@pwrdrvr/microapps-cdk 0.4.0-alpha.11 → 0.4.0-alpha.13
This diff represents the content of publicly available package versions that have been released to one of the supported registries. The information contained in this diff is provided for informational purposes only and reflects changes between package versions as they appear in their respective public registries.
- package/.jsii +99 -53
- package/API.md +28 -10
- package/README.md +9 -17
- package/changelog.md +1 -1
- package/lib/MicroApps.d.ts +5 -1
- package/lib/MicroApps.js +4 -3
- package/lib/MicroAppsAPIGwy.js +1 -1
- package/lib/MicroAppsCF.js +1 -1
- package/lib/MicroAppsChildDeployer.d.ts +3 -1
- package/lib/MicroAppsChildDeployer.js +3 -3
- package/lib/MicroAppsEdgeToOrigin.js +1 -1
- package/lib/MicroAppsS3.js +1 -1
- package/lib/MicroAppsSvcs.d.ts +5 -1
- package/lib/MicroAppsSvcs.js +6 -5
- package/lib/MicroAppsTable.js +1 -1
- package/lib/microapps-deployer/index.js +46 -46
- package/lib/microapps-deployer/index.js.map +4 -4
- package/lib/microapps-edge-to-origin/index.js +1 -1
- package/lib/microapps-edge-to-origin/index.js.map +2 -2
- package/package.json +1 -1
- package/releasetag.txt +1 -1
- package/version.txt +1 -1
package/.jsii
CHANGED
|
@@ -3100,7 +3100,7 @@
|
|
|
3100
3100
|
},
|
|
3101
3101
|
"name": "@pwrdrvr/microapps-cdk",
|
|
3102
3102
|
"readme": {
|
|
3103
|
-
"markdown": "[](https://github.com/pwrdrvr/microapps-core/actions/workflows/ci.yml) [](https://github.com/pwrdrvr/microapps-core/actions/workflows/main-build.yml) [](https://github.com/pwrdrvr/microapps-core/actions/workflows/release.yml)\n\n# Overview\n\nThe MicroApps project enables rapidly deploying many web apps to AWS on a single shared host name, fronted by a CloudFront Distribution, serving static assets from an S3 Bucket, and routing application requests via API Gateway. MicroApps is delivered as a CDK Construct for deployment, although alternative deployment methods can be used if desired and implemented.\n\nMicroApps allows many versions of an application to be deployed either as ephemeral deploys (e.g. for pull request builds) or as semi-permanent deploys. The `microapps-router` Lambda function handled routing requests to apps to the current version targeted for a particular application start request using rules as complex as one is interested in implementing (e.g. A/B testing integration, canary releases, per-user rules for logged in users, per-group, per-deparment, and default rules).\n\nUsers start applications via a URL such as `[/{prefix}]/{appname}/`, which hits the `microapps-router` Lambda@Edge OriginRequest handler that looks up the version of the application to be run, and either forwards the request to the target Lambda Function URL (`--startupType direct` invoke mode) or returns a transparent `iframe` (`--startupType iframe`) with a link to that version. `direct` mode works with frameworks, like Next.js, that can return pages that have build-time computed relative URLs to static resources and API calls. `iframe` mode works with frameworks that do not write computed relative URLs at build time and/or that do not use URLs that are completely relative to wherever the applications is rooted at runtime; this mode is primarily for quick prototyping as it has other complications (such as indirect access to query strings). The URL seen by the user in the browser (and available for bookmarking) has no version in it, so subsequent launches (e.g. the next day or just in another tab) will lookup the version again. All relative URL API requests (e.g. `some/api/path`) will go to the corresponding API version that matches the version of the loaded static files, eliminating issues of incompatibility between static files and API deployments.\n\nFor development / testing purposes only, each version of an applicaton can be accessed directly via a URL of the patterns `[/{prefix}]/{appname}?appver={semver}` for `direct` mode or `[/{prefix}]/{appname}/{semver}/` for `iframe` mode. These \"versioned\" URLs are not intended to be advertised to end users as they would cause a user to be stuck on a particular version of the app if the URL was bookmarked. Note that the system does not limit access to particular versions of an application, as of 2023-03-04, but that can be added as a feature.\n\n# Table of Contents <!-- omit in toc -->\n\n- [Overview](#overview)\n- [Why MicroApps](#why-microapps)\n- [Request Routing for Static Assets / App - Diagram](#request-routing-for-static-assets--app---diagram)\n- [Request Dispatch Model for Multi-Account Deployments](#request-dispatch-model-for-multi-account-deployments)\n- [Video Preview of the Deploying CDK Construct](#video-preview-of-the-deploying-cdk-construct)\n- [Installation / CDK Constructs](#installation--cdk-constructs)\n- [Tutorial - Bootstrapping a Deploy](#tutorial---bootstrapping-a-deploy)\n- [Limitations / Future Development](#limitations--future-development)\n- [Related Projects / Components](#related-projects--components)\n- [Why Lambda @ Origin and Not Lambda @ Edge for Apps](#why-lambda--origin-and-not-lambda--edge-for-apps)\n- [Architecure Diagram](#architecure-diagram)\n- [Project Layout](#project-layout)\n- [Creating a MicroApp Using Zip Lambda Functions](#creating-a-microapp-using-zip-lambda-functions)\n- [Creating a MicroApp Using Docker Lambda Functions](#creating-a-microapp-using-docker-lambda-functions)\n - [Next.js Apps](#nextjs-apps)\n - [Modify package.json](#modify-packagejson)\n - [Install Dependencies](#install-dependencies)\n - [Dockerfile](#dockerfile)\n - [next.config.js](#nextconfigjs)\n- [Troubleshooting](#troubleshooting)\n - [CloudFront Requests to API Gateway are Rejected with 403 Forbidden](#cloudfront-requests-to-api-gateway-are-rejected-with-403-forbidden)\n - [SignatureV4 Headers](#signaturev4-headers)\n\n# Why MicroApps\n\nMicroApps are like micro services, but for Web UIs. A MicroApp allows a single functional site to be developed by many independent teams within an organization. Teams must coordinate deployments and agree upon one implementation technology and framework when building a monolithic, or even a monorepo, web application.\n\nTeams using MicroApps can deploy independently of each other with coordination being required only at points of intentional integration (e.g. adding a feature to pass context from one MicroApp to another or coordination of a major feature release to users) and sharing UI styles, if desired (it is possible to build styles that look the same across many different UI frameworks).\n\nMicroApps also allow each team to use a UI framework and backend language that is most appropriate for their solving their business problem. Not every app has to use React or Next.js or even Node on the backend, but instead they can use whatever framework they want and Java, Go, C#, Python, etc. for UI API calls.\n\nFor internal sites, or logged-in-customer sites, different tools or products can be hosted in entirely independent MicroApps. A menuing system / toolbar application can be created as a MicroApp and that menu app can open the apps in the system within a transparent iframe. For externally facing sites, such as for an e-commerce site, it is possible to have a MicroApp serving `/product/...`, another serving `/search/...`, another serving `/`, etc.\n\n# Request Routing for Static Assets / App - Diagram\n\n\n\n# Request Dispatch Model for Multi-Account Deployments\n\nNote: requests can also be dispatched into the same account, but this model is more likely to be used by organizations with many AWS accounts.