| Parameter | Type | Default | Description |
|
|
130
|
+
|-----------|------|---------|-------------|
|
|
131
|
+
| Workflow JSON Field | string | `json` | Input field containing the workflow JSON |
|
|
132
|
+
| Workflows Array Field | string | `workflows` | Input field containing the workflows array |
|
|
133
|
+
| File Path | string | `workflow.json` | Identifier for the workflow in results |
|
|
134
|
+
|
|
135
|
+
**Setup:**
|
|
136
|
+
|
|
137
|
+
```
|
|
138
|
+
[HTTP Request (GET /api/v1/workflows)] → [Trusera Scan] → [Slack / Email / DB]
|
|
139
|
+
```
|
|
140
|
+
|
|
141
|
+
**Output example:**
|
|
142
|
+
|
|
143
|
+
```json
|
|
144
|
+
{
|
|
145
|
+
"components": [
|
|
146
|
+
{
|
|
147
|
+
"name": "GPT-4o Agent",
|
|
148
|
+
"type": "llm_provider",
|
|
149
|
+
"provider": "OpenAI",
|
|
150
|
+
"modelName": "gpt-4o",
|
|
151
|
+
"risk": { "score": 45, "severity": "medium", "factors": [...] },
|
|
152
|
+
"flags": ["no_error_handling", "unpinned_model"]
|
|
153
|
+
}
|
|
154
|
+
],
|
|
155
|
+
"totalComponents": 1
|
|
156
|
+
}
|
|
157
|
+
```
|
|
158
|
+
|
|
159
|
+
---
|
|
22
160
|
|
|
23
161
|
### Trusera Policy
|
|
24
162
|
|
|
25
|
-
|
|
163
|
+
> Use this to enforce security gates — block deployments with critical findings.
|
|
164
|
+
|
|
165
|
+
| | |
|
|
166
|
+
|---|---|
|
|
167
|
+
| **Type** | Action |
|
|
168
|
+
| **Input** | Scan results from Trusera Scan |
|
|
169
|
+
| **Output** | `{ passed: boolean, violations: string[] }` |
|
|
170
|
+
|
|
171
|
+
Evaluates scan results against configurable security policies. Chain after Trusera Scan to implement CI/CD security gates.
|
|
172
|
+
|
|
173
|
+
**Parameters:**
|
|
26
174
|
|
|
27
|
-
|
|
28
|
-
|
|
29
|
-
|
|
30
|
-
-
|
|
175
|
+
| Parameter | Type | Default | Description |
|
|
176
|
+
|-----------|------|---------|-------------|
|
|
177
|
+
| Scan Result Field | string | _(empty)_ | Field containing scan result (empty = entire input) |
|
|
178
|
+
| Max Critical | number | `0` | Maximum critical-severity components allowed |
|
|
179
|
+
| Max High | number | `-1` | Maximum high-severity components (-1 = unlimited) |
|
|
180
|
+
| Max Risk Score | number | `-1` | Maximum risk score for any component (-1 = unlimited) |
|
|
181
|
+
| Block Providers | string | _(empty)_ | Comma-separated provider blocklist (e.g., `OpenAI,Anthropic`) |
|
|
182
|
+
| Block Flags | string | _(empty)_ | Comma-separated flag blocklist (e.g., `hardcoded_api_key,no_auth`) |
|
|
183
|
+
|
|
184
|
+
**Setup:**
|
|
185
|
+
|
|
186
|
+
```
|
|
187
|
+
[Trusera Scan] → [Trusera Policy] → [IF passed] → [Deploy] / [Alert]
|
|
188
|
+
```
|
|
189
|
+
|
|
190
|
+
**Output example:**
|
|
191
|
+
|
|
192
|
+
```json
|
|
193
|
+
{
|
|
194
|
+
"passed": false,
|
|
195
|
+
"violations": [
|
|
196
|
+
"Found 2 critical components (max: 0)",
|
|
197
|
+
"Blocked provider: OpenAI"
|
|
198
|
+
],
|
|
199
|
+
"totalComponents": 15
|
|
200
|
+
}
|
|
201
|
+
```
|
|
202
|
+
|
|
203
|
+
---
|
|
31
204
|
|
|
32
205
|
### Trusera Report
|
|
33
206
|
|
|
34
|
-
|
|
207
|
+
> Use this to generate human-readable reports for Slack, email, or documentation.
