open-shield-python 0.2.5__tar.gz → 0.2.7__tar.gz
This diff represents the content of publicly available package versions that have been released to one of the supported registries. The information contained in this diff is provided for informational purposes only and reflects changes between package versions as they appear in their respective public registries.
- open_shield_python-0.2.7/CHANGELOG.md +47 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/PKG-INFO +36 -28
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/README.md +35 -27
- open_shield_python-0.2.7/docs/images/sequence-flow.png +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/pyproject.toml +1 -1
- open_shield_python-0.2.5/CHANGELOG.md +0 -13
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/.agent/skills/python-packaging/SKILL.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/.agent/skills/python-packaging/resources/implementation-playbook.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/.agent/skills/python-pro/SKILL.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/.agent/skills/python-testing-patterns/SKILL.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/.agent/skills/python-testing-patterns/resources/implementation-playbook.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/.agent/skills/solid_architecture/SKILL.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/.agent/skills/solid_architecture/examples/before_after_refactor.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/.agent/skills/solid_architecture/examples/clean_architecture_layout.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/.agent/skills/solid_architecture/examples/dip_ports_adapters.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/.agent/skills/solid_architecture/resources/code_review_checklist.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/.github/workflows/ci.yml +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/.gitignore +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/CODE_OF_CONDUCT.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/CONTRIBUTING.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/LICENSE +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/SECURITY.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/docs/architecture/system-overview.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/docs/design/overview.md +0 -0
- {open_shield_python-0.2.5/docs → open_shield_python-0.2.7/docs/images}/architecture.png +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/docs/implementation/guidelines.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/docs/planning/README.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/docs/planning/backlog.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/docs/planning/decisions/0000-template.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/docs/planning/decisions/001-clean-architecture.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/docs/planning/decisions/002-modern-tooling.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/docs/planning/decisions/003-pydantic-usage.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/docs/planning/phases/phase-0-init.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/docs/planning/phases/phase-1-core.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/docs/planning/phases/phase-2-authz.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/docs/planning/phases/phase-3-integration.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/docs/planning/phases/phase-4-publish.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/docs/planning/roadmap.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/docs/planning/specs.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/docs/planning/tasks.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/docs/planning/tech-debt.md +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/main.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/adapters/__init__.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/adapters/config.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/adapters/key_provider.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/adapters/token_validator.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/api/__init__.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/api/fastapi/__init__.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/api/fastapi/dependencies.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/api/fastapi/middleware.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/domain/__init__.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/domain/entities.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/domain/exceptions.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/domain/ports/__init__.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/domain/ports/key_provider.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/domain/ports/tenant_resolver.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/domain/ports/token_validator.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/domain/services/__init__.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/domain/services/authorization_service.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/domain/services/claim_mapping.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/domain/services/token_service.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/tests/integration/adapters/test_key_provider.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/tests/integration/adapters/test_token_validator.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/tests/integration/api/test_fastapi.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/tests/unit/adapters/test_config.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/tests/unit/domain/test_authorization_service.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/tests/unit/domain/test_claim_mapping.py +0 -0
- {open_shield_python-0.2.5 → open_shield_python-0.2.7}/tests/unit/domain/test_token_service.py +0 -0
|
@@ -0,0 +1,47 @@
|
|
|
1
|
+
# Changelog
|
|
2
|
+
|
|
3
|
+
All notable changes to this project will be documented in this file.
|
|
4
|
+
|
|
5
|
+
## [v0.2.7] - 2026-03-06
|
|
6
|
+
|
|
7
|
+
### Changed
|
|
8
|
+
- **Documentation**: Restructured README to prioritize architecture diagrams for better impact on PyPI and GitHub.