\n\n\n\n# Video Preview of the Deploying CDK Construct\n\n\n\n# Installation / CDK Constructs\n\n- `npm i --save-dev @pwrdrvr/microapps-cdk`\n- Add `MicroApps` construct to your stack\n- The `MicroApps` construct does a \"turn-key\" deployment complete with the Release app\n- [Construct Hub](https://constructs.dev/packages/@pwrdrvr/microapps-cdk/)\n - CDK API docs\n - Python, DotNet, Java, JS/TS installation instructions\n\n# Tutorial - Bootstrapping a Deploy\n\n- `git clone https://github.com/pwrdrvr/microapps-core.git`\n - Note: the repo is only being for the example CDK Stack, it is not necessary to clone the repo when used in a custom CDK Stack\n- `cd microapps-core`\n- `npm i -g aws-cdk`\n - Install AWS CDK v2 CLI\n- `asp [my-sso-profile-name]`\n - Using the `aws` plugin from `oh-my-zsh` for AWS SSO\n - Of course, there are other methods of setting env vars\n- `aws sso login`\n - Establish an AWS SSO session\n- `export AWS_REGION=us-east-2`\n - Region needs to be set for the Lambda invoke - This can be done other ways in `~/.aws/config` as well\n- `./deploy.sh`\n - Deploys the CDK Stack\n - Essentially runs two commands along with extraction of outputs:\n - `npx cdk deploy --context @pwrdrvr/microapps:deployReleaseApp=true microapps-basic`\n - `npx microapps-publish publish --app-name release --new-version ${RELEASE_APP_PACKAGE_VERSION} --deployer-lambda-name ${DEPLOYER_LAMBDA_NAME} --app-lambda-name ${RELEASE_APP_LAMBDA_NAME} --static-assets-path node_modules/@pwrdrvr/microapps-app-release-cdk/lib/static_files/release/${RELEASE_APP_PACKAGE_VERSION}/ --overwrite --no-cache`\n - URL will be printed as last output\n\n# Limitations / Future Development\n\n- AWS Only\n - For the time being this has only been implemented for AWS technologies and APIs\n - It is possible that Azure and GCP have sufficient support to enable porting the framework\n - CDK would have to be replaced as well (unless it's made available for Azure and GCP in the near future)\n- `microapps-publish` only supports Lambda function apps\n - There is no technical reason for the apps to only run as Lambda functions\n - Web apps could just as easily run on EC2, Kubernetes, EKS, ECS, etc\n - Anything that API Gateway can route to can work for serving a MicroApp\n - The publish tool needs to provide additional options for setting up the API Gateway route to the app\n- Authentication\n - Authentication requires rolling your own API Gateway and CloudFront deployment at the moment\n - The \"turn key\" CDK Construct should provide options to show an example of how authentication can be integrated\n- Release Rules\n - Currently only a Default rule is supported\n - Need to evaluate if a generic implementation can be made, possibly allowing plugins or webhooks to support arbitrary rules\n - If not possible to make it perfectly generic, consider providing a more complete reference implementation of examples\n\n# Related Projects / Components\n\n- Release App\n - The Release app is an initial, rudimentary, release control console for setting the default version of an application\n - Built with Next.js\n - [pwrdrvr/microapps-app-release](https://github.com/pwrdrvr/microapps-app-release)\n- Next.js Demo App\n - The Next.js Tutorial application deployed as a MicroApp\n - [pwrdrvr/serverless-nextjs-demo](https://github.com/pwrdrvr/serverless-nextjs-demo)\n\n\n# Why Lambda @ Origin and Not Lambda @ Edge for Apps\n\nCalling resources (DBs and other services) and waiting for a long synchronous response is an anti-pattern in Lambda as the Lambda function will be billed for the time spent waiting for the response. This is especially true for Lambda@Edge as the cost is 3x higher than Lambda at the origin.\n\nWith Lambda@Edge (even with Origin Requests) the cost is 3x higher per GB-second and the time spent waiting for a 1 ms service response from an origin that is 250 ms away is 750x higher (250 ms / 1ms * 3x higher cost) than making that same request within the region where the resource resides.\n\n- Lambda@Edge is _at least_ 3x more expensive than Lambda at the origin:\n - In US East 1, the price per GB-Second is $0.00005001 for Lambda@Edge\n - Source: https://aws.amazon.com/lambda/pricing/ (bottom of page)\n - Updated: 2023-03-04\n - In US East 1, the price per GB-Second is $0.0000166667 for Lambda at the origin on x86\n - Source: https://aws.amazon.com/lambda/pricing/\n - Updated: 2023-03-04\n - Ratio\n - Lambda@Edge / Lambda@Origin = $0.00005001 / $0.0000166667 = 3.0006x\n- Any DB or services calls from Lambda@Edge back to the origin will pay that 3x higher per GB-Second cost for any time spent waiting to send the request and get a response. Example:\n - Lambda@Edge\n - 0.250s Round Trip Time (RTT) for EU-zone edge request to hit US-East 1 Origin\n - 0.200s DB lookup time\n - 0.050s CPU usage to process the DB response\n - 0.500s total billed time @ $0.00005001 @ 128 MB\n - $0.000003125625 total charge\n - Lambda at Origin\n - RTT does not apply (it's effectively 1-2 ms to hit a DB in the same region)\n - 0.200s DB lookup time\n - 0.050s CPU usage to process the DB response\n - 0.250s total billed time @ $0.0000166667 @ 128 MB\n - Half the billed time of running on Lambda@Edge\n - 1/6th the cost of running on Lambda@Edge:\n - $0.000000520834375 total charge (assuming no CPU time to process the response)\n - $0.000003125625 / $0.000000520834375 = 6x more expensive in Lambda@Edge\n\n# Architecure Diagram\n\n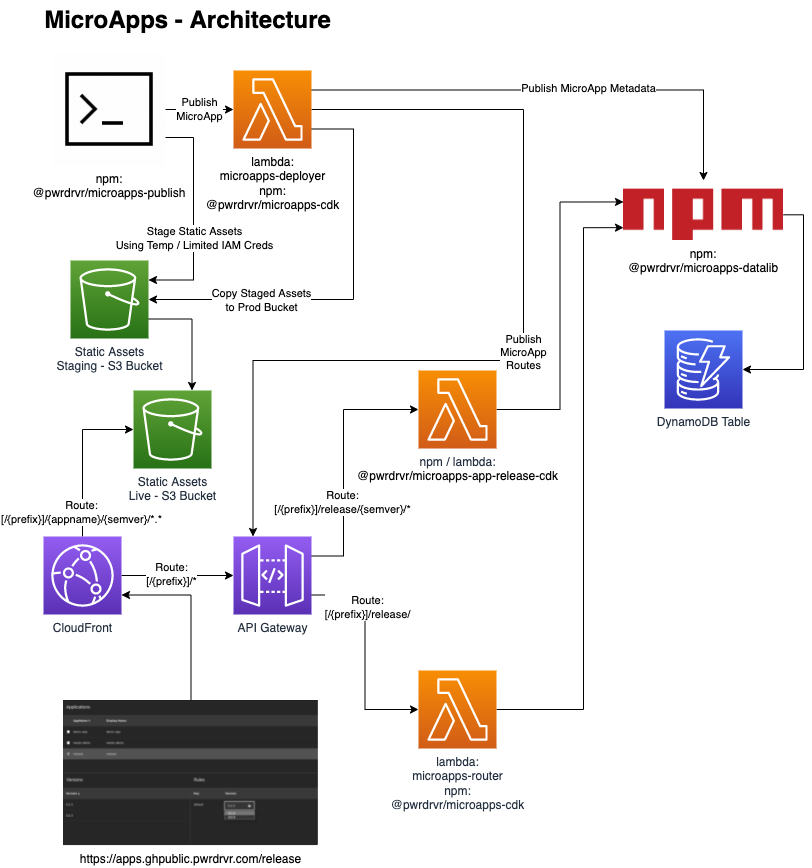\n\n# Project Layout\n\n- [packages/cdk](https://github.com/pwrdrvr/microapps-core/tree/main/packages/cdk)\n - Example CDK Stack\n - Deploys MicroApps CDK stack for the GitHub Workflows\n - Can be used as an example of how to use the MicroApps CDK Construct\n- [packages/demo-app](https://github.com/pwrdrvr/microapps-core/tree/main/packages/demo-app)\n - Example app with static resources and a Lambda function\n - Does not use any Web UI framework at all\n- [packages/microapps-cdk](https://github.com/pwrdrvr/microapps-core/tree/main/packages/microapps-cdk)\n - MicroApps\n - \"Turn key\" CDK Construct that creates all assets needed for a working MicroApps deployment\n - MicroAppsAPIGwy\n - Create APIGateway HTTP API\n - Creates domain names to point to the edge (Cloudfront) and origin (API Gateway)\n - MicroAppsCF\n - Creates Cloudfront distribution\n - MicroAppsS3\n - Creates S3 buckets\n - MicroAppsSvcs\n - Create DynamoDB table\n - Create Deployer Lambda function\n - Create Router Lambda function\n- [packages/microapps-datalib](https://github.com/pwrdrvr/microapps-core/tree/main/packages/microapps-datalib)\n - Installed from `npm`:\n - `npm i -g @pwrdrvr/microapps-datalib`\n - APIs for access to the DynamoDB Table used by `microapps-publish`, `microapps-deployer`, and `@pwrdrvr/microapps-app-release-cdk`\n- [packages/microapps-deployer](https://github.com/pwrdrvr/microapps-core/tree/main/packages/microapps-deployer)\n - Lambda service invoked by `microapps-publish` to record new app/version in the DynamoDB table, create API Gateway integrations, copy S3 assets from staging to prod bucket, etc.\n - Returns a temporary S3 token with restricted access to the staging S3 bucket for upload of the static files for one app/semver\n- [packages/microapps-publish](https://github.com/pwrdrvr/microapps-core/tree/main/packages/microapps-publish)\n - Installed from `npm`:\n - `npm i -g @pwrdrvr/microapps-publish`\n - Node executable that updates versions in config files, deploys static assets to the S3 staging bucket, optionally compiles and deploys a new Lambda function version, and invokes `microapps-deployer`\n - AWS IAM permissions required:\n - `lambda:InvokeFunction`\n- [packages/microapps-router](https://github.com/pwrdrvr/microapps-core/tree/main/packages/microapps-router)\n - Lambda function that determines which version of an app to point a user to on a particular invocation\n\n# Creating a MicroApp Using Zip Lambda Functions\n\n[TBC]\n\n# Creating a MicroApp Using Docker Lambda Functions\n\nNote: semi-deprecated as of 2022-01-27. Zip Lambda functions are better supported.\n\n## Next.js Apps\n\nCreate a Next.js app then follow the steps in this section to set it up for publishing to AWS Lambda @ Origin as a MicroApp. To publish new versions of the app use `npx microapps-publish --new-version x.y.z` when logged in to the target AWS account.\n\n### Modify package.json\n\nReplace the version with `0.0.0` so it can be modified by the `microapps-publish` tool.\n\n### Install Dependencies\n\n```\nnpm i --save-dev @pwrdrvr/microapps-publish\n```\n\n### Dockerfile\n\nFIXME: Out of date 2023-03-04\n\nAdd this file to the root of the app.\n\n```Dockerfile\nFROM node:15-slim as base\n\nWORKDIR /app\n\n# Download the sharp libs once to save time\n# Do this before copying anything else in\nRUN mkdir -p image-lambda-npms && \\\n cd image-lambda-npms && npm i sharp && \\\n rm -rf node_modules/sharp/vendor/*/include/\n\n# Copy in the build output from `npx serverless`\nCOPY .serverless_nextjs .\nCOPY config.json .\n\n# Move the sharp libs into place\nRUN rm -rf image-lambda/node_modules/ && \\\n mv image-lambda-npms/node_modules image-labmda/ && \\\n rm -rf image-lambda-npms\n\nFROM public.ecr.aws/lambda/nodejs:14 AS final\n\n# Copy in the munged code\nCOPY --from=base /app .\n\nCMD [ \"./index.handler\" ]\n```\n\n### next.config.js\n\nFIXME: Out of date 2023-03-04\n\nAdd this file to the root of the app.\n\nReplace `appname` with your URL path-compatible application name.