|
|
208
|
+
|
|
209
|
+
| | |
|
|
210
|
+
|---|---|
|
|
211
|
+
| **Type** | Action |
|
|
212
|
+
| **Input** | Scan results from Trusera Scan |
|
|
213
|
+
| **Output** | Markdown or JSON report |
|
|
214
|
+
|
|
215
|
+
Generates formatted security reports from scan results.
|
|
216
|
+
|
|
217
|
+
**Parameters:**
|
|
35
218
|
|
|
36
|
-
|
|
37
|
-
|
|
38
|
-
|
|
219
|
+
| Parameter | Type | Default | Description |
|
|
220
|
+
|-----------|------|---------|-------------|
|
|
221
|
+
| Scan Result Field | string | _(empty)_ | Field containing scan result (empty = entire input) |
|
|
222
|
+
| Format | options | `markdown` | `markdown` or `jsonSummary` |
|
|
223
|
+
| Include Low Severity | boolean | `false` | Whether to include low-severity findings |
|
|
224
|
+
|
|
225
|
+
**Setup:**
|
|
226
|
+
|
|
227
|
+
```
|
|
228
|
+
[Trusera Scan] → [Trusera Report] → [Send Email / Slack Message]
|
|
229
|
+
```
|
|
230
|
+
|
|
231
|
+
---
|
|
39
232
|
|
|
40
233
|
## Credentials
|
|
41
234
|
|
|
42
|
-
###
|
|
235
|
+
### n8n API
|
|
236
|
+
|
|
237
|
+
The Trusera nodes connect to your n8n instance's own REST API to fetch workflows.
|
|
238
|
+
|
|
239
|
+
| Field | Description |
|
|
240
|
+
|-------|-------------|
|
|
241
|
+
| API Key | Your n8n API key (Settings > n8n API > Create API Key) |
|
|
242
|
+
| n8n Base URL | URL of your n8n instance (default: `http://localhost:5678`) |
|
|
43
243
|
|
|
44
|
-
|
|
244
|
+
## What It Detects
|
|
245
|
+
|
|
246
|
+
The scanner identifies AI components across your workflows:
|
|
247
|
+
|
|
248
|
+
- **LLM Providers** — OpenAI, Anthropic, Google Gemini, Mistral, Groq, Ollama, Azure OpenAI, AWS Bedrock, Cohere, HuggingFace
|
|
249
|
+
- **Agent Frameworks** — n8n AI agents, LangChain chains, ReAct agents
|
|
250
|
+
- **Tools** — Code execution nodes, HTTP request tools, vector stores (Pinecone, Qdrant, Weaviate, ChromaDB, Supabase)
|
|
251
|
+
- **MCP Clients** — Model Context Protocol connections to external servers
|
|
252
|
+
- **Models** — Embedding models, chat models, completion models
|
|
253
|
+
- **Memory** — Buffer memory, conversation memory, session-based memory
|
|
45
254
|
|
|
46
255
|
## Risk Flags
|
|
47
256
|
|
|
48
257
|
| Flag | Weight | Description |
|
|
49
|
-
|
|
50
|
-
| hardcoded_api_key | 30 | Hardcoded API key
|
|
51
|
-