|
|
9
|
+
|
|
10
|
+
## [v0.2.6] - 2026-03-06
|
|
11
|
+
|
|
12
|
+
### Added
|
|
13
|
+
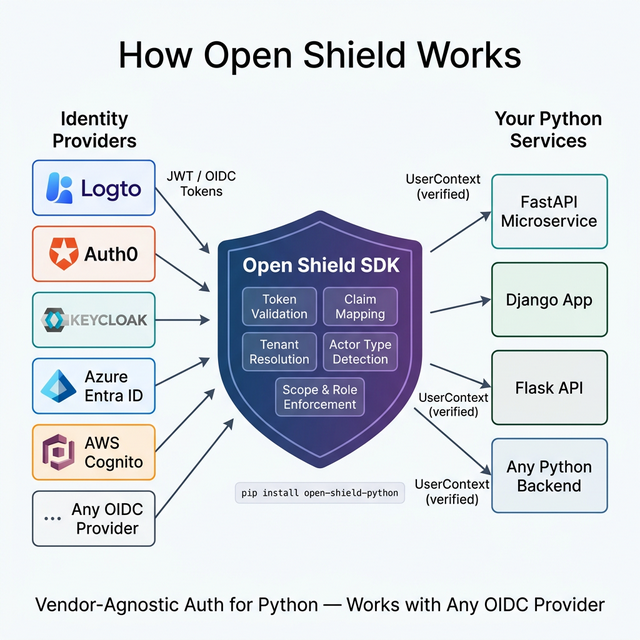
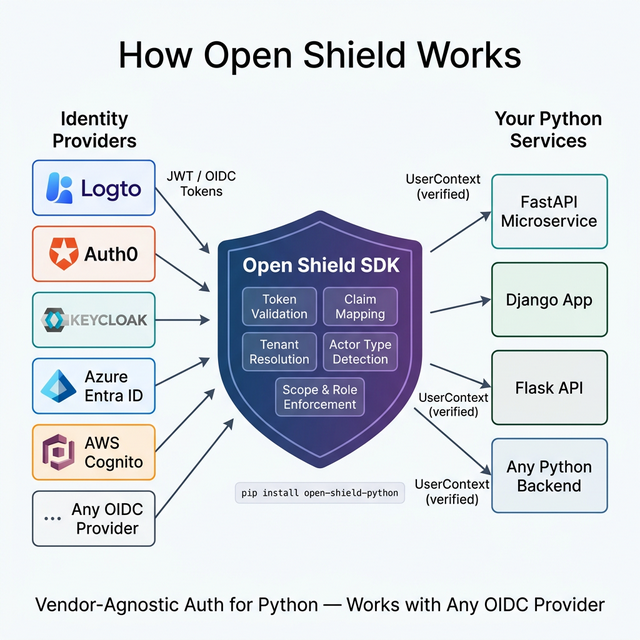
- **Architecture Diagram**: High-level architecture image showing how Open Shield SDK sits between identity providers and Python backends.
|
|
14
|
+
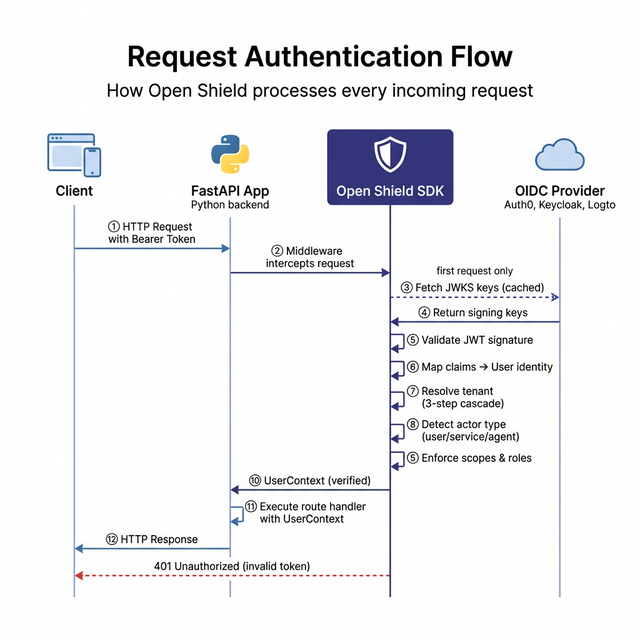
- **Sequence Diagram**: Request authentication flow diagram illustrating the step-by-step processing of each incoming request.
|
|
15
|
+
|
|
16
|
+
### Changed
|
|
17
|
+
- **Documentation**: Completely overhauled the Architecture section in README with visual diagrams and detailed explanations.
|
|
18
|
+
- **Images**: Organized documentation images into `docs/images/` directory.
|
|
19
|
+
|
|
20
|
+
### Project Maintenance
|
|
21
|
+
- **Git Identity Cleaned**: Rewrote entire repository history to unify all commits under the `avinash-singh-io` identity with a verified email.