\n\n```js\nconst appRoot = '/appname/0.0.0';\n\n// eslint-disable-next-line no-undef\nmodule.exports = {\n target: 'serverless',\n webpack: (config, _options) => {\n return config;\n },\n basePath: appRoot,\n publicRuntimeConfig: {\n // Will be available on both server and client\n staticFolder: appRoot,\n },\n};\n```\n\n# Troubleshooting\n\n## CloudFront Requests to API Gateway are Rejected with 403 Forbidden\n\nRequests to the API Gateway origin can be rejected with a 403 Forbidden error if the signed request headers are not sent to the origin by CloudFront.\n\nThe error in the API Gateway CloudWatch logs will show up as:\n\n```log\n\"authorizerError\": \"The request for the IAM Authorizer doesn't match the format that API Gateway expects.\"\n```\n\nThis can be simulated by simply running `curl [api-gateway-url]`, with no headers.\n\nTo confirm that API Gateway is allowing signed requests when the IAM Authorizer is configured, establish credentials as a user that is allowed to execute the API Gateay, install `awscurl` with `pip3 install awscurl`, then then use `awscurl --service execute-api --region [api-gateway-region] [api-gateway-url]`.\n\nSignature headers will not be sent from CloudFront to API Gateway unless the `OriginRequestPolicy` is set to specifically include those headers on requests to the origin, or the `headersBehavior` is set to `cfront.OriginRequestHeaderBehavior.all()`.\n\nSimilarly, if `presign` is used, the `OriginRequestPolicy` must be set to `cfront.OriginRequestQueryStringBehavior.all()` or to specifically forward the query string parameters used by the presigned URL.\n\n### SignatureV4 Headers\n- `authorization`\n- `x-amz-date`\n- `x-amz-security-token`\n- `x-amz-content-sha256`\n"
|
|
3103
|
+
"markdown": "[](https://github.com/pwrdrvr/microapps-core/actions/workflows/ci.yml) [](https://github.com/pwrdrvr/microapps-core/actions/workflows/main-build.yml) [](https://github.com/pwrdrvr/microapps-core/actions/workflows/release.yml)\n\n# Overview\n\nThe MicroApps project enables rapidly deploying many web apps to AWS on a single shared host name, fronted by a CloudFront Distribution, serving static assets from an S3 Bucket, and routing application requests via API Gateway. MicroApps is delivered as a CDK Construct for deployment, although alternative deployment methods can be used if desired and implemented.\n\nMicroApps allows many versions of an application to be deployed either as ephemeral deploys (e.g. for pull request builds) or as semi-permanent deploys. The `microapps-router` Lambda function handled routing requests to apps to the current version targeted for a particular application start request using rules as complex as one is interested in implementing (e.g. A/B testing integration, canary releases, per-user rules for logged in users, per-group, per-deparment, and default rules).\n\nUsers start applications via a URL such as `[/{prefix}]/{appname}/`, which hits the `microapps-router` Lambda@Edge OriginRequest handler that looks up the version of the application to be run, and either forwards the request to the target Lambda Function URL (`--startupType direct` invoke mode) or returns a transparent `iframe` (`--startupType iframe`) with a link to that version. `direct` mode works with frameworks, like Next.js, that can return pages that have build-time computed relative URLs to static resources and API calls. `iframe` mode works with frameworks that do not write computed relative URLs at build time and/or that do not use URLs that are completely relative to wherever the applications is rooted at runtime; this mode is primarily for quick prototyping as it has other complications (such as indirect access to query strings). The URL seen by the user in the browser (and available for bookmarking) has no version in it, so subsequent launches (e.g. the next day or just in another tab) will lookup the version again. All relative URL API requests (e.g. `some/api/path`) will go to the corresponding API version that matches the version of the loaded static files, eliminating issues of incompatibility between static files and API deployments.\n\nFor development / testing purposes only, each version of an applicaton can be accessed directly via a URL of the patterns `[/{prefix}]/{appname}?appver={semver}` for `direct` mode or `[/{prefix}]/{appname}/{semver}/` for `iframe` mode. These \"versioned\" URLs are not intended to be advertised to end users as they would cause a user to be stuck on a particular version of the app if the URL was bookmarked. Note that the system does not limit access to particular versions of an application, as of 2023-03-04, but that can be added as a feature.\n\n# Table of Contents <!-- omit in toc -->\n\n- [Overview](#overview)\n- [Why MicroApps](#why-microapps)\n- [Request Routing for Static Assets / App - Diagram](#request-routing-for-static-assets--app---diagram)\n- [Request Dispatch Model for Multi-Account Deployments](#request-dispatch-model-for-multi-account-deployments)\n- [Video Preview of the Deploying CDK Construct](#video-preview-of-the-deploying-cdk-construct)\n- [Installation / CDK Constructs](#installation--cdk-constructs)\n- [Tutorial - Bootstrapping a Deploy](#tutorial---bootstrapping-a-deploy)\n- [Limitations / Future Development](#limitations--future-development)\n- [Related Projects / Components](#related-projects--components)\n- [Why Lambda @ Origin and Not Lambda @ Edge for Apps](#why-lambda--origin-and-not-lambda--edge-for-apps)\n- [Architecure Diagram](#architecure-diagram)\n- [Project Layout](#project-layout)\n- [Creating a MicroApp Using Zip Lambda Functions](#creating-a-microapp-using-zip-lambda-functions)\n- [Creating a MicroApp Using Docker Lambda Functions](#creating-a-microapp-using-docker-lambda-functions)\n - [Next.js Apps](#nextjs-apps)\n - [Modify package.json](#modify-packagejson)\n - [Install Dependencies](#install-dependencies)\n - [Dockerfile](#dockerfile)\n - [next.config.js](#nextconfigjs)\n- [Troubleshooting](#troubleshooting)\n - [CloudFront Requests to API Gateway are Rejected with 403 Forbidden](#cloudfront-requests-to-api-gateway-are-rejected-with-403-forbidden)\n - [SignatureV4 Headers](#signaturev4-headers)\n\n# Why MicroApps\n\nMicroApps are like micro services, but for Web UIs. A MicroApp allows a single functional site to be developed by many independent teams within an organization. Teams must coordinate deployments and agree upon one implementation technology and framework when building a monolithic, or even a monorepo, web application.\n\nTeams using MicroApps can deploy independently of each other with coordination being required only at points of intentional integration (e.g. adding a feature to pass context from one MicroApp to another or coordination of a major feature release to users) and sharing UI styles, if desired (it is possible to build styles that look the same across many different UI frameworks).\n\nMicroApps also allow each team to use a UI framework and backend language that is most appropriate for their solving their business problem. Not every app has to use React or Next.js or even Node on the backend, but instead they can use whatever framework they want and Java, Go, C#, Python, etc. for UI API calls.\n\nFor internal sites, or logged-in-customer sites, different tools or products can be hosted in entirely independent MicroApps. A menuing system / toolbar application can be created as a MicroApp and that menu app can open the apps in the system within a transparent iframe. For externally facing sites, such as for an e-commerce site, it is possible to have a MicroApp serving `/product/...`, another serving `/search/...`, another serving `/`, etc.\n\n# Request Routing for Static Assets / App - Diagram\n\n\n\n# Request Dispatch Model for Multi-Account Deployments\n\nNote: requests can also be dispatched into the same account, but this model is more likely to be used by organizations with many AWS accounts.