| hardcoded_credentials | 30 | Hardcoded credentials in
|
|
52
|
-
| code_http_tools | 30 | Agent with code execution and HTTP tools |
|
|
53
|
-
| shadow_ai | 25 | AI dependency not declared in project files |
|
|
54
|
-
| webhook_no_auth | 25 |
|
|
55
|
-
| internet_facing | 20 | AI
|
|
56
|
-
| multi_agent_no_trust | 20 | Multi-agent system without trust boundaries |
|
|
57
|
-
| agent_chain_no_validation | 20 | Agent-to-agent chain without validation |
|
|
58
|
-
| mcp_unknown_server | 20 | MCP client connected to unknown server |
|
|
59
|
-
| no_auth | 15 | AI endpoint without authentication |
|
|
60
|
-
| no_rate_limit | 10 | No rate limiting on AI endpoint |
|
|
61
|
-
| deprecated_model | 10 | Using deprecated AI model |
|
|
62
|
-
| no_error_handling | 10 | No error handling for AI calls |
|
|
63
|
-
| unpinned_model | 5 | Model version not pinned |
|
|
258
|
+
|------|--------|-------------|
|
|
259
|
+
| `hardcoded_api_key` | 30 | Hardcoded API key in workflow JSON |
|
|
260
|
+
| `hardcoded_credentials` | 30 | Hardcoded credentials in node parameters |
|
|
261
|
+
| `code_http_tools` | 30 | Agent with both code execution and HTTP request tools |
|
|
262
|
+
| `shadow_ai` | 25 | AI dependency not declared in project files |
|
|
263
|
+
| `webhook_no_auth` | 25 | Webhook trigger without authentication |
|
|
264
|
+
| `internet_facing` | 20 | AI components exposed to internet via webhook |
|
|
265
|
+
| `multi_agent_no_trust` | 20 | Multi-agent system without trust boundaries |
|
|
266
|
+
| `agent_chain_no_validation` | 20 | Agent-to-agent chain without output validation |
|
|
267
|
+
| `mcp_unknown_server` | 20 | MCP client connected to unknown/external server |
|
|
268
|
+
| `no_auth` | 15 | AI endpoint without authentication |
|
|
269
|
+
| `no_rate_limit` | 10 | No rate limiting on AI endpoint |
|
|
270
|
+
| `deprecated_model` | 10 | Using a deprecated AI model version |
|
|
271
|
+
| `no_error_handling` | 10 | No error handling configured for AI calls |
|
|
272
|
+
| `unpinned_model` | 5 | Model version not pinned to specific release |
|
|
64
273
|
|
|
65
274
|
## Severity Thresholds
|
|
66
275
|
|
|
67
|
-
| Severity | Score Range |
|
|
68
|
-
|
|
69
|
-
| Critical | 76 - 100 |
|
|
70
|
-
| High | 51 - 75 |
|
|
71
|
-
| Medium | 26 - 50 |
|
|
72
|
-
| Low | 0 - 25 |
|
|
276
|
+