|
|
22
|
+
- **Collaborator Cleanup**: Pruned legacy collaborator access and stale remote tracking branches.
|
|
23
|
+
- **Release Synchronization**: Synchronized GitHub tags and releases with the new clean history.
|
|
24
|
+
|
|
25
|
+
|
|
26
|
+
## [v0.2.0] - 2026-02-16
|
|
27
|
+
|
|
28
|
+
### Added
|
|
29
|
+
- **Configurable Claim Mapping**: Map any JWT claim to user/tenant/role fields via environment variables — zero code changes when switching providers.
|
|
30
|
+
- **3-Step Tenant Resolution Cascade**: Support for individual users (`sub` fallback), SaaS organizations (org claim), and M2M service accounts (`TenantResolverPort`).
|
|
31
|
+
- **Actor Type Inference**: Automatic detection of `user`, `service`, and `agent` actor types.
|
|
32
|
+
- **Tenant Resolution Metadata**: Every resolved tenant includes traceability (`m2m_lookup`, `claim`, `sub_fallback`).
|
|
33
|
+
- **Optional Authentication**: `get_optional_user_context` dependency for routes that work with or without auth.
|
|
34
|
+
|
|
35
|
+
### Changed
|
|
36
|
+
- **Configuration**: Added environment variables for claim mapping (`OPEN_SHIELD_USER_ID_CLAIM`, `OPEN_SHIELD_TENANT_ID_CLAIM`, etc.).
|
|
37
|
+
- **Open Source Readiness**: Added `CODE_OF_CONDUCT.md`, `SECURITY.md`, `CONTRIBUTING.md`, and comprehensive project metadata.
|
|
38
|
+
|
|
39
|
+
## [v0.1.0] - 2026-02-12
|
|
40
|
+
|
|
41
|
+
### Added
|
|
42
|
+
- **Core Domain**: Implemented `TokenService`, `AuthorizationService`, and core entities (`User`, `Token`).
|
|
43
|
+
- **Adapters**: Added `PyJWTValidator` for token validation and `OIDCDiscoKeyProvider` for JWKS fetching.
|
|
44
|
+
- **FastAPI Integration**: Added `OpenShieldMiddleware` and dependencies (`get_user_context`, `RequireScope`, `RequireRole`).
|
|
45
|
+
- **Configuration**: `Pydantic` based configuration loading from environment variables.
|
|
46
|
+
- **Documentation**: Comprehensive `README.md` and `CONTRIBUTING.md`.
|
|
47
|
+
- **Testing**: Integration tests for adapters and API layer.
|
|
@@ -1,6 +1,6 @@
|
|
|
1
1
|
Metadata-Version: 2.4
|
|
2
2
|
Name: open-shield-python
|
|
3
|
-
Version: 0.2.
|
|
3
|
+
Version: 0.2.7
|
|
4
4
|
Summary: Vendor-agnostic authentication and authorization enforcement SDK
|
|
5
5
|
Project-URL: Homepage, https://github.com/avinash-singh-io/open-shield-python
|
|
6
6
|
Project-URL: Repository, https://github.com/avinash-singh-io/open-shield-python
|
|
@@ -32,6 +32,39 @@ Vendor-agnostic authentication and authorization enforcement SDK for Python.
|
|
|
32
32
|
|
|
33
33
|
Open Shield lets you enforce authentication (AuthN) and authorization (AuthZ) in your Python applications without coupling to a specific identity provider. Works with **Logto**, **Keycloak**, **Auth0**, **Entra ID**, **Cognito**, or any OIDC-compliant provider.
|
|
34
34
|
|
|
35
|
+
---
|
|
36
|
+
|
|
37
|
+
## Architecture
|
|
38
|
+
|
|
39
|
+
Open Shield sits as a **thin, powerful layer** between your identity provider and your Python backend — handling all the complexity of token validation, claim extraction, tenant resolution, and authorization enforcement so you don't have to.
|
|
40
|
+
|
|
41
|
+
|
|
42
|
+
|
|
43
|
+
### How It Works
|
|
44
|
+
|
|
45
|
+
1. **Any OIDC Identity Provider** (Logto, Auth0, Keycloak, Azure Entra ID, AWS Cognito, or your own) issues a JWT token when a user or service authenticates.