\n\n\n\n# Video Preview of the Deploying CDK Construct\n\n\n\n# Installation / CDK Constructs\n\n- `npm i --save-dev @pwrdrvr/microapps-cdk`\n- Add `MicroApps` construct to your stack\n- The `MicroApps` construct does a \"turn-key\" deployment complete with the Release app\n- [Construct Hub](https://constructs.dev/packages/@pwrdrvr/microapps-cdk/)\n - CDK API docs\n - Python, DotNet, Java, JS/TS installation instructions\n\n# Tutorial - Bootstrapping a Deploy\n\n- `git clone https://github.com/pwrdrvr/microapps-core.git`\n - Note: the repo is only being for the example CDK Stack, it is not necessary to clone the repo when used in a custom CDK Stack\n- `cd microapps-core`\n- `npm i -g aws-cdk`\n - Install AWS CDK v2 CLI\n- `asp [my-sso-profile-name]`\n - Using the `aws` plugin from `oh-my-zsh` for AWS SSO\n - Of course, there are other methods of setting env vars\n- `aws sso login`\n - Establish an AWS SSO session\n- `export AWS_REGION=us-east-2`\n - Region needs to be set for the Lambda invoke - This can be done other ways in `~/.aws/config` as well\n- `./deploy.sh`\n - Deploys the CDK Stack\n - Essentially runs two commands along with extraction of outputs:\n - `npx cdk deploy --context @pwrdrvr/microapps:deployReleaseApp=true microapps-basic`\n - `npx pwrdrvr publish --app-name release --new-version ${RELEASE_APP_PACKAGE_VERSION} --deployer-lambda-name ${DEPLOYER_LAMBDA_NAME} --app-lambda-name ${RELEASE_APP_LAMBDA_NAME} --static-assets-path node_modules/@pwrdrvr/microapps-app-release-cdk/lib/static_files/release/${RELEASE_APP_PACKAGE_VERSION}/ --overwrite --no-cache`\n - URL will be printed as last output\n\n# Limitations / Future Development\n\n- AWS Only\n - For the time being this has only been implemented for AWS technologies and APIs\n - It is possible that Azure and GCP have sufficient support to enable porting the framework\n - CDK would have to be replaced as well (unless it's made available for Azure and GCP in the near future)\n- Release Rules\n - Currently only a Default rule is supported\n - Need to evaluate if a generic implementation can be made, possibly allowing plugins or webhooks to support arbitrary rules\n - If not possible to make it perfectly generic, consider providing a more complete reference implementation of examples\n\n# Related Projects / Components\n\n- Release App\n - The Release app is an initial, rudimentary, release control console for setting the default version of an application\n - Built with Next.js\n - [pwrdrvr/microapps-app-release](https://github.com/pwrdrvr/microapps-app-release)\n- Next.js Demo App\n - The Next.js Tutorial application deployed as a MicroApp\n - [pwrdrvr/serverless-nextjs-demo](https://github.com/pwrdrvr/serverless-nextjs-demo)\n\n\n# Why Lambda @ Origin and Not Lambda @ Edge for Apps\n\nCalling resources (DBs and other services) and waiting for a long synchronous response is an anti-pattern in Lambda as the Lambda function will be billed for the time spent waiting for the response. This is especially true for Lambda@Edge as the cost is 3x higher than Lambda at the origin.\n\nWith Lambda@Edge (even with Origin Requests) the cost is 3x higher per GB-second and the time spent waiting for a 1 ms service response from an origin that is 250 ms away is 750x higher (250 ms / 1ms * 3x higher cost) than making that same request within the region where the resource resides.\n\n- Lambda@Edge is _at least_ 3x more expensive than Lambda at the origin:\n - In US East 1, the price per GB-Second is $0.00005001 for Lambda@Edge\n - Source: https://aws.amazon.com/lambda/pricing/ (bottom of page)\n - Updated: 2023-03-04\n - In US East 1, the price per GB-Second is $0.0000166667 for Lambda at the origin on x86\n - Source: https://aws.amazon.com/lambda/pricing/\n - Updated: 2023-03-04\n - Ratio\n - Lambda@Edge / Lambda@Origin = $0.00005001 / $0.0000166667 = 3.0006x\n- Any DB or services calls from Lambda@Edge back to the origin will pay that 3x higher per GB-Second cost for any time spent waiting to send the request and get a response. Example:\n - Lambda@Edge\n - 0.250s Round Trip Time (RTT) for EU-zone edge request to hit US-East 1 Origin\n - 0.200s DB lookup time\n - 0.050s CPU usage to process the DB response\n - 0.500s total billed time @ $0.00005001 @ 128 MB\n - $0.000003125625 total charge\n - Lambda at Origin\n - RTT does not apply (it's effectively 1-2 ms to hit a DB in the same region)\n - 0.200s DB lookup time\n - 0.050s CPU usage to process the DB response\n - 0.250s total billed time @ $0.0000166667 @ 128 MB\n - Half the billed time of running on Lambda@Edge\n - 1/6th the cost of running on Lambda@Edge:\n - $0.000000520834375 total charge (assuming no CPU time to process the response)\n - $0.000003125625 / $0.000000520834375 = 6x more expensive in Lambda@Edge\n\n# Architecure Diagram\n\n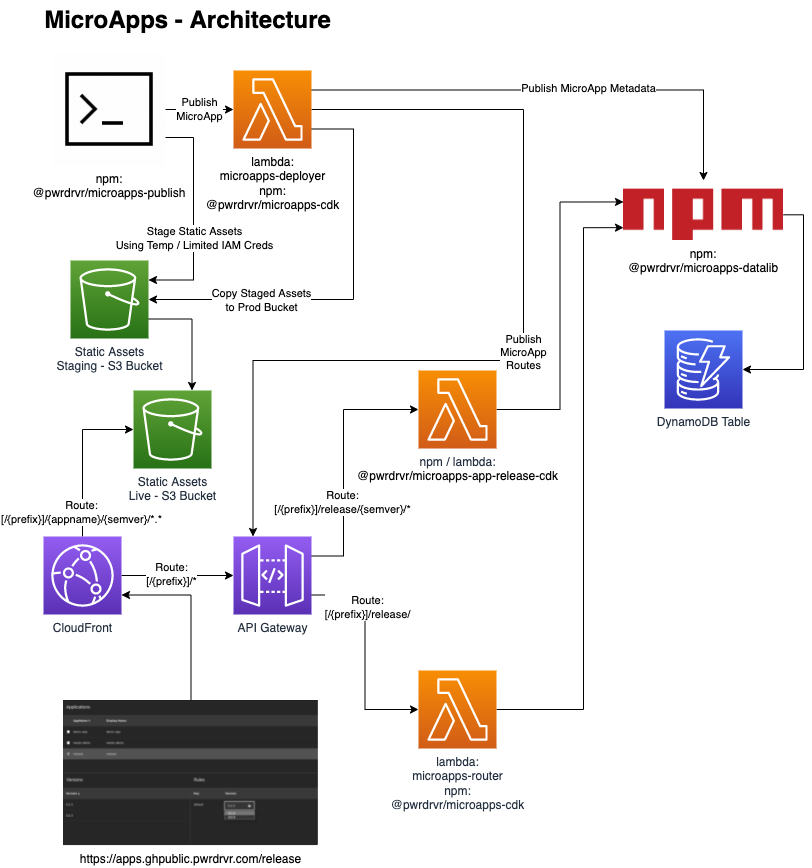\n\n# Project Layout\n\n- [packages/cdk](https://github.com/pwrdrvr/microapps-core/tree/main/packages/cdk)\n - Example CDK Stack\n - Deploys MicroApps CDK stack for the GitHub Workflows\n - Can be used as an example of how to use the MicroApps CDK Construct\n- [packages/demo-app](https://github.com/pwrdrvr/microapps-core/tree/main/packages/demo-app)\n - Example app with static resources and a Lambda function\n - Does not use any Web UI framework at all\n- [packages/microapps-cdk](https://github.com/pwrdrvr/microapps-core/tree/main/packages/microapps-cdk)\n - MicroApps\n - \"Turn key\" CDK Construct that creates all assets needed for a working MicroApps deployment\n - MicroAppsAPIGwy\n - Create APIGateway HTTP API\n - Creates domain names to point to the edge (Cloudfront) and origin (API Gateway)\n - MicroAppsCF\n - Creates Cloudfront distribution\n - MicroAppsS3\n - Creates S3 buckets\n - MicroAppsSvcs\n - Create DynamoDB table\n - Create Deployer Lambda function\n - Create Router Lambda function\n- [packages/microapps-datalib](https://github.com/pwrdrvr/microapps-core/tree/main/packages/microapps-datalib)\n - Installed from `npm`:\n - `npm i -g @pwrdrvr/microapps-datalib`\n - APIs for access to the DynamoDB Table used by the `pwrdrvr` CLI, `microapps-deployer`, and `@pwrdrvr/microapps-app-release-cdk`\n- [packages/microapps-deployer](https://github.com/pwrdrvr/microapps-core/tree/main/packages/microapps-deployer)\n - Lambda service invoked by the `pwrdrvr` CLI to record new app/version in the DynamoDB table, create API Gateway integrations, copy S3 assets from staging to prod bucket, etc.\n - Returns a temporary S3 token with restricted access to the staging S3 bucket for upload of the static files for one app/semver\n- [packages/pwrdrvr](https://github.com/pwrdrvr/microapps-core/tree/main/packages/pwrdrvr)\n - Installed from `npm`:\n - `npm i -g pwrdrvr`\n - Node executable that updates versions in config files, deploys static assets to the S3 staging bucket, optionally compiles and deploys a new Lambda function version, and invokes `microapps-deployer`\n - AWS IAM permissions required:\n - `lambda:InvokeFunction`\n- [packages/microapps-router](https://github.com/pwrdrvr/microapps-core/tree/main/packages/microapps-router)\n - Lambda function that determines which version of an app to point a user to on a particular invocation\n\n# Creating a MicroApp Using Zip Lambda Functions\n\n[TBC]\n\n# Creating a MicroApp Using Docker Lambda Functions\n\nDocker Lambdas are great for large applications. These used to be slower to cold start but as of early 2023 that appears to no longer be an issue.\n\n## Next.js Apps\n\nCreate a Next.js app then follow the steps in this section to set it up for publishing to AWS Lambda @ Origin as a MicroApp. To publish new versions of the app use `npx pwrdrvr --new-version x.y.z` when logged in to the target AWS account.\n\n### Modify package.json\n\nReplace the version with `0.0.0` so it can be modified by the `pwrdrvr` CLI.\n\n### Install Dependencies\n\n```\nnpm i --save-dev pwrdrvr\n```\n\n### Dockerfile\n\nFIXME: Out of date 2023-03-04\n\nAdd this file to the root of the app.\n\n```Dockerfile\nFROM node:15-slim as base\n\nWORKDIR /app\n\n# Download the sharp libs once to save time\n# Do this before copying anything else in\nRUN mkdir -p image-lambda-npms && \\\n cd image-lambda-npms && npm i sharp && \\\n rm -rf node_modules/sharp/vendor/*/include/\n\n# Copy in the build output from `npx serverless`\nCOPY .serverless_nextjs .\nCOPY config.json .\n\n# Move the sharp libs into place\nRUN rm -rf image-lambda/node_modules/ && \\\n mv image-lambda-npms/node_modules image-labmda/ && \\\n rm -rf image-lambda-npms\n\nFROM public.ecr.aws/lambda/nodejs:14 AS final\n\n# Copy in the munged code\nCOPY --from=base /app .\n\nCMD [ \"./index.handler\" ]\n```\n\n### next.config.js\n\nFIXME: Out of date 2023-03-04\n\nAdd this file to the root of the app.\n\nReplace `appname` with your URL path-compatible application name.