| Severity | Score Range | Color |
|
|
277
|
+
|----------|-------------|-------|
|
|
278
|
+
| Critical | 76 - 100 | Red |
|
|
279
|
+
| High | 51 - 75 | Orange |
|
|
280
|
+
| Medium | 26 - 50 | Blue |
|
|
281
|
+
| Low | 0 - 25 | Green |
|
|
282
|
+
|
|
283
|
+
## Dashboard Features
|
|
284
|
+
|
|
285
|
+
The interactive HTML dashboard includes:
|
|
286
|
+
|
|
287
|
+
- **Summary cards** — total components, workflows scanned, highest risk score, scan duration
|
|
288
|
+
- **Severity distribution chart** — donut chart showing critical/high/medium/low breakdown
|
|
289
|
+
- **Component types chart** — bar chart of LLM providers, agents, tools, models, MCP clients
|
|
290
|
+
- **OWASP LLM Top 10 chart** — risk flags mapped to OWASP categories
|
|
291
|
+
- **Scanned workflows table** — each workflow with trigger type, AI component count, highest risk, severity badge
|
|
292
|
+
- **Findings table** — all detected components with name, type, provider, severity, risk score, workflow
|
|
293
|
+
- **Filters** — search by name, filter by severity/type/workflow
|
|
294
|
+
- **Export** — CSV and JSON export buttons
|
|
295
|
+
- **Dark/light mode** — toggle in the header
|
|
296
|
+
- **Password protection** — optional AES-256-GCM encryption
|
|
297
|
+
|
|
298
|
+
## Example Workflows
|
|
299
|
+
|
|
300
|
+
### Minimal: Security Dashboard
|
|
301
|
+
|
|
302
|
+
```
|
|
303
|
+
[Trusera Webhook] → activate → visit /webhook/trusera
|
|
304
|
+
```
|
|
305
|
+
|
|
306
|
+
### CI/CD Gate: Block Risky Deployments
|
|
307
|
+
|
|
308
|
+
```
|
|
309
|
+
[Schedule Trigger] → [HTTP Request: GET /api/v1/workflows]
|
|
310
|
+
→ [Trusera Scan]
|
|
311
|
+
→ [Trusera Policy (maxCritical: 0)]
|
|
312
|
+
→ [IF: passed = true]
|
|
313
|
+
→ Yes: [Deploy]
|
|
314
|
+
→ No: [Slack Alert]
|
|
315
|
+
```
|
|
316
|
+
|
|
317
|
+
### Weekly Report: Email Summary
|
|
318
|
+
|
|
319
|
+
```
|
|
320
|
+
[Schedule Trigger (weekly)] → [HTTP Request: GET /api/v1/workflows]
|
|
321
|
+
→ [Trusera Scan (scanMultiple)]
|
|
322
|
+
→ [Trusera Report (markdown)]
|
|
323
|
+
→ [Send Email]
|
|
324
|
+
```
|
|
73
325
|
|
|
74
326
|
## License
|
|
75
327
|
|
|
76
|
-
|
|
328
|
+
MIT
|
|
@@ -1 +1 @@
|
|
|
1
|
-