|
|
46
|
+
2. **Open Shield SDK** intercepts the incoming request in your Python application and:
|
|
47
|
+
- **Validates the token** — verifies the signature using auto-fetched JWKS keys from the provider's OIDC discovery endpoint.
|
|
48
|
+
- **Maps claims** — extracts user ID, email, tenant, scopes, and roles from the JWT using your configurable claim mapping (every provider names claims differently — Open Shield normalizes them).
|
|
49
|
+
- **Resolves the tenant** — determines tenant isolation using the 3-step cascade (M2M lookup → org claim → sub fallback).
|
|
50
|
+
- **Detects actor type** — classifies the caller as `user`, `service`, or `agent`.
|
|
51
|
+
- **Enforces authorization** — checks scopes and roles before the request reaches your handler.
|
|
52
|
+
3. **Your Python service** receives a clean, verified `UserContext` object — ready to use. No JWT parsing, no OIDC plumbing, no provider-specific code.
|
|
53
|
+
|
|
54
|
+
### Request Authentication Flow
|
|
55
|
+
|
|
56
|
+
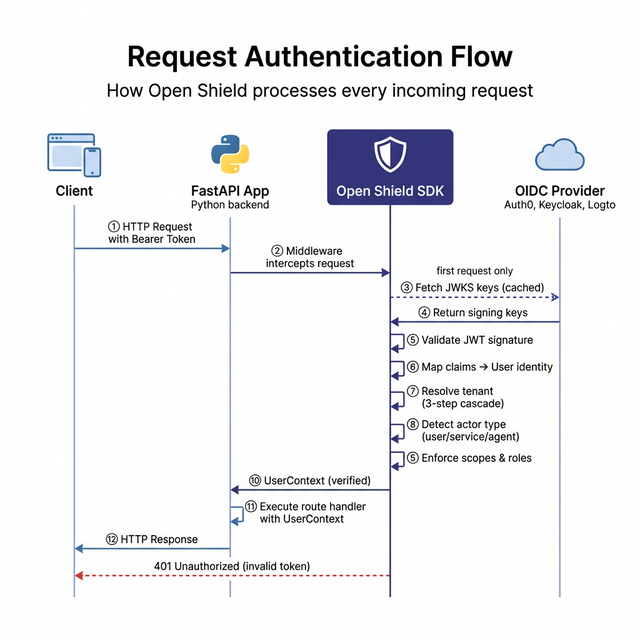
|
|
57
|
+
|
|
58
|
+
### Why This Matters
|
|
59
|
+
|
|
60
|
+
- **Works with any OIDC provider** — Switch from Auth0 to Keycloak? Change two environment variables. Zero code changes.
|
|
61
|
+
- **Works with any Python framework** — First-class FastAPI support today, with Django and Flask coming soon. The core logic is pure Python with no framework dependency.
|
|
62
|
+
- **Built on Clean Architecture** — The domain layer has zero external dependencies. All I/O (JWT decoding, OIDC discovery) happens through abstract ports implemented by swappable adapters.
|
|
63
|
+
- **Easy to test** — Mock the `TokenValidatorPort` for fast unit tests without any HTTP calls.
|
|
64
|
+
- **Easy to extend** — Implement `TenantResolverPort` to wire in your own database for M2M tenant lookups.
|
|
65
|
+
|
|
66
|
+
---
|
|
67
|
+
|
|
35
68
|
## Features
|
|
36
69
|
|
|
37
70
|
- **Vendor Neutral** — Works with any OIDC-compliant identity provider
|
|
@@ -43,6 +76,8 @@ Open Shield lets you enforce authentication (AuthN) and authorization (AuthZ) in
|
|
|
43
76
|
- **Type Safe** — Fully typed, checked with `mypy`
|
|
44
77
|
- **Automatic JWKS Rotation** — Fetches and caches keys from OIDC discovery
|
|
45
78
|
|
|
79
|
+
---
|
|
80
|
+
|
|
46
81
|
## Installation
|
|
47
82
|
|
|
48
83
|
```bash
|
|
@@ -262,33 +297,6 @@ ctx.user.actor_type # "user" | "service" | "agent"
|
|
|
262
297
|
|
|
263
298
|
---
|
|
264
299
|
|
|
265
|
-
## Architecture
|
|
266
|
-
|
|
267
|
-
Open Shield sits as a **thin, powerful layer** between your identity provider and your Python backend — handling all the complexity of token validation, claim extraction, tenant resolution, and authorization enforcement so you don't have to.