\n\n```js\nconst appRoot = '/appname/0.0.0';\n\n// eslint-disable-next-line no-undef\nmodule.exports = {\n target: 'serverless',\n webpack: (config, _options) => {\n return config;\n },\n basePath: appRoot,\n publicRuntimeConfig: {\n // Will be available on both server and client\n staticFolder: appRoot,\n },\n};\n```\n\n# Troubleshooting\n\n## CloudFront Requests to API Gateway are Rejected with 403 Forbidden\n\nRequests to the API Gateway origin can be rejected with a 403 Forbidden error if the signed request headers are not sent to the origin by CloudFront.\n\nThe error in the API Gateway CloudWatch logs will show up as:\n\n```log\n\"authorizerError\": \"The request for the IAM Authorizer doesn't match the format that API Gateway expects.\"\n```\n\nThis can be simulated by simply running `curl [api-gateway-url]`, with no headers.\n\nTo confirm that API Gateway is allowing signed requests when the IAM Authorizer is configured, establish credentials as a user that is allowed to execute the API Gateay, install `awscurl` with `pip3 install awscurl`, then then use `awscurl --service execute-api --region [api-gateway-region] [api-gateway-url]`.\n\nSignature headers will not be sent from CloudFront to API Gateway unless the `OriginRequestPolicy` is set to specifically include those headers on requests to the origin, or the `headersBehavior` is set to `cfront.OriginRequestHeaderBehavior.all()`.\n\nSimilarly, if `presign` is used, the `OriginRequestPolicy` must be set to `cfront.OriginRequestQueryStringBehavior.all()` or to specifically forward the query string parameters used by the presigned URL.\n\n### SignatureV4 Headers\n- `authorization`\n- `x-amz-date`\n- `x-amz-security-token`\n- `x-amz-content-sha256`\n"
|
|
3104
3104
|
},
|
|
3105
3105
|
"repository": {
|
|
3106
3106
|
"type": "git",
|
|
@@ -3464,7 +3464,7 @@
|
|
|
3464
3464
|
"kind": "interface",
|
|
3465
3465
|
"locationInModule": {
|
|
3466
3466
|
"filename": "src/MicroApps.ts",
|
|
3467
|
-
"line":
|
|
3467
|
+
"line": 323
|
|
3468
3468
|
},
|
|
3469
3469
|
"name": "IMicroApps",
|
|
3470
3470
|
"properties": [
|
|
@@ -3477,7 +3477,7 @@
|
|
|
3477
3477
|
"immutable": true,
|
|
3478
3478
|
"locationInModule": {
|
|
3479
3479
|
"filename": "src/MicroApps.ts",
|
|
3480
|
-
"line":
|
|
3480
|
+
"line": 325
|
|
3481
3481
|
},
|
|
3482
3482
|
"name": "cf",
|
|
3483
3483
|
"type": {
|
|
@@ -3493,7 +3493,7 @@
|
|
|
3493
3493
|
"immutable": true,
|
|
3494
3494
|
"locationInModule": {
|
|
3495
3495
|
"filename": "src/MicroApps.ts",
|
|
3496
|
-
"line":
|
|
3496
|
+
"line": 331
|
|
3497
3497
|
},
|
|
3498
3498
|
"name": "s3",
|
|
3499
3499
|
"type": {
|
|
@@ -3509,7 +3509,7 @@
|
|
|
3509
3509
|
"immutable": true,
|
|
3510
3510
|
"locationInModule": {
|
|
3511
3511
|
"filename": "src/MicroApps.ts",
|
|
3512
|
-
"line":
|
|
3512
|
+
"line": 334
|
|
3513
3513
|
},
|
|
3514
3514
|
"name": "svcs",
|
|
3515
3515
|
"type": {
|
|
@@ -3525,7 +3525,7 @@
|
|
|
3525
3525
|
"immutable": true,
|
|
3526
3526
|
"locationInModule": {
|
|
3527
3527
|
"filename": "src/MicroApps.ts",
|
|
3528
|
-
"line":
|
|
3528
|
+
"line": 337
|
|
3529
3529
|
},
|
|
3530
3530
|
"name": "apigwy",
|
|
3531
3531
|
"optional": true,
|
|
@@ -3542,7 +3542,7 @@
|
|
|
3542
3542
|
"immutable": true,
|
|
3543
3543
|
"locationInModule": {
|
|
3544
3544
|
"filename": "src/MicroApps.ts",
|
|
3545
|
-
"line":
|
|
3545
|
+
"line": 328
|
|
3546
3546
|
},
|
|
3547
3547
|
"name": "edgeToOrigin",
|
|
3548
3548
|
"optional": true,
|
|
@@ -3646,7 +3646,7 @@
|
|
|
3646
3646
|
"kind": "interface",
|
|
3647
3647
|
"locationInModule": {
|
|
3648
3648
|
"filename": "src/MicroAppsChildDeployer.ts",
|
|
3649
|
-
"line":
|
|
3649
|
+
"line": 70
|
|
3650
3650
|
},
|
|
3651
3651
|
"name": "IMicroAppsChildDeployer",
|
|
3652
3652
|
"properties": [
|
|
@@ -3659,7 +3659,7 @@
|
|
|
3659
3659
|
"immutable": true,
|
|
3660
3660
|
"locationInModule": {
|
|
3661
3661
|
"filename": "src/MicroAppsChildDeployer.ts",
|
|
3662
|
-
"line":
|
|
3662
|
+
"line": 74
|
|
3663
3663
|
},
|
|
3664
3664
|
"name": "deployerFunc",
|
|
3665
3665
|
"type": {
|
|
@@ -3872,7 +3872,7 @@
|
|
|
3872
3872
|
"kind": "interface",
|
|
3873
3873
|
"locationInModule": {
|
|
3874
3874
|
"filename": "src/MicroAppsSvcs.ts",
|
|
3875
|
-
"line":
|
|
3875
|
+
"line": 191
|
|
3876
3876
|
},
|
|
3877
3877
|
"name": "IMicroAppsSvcs",
|
|
3878
3878
|
"properties": [
|
|
@@ -3885,7 +3885,7 @@
|
|
|
3885
3885
|
"immutable": true,
|
|
3886
3886
|
"locationInModule": {
|
|
3887
3887
|
"filename": "src/MicroAppsSvcs.ts",
|
|
3888
|
-
"line":
|
|
3888
|
+
"line": 200
|
|
3889
3889
|
},
|
|
3890
3890
|
"name": "deployerFunc",
|
|
3891
3891
|
"type": {
|
|
@@ -3901,7 +3901,7 @@
|
|
|
3901
3901
|
"immutable": true,
|
|
3902
3902
|
"locationInModule": {
|
|
3903
3903
|
"filename": "src/MicroAppsSvcs.ts",
|
|
3904
|
-
"line":
|
|
3904
|
+
"line": 195
|
|
3905
3905
|
},
|
|
3906
3906
|
"name": "table",
|
|
3907
3907
|
"type": {
|
|
@@ -3917,7 +3917,7 @@
|
|
|
3917
3917
|
"immutable": true,
|
|
3918
3918
|
"locationInModule": {
|
|
3919
3919
|
"filename": "src/MicroAppsSvcs.ts",
|
|
3920
|
-
"line":
|
|
3920
|
+
"line": 205
|
|
3921
3921
|
},
|
|
3922
3922
|
"name": "routerFunc",
|
|
3923
3923
|
"optional": true,
|
|
@@ -3980,7 +3980,7 @@
|
|
|
3980
3980
|
},
|
|
3981
3981
|
"locationInModule": {
|
|
3982
3982
|
"filename": "src/MicroApps.ts",
|
|
3983
|
-
"line":
|
|
3983
|
+
"line": 386
|
|
3984
3984
|
},
|
|
3985
3985
|
"parameters": [
|
|
3986
3986
|
{
|
|
@@ -4010,7 +4010,7 @@
|
|
|
4010
4010
|
"kind": "class",
|
|
4011
4011
|
"locationInModule": {
|
|
4012
4012
|
"filename": "src/MicroApps.ts",
|
|
4013
|
-
"line":
|
|
4013
|
+
"line": 360
|
|
4014
4014
|
},
|
|
4015
4015
|
"name": "MicroApps",
|
|
4016
4016
|
"properties": [
|
|
@@ -4022,7 +4022,7 @@
|
|
|
4022
4022
|
"immutable": true,
|
|
4023
4023
|
"locationInModule": {
|
|
4024
4024
|
"filename": "src/MicroApps.ts",
|
|
4025
|
-
"line":
|
|
4025
|
+
"line": 362
|
|
4026
4026
|
},
|
|
4027
4027
|
"name": "cf",
|
|
4028
4028
|
"overrides": "@pwrdrvr/microapps-cdk.IMicroApps",
|
|
@@ -4038,7 +4038,7 @@
|
|
|
4038
4038
|
"immutable": true,
|
|
4039
4039
|
"locationInModule": {
|
|
4040
4040
|
"filename": "src/MicroApps.ts",
|
|
4041
|
-
"line":
|
|
4041
|
+
"line": 372
|
|
4042
4042
|
},
|
|
4043
4043
|
"name": "s3",
|
|
4044
4044
|
"overrides": "@pwrdrvr/microapps-cdk.IMicroApps",
|
|
@@ -4054,7 +4054,7 @@
|
|
|
4054
4054
|
"immutable": true,
|
|
4055
4055
|
"locationInModule": {
|
|
4056
4056
|
"filename": "src/MicroApps.ts",
|
|
4057
|
-
"line":
|
|
4057
|
+
"line": 382
|
|
4058
4058
|
},
|
|
4059
4059
|
"name": "svcs",
|
|
4060
4060
|
"overrides": "@pwrdrvr/microapps-cdk.IMicroApps",
|
|
@@ -4070,7 +4070,7 @@
|
|
|
4070
4070
|
"immutable": true,
|
|
4071
4071
|
"locationInModule": {
|
|
4072
4072
|
"filename": "src/MicroApps.ts",
|
|
4073
|
-
"line":
|
|
4073
|
+
"line": 377
|
|
4074
4074
|
},
|
|
4075
4075
|
"name": "apigwy",
|
|
4076
4076
|
"optional": true,
|
|
@@ -4087,7 +4087,7 @@
|
|
|
4087
4087
|
"immutable": true,
|
|
4088
4088
|
"locationInModule": {
|
|
4089
4089
|
"filename": "src/MicroApps.ts",
|
|
4090
|
-
"line":
|
|
4090
|
+
"line": 367
|
|
4091
4091
|
},
|
|
4092
4092
|
"name": "edgeToOrigin",
|
|
4093
4093
|
"optional": true,
|
|
@@ -4818,7 +4818,7 @@
|
|
|
4818
4818
|
},
|
|
4819
4819
|
"locationInModule": {
|
|
4820
4820
|
"filename": "src/MicroAppsChildDeployer.ts",
|
|
4821
|
-
"line":
|
|
4821
|
+
"line": 86
|
|
4822
4822
|
},
|
|
4823
4823
|
"parameters": [
|
|
4824
4824
|
{
|
|
@@ -4848,7 +4848,7 @@
|
|
|
4848
4848
|
"kind": "class",
|
|
4849
4849
|
"locationInModule": {
|
|
4850
4850
|
"filename": "src/MicroAppsChildDeployer.ts",
|
|
4851
|
-
"line":
|
|
4851
|
+
"line": 80
|
|
4852
4852
|
},
|
|
4853
4853
|
"name": "MicroAppsChildDeployer",
|
|
4854
4854
|
"properties": [
|
|
@@ -4860,7 +4860,7 @@
|
|
|
4860
4860
|
"immutable": true,
|
|
4861
4861
|
"locationInModule": {
|
|
4862
4862
|
"filename": "src/MicroAppsChildDeployer.ts",
|
|
4863
|
-
"line":
|
|
4863
|
+
"line": 82
|
|
4864
4864
|
},
|
|
4865
4865
|
"name": "deployerFunc",
|
|
4866
4866
|
"overrides": "@pwrdrvr/microapps-cdk.IMicroAppsChildDeployer",
|
|
@@ -4895,29 +4895,13 @@
|
|
|
4895
4895
|
"immutable": true,
|
|
4896
4896
|
"locationInModule": {
|
|
4897
4897
|
"filename": "src/MicroAppsChildDeployer.ts",
|
|
4898
|
-
"line":
|
|
4898
|
+
"line": 39
|
|
4899
4899
|
},
|
|
4900
4900
|
"name": "appEnv",
|
|
4901
4901
|
"type": {
|
|
4902
4902
|
"primitive": "string"
|
|
4903
4903
|
}
|
|
4904
4904
|
},
|
|
4905
|
-
{
|
|
4906
|
-
"abstract": true,
|
|
4907
|
-
"docs": {
|
|
4908
|
-
"stability": "experimental",
|
|
4909
|
-
"summary": "ARN of the IAM Role for the Edge to Origin Lambda Function."