{"version":3,"file":"TruseraWebhook.node.d.ts","sourceRoot":"","sources":["../../../nodes/TruseraWebhook/TruseraWebhook.node.ts"],"names":[],"mappings":"AAAA,OAAO,KAAK,EACV,iBAAiB,EACjB,oBAAoB,EACpB,SAAS,EACT,oBAAoB,EACrB,MAAM,cAAc,CAAC;AAKtB,qBAAa,cAAe,YAAW,SAAS;IAC9C,WAAW,EAAE,oBAAoB,
|
|
1
|
+
{"version":3,"file":"TruseraWebhook.node.d.ts","sourceRoot":"","sources":["../../../nodes/TruseraWebhook/TruseraWebhook.node.ts"],"names":[],"mappings":"AAAA,OAAO,KAAK,EACV,iBAAiB,EACjB,oBAAoB,EACpB,SAAS,EACT,oBAAoB,EACrB,MAAM,cAAc,CAAC;AAKtB,qBAAa,cAAe,YAAW,SAAS;IAC9C,WAAW,EAAE,oBAAoB,CAyC/B;IAEI,OAAO,CAAC,IAAI,EAAE,iBAAiB,GAAG,OAAO,CAAC,oBAAoB,CAAC;CA+DtE"}
|
|
@@ -15,6 +15,7 @@ class TruseraWebhook {
|
|
|
15
15
|
description: 'One-node security dashboard — add n8n API credentials, activate, and visit /webhook/trusera to see your AI-BOM report.',
|
|
16
16
|
defaults: {
|
|
17
17
|
name: 'Trusera Webhook',
|
|
18
|
+
webhookId: 'trusera-ai-bom',
|
|
18
19
|
},
|
|
19
20
|
inputs: [],
|
|
20
21
|
outputs: ['main'],
|
|
@@ -1 +1 @@
|
|
|
1
|
-
{"version":3,"file":"TruseraWebhook.node.js","sourceRoot":"","sources":["../../../nodes/TruseraWebhook/TruseraWebhook.node.ts"],"names":[],"mappings":";;;AAOA,+CAAkD;AAClD,2DAAgE;AAEhE,MAAa,cAAc;IAA3B;QACE,gBAAW,GAAyB;YAClC,WAAW,EAAE,iBAAiB;YAC9B,IAAI,EAAE,gBAAgB;YACtB,IAAI,EAAE,kBAAkB;YACxB,KAAK,EAAE,CAAC,SAAS,CAAC;YAClB,OAAO,EAAE,CAAC;YACV,QAAQ,EAAE,uBAAuB;YACjC,WAAW,EACT,wHAAwH;YAC1H,QAAQ,EAAE;gBACR,IAAI,EAAE,iBAAiB;
|
|
1
|
+
{"version":3,"file":"TruseraWebhook.node.js","sourceRoot":"","sources":["../../../nodes/TruseraWebhook/TruseraWebhook.node.ts"],"names":[],"mappings":";;;AAOA,+CAAkD;AAClD,2DAAgE;AAEhE,MAAa,cAAc;IAA3B;QACE,gBAAW,GAAyB;YAClC,WAAW,EAAE,iBAAiB;YAC9B,IAAI,EAAE,gBAAgB;YACtB,IAAI,EAAE,kBAAkB;YACxB,KAAK,EAAE,CAAC,SAAS,CAAC;YAClB,OAAO,EAAE,CAAC;YACV,QAAQ,EAAE,uBAAuB;YACjC,WAAW,EACT,wHAAwH;YAC1H,QAAQ,EAAE;gBACR,IAAI,EAAE,iBAAiB;gBACvB,SAAS,EAAE,gBAAgB;aACQ;YACrC,MAAM,EAAE,EAAE;YACV,OAAO,EAAE,CAAC,MAAM,CAAC;YACjB,WAAW,EAAE;gBACX;oBACE,IAAI,EAAE,YAAY;oBAClB,QAAQ,EAAE,IAAI;iBACf;aACF;YACD,QAAQ,EAAE;gBACR;oBACE,IAAI,EAAE,SAAS;oBACf,UAAU,EAAE,KAAK;oBACjB,YAAY,EAAE,UAAU;oBACxB,IAAI,EAAE,SAAS;oBACf,UAAU,EAAE,IAAI;iBACjB;aACF;YACD,UAAU,EAAE;gBACV;oBACE,WAAW,EAAE,oBAAoB;oBACjC,IAAI,EAAE,UAAU;oBAChB,IAAI,EAAE,QAAQ;oBACd,WAAW,EAAE,EAAE,QAAQ,EAAE,IAAI,EAAE;oBAC/B,OAAO,EAAE,EAAE;oBACX,WAAW,EACT,4GAA4G;iBAC/G;aACF;SACF,CAAC;IAiEJ,CAAC;IA/DC,KAAK,CAAC,OAAO;QACX,MAAM,GAAG,GAAG,IAAI,CAAC,iBAAiB,EAAE,CAAC;QAErC,IAAI,CAAC;YACH,MAAM,KAAK,GAAG,MAAM,IAAI,CAAC,cAAc,CAAC,YAAY,CAAC,CAAC;YACtD,MAAM,OAAO,GAAG,CAAE,KAAK,CAAC,OAAkB,IAAI,uBAAuB,CAAC,CAAC,OAAO,CAAC,KAAK,EAAE,EAAE,CAAC,CAAC;YAC1F,MAAM,MAAM,GAAG,KAAK,CAAC,MAAgB,CAAC;YACtC,MAAM,QAAQ,GAAG,IAAI,CAAC,gBAAgB,CAAC,UAAU,EAAE,EAAE,CAAW,CAAC;YAEjE,mDAAmD;YACnD,MAAM,YAAY,GAAmC,EAAE,CAAC;YACxD,IAAI,MAAM,GAAkB,IAAI,CAAC;YACjC,GAAG,CAAC;gBACF,MAAM,GAAG,GACP,GAAG,OAAO,6BAA6B;oBACvC,CAAC,MAAM,CAAC,CAAC,CAAC,WAAW,MAAM,EAAE,CAAC,CAAC,CAAC,EAAE,CAAC,CAAC;gBACtC,MAAM,IAAI,GAAG,MAAM,KAAK,CAAC,GAAG,EAAE;oBAC5B,OAAO,EAAE;wBACP,eAAe,EAAE,MAAM;wBACvB,QAAQ,EAAE,kBAAkB;qBAC7B;iBACF,CAAC,CAAC;gBACH,IAAI,CAAC,IAAI,CAAC,EAAE,EAAE,CAAC;oBACb,MAAM,IAAI,KAAK,CAAC,kBAAkB,IAAI,CAAC,MAAM,IAAI,MAAM,IAAI,CAAC,IAAI,EAAE,EAAE,CAAC,CAAC;gBACxE,CAAC;gBACD,MAAM,IAAI,GAAG,CAAC,MAAM,IAAI,CAAC,IAAI,EAAE,CAG9B,CAAC;gBACF,YAAY,CAAC,IAAI,CAAC,GAAG,IAAI,CAAC,IAAI,CAAC,CAAC;gBAChC,MAAM,GAAG,IAAI,CAAC,UAAU,IAAI,IAAI,CAAC;YACnC,CAAC,QAAQ,MAAM,EAAE;YAEjB,qBAAqB;YACrB,MAAM,SAAS,GAAG,YAAY,CAAC,GAAG,CAAC,CAAC,EAAE,EAAE,EAAE,CAAC,CAAC;gBAC1C,IAAI,EAAE,EAAE;gBACR,QAAQ,EAAG,EAAE,CAAC,IAAe,IAAK,EAAE,CAAC,EAAa,IAAI,SAAS;aAChE,CAAC,CAAC,CAAC;YACJ,MAAM,UAAU,GAAG,IAAA,uBAAa,EAAC,SAAS,CAAC,CAAC;YAE5C,0BAA0B;YAC1B,MAAM,IAAI,GAAG,IAAA,qCAAqB,EAAC,UAAU,EAAE,QAAQ,IAAI,SAAS,CAAC,CAAC;YAEtE,sBAAsB;YACtB,GAAG,CAAC,SAAS,CAAC,cAAc,EAAE,0BAA0B,CAAC,CAAC;YAC1D,GAAG,CAAC,MAAM,CAAC,GAAG,CAAC,CAAC,GAAG,CAAC,IAAI,CAAC,CAAC;QAC5B,CAAC;QAAC,OAAO,GAAG,EAAE,CAAC;YACb,GAAG,CAAC,SAAS,CAAC,cAAc,EAAE,0BAA0B,CAAC,CAAC;YAC1D,GAAG,CAAC,MAAM,CAAC,GAAG,CAAC,CAAC,GAAG,CACjB,yEAAyE;gBACzE,kCAAkC;gBAClC,0BAA2B,GAAa,CAAC,OAAO,QAAQ;gBACxD,gBAAgB,CACjB,CAAC;QACJ,CAAC;QAED,OAAO;YACL,iBAAiB,EAAE,IAAI;YACvB,YAAY,EAAE;gBACZ,CAAC,EAAE,IAAI,EAAE,EAAE,MAAM,EAAE,IAAI,EAAE,SAAS,EAAE,IAAI,IAAI,EAAE,CAAC,WAAW,EAAE,EAAE,EAAE,CAAC;aAClE;SACF,CAAC;IACJ,CAAC;CACF;AA3GD,wCA2GC"}
|
|
@@ -20,7 +20,8 @@ export class TruseraWebhook implements INodeType {
|
|
|
20
20
|
'One-node security dashboard — add n8n API credentials, activate, and visit /webhook/trusera to see your AI-BOM report.',
|
|
21
21
|
defaults: {
|
|
22
22
|
name: 'Trusera Webhook',
|
|
23
|
-
|
|
23
|
+
webhookId: 'trusera-ai-bom',
|
|
24
|
+
} as INodeTypeDescription['defaults'],
|
|
24
25
|
inputs: [],
|
|
25
26
|
outputs: ['main'],
|
|
26
27
|
credentials: [
|