|
|
268
|
-
|
|
269
|
-

|
|
270
|
-
|
|
271
|
-
### How It Works
|
|
272
|
-
|
|
273
|
-
1. **Any OIDC Identity Provider** (Logto, Auth0, Keycloak, Azure Entra ID, AWS Cognito, or your own) issues a JWT token when a user or service authenticates.
|
|
274
|
-
2. **Open Shield SDK** intercepts the incoming request in your Python application and:
|
|
275
|
-
- **Validates the token** — verifies the signature using auto-fetched JWKS keys from the provider's OIDC discovery endpoint.
|
|
276
|
-
- **Maps claims** — extracts user ID, email, tenant, scopes, and roles from the JWT using your configurable claim mapping (every provider names claims differently — Open Shield normalizes them).
|
|
277
|
-
- **Resolves the tenant** — determines tenant isolation using the 3-step cascade (M2M lookup → org claim → sub fallback).
|
|
278
|
-
- **Detects actor type** — classifies the caller as `user`, `service`, or `agent`.
|
|
279
|
-
- **Enforces authorization** — checks scopes and roles before the request reaches your handler.
|
|
280
|
-
3. **Your Python service** receives a clean, verified `UserContext` object — ready to use. No JWT parsing, no OIDC plumbing, no provider-specific code.
|
|
281
|
-
|
|
282
|
-
### Why This Matters
|
|
283
|
-
|
|
284
|
-
- **Works with any OIDC provider** — Switch from Auth0 to Keycloak? Change two environment variables. Zero code changes.
|
|
285
|
-
- **Works with any Python framework** — First-class FastAPI support today, with Django and Flask coming soon. The core logic is pure Python with no framework dependency.
|
|
286
|
-
- **Built on Clean Architecture** — The domain layer has zero external dependencies. All I/O (JWT decoding, OIDC discovery) happens through abstract ports implemented by swappable adapters.
|
|
287
|
-
- **Easy to test** — Mock the `TokenValidatorPort` for fast unit tests without any HTTP calls.
|
|
288
|
-
- **Easy to extend** — Implement `TenantResolverPort` to wire in your own database for M2M tenant lookups.
|
|
289
|
-
|
|
290
|
-
---
|
|
291
|
-
|
|
292
300
|
## Optional Authentication
|
|
293
301
|
|
|
294
302
|
For routes that work with or without auth (e.g., public APIs with enhanced features for logged-in users):
|
|
@@ -6,6 +6,39 @@ Vendor-agnostic authentication and authorization enforcement SDK for Python.
|
|
|
6
6
|
|
|
7
7
|
Open Shield lets you enforce authentication (AuthN) and authorization (AuthZ) in your Python applications without coupling to a specific identity provider. Works with **Logto**, **Keycloak**, **Auth0**, **Entra ID**, **Cognito**, or any OIDC-compliant provider.
|
|
8
8
|
|
|
9
|
+
---
|
|
10
|
+
|
|
11
|
+
## Architecture
|
|
12
|
+
|
|
13
|
+
Open Shield sits as a **thin, powerful layer** between your identity provider and your Python backend — handling all the complexity of token validation, claim extraction, tenant resolution, and authorization enforcement so you don't have to.
|
|
14
|
+
|
|
15
|
+
|
|
16
|
+
|
|
17
|
+
### How It Works
|
|
18
|
+
|
|
19
|
+
1. **Any OIDC Identity Provider** (Logto, Auth0, Keycloak, Azure Entra ID, AWS Cognito, or your own) issues a JWT token when a user or service authenticates.
|
|
20
|
+
2. **Open Shield SDK** intercepts the incoming request in your Python application and:
|
|
21
|
+
- **Validates the token** — verifies the signature using auto-fetched JWKS keys from the provider's OIDC discovery endpoint.
|
|
22
|
+
- **Maps claims** — extracts user ID, email, tenant, scopes, and roles from the JWT using your configurable claim mapping (every provider names claims differently — Open Shield normalizes them).
|
|
23
|
+
- **Resolves the tenant** — determines tenant isolation using the 3-step cascade (M2M lookup → org claim → sub fallback).