|
|
4910
|
-
},
|
|
4911
|
-
"immutable": true,
|
|
4912
|
-
"locationInModule": {
|
|
4913
|
-
"filename": "src/MicroAppsChildDeployer.ts",
|
|
4914
|
-
"line": 22
|
|
4915
|
-
},
|
|
4916
|
-
"name": "edgeToOriginRoleARN",
|
|
4917
|
-
"type": {
|
|
4918
|
-
"primitive": "string"
|
|
4919
|
-
}
|
|
4920
|
-
},
|
|
4921
4905
|
{
|
|
4922
4906
|
"abstract": true,
|
|
4923
4907
|
"docs": {
|
|
@@ -4945,7 +4929,7 @@
|
|
|
4945
4929
|
"immutable": true,
|
|
4946
4930
|
"locationInModule": {
|
|
4947
4931
|
"filename": "src/MicroAppsChildDeployer.ts",
|
|
4948
|
-
"line":
|
|
4932
|
+
"line": 47
|
|
4949
4933
|
},
|
|
4950
4934
|
"name": "assetNameRoot",
|
|
4951
4935
|
"optional": true,
|
|
@@ -4964,7 +4948,7 @@
|
|
|
4964
4948
|
"immutable": true,
|
|
4965
4949
|
"locationInModule": {
|
|
4966
4950
|
"filename": "src/MicroAppsChildDeployer.ts",
|
|
4967
|
-
"line":
|
|
4951
|
+
"line": 55
|
|
4968
4952
|
},
|
|
4969
4953
|
"name": "assetNameSuffix",
|
|
4970
4954
|
"optional": true,
|
|
@@ -4983,7 +4967,7 @@
|
|
|
4983
4967
|
"immutable": true,
|
|
4984
4968
|
"locationInModule": {
|
|
4985
4969
|
"filename": "src/MicroAppsChildDeployer.ts",
|
|
4986
|
-
"line":
|
|
4970
|
+
"line": 64
|
|
4987
4971
|
},
|
|
4988
4972
|
"name": "deployerTimeout",
|
|
4989
4973
|
"optional": true,
|
|
@@ -4991,6 +4975,24 @@
|
|
|
4991
4975
|
"fqn": "aws-cdk-lib.Duration"
|
|
4992
4976
|
}
|
|
4993
4977
|
},
|
|
4978
|
+
{
|
|
4979
|
+
"abstract": true,
|
|
4980
|
+
"docs": {
|
|
4981
|
+
"remarks": "For child accounts this can be blank as it is retrieved from the parent Deployer",
|
|
4982
|
+
"stability": "experimental",
|
|
4983
|
+
"summary": "ARN of the IAM Role for the Edge to Origin Lambda Function."
|
|
4984
|
+
},
|
|
4985
|
+
"immutable": true,
|
|
4986
|
+
"locationInModule": {
|
|
4987
|
+
"filename": "src/MicroAppsChildDeployer.ts",
|
|
4988
|
+
"line": 24
|
|
4989
|
+
},
|
|
4990
|
+
"name": "edgeToOriginRoleARN",
|
|
4991
|
+
"optional": true,
|
|
4992
|
+
"type": {
|
|
4993
|
+
"primitive": "string"
|
|
4994
|
+
}
|
|
4995
|
+
},
|
|
4994
4996
|
{
|
|
4995
4997
|
"abstract": true,
|
|
4996
4998
|
"docs": {
|
|
@@ -5002,7 +5004,7 @@
|
|
|
5002
5004
|
"immutable": true,
|
|
5003
5005
|
"locationInModule": {
|
|
5004
5006
|
"filename": "src/MicroAppsChildDeployer.ts",
|
|
5005
|
-
"line":
|
|
5007
|
+
"line": 33
|
|
5006
5008
|
},
|
|
5007
5009
|
"name": "removalPolicy",
|
|
5008
5010
|
"optional": true,
|
|
@@ -5692,6 +5694,28 @@
|
|
|
5692
5694
|
}
|
|
5693
5695
|
}
|
|
5694
5696
|
},
|
|
5697
|
+
{
|
|
5698
|
+
"abstract": true,
|
|
5699
|
+
"docs": {
|
|
5700
|
+
"stability": "experimental",
|
|
5701
|
+
"summary": "Additional IAM Role ARNs that should be allowed to invoke apps in child accounts."
|
|
5702
|
+
},
|
|
5703
|
+
"immutable": true,
|
|
5704
|
+
"locationInModule": {
|
|
5705
|
+
"filename": "src/MicroApps.ts",
|
|
5706
|
+
"line": 317
|
|
5707
|
+
},
|
|
5708
|
+
"name": "edgeToOriginRoleARNs",
|
|
5709
|
+
"optional": true,
|
|
5710
|
+
"type": {
|
|
5711
|
+
"collection": {
|
|
5712
|
+
"elementtype": {
|
|
5713
|
+
"primitive": "string"
|
|
5714
|
+
},
|
|
5715
|
+
"kind": "array"
|
|
5716
|
+
}
|
|
5717
|
+
}
|
|
5718
|
+
},
|
|
5695
5719
|
{
|
|
5696
5720
|
"abstract": true,
|
|
5697
5721
|
"docs": {
|
|
@@ -5806,7 +5830,7 @@
|
|
|
5806
5830
|
"abstract": true,
|
|
5807
5831
|
"docs": {
|
|
5808
5832
|
"example": "[ 'AROA1234567890123' ]",
|
|
5809
|
-
"remarks": "AROAs of the IAM Role to exclude from the DENY rules on the S3 Bucket Policy.\nThis allows sessions that assume the IAM Role to be excluded from the\nDENY rules on the S3 Bucket Policy.\n\nTypically any admin roles / users that need to view or manage the S3 Bucket\nwould be added to this list.\n\nRoles / users that are used directly, not assumed, can be added to `s3PolicyBypassRoleNames` instead.\n\nNote: This AROA must be specified to prevent this policy from locking\nout non-root sessions that have assumed the admin role.\n\nThe notPrincipals will only match the role name exactly and will not match\nany session that has assumed the role since notPrincipals does not allow\nwildcard matches and does not do wildcard matches implicitly either.\n\nThe AROA must be used because there are only 3 Principal variables available:\n https://docs.aws.amazon.com/IAM/latest/UserGuide/reference_policies_variables.html#principaltable\n aws:username, aws:userid, aws:PrincipalTag\n\nFor an assumed role, aws:username is blank, aws:userid is:\n [unique id AKA AROA for Role]:[session name]\n\nTable of unique ID prefixes such as AROA:\n https://docs.aws.amazon.com/IAM/latest/UserGuide/reference_identifiers.html#identifiers-prefixes\n\nThe name of the role is simply not available for an assumed role and, if it was,\na complicated comparison would be requierd to prevent exclusion\nof applying the Deny Rule to roles from other accounts.\n\nTo get the AROA with the AWS CLI:\n aws iam get-role --role-name ROLE-NAME\n aws iam get-user
|
|
5833
|
+
"remarks": "AROAs of the IAM Role to exclude from the DENY rules on the S3 Bucket Policy.\nThis allows sessions that assume the IAM Role to be excluded from the\nDENY rules on the S3 Bucket Policy.\n\nTypically any admin roles / users that need to view or manage the S3 Bucket\nwould be added to this list.\n\nRoles / users that are used directly, not assumed, can be added to `s3PolicyBypassRoleNames` instead.\n\nNote: This AROA must be specified to prevent this policy from locking\nout non-root sessions that have assumed the admin role.\n\nThe notPrincipals will only match the role name exactly and will not match\nany session that has assumed the role since notPrincipals does not allow\nwildcard matches and does not do wildcard matches implicitly either.\n\nThe AROA must be used because there are only 3 Principal variables available:\n https://docs.aws.amazon.com/IAM/latest/UserGuide/reference_policies_variables.html#principaltable\n aws:username, aws:userid, aws:PrincipalTag\n\nFor an assumed role, aws:username is blank, aws:userid is:\n [unique id AKA AROA for Role]:[session name]\n\nTable of unique ID prefixes such as AROA:\n https://docs.aws.amazon.com/IAM/latest/UserGuide/reference_identifiers.html#identifiers-prefixes\n\nThe name of the role is simply not available for an assumed role and, if it was,\na complicated comparison would be requierd to prevent exclusion\nof applying the Deny Rule to roles from other accounts.\n\nTo get the AROA with the AWS CLI:\n aws iam get-role --role-name ROLE-NAME\n aws iam get-user --user-name USER-NAME",
|
|
5810
5834
|
"see": "s3StrictBucketPolicy",
|
|
5811
5835
|
"stability": "experimental",
|
|
5812
5836
|
"summary": "Applies when using s3StrictBucketPolicy = true."
|
|
@@ -6242,7 +6266,7 @@
|
|
|
6242
6266
|
},
|
|
6243
6267
|
"locationInModule": {
|
|
6244
6268
|
"filename": "src/MicroAppsSvcs.ts",
|
|
6245
|
-
"line":
|
|
6269
|
+
"line": 229
|
|
6246
6270
|
},
|
|
6247
6271
|
"parameters": [
|
|
6248
6272
|
{
|
|
@@ -6272,7 +6296,7 @@
|
|
|
6272
6296
|
"kind": "class",
|
|
6273
6297
|
"locationInModule": {
|
|
6274
6298
|
"filename": "src/MicroAppsSvcs.ts",
|
|
6275
|
-
"line":
|
|
6299
|
+
"line": 212
|
|
6276
6300
|
},
|
|
6277
6301
|
"name": "MicroAppsSvcs",
|
|
6278
6302
|
"properties": [
|
|
@@ -6284,7 +6308,7 @@
|
|
|
6284
6308
|
"immutable": true,
|
|
6285
6309
|
"locationInModule": {
|
|
6286
6310
|
"filename": "src/MicroAppsSvcs.ts",
|
|
6287
|
-
"line":
|
|
6311
|
+
"line": 220
|
|
6288
6312
|
},
|
|
6289
6313
|
"name": "deployerFunc",
|
|
6290
6314
|
"overrides": "@pwrdrvr/microapps-cdk.IMicroAppsSvcs",
|
|
@@ -6300,7 +6324,7 @@
|
|
|
6300
6324
|
"immutable": true,
|
|
6301
6325
|
"locationInModule": {
|
|
6302
6326
|
"filename": "src/MicroAppsSvcs.ts",
|
|
6303
|
-
"line":
|
|
6327
|
+
"line": 215
|
|
6304
6328
|
},
|
|
6305
6329
|
"name": "table",
|
|
6306
6330
|
"overrides": "@pwrdrvr/microapps-cdk.IMicroAppsSvcs",
|
|
@@ -6316,7 +6340,7 @@
|
|
|
6316
6340
|
"immutable": true,
|
|
6317
6341
|
"locationInModule": {
|
|
6318
6342
|
"filename": "src/MicroAppsSvcs.ts",
|
|
6319
|
-
"line":
|
|
6343
|
+
"line": 225
|
|
6320
6344
|
},
|
|
6321
6345
|
"name": "routerFunc",
|
|
6322
6346
|
"optional": true,
|
|
@@ -6464,6 +6488,28 @@
|
|
|
6464
6488
|
"fqn": "aws-cdk-lib.Duration"
|
|
6465
6489
|
}
|
|
6466
6490
|
},
|
|
6491
|
+
{
|
|
6492
|
+
"abstract": true,
|
|
6493
|
+
"docs": {
|
|
6494
|
+
"stability": "experimental",
|
|
6495
|
+
"summary": "ARN of the IAM Role for the Edge to Origin Lambda Function."
|
|
6496
|
+
},
|
|
6497
|
+
"immutable": true,
|
|
6498
|
+
"locationInModule": {
|
|
6499
|
+
"filename": "src/MicroAppsSvcs.ts",
|
|
6500
|
+
"line": 185
|
|
6501
|
+
},
|
|
6502
|
+
"name": "edgeToOriginRoleARN",
|
|
6503
|
+
"optional": true,
|
|
6504
|
+
"type": {
|
|
6505
|
+
"collection": {
|
|
6506
|
+
"elementtype": {
|
|
6507
|
+
"primitive": "string"
|
|
6508
|
+
},
|
|
6509
|
+
"kind": "array"
|
|
6510
|
+
}
|
|
6511
|
+
}
|
|
6512
|
+
},
|
|
6467
6513
|
{
|
|
6468
6514
|
"abstract": true,
|
|
6469
6515
|
"docs": {
|
|
@@ -6541,7 +6587,7 @@
|
|
|
6541
6587
|
"abstract": true,
|
|
6542
6588
|
"docs": {
|
|
6543
6589
|
"example": "[ 'AROA1234567890123' ]",
|
|
6544
|
-
"remarks": "AROAs of the IAM Role to exclude from the DENY rules on the S3 Bucket Policy.\nThis allows sessions that assume the IAM Role to be excluded from the\nDENY rules on the S3 Bucket Policy.\n\nTypically any admin roles / users that need to view or manage the S3 Bucket\nwould be added to this list.\n\nRoles / users that are used directly, not assumed, can be added to `s3PolicyBypassRoleNames` instead.\n\nNote: This AROA must be specified to prevent this policy from locking\nout non-root sessions that have assumed the admin role.\n\nThe notPrincipals will only match the role name exactly and will not match\nany session that has assumed the role since notPrincipals does not allow\nwildcard matches and does not do wildcard matches implicitly either.\n\nThe AROA must be used because there are only 3 Principal variables available:\n https://docs.aws.amazon.com/IAM/latest/UserGuide/reference_policies_variables.html#principaltable\n aws:username, aws:userid, aws:PrincipalTag\n\nFor an assumed role, aws:username is blank, aws:userid is:\n [unique id AKA AROA for Role]:[session name]\n\nTable of unique ID prefixes such as AROA:\n https://docs.aws.amazon.com/IAM/latest/UserGuide/reference_identifiers.html#identifiers-prefixes\n\nThe name of the role is simply not available for an assumed role and, if it was,\na complicated comparison would be requierd to prevent exclusion\nof applying the Deny Rule to roles from other accounts.\n\nTo get the AROA with the AWS CLI:\n aws iam get-role --role-name ROLE-NAME\n aws iam get-user
|
|
6590
|
+
"remarks": "AROAs of the IAM Role to exclude from the DENY rules on the S3 Bucket Policy.\nThis allows sessions that assume the IAM Role to be excluded from the\nDENY rules on the S3 Bucket Policy.\n\nTypically any admin roles / users that need to view or manage the S3 Bucket\nwould be added to this list.\n\nRoles / users that are used directly, not assumed, can be added to `s3PolicyBypassRoleNames` instead.\n\nNote: This AROA must be specified to prevent this policy from locking\nout non-root sessions that have assumed the admin role.\n\nThe notPrincipals will only match the role name exactly and will not match\nany session that has assumed the role since notPrincipals does not allow\nwildcard matches and does not do wildcard matches implicitly either.\n\nThe AROA must be used because there are only 3 Principal variables available:\n https://docs.aws.amazon.com/IAM/latest/UserGuide/reference_policies_variables.html#principaltable\n aws:username, aws:userid, aws:PrincipalTag\n\nFor an assumed role, aws:username is blank, aws:userid is:\n [unique id AKA AROA for Role]:[session name]\n\nTable of unique ID prefixes such as AROA:\n https://docs.aws.amazon.com/IAM/latest/UserGuide/reference_identifiers.html#identifiers-prefixes\n\nThe name of the role is simply not available for an assumed role and, if it was,\na complicated comparison would be requierd to prevent exclusion\nof applying the Deny Rule to roles from other accounts.\n\nTo get the AROA with the AWS CLI:\n aws iam get-role --role-name ROLE-NAME\n aws iam get-user --user-name USER-NAME",
|
|
6545
6591
|
"see": "s3StrictBucketPolicy",
|
|
6546
6592
|
"stability": "experimental",
|
|
6547
6593
|
"summary": "Applies when using s3StrictBucketPolicy = true."
|
|
@@ -6776,6 +6822,6 @@
|
|
|
6776
6822
|
"symbolId": "src/MicroAppsTable:MicroAppsTableProps"
|
|
6777
6823
|
}
|
|
6778
6824
|
},
|
|
6779
|
-
"version": "0.4.0-alpha.
|
|
6780
|
-
"fingerprint": "
|
|
6825
|
+
"version": "0.4.0-alpha.13",
|
|
6826
|
+
"fingerprint": "DWXHX6oj5UJpamTw9wgiTVLPFcYLq+wz3SkY3Wd7zNI="
|
|
6781
6827
|
}
|
package/API.md
CHANGED
|
@@ -979,14 +979,6 @@ Application environment, passed as `NODE_ENV` to the Router and Deployer Lambda
|
|
|
979
979
|
|
|
980
980
|
---
|
|
981
981
|
|
|
982
|
-
##### `edgeToOriginRoleARN`<sup>Required</sup> <a name="@pwrdrvr/microapps-cdk.MicroAppsChildDeployerProps.edgeToOriginRoleARN"></a>
|
|
983
|
-
|
|
984
|
-
- *Type:* `string`
|
|
985
|
-
|
|
986
|
-
ARN of the IAM Role for the Edge to Origin Lambda Function.
|
|
987
|
-
|
|
988
|
-
---
|
|
989
|
-
|
|
990
982
|
##### `parentDeployerLambdaARN`<sup>Required</sup> <a name="@pwrdrvr/microapps-cdk.MicroAppsChildDeployerProps.parentDeployerLambdaARN"></a>
|
|
991
983
|
|
|
992
984
|
- *Type:* `string`
|
|
@@ -1024,6 +1016,16 @@ For larger applications this needs to be set up to 2-5 minutes for the S3 copy
|
|
|
1024
1016
|
|
|
1025
1017
|
---
|
|
1026
1018
|
|
|
1019
|
+
##### `edgeToOriginRoleARN`<sup>Optional</sup> <a name="@pwrdrvr/microapps-cdk.MicroAppsChildDeployerProps.edgeToOriginRoleARN"></a>
|
|
1020
|
+
|
|
1021
|
+
- *Type:* `string`
|
|
1022
|
+
|
|
1023
|
+
ARN of the IAM Role for the Edge to Origin Lambda Function.