|
|
24
|
+
- **Detects actor type** — classifies the caller as `user`, `service`, or `agent`.
|
|
25
|
+
- **Enforces authorization** — checks scopes and roles before the request reaches your handler.
|
|
26
|
+
3. **Your Python service** receives a clean, verified `UserContext` object — ready to use. No JWT parsing, no OIDC plumbing, no provider-specific code.
|
|
27
|
+
|
|
28
|
+
### Request Authentication Flow
|
|
29
|
+
|
|
30
|
+
|
|
31
|
+
|
|
32
|
+
### Why This Matters
|
|
33
|
+
|
|
34
|
+
- **Works with any OIDC provider** — Switch from Auth0 to Keycloak? Change two environment variables. Zero code changes.
|
|
35
|
+
- **Works with any Python framework** — First-class FastAPI support today, with Django and Flask coming soon. The core logic is pure Python with no framework dependency.
|
|
36
|
+
- **Built on Clean Architecture** — The domain layer has zero external dependencies. All I/O (JWT decoding, OIDC discovery) happens through abstract ports implemented by swappable adapters.
|
|
37
|
+
- **Easy to test** — Mock the `TokenValidatorPort` for fast unit tests without any HTTP calls.
|
|
38
|
+
- **Easy to extend** — Implement `TenantResolverPort` to wire in your own database for M2M tenant lookups.
|
|
39
|
+
|
|
40
|
+
---
|
|
41
|
+
|
|
9
42
|
## Features
|
|
10
43
|
|
|
11
44
|
- **Vendor Neutral** — Works with any OIDC-compliant identity provider
|
|
@@ -17,6 +50,8 @@ Open Shield lets you enforce authentication (AuthN) and authorization (AuthZ) in
|
|
|
17
50
|
- **Type Safe** — Fully typed, checked with `mypy`
|
|
18
51
|
- **Automatic JWKS Rotation** — Fetches and caches keys from OIDC discovery
|
|
19
52
|
|
|
53
|
+
---
|
|
54
|
+
|
|
20
55
|
## Installation
|
|
21
56
|
|
|
22
57
|
```bash
|
|
@@ -236,33 +271,6 @@ ctx.user.actor_type # "user" | "service" | "agent"
|
|
|
236
271
|
|
|
237
272
|
---
|
|
238
273
|
|
|
239
|
-
## Architecture
|
|
240
|
-
|
|
241
|
-
Open Shield sits as a **thin, powerful layer** between your identity provider and your Python backend — handling all the complexity of token validation, claim extraction, tenant resolution, and authorization enforcement so you don't have to.
|
|
242
|
-
|
|
243
|
-

|
|
244
|
-
|
|
245
|
-
### How It Works
|
|
246
|
-
|
|
247
|
-
1. **Any OIDC Identity Provider** (Logto, Auth0, Keycloak, Azure Entra ID, AWS Cognito, or your own) issues a JWT token when a user or service authenticates.
|
|
248
|
-
2. **Open Shield SDK** intercepts the incoming request in your Python application and:
|
|
249
|
-
- **Validates the token** — verifies the signature using auto-fetched JWKS keys from the provider's OIDC discovery endpoint.
|
|
250
|
-
- **Maps claims** — extracts user ID, email, tenant, scopes, and roles from the JWT using your configurable claim mapping (every provider names claims differently — Open Shield normalizes them).
|
|
251
|
-
- **Resolves the tenant** — determines tenant isolation using the 3-step cascade (M2M lookup → org claim → sub fallback).
|
|
252
|
-
- **Detects actor type** — classifies the caller as `user`, `service`, or `agent`.
|
|
253
|
-
- **Enforces authorization** — checks scopes and roles before the request reaches your handler.
|
|
254
|
-
3. **Your Python service** receives a clean, verified `UserContext` object — ready to use. No JWT parsing, no OIDC plumbing, no provider-specific code.
|
|
255
|
-
|
|
256
|
-
### Why This Matters
|
|
257
|
-
|
|
258
|
-
- **Works with any OIDC provider** — Switch from Auth0 to Keycloak? Change two environment variables. Zero code changes.
|
|
259
|
-
- **Works with any Python framework** — First-class FastAPI support today, with Django and Flask coming soon. The core logic is pure Python with no framework dependency.