|
|
1024
|
+
|
|
1025
|
+
For child accounts this can be blank as it is retrieved from the parent Deployer
|
|
1026
|
+
|
|
1027
|
+
---
|
|
1028
|
+
|
|
1027
1029
|
##### `removalPolicy`<sup>Optional</sup> <a name="@pwrdrvr/microapps-cdk.MicroAppsChildDeployerProps.removalPolicy"></a>
|
|
1028
1030
|
|
|
1029
1031
|
- *Type:* [`aws-cdk-lib.RemovalPolicy`](#aws-cdk-lib.RemovalPolicy)
|
|
@@ -1330,6 +1332,14 @@ Additional edge lambda functions.
|
|
|
1330
1332
|
|
|
1331
1333
|
---
|
|
1332
1334
|
|
|
1335
|
+
##### `edgeToOriginRoleARNs`<sup>Optional</sup> <a name="@pwrdrvr/microapps-cdk.MicroAppsProps.edgeToOriginRoleARNs"></a>
|
|
1336
|
+
|
|
1337
|
+
- *Type:* `string`[]
|
|
1338
|
+
|
|
1339
|
+
Additional IAM Role ARNs that should be allowed to invoke apps in child accounts.
|
|
1340
|
+
|
|
1341
|
+
---
|
|
1342
|
+
|
|
1333
1343
|
##### `originRegion`<sup>Optional</sup> <a name="@pwrdrvr/microapps-cdk.MicroAppsProps.originRegion"></a>
|
|
1334
1344
|
|
|
1335
1345
|
- *Type:* `string`
|
|
@@ -1432,7 +1442,7 @@ of applying the Deny Rule to roles from other accounts.
|
|
|
1432
1442
|
|
|
1433
1443
|
To get the AROA with the AWS CLI:
|
|
1434
1444
|
aws iam get-role --role-name ROLE-NAME
|
|
1435
|
-
aws iam get-user
|
|
1445
|
+
aws iam get-user --user-name USER-NAME
|
|
1436
1446
|
|
|
1437
1447
|
> s3StrictBucketPolicy
|
|
1438
1448
|
|
|
@@ -1655,6 +1665,14 @@ For larger applications this needs to be set up to 2-5 minutes for the S3 copy
|
|
|
1655
1665
|
|
|
1656
1666
|
---
|
|
1657
1667
|
|
|
1668
|
+
##### `edgeToOriginRoleARN`<sup>Optional</sup> <a name="@pwrdrvr/microapps-cdk.MicroAppsSvcsProps.edgeToOriginRoleARN"></a>
|
|
1669
|
+
|
|
1670
|
+
- *Type:* `string`[]
|
|
1671
|
+
|
|
1672
|
+
ARN of the IAM Role for the Edge to Origin Lambda Function.
|
|
1673
|
+
|
|
1674
|
+
---
|
|
1675
|
+
|
|
1658
1676
|
##### `httpApi`<sup>Optional</sup> <a name="@pwrdrvr/microapps-cdk.MicroAppsSvcsProps.httpApi"></a>
|
|
1659
1677
|
|
|
1660
1678
|
- *Type:* [`@aws-cdk/aws-apigatewayv2-alpha.HttpApi`](#@aws-cdk/aws-apigatewayv2-alpha.HttpApi)
|
|
@@ -1730,7 +1748,7 @@ of applying the Deny Rule to roles from other accounts.
|
|
|
1730
1748
|
|
|
1731
1749
|
To get the AROA with the AWS CLI:
|
|
1732
1750
|
aws iam get-role --role-name ROLE-NAME
|
|
1733
|
-
aws iam get-user
|
|
1751
|
+
aws iam get-user --user-name USER-NAME
|
|
1734
1752
|
|
|
1735
1753
|
> s3StrictBucketPolicy
|
|
1736
1754
|
|
package/README.md
CHANGED
|
@@ -86,7 +86,7 @@ Note: requests can also be dispatched into the same account, but this model is m
|
|
|
86
86
|
- Deploys the CDK Stack
|
|
87
87
|
- Essentially runs two commands along with extraction of outputs:
|
|
88
88
|
- `npx cdk deploy --context @pwrdrvr/microapps:deployReleaseApp=true microapps-basic`
|
|
89
|
-
- `npx
|
|
89
|
+
- `npx pwrdrvr publish --app-name release --new-version ${RELEASE_APP_PACKAGE_VERSION} --deployer-lambda-name ${DEPLOYER_LAMBDA_NAME} --app-lambda-name ${RELEASE_APP_LAMBDA_NAME} --static-assets-path node_modules/@pwrdrvr/microapps-app-release-cdk/lib/static_files/release/${RELEASE_APP_PACKAGE_VERSION}/ --overwrite --no-cache`
|
|
90
90
|
- URL will be printed as last output
|
|
91
91
|
|
|
92
92
|
# Limitations / Future Development
|
|
@@ -95,14 +95,6 @@ Note: requests can also be dispatched into the same account, but this model is m
|
|
|
95
95
|
- For the time being this has only been implemented for AWS technologies and APIs
|
|
96
96
|
- It is possible that Azure and GCP have sufficient support to enable porting the framework
|
|
97
97
|
- CDK would have to be replaced as well (unless it's made available for Azure and GCP in the near future)
|
|
98
|
-
- `microapps-publish` only supports Lambda function apps
|
|
99
|
-
- There is no technical reason for the apps to only run as Lambda functions
|
|
100
|
-
- Web apps could just as easily run on EC2, Kubernetes, EKS, ECS, etc
|
|
101
|
-
- Anything that API Gateway can route to can work for serving a MicroApp
|
|
102
|
-
- The publish tool needs to provide additional options for setting up the API Gateway route to the app
|
|
103
|
-
- Authentication
|
|
104
|
-
- Authentication requires rolling your own API Gateway and CloudFront deployment at the moment
|
|
105
|
-
- The "turn key" CDK Construct should provide options to show an example of how authentication can be integrated
|
|
106
98
|
- Release Rules
|
|
107
99
|
- Currently only a Default rule is supported
|
|
108
100
|
- Need to evaluate if a generic implementation can be made, possibly allowing plugins or webhooks to support arbitrary rules
|
|
@@ -181,13 +173,13 @@ With Lambda@Edge (even with Origin Requests) the cost is 3x higher per GB-second
|
|
|
181
173
|
- [packages/microapps-datalib](https://github.com/pwrdrvr/microapps-core/tree/main/packages/microapps-datalib)
|
|
182
174
|
- Installed from `npm`:
|
|
183
175
|
- `npm i -g @pwrdrvr/microapps-datalib`
|
|
184
|
-
- APIs for access to the DynamoDB Table used by `
|
|
176
|
+
- APIs for access to the DynamoDB Table used by the `pwrdrvr` CLI, `microapps-deployer`, and `@pwrdrvr/microapps-app-release-cdk`
|
|
185
177
|
- [packages/microapps-deployer](https://github.com/pwrdrvr/microapps-core/tree/main/packages/microapps-deployer)
|
|
186
|
-
- Lambda service invoked by `
|
|
178
|
+
- Lambda service invoked by the `pwrdrvr` CLI to record new app/version in the DynamoDB table, create API Gateway integrations, copy S3 assets from staging to prod bucket, etc.
|
|
187
179
|
- Returns a temporary S3 token with restricted access to the staging S3 bucket for upload of the static files for one app/semver
|
|
188
|
-
- [packages/
|
|
180
|
+
- [packages/pwrdrvr](https://github.com/pwrdrvr/microapps-core/tree/main/packages/pwrdrvr)
|
|
189
181
|
- Installed from `npm`:
|
|
190
|
-
- `npm i -g
|
|
182
|
+
- `npm i -g pwrdrvr`
|
|
191
183
|
- Node executable that updates versions in config files, deploys static assets to the S3 staging bucket, optionally compiles and deploys a new Lambda function version, and invokes `microapps-deployer`
|
|
192
184
|
- AWS IAM permissions required:
|
|
193
185
|
- `lambda:InvokeFunction`
|
|
@@ -200,20 +192,20 @@ With Lambda@Edge (even with Origin Requests) the cost is 3x higher per GB-second
|
|
|
200
192
|
|
|
201
193
|
# Creating a MicroApp Using Docker Lambda Functions
|
|
202
194
|
|
|
203
|
-
|
|
195
|
+
Docker Lambdas are great for large applications. These used to be slower to cold start but as of early 2023 that appears to no longer be an issue.
|
|
204
196
|
|
|
205
197
|
## Next.js Apps
|
|
206
198
|
|
|
207
|
-
Create a Next.js app then follow the steps in this section to set it up for publishing to AWS Lambda @ Origin as a MicroApp. To publish new versions of the app use `npx
|
|
199
|
+
Create a Next.js app then follow the steps in this section to set it up for publishing to AWS Lambda @ Origin as a MicroApp. To publish new versions of the app use `npx pwrdrvr --new-version x.y.z` when logged in to the target AWS account.
|
|
208
200
|
|
|
209
201
|
### Modify package.json
|
|
210
202
|
|
|
211
|
-
Replace the version with `0.0.0` so it can be modified by the `
|
|
203
|
+
Replace the version with `0.0.0` so it can be modified by the `pwrdrvr` CLI.
|
|
212
204
|
|
|
213
205
|
### Install Dependencies
|
|
214
206
|
|
|
215
207
|
```
|
|
216
|
-
npm i --save-dev
|
|
208
|
+
npm i --save-dev pwrdrvr
|
|
217
209
|
```
|
|
218
210
|
|
|
219
211
|
### Dockerfile
|