|
|
260
|
-
- **Built on Clean Architecture** — The domain layer has zero external dependencies. All I/O (JWT decoding, OIDC discovery) happens through abstract ports implemented by swappable adapters.
|
|
261
|
-
- **Easy to test** — Mock the `TokenValidatorPort` for fast unit tests without any HTTP calls.
|
|
262
|
-
- **Easy to extend** — Implement `TenantResolverPort` to wire in your own database for M2M tenant lookups.
|
|
263
|
-
|
|
264
|
-
---
|
|
265
|
-
|
|
266
274
|
## Optional Authentication
|
|
267
275
|
|
|
268
276
|
For routes that work with or without auth (e.g., public APIs with enhanced features for logged-in users):
|
|
Binary file
|
|
@@ -1,13 +0,0 @@
|
|
|
1
|
-
# Changelog
|
|
2
|
-
|
|
3
|
-
All notable changes to this project will be documented in this file.
|
|
4
|
-
|
|
5
|
-
## [v0.1.0] - 2026-02-12
|
|
6
|
-
|
|
7
|
-
### Added
|
|
8
|
-
- **Core Domain**: Implemented `TokenService`, `AuthorizationService`, and core entities (`User`, `Token`).
|
|
9
|
-
- **Adapters**: Added `PyJWTValidator` for token validation and `OIDCDiscoKeyProvider` for JWKS fetching.
|
|
10
|
-
- **FastAPI Integration**: Added `OpenShieldMiddleware` and dependencies (`get_user_context`, `RequireScope`, `RequireRole`).
|
|
11
|
-
- **Configuration**: `Pydantic` based configuration loading from environment variables.
|
|
12
|
-
- **Documentation**: Comprehensive `README.md` and `CONTRIBUTING.md`.
|
|
13
|
-
- **Testing**: Integration tests for adapters and API layer.
|
{open_shield_python-0.2.5 → open_shield_python-0.2.7}/.agent/skills/python-packaging/SKILL.md
RENAMED
|
File without changes
|
|
File without changes
|
|
File without changes
|
{open_shield_python-0.2.5 → open_shield_python-0.2.7}/.agent/skills/python-testing-patterns/SKILL.md
RENAMED
|
File without changes
|
|
File without changes
|
{open_shield_python-0.2.5 → open_shield_python-0.2.7}/.agent/skills/solid_architecture/SKILL.md
RENAMED
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
{open_shield_python-0.2.5 → open_shield_python-0.2.7}/docs/planning/decisions/0000-template.md
RENAMED
|
File without changes
|
|
File without changes
|
{open_shield_python-0.2.5 → open_shield_python-0.2.7}/docs/planning/decisions/002-modern-tooling.md
RENAMED
|
File without changes
|
{open_shield_python-0.2.5 → open_shield_python-0.2.7}/docs/planning/decisions/003-pydantic-usage.md
RENAMED
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
{open_shield_python-0.2.5 → open_shield_python-0.2.7}/docs/planning/phases/phase-3-integration.md
RENAMED
|
File without changes
|
{open_shield_python-0.2.5 → open_shield_python-0.2.7}/docs/planning/phases/phase-4-publish.md
RENAMED
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
{open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/adapters/key_provider.py
RENAMED
|
File without changes
|
{open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/adapters/token_validator.py
RENAMED
|
File without changes
|
|
File without changes
|
{open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/api/fastapi/__init__.py
RENAMED
|
File without changes
|
{open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/api/fastapi/dependencies.py
RENAMED
|
File without changes
|
{open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/api/fastapi/middleware.py
RENAMED
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
{open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/domain/ports/__init__.py
RENAMED
|
File without changes
|
{open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/domain/ports/key_provider.py
RENAMED
|
File without changes
|
|
File without changes
|
|
File without changes
|
{open_shield_python-0.2.5 → open_shield_python-0.2.7}/src/open_shield/domain/services/__init__.py
RENAMED
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
|
File without changes
|
{open_shield_python-0.2.5 → open_shield_python-0.2.7}/tests/unit/domain/test_claim_mapping.py
RENAMED
|
File without changes
|
{open_shield_python-0.2.5 → open_shield_python-0.2.7}/tests/unit/domain/test_token_service.py
RENAMED
|
File without changes
|